Dump Event Log Dumpel Dumpel exe Retrieves information
![Reg C: >reg REG Operation [Parameter List] Operation [ QUERY | ADD | DELETE Reg C: >reg REG Operation [Parameter List] Operation [ QUERY | ADD | DELETE](https://slidetodoc.com/presentation_image/aea8a83514a2f0a3cf762235e7b7ff52/image-5.jpg)
- Slides: 10
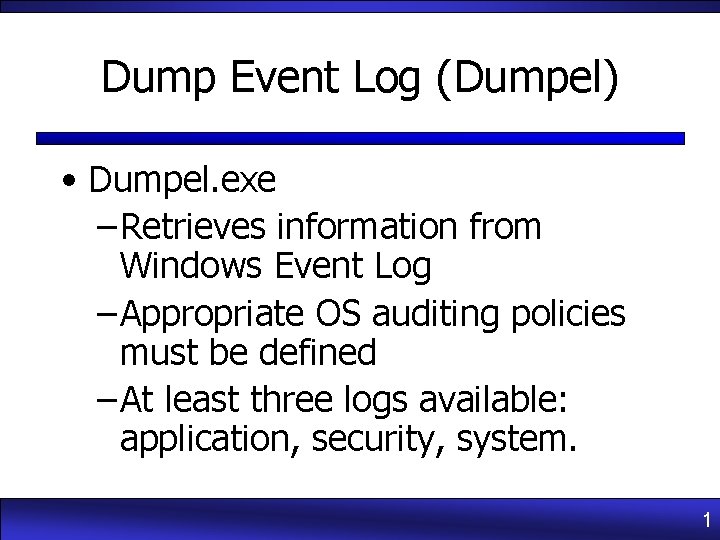
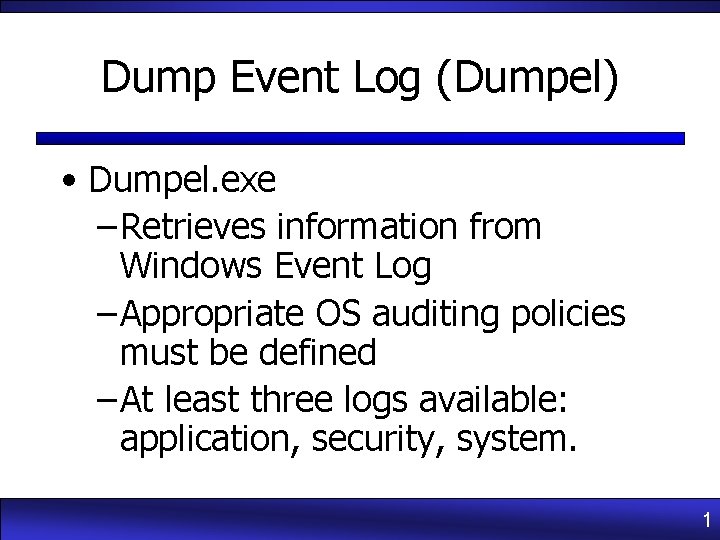
Dump Event Log (Dumpel) • Dumpel. exe – Retrieves information from Windows Event Log – Appropriate OS auditing policies must be defined – At least three logs available: application, security, system. 1
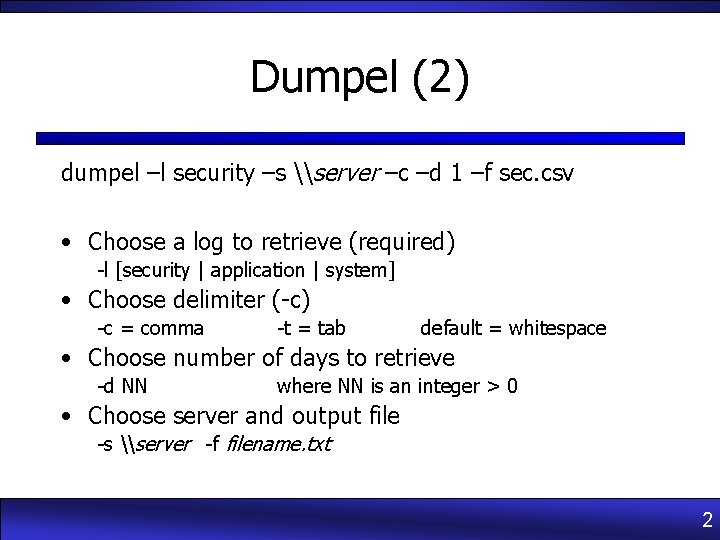
