DVD Copyright Management Schemes Tanveer Alam CVN 1
- Slides: 12
DVD Copyright Management Schemes Tanveer Alam CVN 1
Project Goals l Compare high level schemes: – CSS (Content Scrambling System) – Advance access ctrl system (AACS) – Content Protection for Recordable Media (CPRM) & Pre-Recording Media (CPPM- Audio) l Some methods: – Scrambling – Vertical synch – Watermarking 2
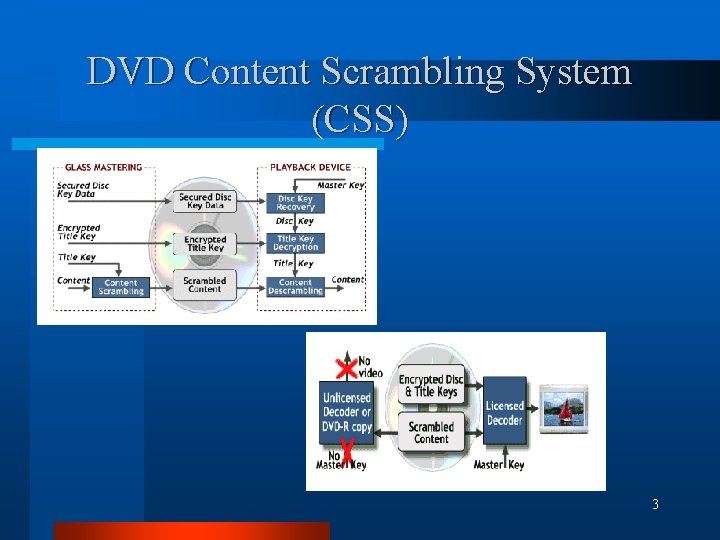
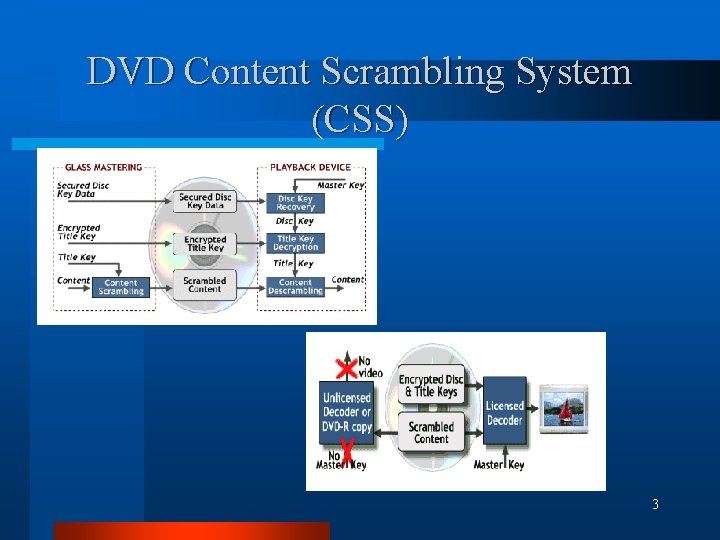
DVD Content Scrambling System (CSS) 3
Content Scrambling System (CSS) l Strengths – Proprietary code - harder to break – Key controlled by a few in expert group – Unique key for each DVD during etching l Weakness – – Existing method already circumvented De. CSS DVD manufacturers don’t want to pay loyally Currently easy to bypass. Newer more secure & robust methods needed. 4
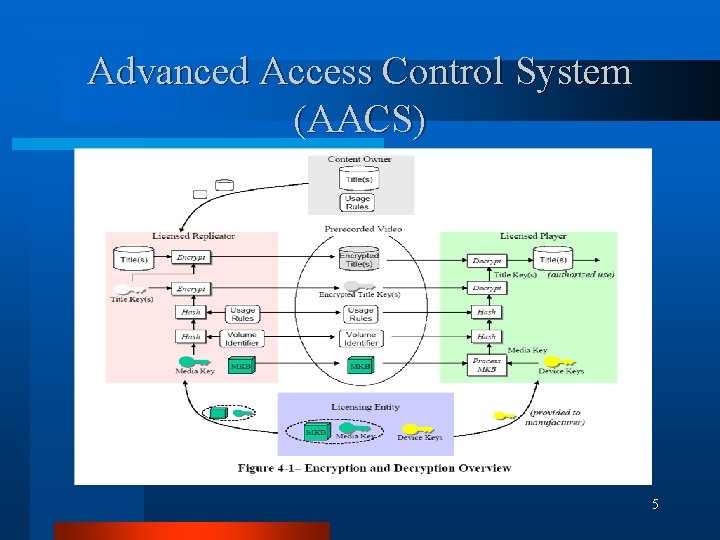
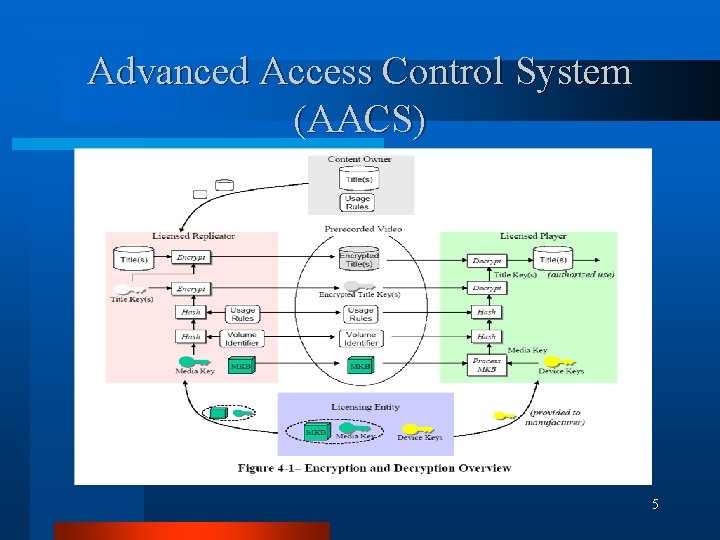
Advanced Access Control System (AACS) 5
