DPWSec The Devices Profile for Web Services Security
DPWSec: The Devices Profile for Web Services Security Sebastian Unger Dirk Timmermann University of Rostock, Germany Mu. SAMA DFG Graduate Programme
Agenda • Motivation • Basic Principles & Related Work • Requirements • Methodology • Features of DPWSec • Conclusion & Outlook 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 2
Agenda • Motivation • Basic Principles & Related Work • Requirements • Methodology • Features of DPWSec • Conclusion & Outlook 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 3
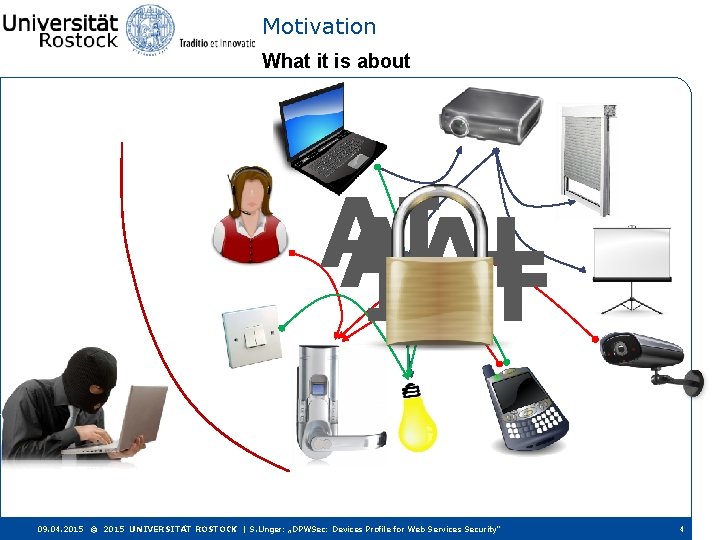
Motivation What it is about AI AAL Io. T 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 4
Motivation Real-Life Threats I Source: http: //www. forbes. com/sites/singularity/2012/12/06/yes-you-can-hack-a-pacemaker-and-other-medical -devices-too/ 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 5
Motivation Real-Life Threats II http: //www. spiegel. de/netzwelt/web/defcon-konferenz-in-las-vegas-hacker-lieben-internet-der-dinge-a-985733. html - Attackers love the Io. T - Once eradicated security flaws come back Botnet from fridges 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 6
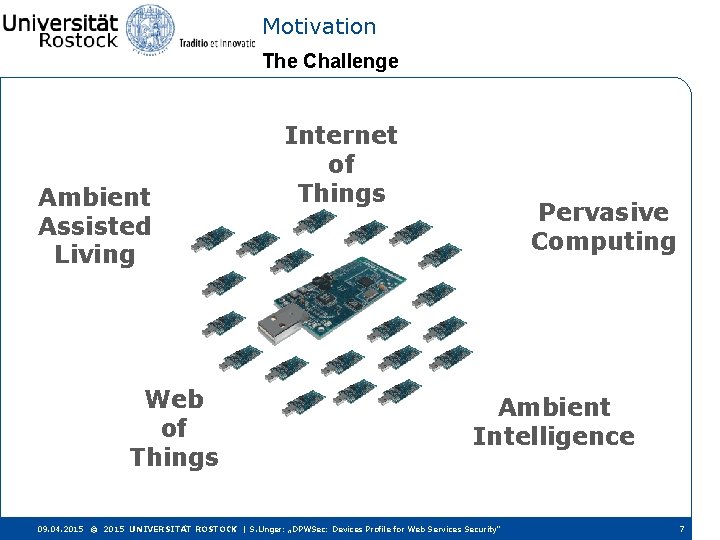
Motivation The Challenge Ambient Assisted Living Web of Things Internet of Things Pervasive Computing Ambient Intelligence 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 7
Motivation The Goal DPWS Device Profile for Web Services This work: Security scheme for DPWS based on Web Services Security Specification Suite Devices Profile for WS Security (DPWSec) This presentation: • Requirements analysis • Developed methodology • DPWSec’s functionality 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 8
Agenda • Motivation • Basic Principles & Related Work • Requirements • Methodology • Features of DPWSec • Conclusion & Outlook 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 9
Basic Principles & Related Work DPWS: the Devices Profile for Web Services DPWS is a communication standard for distributed embedded devices DPWS = Web Services for resource-constrained devices + Dynamic Discovery (bootstrap w/o central instance) + Eventing (asynchronous messaging) Originally designed for integration of e. g. printers into enterprise networks Found use in • Building automation • WSN • Industrial domain • Medical devices • Internet of things • Automotive 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 10
Basic Principles & Related Work Security in DPWS: Profile Mechanism Security in DPWS is covered by a flexible profile mechanism. A profile is a set of rules and assumptions, two devices agree on before communicating for the first time. Free choice of security profiles. 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 11
