e BPF Programs Elazar Gershuni Noam Rinetzky Mooly
e. BPF Programs Elazar Gershuni, Noam Rinetzky, Mooly Sagiv (TAU) Leonid Ryzhyk, Nadav Amit, Nina Narodytska (VMWare Research) Jorge A. Navas (SRI International) Arie Gurfinkel (University of Waterloo)
• Device drivers (Slam, Blast) • Avionics (Astrée, CGS) • OS kernel extensions • e. BPF • Restricted class of programs • Safety is crucial • Particular properties • Verification is already mandatory • Programming for verifiability • Better analysis more programs
§ Simple § Scalable § Precise in practice § Improves functionality over existing verifier
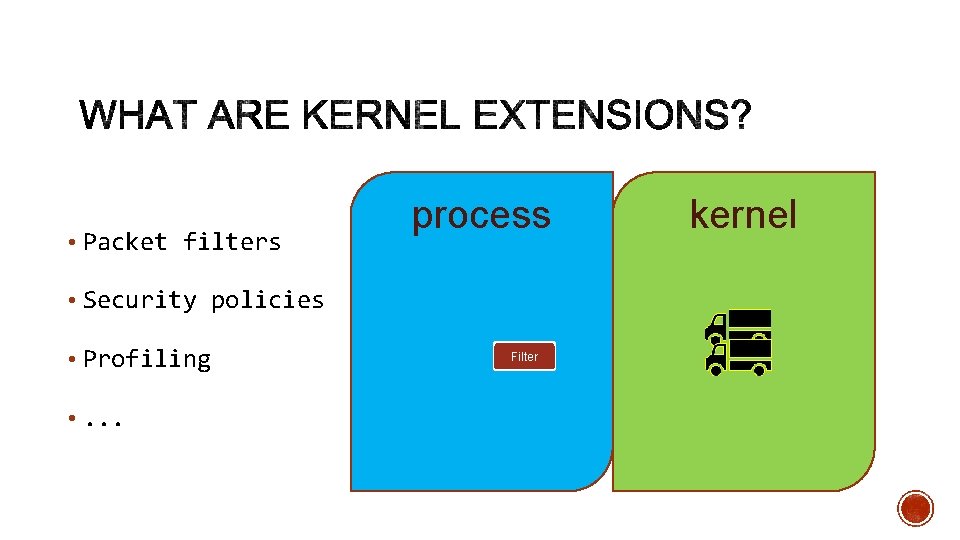
• Packet filters • Security policies • Profiling • . . . process P Filter kernel
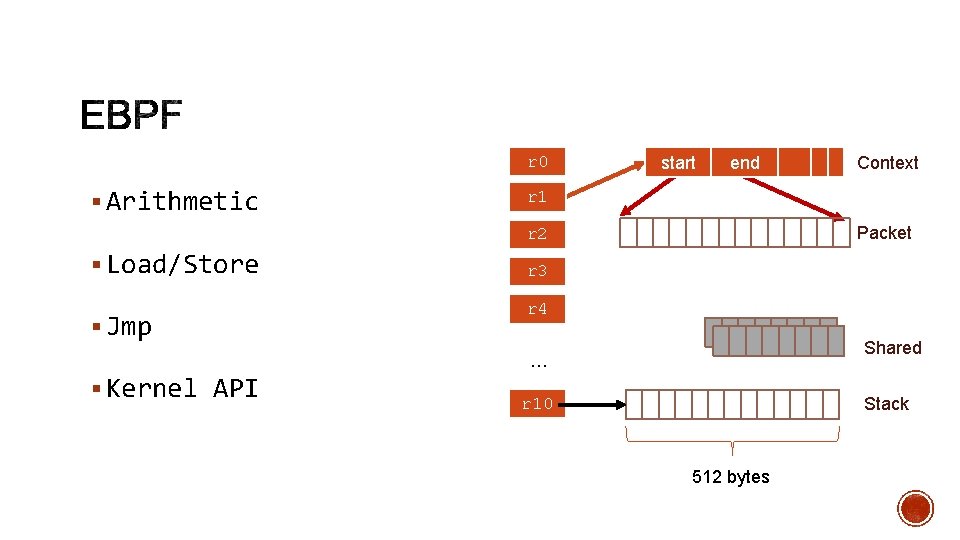
r 0 § Arithmetic start end r 1 Packet r 2 § Load/Store § Jmp r 3 r 4 Shared … § Kernel API Context Stack r 10 512 bytes
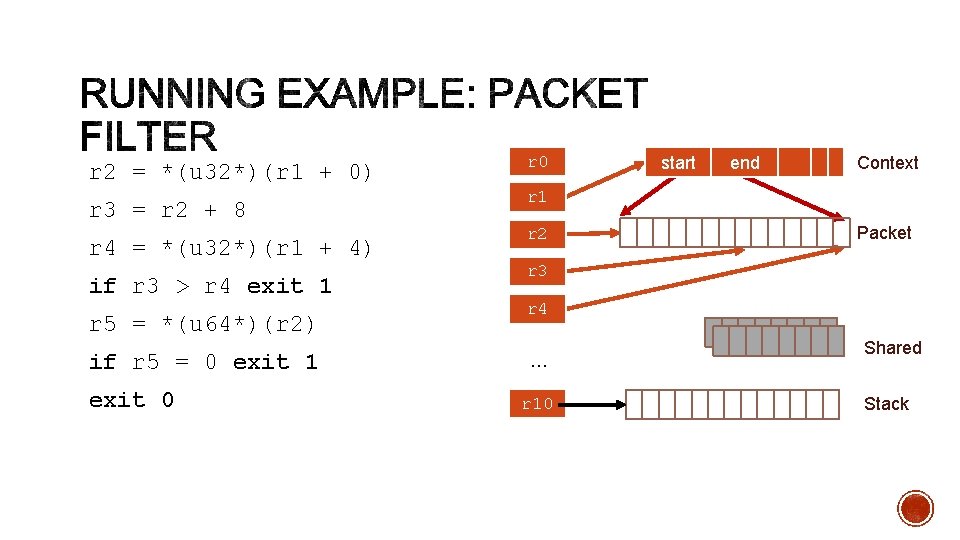
r 2 = *(u 32*)(r 1 + 0) r 3 = r 2 + 8 r 4 = *(u 32*)(r 1 + 4) if r 3 > r 4 exit 1 r 5 = *(u 64*)(r 2) if r 5 = 0 exit 1 exit 0 r 0 start end Context r 1 r 2 Packet r 3 r 4 … r 10 Shared Stack
