DSD ESecurity DSD and ESecurity Tim Burmeister Information
DSD & E-Security DSD and E-Security Tim Burmeister Information Security Policy Defence Signals Directorate Tim. Burmeister@dsd. gov. au Information Security Group
E-security in Government Today • Risk Management • Greater prevalence of mixed environments • Service delivery vs. secure operating environments DSD & E-Security Information Security Group
DSD & E-Security The Future … Information Security Group
The Information Security Business • DSD has been doing it for over 50 years • But we no longer have a monopoly • Government used to provide its own solutions • Now everyone seems to be in on the act DSD & E-Security Information Security Group
Costs • Melissa: $80 million damage • I Love You: $10 billion damage • Software piracy: $ 7. 5 billion DSD & E-Security Information Security Group
Diverse Sources of ‘Attack’ • Chernobyl: June 1998, Taiwan • Melissa: March 1999, US • I love You: May 2000, The Philippines • Kournikova: Feb 2001, The Netherlands DSD & E-Security Information Security Group
Infrastructure Attacks • 1996 - 911 Services, Florida • 1997 - regional airport disruption, US • 1999 - threat to power supplies, Belgium DSD & E-Security Information Security Group
Computer Hacker Caused Sewage Overflows, Police Say An alleged computer hacker caused raw sewage to overflow on Queensland's Sunshine Coast by using radio transmissions to alter council sewage pump stations, police said today. The charges include stealing, computer hacking and using radio communications equipment without authority. Police will allege the man caused the overflows of sewage into Maroochy Shire waterways late last year and early this year using radio transmissions to alter council sewage pump stations. (Australian Associated Press, 23/5/2000) DSD & E-Security Information Security Group
More Coordinated Attacks DSD & E-Security The so-called Israeli/Palestinian Cyberwar Information Security Group
DSD & E-Security Infrastructure Attacks But what don’t we know about? Information Security Group
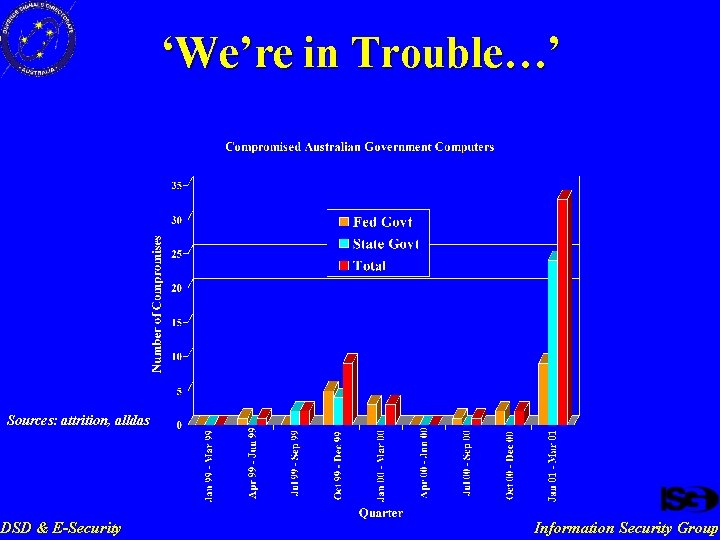
‘We’re in Trouble…’ Sources: attrition, alldas DSD & E-Security Information Security Group
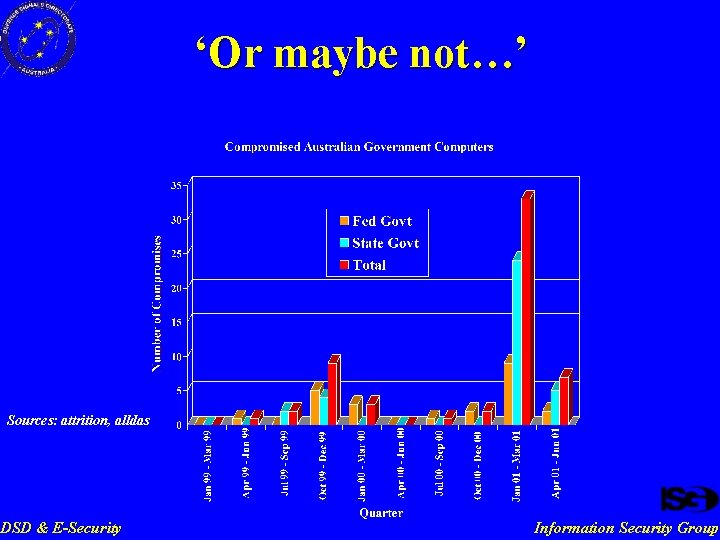
‘Or maybe not…’ Sources: attrition, alldas DSD & E-Security Information Security Group
DSD’s Functions From the 1986 government directive: — — Provide material, advice and assistance to Commonwealth Government Departments and authorities and the Defence Force on matters relevant to the security and integrity of official information, and or loss or compromise of which could adversely affect National Security; and Provide advice on request to Commonwealth Government Departments and authorities in relation to other sensitive official information unrelated to National Security. DSD & E-Security Information Security Group
Functions of DSD 7 … (c) to provide material, advice and other assistance to Commonwealth and State authorities on matters relating to the security and integrity of information that is processed, stored or communicated by electronic or similar means; and (d) to provide assistance to Commonwealth and State authorities in relation to cryptography and communications technologies. DSD & E-Security Intelligence Services Bill, 2001 Information Security Group
DSD and E-Security • The Australasian Information Security Evaluation Program (AISEP) • Advice and Assistance • Computer Network Vulnerability Team • Protection of the National Information Infrastructure DSD & E-Security Information Security Group
AISEP Evaluation • Evaluation is the thorough examination of a product’s security claims using a defined criteria. • Australia uses two evaluation criteria • — Common Criteria — ITSEC Common Criteria is the more recent evaluation criteria — DSD & E-Security Broad scope of mutual recognition internationally Information Security Group
Concept of Assurance • Assurance is: — — DSD & E-Security The degree of confidence in the claimed security features of a product or system. Defined by a Security Target. Information Security Group
The EPL • • DSD lists products that have completed evaluation on the EPL (certified) — Certification Reports available — Use in conjunction with the published Security Target Products that are ‘In-Evaluation’ are also listed on the EPL — Buyer beware — Can not provide the same level of assurance DSD & E-Security Information Security Group
And this is good because … • there are products available which are known to perform appropriately • not just for government use — DSD & E-Security use in the private sector can help to promote a more secure IT environment Information Security Group
Advice and Assistance • establishing IT security policy guidance on setting up IT networks • providing assistance to departments in securing their IT systems • performing internet gateway certifications for government • whole of Government infrastructure — Gatekeeper (a public key infrastructure) — Fedlink (secure network connecting all departments) DSD & E-Security Information Security Group
Computer Network Vulnerability Team • keep abreast of known vulnerabilities in software and equipment • research, test software and equipment for potential new problems • perform security audits on client's systems and networks • incident response capability DSD & E-Security Information Security Group
National Information Infrastructure • two broad roles — — • intelligence (threat and vulnerability assessments, other products) incident response, together with ASIO and the AFP incident reporting scheme for commonwealth government agencies — ISIDRAS currently — Onsecure Website, in concert with NOIE DSD & E-Security Information Security Group
Conclusion • Known threats and unknown threats • DSD helps government prepare itself for both DSD & E-Security Information Security Group
- Slides: 23