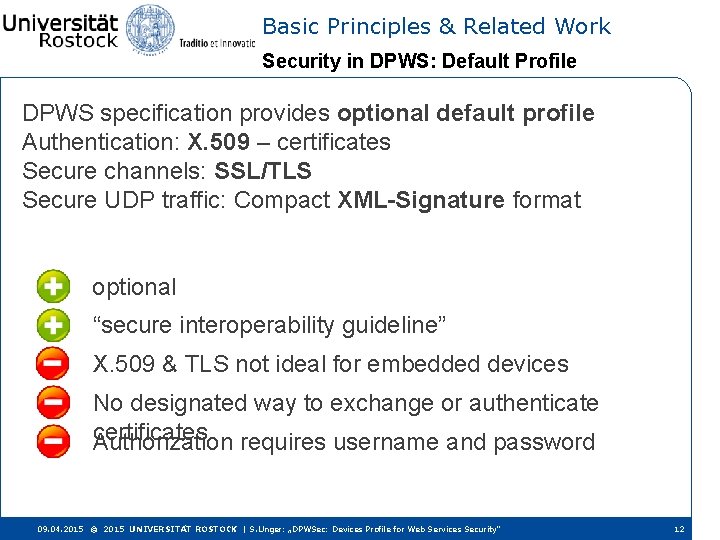
Basic Principles & Related Work Security in DPWS: Default Profile DPWS specification provides optional default profile Authentication: X. 509 – certificates Secure channels: SSL/TLS Secure UDP traffic: Compact XML-Signature format optional “secure interoperability guideline” X. 509 & TLS not ideal for embedded devices No designated way to exchange or authenticate certificates Authorization requires username and password 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 12
![Basic Principles & Related Work Security in DPWS: Related Work Muller et al: [1] Basic Principles & Related Work Security in DPWS: Related Work Muller et al: [1]](http://slidetodoc.com/presentation_image_h2/b66bd1c6e3057a2efb1dc97412c5e889/image-13.jpg)
Basic Principles & Related Work Security in DPWS: Related Work Muller et al: [1] Vulnerable against MITM-Attack Hernández et al: [2] Vulnerable against Replay-Attack Martínez et al: [3] Large office spaces X. 509 certificates, PKI Does not consider res. -constrained devices Unger et al: [4] Automotive, few devices X. 509 certificates Does not consider res. -constrained devices 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 13
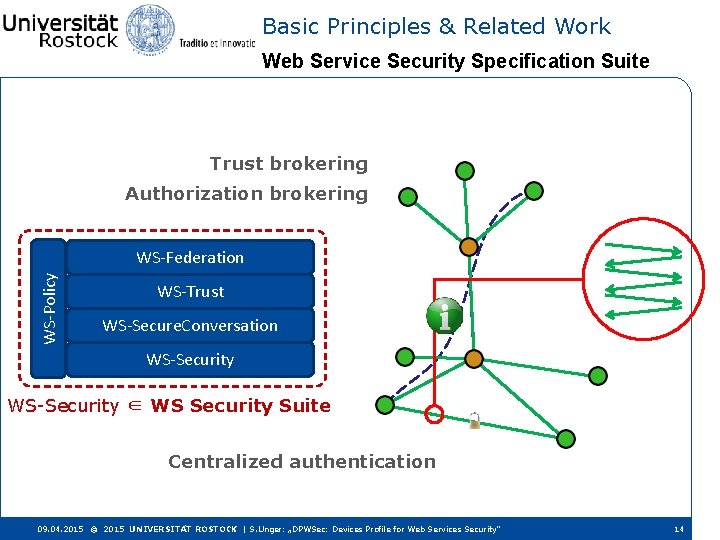
Basic Principles & Related Work Web Service Security Specification Suite Trust brokering Authorization brokering WS-Policy WS-Federation WS-Trust WS-Secure. Conversation WS-Security ∈ WS Security Suite Centralized authentication 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 14
Agenda • Motivation • Basic Principles & Related Work • Requirements • Methodology • Features of DPWSec • Conclusion & Outlook 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 15
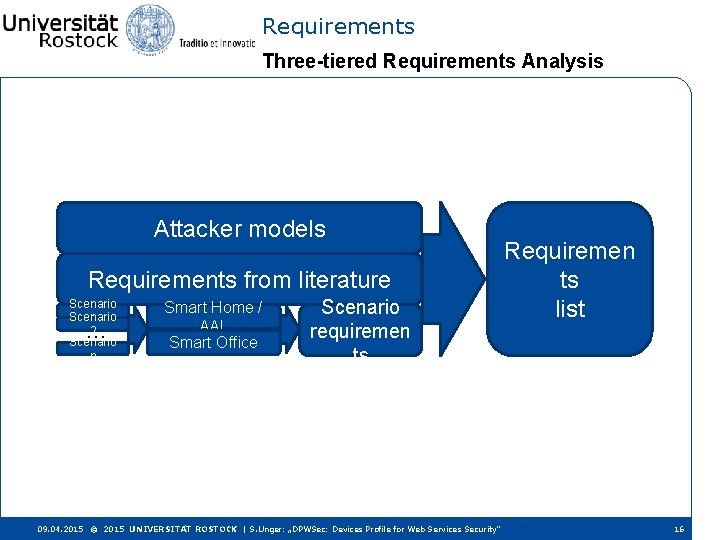
Requirements Three-tiered Requirements Analysis Attacker models Requirements from literature Scenario 1 2 Scenario n … Smart Home / AAL Smart Office Scenario requiremen ts 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ Requiremen ts list 16
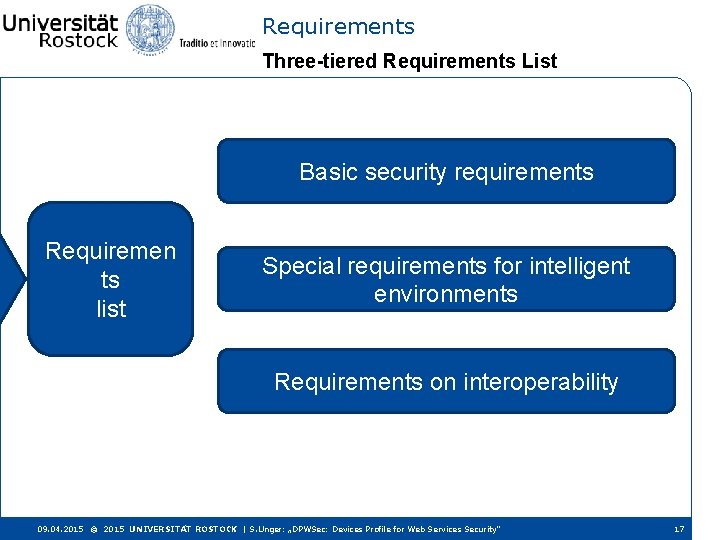
Requirements Three-tiered Requirements List Basic security requirements Requiremen ts list Special requirements for intelligent environments Requirements on interoperability 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 17
Requirements Basic security-related Requirements • DOLEV-YAO-attacker model • Secure external communication • Flexible support for different authorization concepts • Avoid single points of failures • Possibility to form organizational groups • Different levels of security • Secure continuous deployment • Scalable • Ease of use w/o impact on security • Support of secure data persistence 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 18