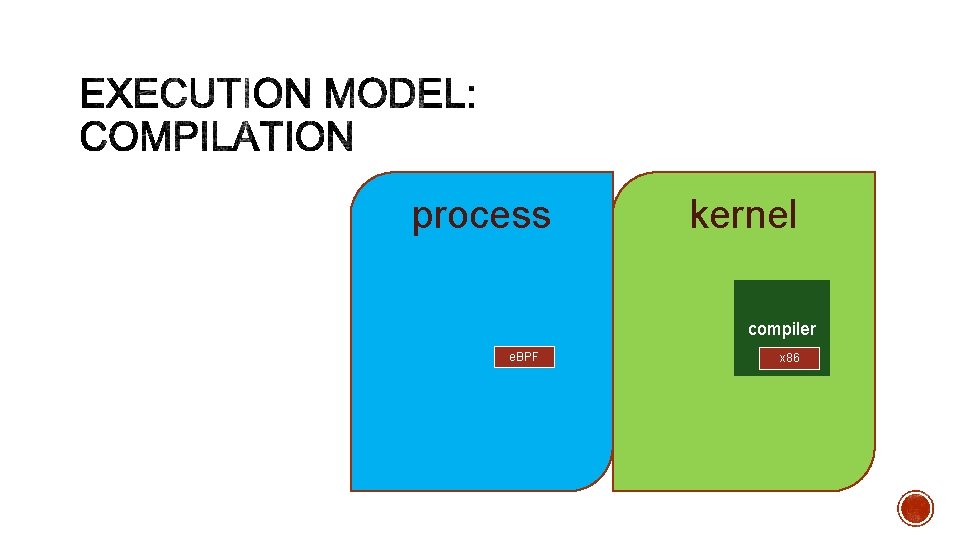
process P kernel compiler e. BPF x 86
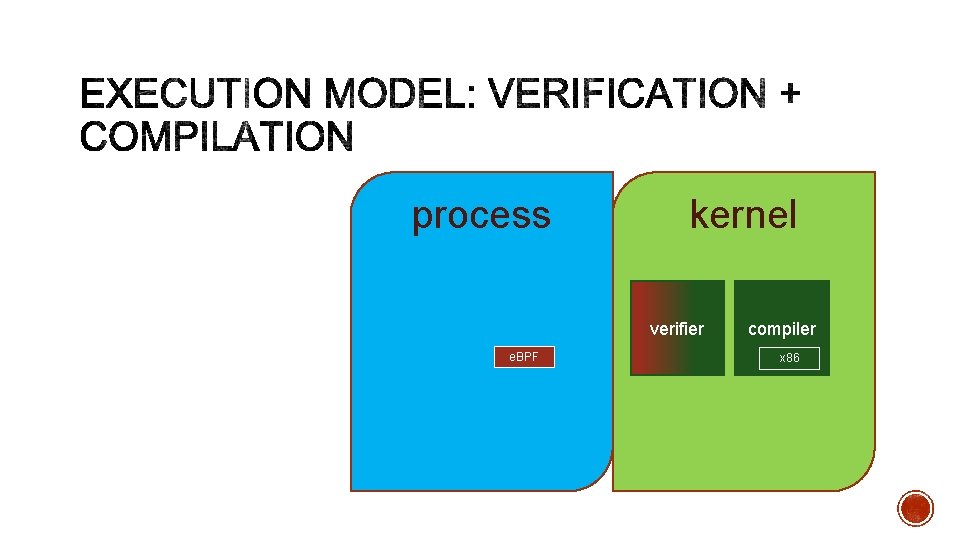
process P kernel verifier e. BPF compiler x 86
• Absence of memory errors • No leakage of kernel addresses • Termination
• Path enumeration • Heuristic pruning • Intervals, bit values, identities • Looks for specific patterns
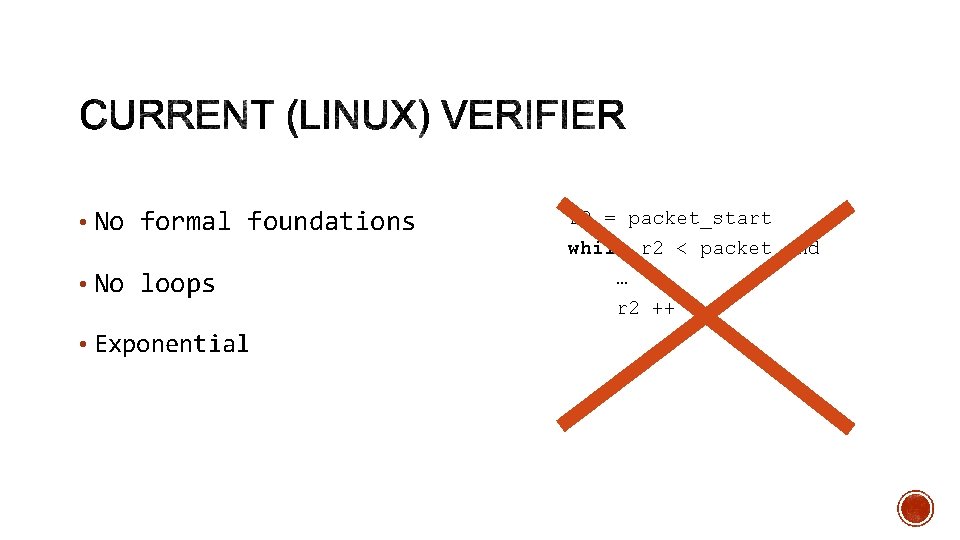
• No formal foundations • No loops • Exponential r 2 = packet_start while r 2 < packet_end … r 2 ++