AACS l Strengths – different levels of access possible – time limits, number of viewings, number of copies controlled – individual distributor can decide what types of protection to offer to consumer – centralized key server for authentication, individual keys for each player l Weakness – decoder must be a authorized unit for scheme to work 6
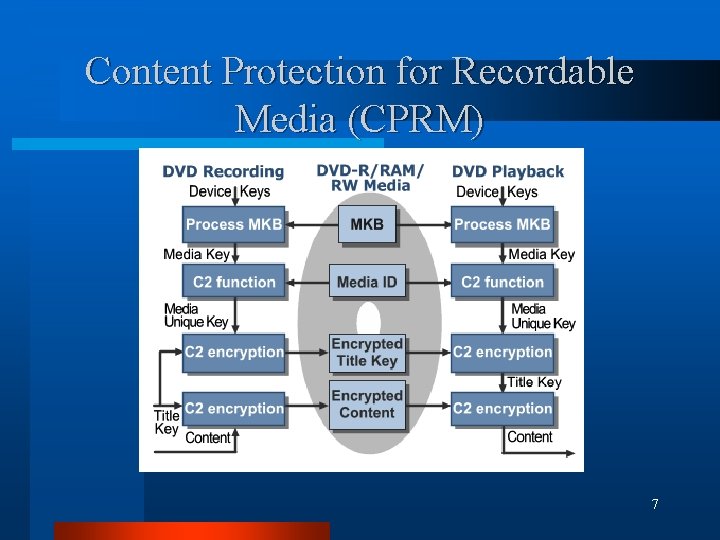
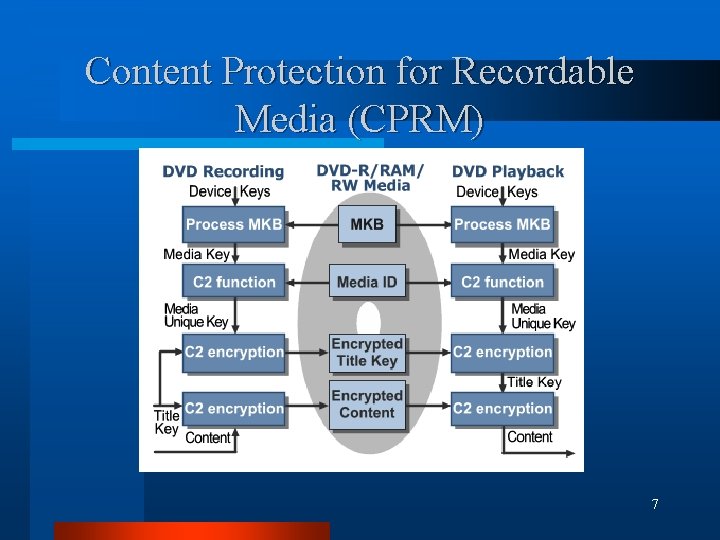
Content Protection for Recordable Media (CPRM) 7
CPRM Applies to DVD-R, DVD-RAM, DVD-RW l Features l – – Cryptomeria Cipher (C 2) for content encryption 4 layers of encryption using 56 -bit keys Unique device key for each recording/playback device Media Key Block (MKB) to allow for revoking a hacked device – Unique Media ID to prevent copying bit-for-bit. – Mutual identification process for PC based systems, which must be performed before CPRM protected data is transferred from DVD drive to the PC. 8
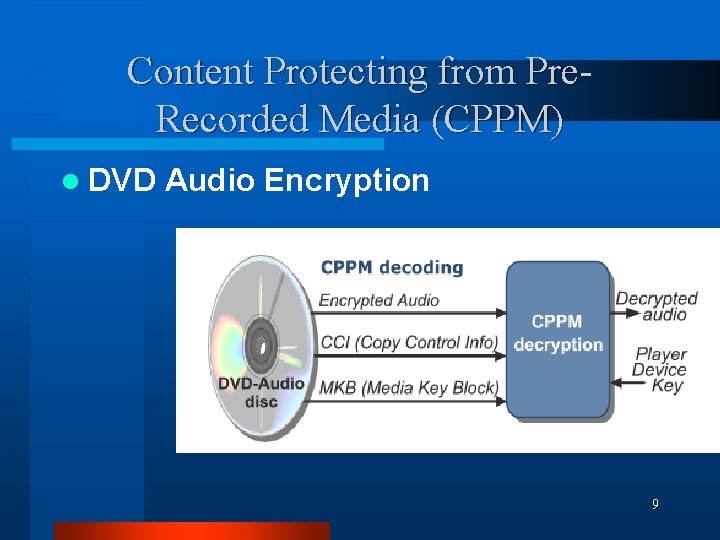
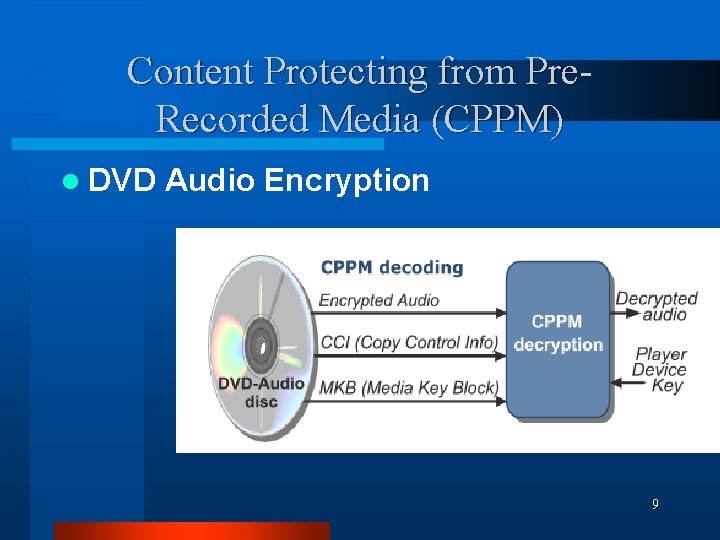
Content Protecting from Pre. Recorded Media (CPPM) l DVD Audio Encryption 9
CPPM l Features – – – Born from the failure of CSS, CSS-II Targeted to DVD- Audio 4 C consortium (IBM, Intel, MEI, Toshiba) 56 bit keys instead of 40 bit in CSS Uses Media Key Blocks (MKB) that can be revoked according to need. – Audio Watermarking included by Verance. 10
Conclusion l Compare methods for the following: – – l Transparency Robustness Security / Vulnerability Resilience Quality Metrics – – – Visual Error Rate Watermark response False Positive Rate Market response Resistance to attacks over time 11
Papers & References l l l Intel Corp, Warner Bros et al. , AACS Technical Overview, July 2004. Bloom, Jefferey A. et al; Copy Protection for DVD Video; Proceedings of IEEE, July 1999. http: //www. disctronics. co. uk/technology/dvdvi deo/dvdvid_copyprot. htm http: //www. cs. berkeley. edu/~daw/teaching/cs 261 -f 02/notes/content-prot http: //www. apim. ens. fr/Watermark 99/oostvee n/ 12