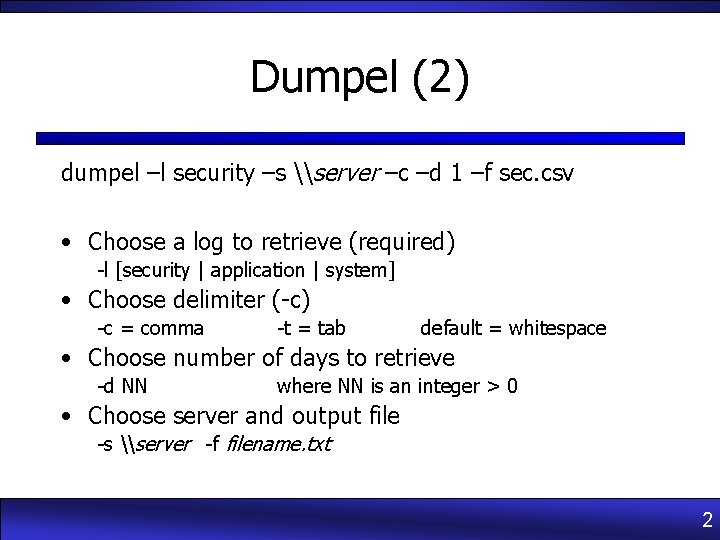
Dumpel (2) dumpel –l security –s \server –c –d 1 –f sec. csv • Choose a log to retrieve (required) -l [security | application | system] • Choose delimiter (-c) -c = comma -t = tab default = whitespace • Choose number of days to retrieve -d NN where NN is an integer > 0 • Choose server and output file -s \server -f filename. txt 2
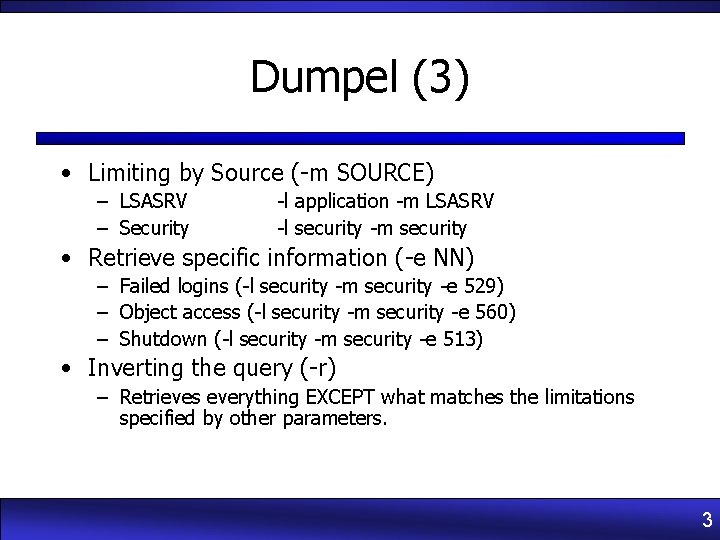
Dumpel (3) • Limiting by Source (-m SOURCE) – LSASRV – Security -l application -m LSASRV -l security -m security • Retrieve specific information (-e NN) – Failed logins (-l security -m security -e 529) – Object access (-l security -m security -e 560) – Shutdown (-l security -m security -e 513) • Inverting the query (-r) – Retrieves everything EXCEPT what matches the limitations specified by other parameters. 3
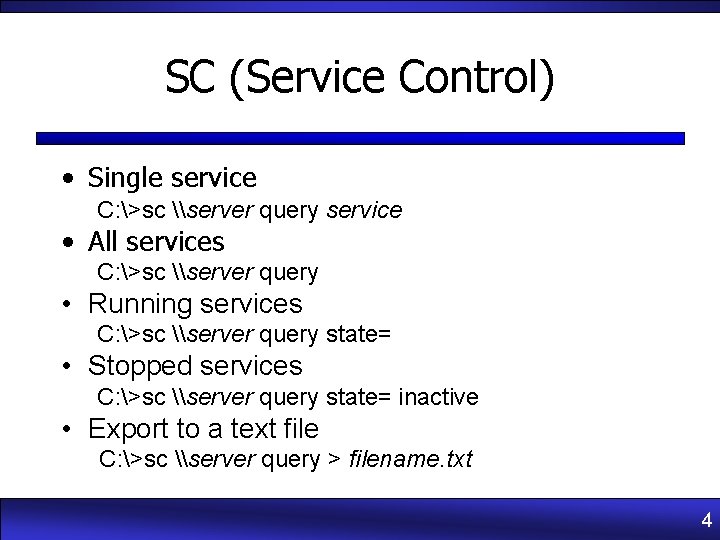
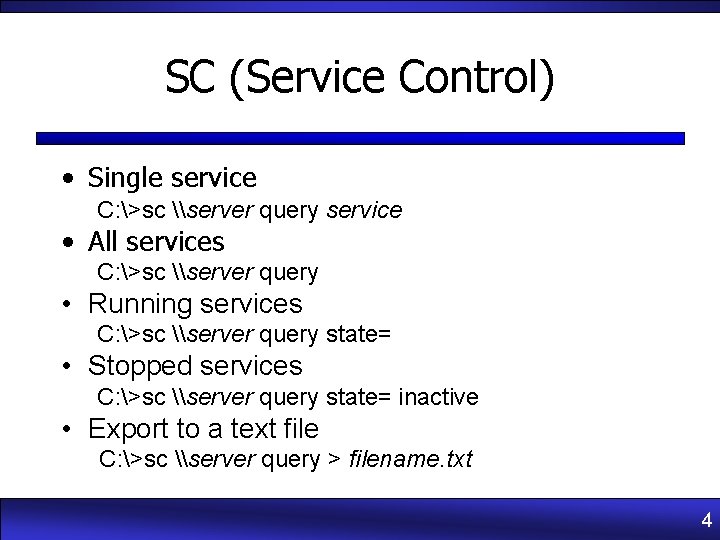
SC (Service Control) • Single service C: >sc \server query service • All services C: >sc \server query • Running services C: >sc \server query state= • Stopped services C: >sc \server query state= inactive • Export to a text file C: >sc \server query > filename. txt 4
![Reg C reg REG Operation Parameter List Operation QUERY ADD DELETE Reg C: >reg REG Operation [Parameter List] Operation [ QUERY | ADD | DELETE](https://slidetodoc.com/presentation_image/aea8a83514a2f0a3cf762235e7b7ff52/image-5.jpg)
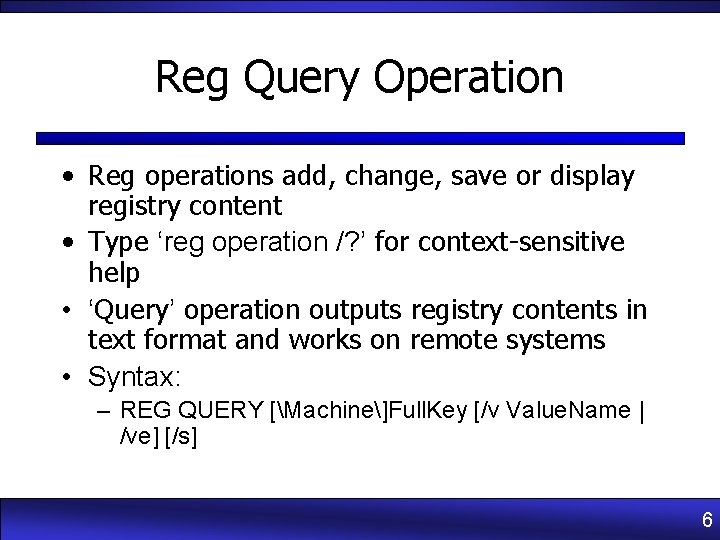
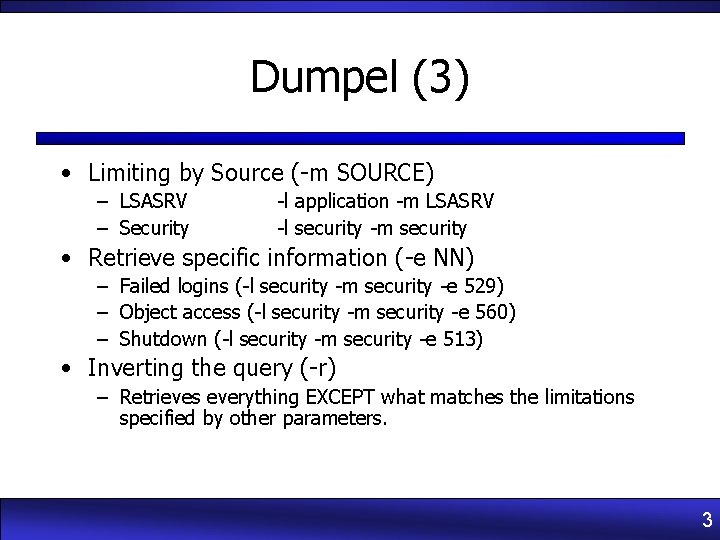
Reg C: >reg REG Operation [Parameter List] Operation [ QUERY | ADD | DELETE | COPY | SAVE | LOAD | UNLOAD | RESTORE | COMPARE | EXPORT | IMPORT ] Return Code: (Except of REG COMPARE) 0 - Successful 1 - Failed For help on a specific operation type: REG Operation /? 5
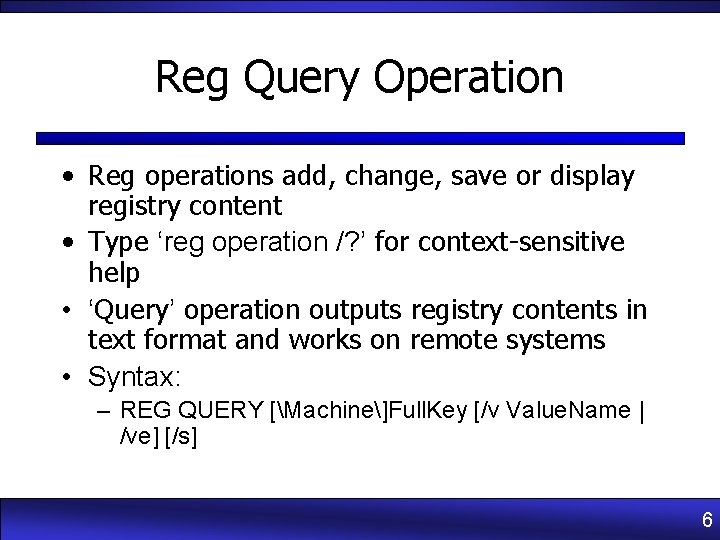
Reg Query Operation • Reg operations add, change, save or display registry content • Type ‘reg operation /? ’ for context-sensitive help • ‘Query’ operation outputs registry contents in text format and works on remote systems • Syntax: – REG QUERY [Machine]Full. Key [/v Value. Name | /ve] [/s] 6
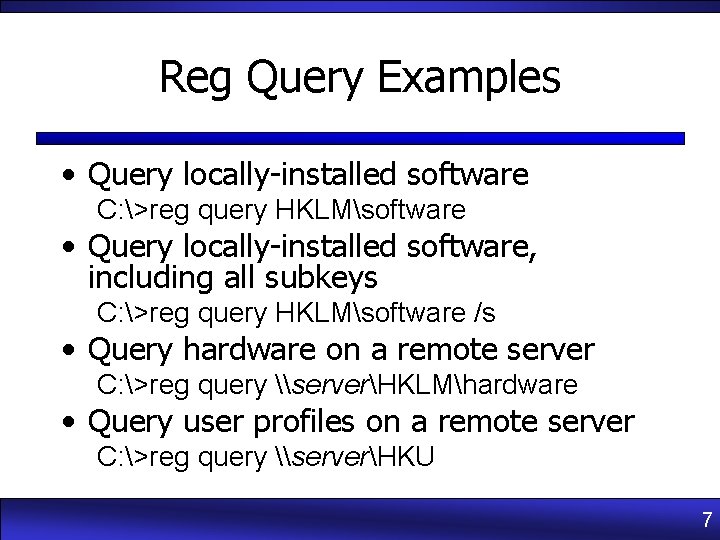
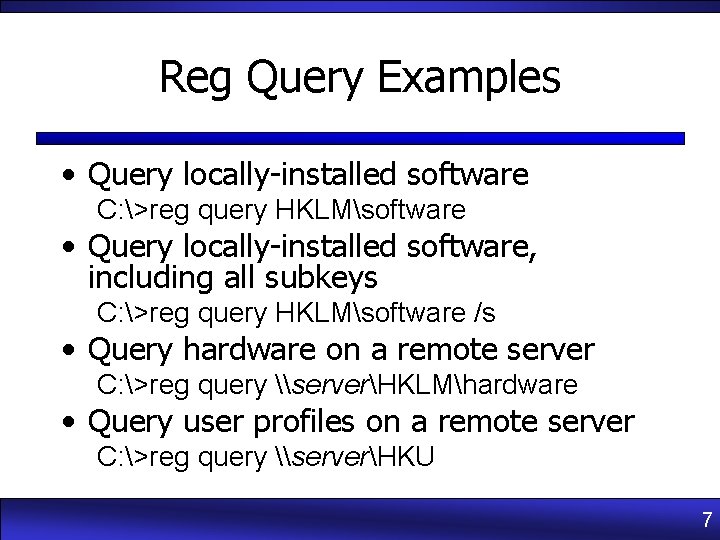
Reg Query Examples • Query locally-installed software C: >reg query HKLMsoftware • Query locally-installed software, including all subkeys C: >reg query HKLMsoftware /s • Query hardware on a remote server C: >reg query \serverHKLMhardware • Query user profiles on a remote server C: >reg query \serverHKU 7
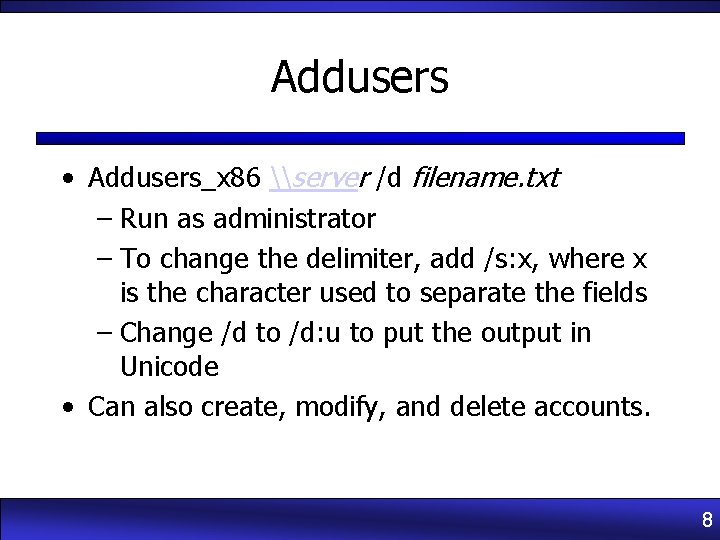
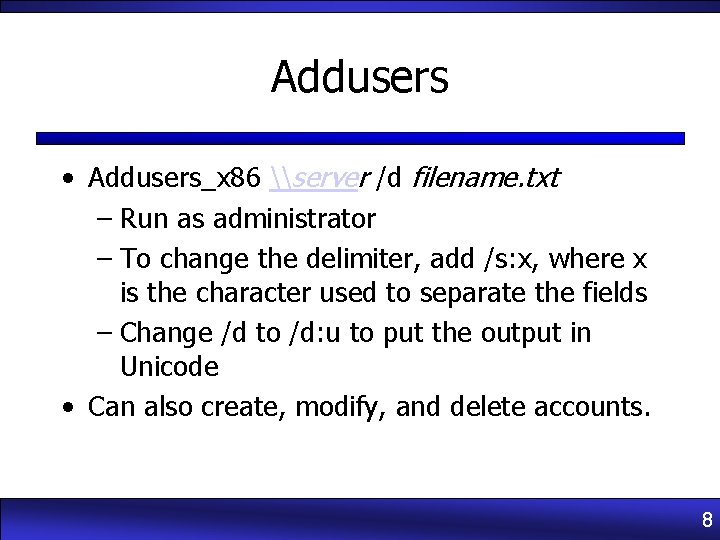