• Based on abstract interpretation • Focus on safety properties • Loops • Cubic in theory • Linear in practice
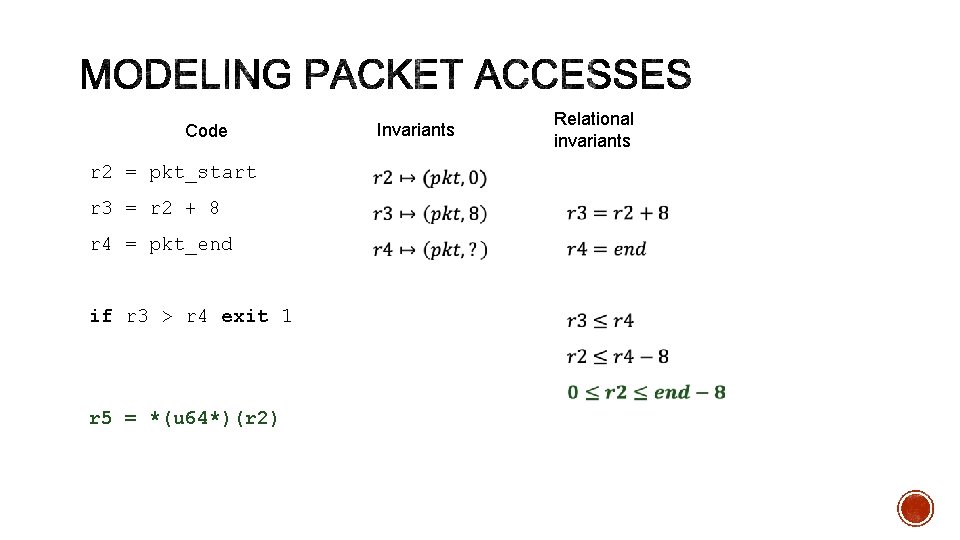
Code r 2 = pkt_start r 3 = r 2 + 8 r 4 = pkt_end if r 3 > r 4 exit 1 r 5 = *(u 64*)(r 2) Invariants Relational invariants
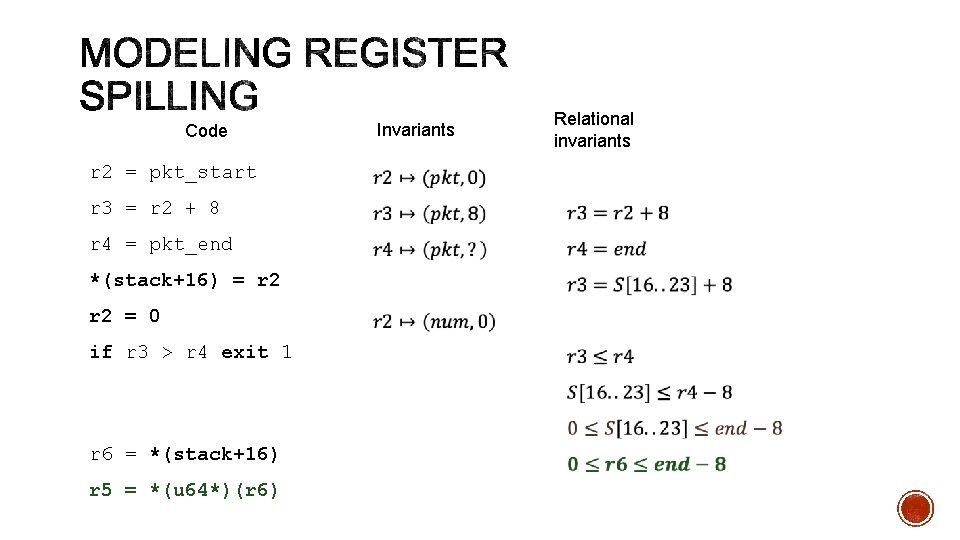
Code r 2 = pkt_start r 3 = r 2 + 8 r 4 = pkt_end *(stack+16) = r 2 = 0 if r 3 > r 4 exit 1 r 6 = *(stack+16) r 5 = *(u 64*)(r 6) Invariants Relational invariants
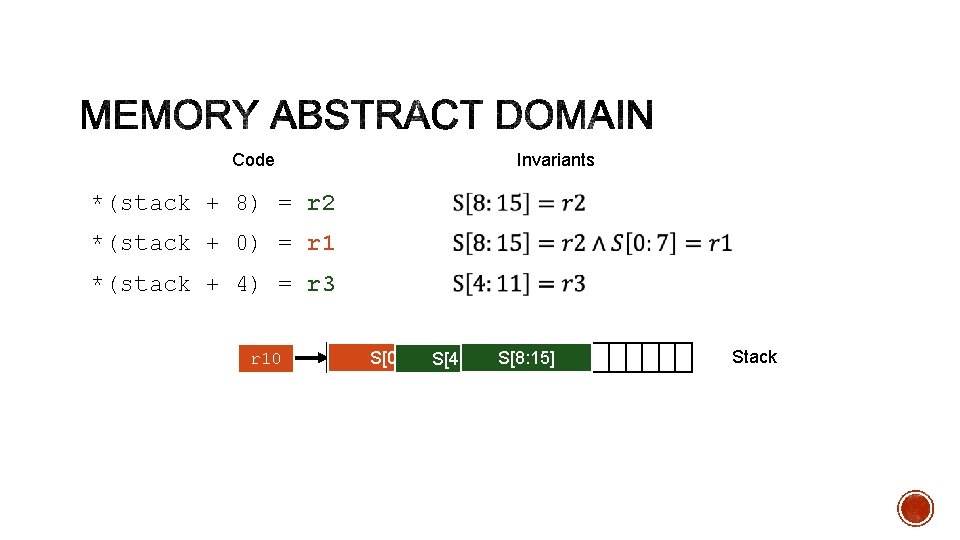