Requirements Basic security-related Requirements • DOLEV-YAO-attacker model • Secure external communication • Flexible support for different authorization concepts • Avoid single points of failures • Possibility to form organizational groups • Different levels of security • Secure continuous deployment • Scalable • Ease of use w/o impact on security • Support of secure data persistence 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 19
Requirements Special Requirements for intelligent Environments • Protect remaining network when member is lost / stolen • Focus on devices, not users • Consider heterogeneity of resources • Coordinated sign-out • Consider heterogeneity of user interfaces • Consider maintenance by experts and end users • Disburden constrained devices • Delegation of access rights 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 20
Requirements Special Requirements for intelligent Environments • Protect remaining network when member is lost / stolen • Focus on devices, not users • Consider heterogeneity of resources • Coordinated sign-out • Consider heterogeneity of user interfaces • Consider maintenance by experts and end users • Disburden constrained devices • Delegation of access rights 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 21
Requirements Special Requirements on Interoperability • Use a widely-deployed, well-accepted technology • Secure protocol interoperability • Secure manufacturer interoperability • Interoperable end-2 -end-security 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 22
Requirements Special Requirements on Interoperability • Use a widely-deployed, well-accepted technology • Secure protocol interoperability • Secure manufacturer interoperability • Interoperable end-2 -end-security 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 23
Agenda • Motivation • Basic Principles & Related Work • Requirements • Methodology • Features of DPWSec • Conclusion & Outlook 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 24
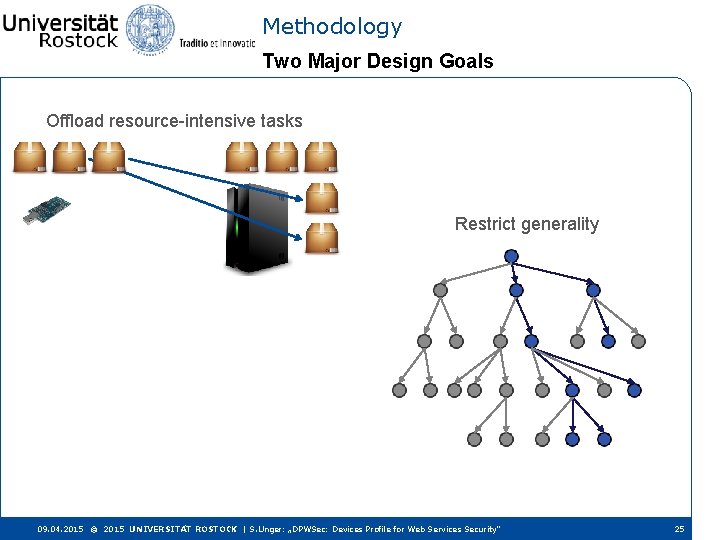
Methodology Two Major Design Goals Offload resource-intensive tasks Restrict generality 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 25
Methodology Offloading Efforts Tasks to be offloaded mostly concern secure connection establishment • Retrieving target’s metadata • Parsing policies and matching connection parameters • Authentication methods • Encryption algorithms • Support in direct authentication • Offer brokered authentication • Offer (semi)centralized authorization 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 26
Methodology Eliminating Specification Parts • Original specifications are very flexible • Offer lots of design choices After all: designed for desktop PCs and server machines Elimination of “unnecessary” or “unsuitable” parts: • Some parts are simply not necessary (according to requirements) • Other restrictions follow patterns: • Trade statelessness for simplicity • Respect communication model of DPWS • Respect architecture of DPWS 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 27