Addusers • Addusers_x 86 \server /d filename. txt – Run as administrator – To change the delimiter, add /s: x, where x is the character used to separate the fields – Change /d to /d: u to put the output in Unicode • Can also create, modify, and delete accounts. 8
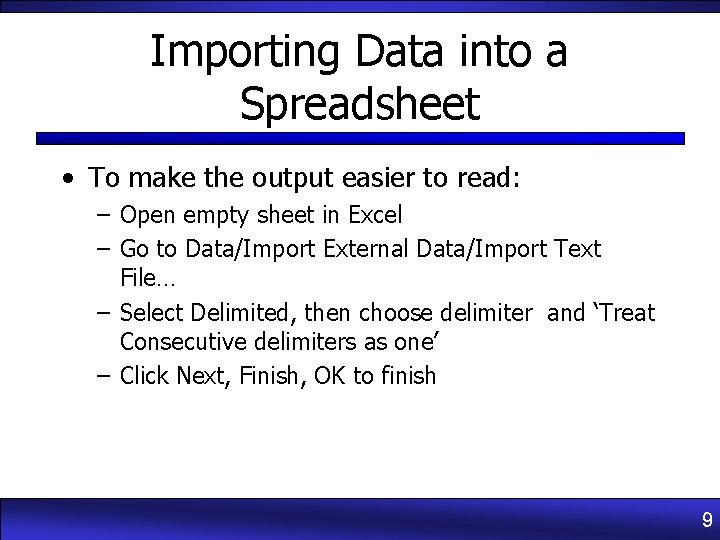
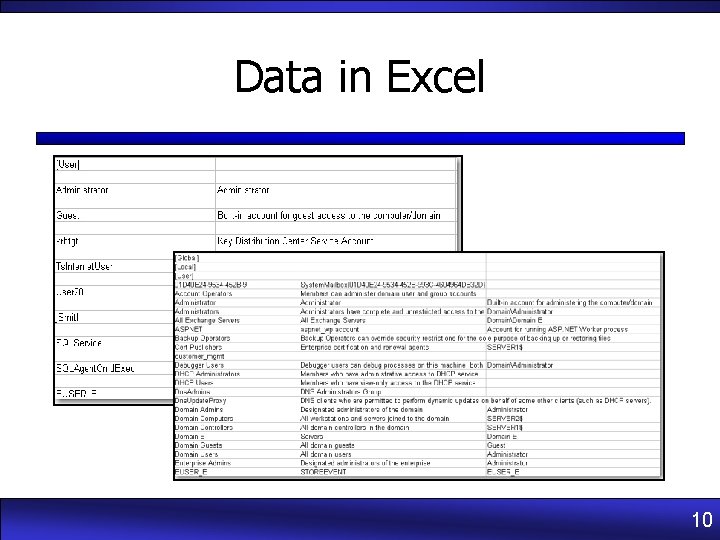
Importing Data into a Spreadsheet • To make the output easier to read: – Open empty sheet in Excel – Go to Data/Import External Data/Import Text File… – Select Delimited, then choose delimiter and ‘Treat Consecutive delimiters as one’ – Click Next, Finish, OK to finish 9
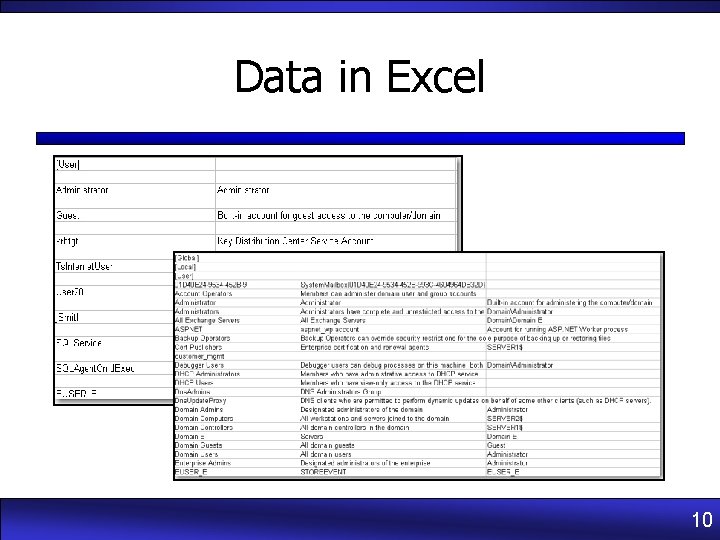
Data in Excel 10