Code Invariants *(stack + 8) = r 2 *(stack + 0) = r 1 *(stack + 4) = r 3 r 10 S[0: 7] S[4: 11] S[8: 15] Stack
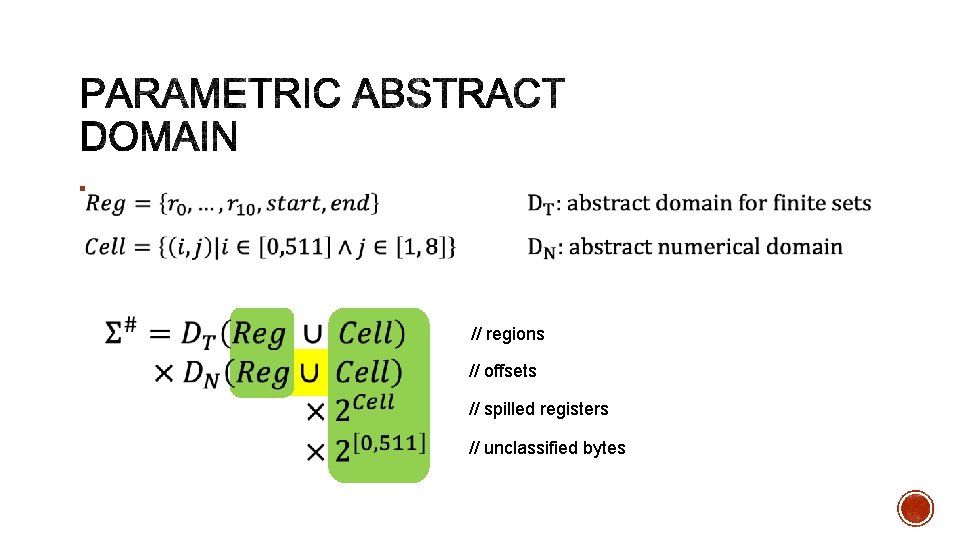
§ // regions // offsets // spilled registers // unclassified bytes
• 192 programs from real-world projects • Linux, Cilium, Open. VSwitch, Suricata • Number of instructions: 2 -3500 • All (currently) pass the Linux verifier
• Interval: 66% (128/192) • Zone, Octagon: 99% (191/192) • Polyhedra: 89% (170/192) • Generates large coefficients that cannot be represented in 64 bits
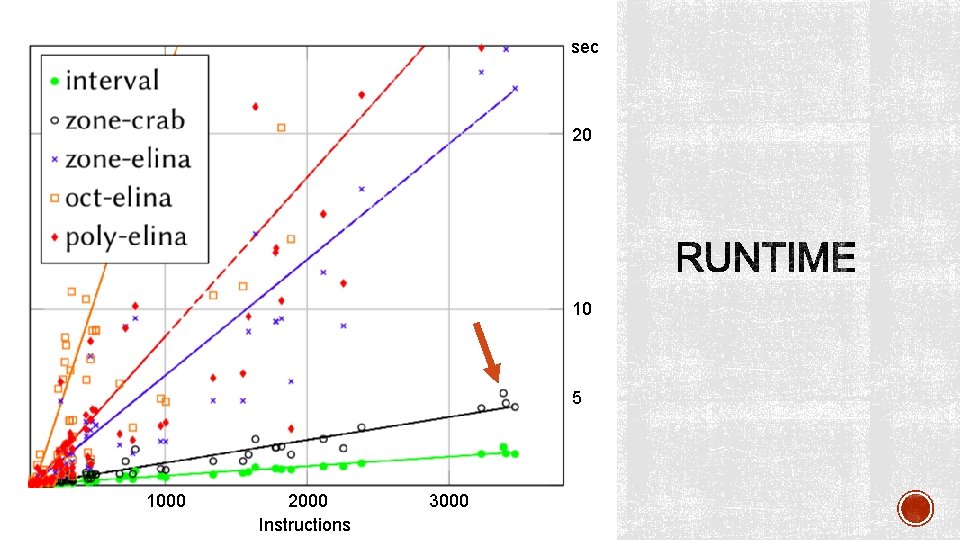
sec 20 10 5 1000 2000 Instructions 3000
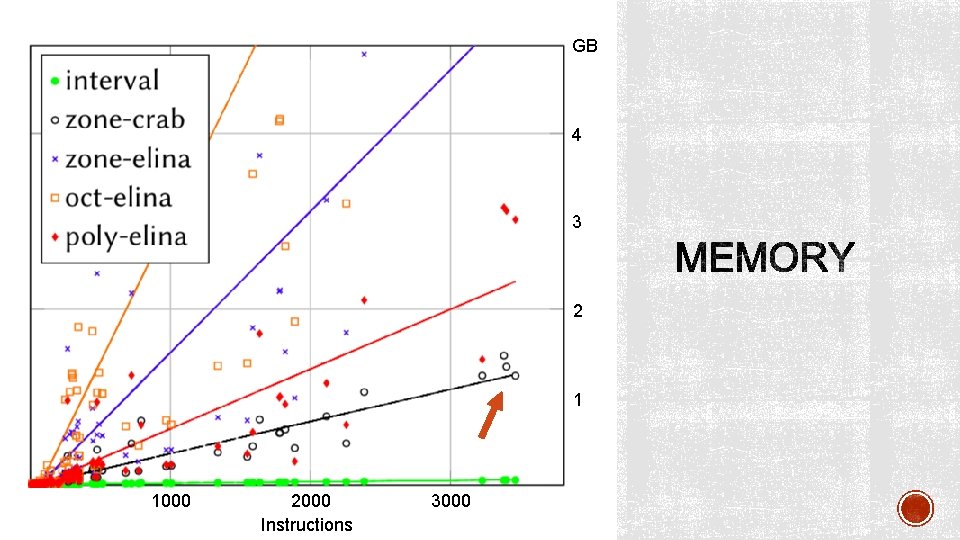
GB 4 3 2 1 1000 2000 Instructions 3000
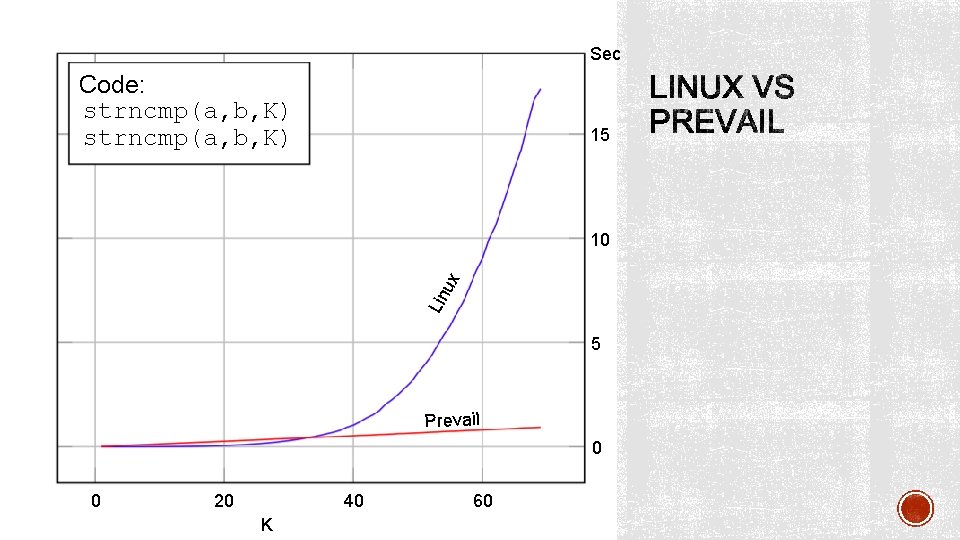
18 Code: strncmp(a, b, K) Sec 16 14 15 12 10 10 Lin ux 8 6 5 4 2 Prevail 0 0 100 New 0 200 300 400 500 600 700 800 Old 40 20 K 60 900 0
• Verification of kernel extensions is in industrial use • Abstract interpretation is even better • An opportunity for the verification community

ENABLER github. com/vbpf/ebpf-verifier
- Slides: 24