Agenda • Motivation • Basic Principles & Related Work • Requirements • Methodology • Features of DPWSec • Conclusion & Outlook 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 28
Features of DPWSec Compact Message Security Scheme • Securing single messages using a compact security scheme on message level proposed earlier [5] • Encrypt SOAP-Payload only, sign complete envelope • Performs similar to Record Protocol of TLS (no sever performance drawback) 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 29
Features of DPWSec Authentication Two authentication approaches • Direct authentication based on OOB PIN exchange • conduct authenticated Elliptic-Curve-Diffie-Hellman • Optionally employ MM-devices to translate OOB channels [6] • Brokered authentication between devices • Optionally offered by “strong” participants • Heavily disburdens “weak” as it relies on trust chains and does not require cryptographic hand shakes 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 30
Features of DPWSec Authorization • Authorization is special, as it requires no cryptography • Instead, it is about making decisions and communicating them DPWSec focuses on infrastructural part only How to ask for permission and how to deliver the decision Proposed a complementary authorization concept • Strong participants offer themselves as synchronous authorizers • If the can’t make a decision, they ask the user asynchronously using e. g. their smart phones 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 31
Agenda • Motivation • Basic Principles & Related Work • Requirements • Methodology • Features of DPWSec • Conclusion & Outlook 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 32
![Conclusion Evaluation It works. Prototype implementation available open source [7] DOLEV-YAO-attacker model Consider heterogeneity Conclusion Evaluation It works. Prototype implementation available open source [7] DOLEV-YAO-attacker model Consider heterogeneity](http://slidetodoc.com/presentation_image_h2/b66bd1c6e3057a2efb1dc97412c5e889/image-33.jpg)
Conclusion Evaluation It works. Prototype implementation available open source [7] DOLEV-YAO-attacker model Consider heterogeneity of resources Secure external communication Focus on devices, not users Flexible support for different authorization Protect remaining network when member is concepts lost / stolen Avoid single points of failures Disburden constrained devices Possibility to form organizational groups Coordinated sign-out Different Levels of Security Consider maintenance by experts and end Secure continuous deployment users Scalable Consider heterogeneity of user interfaces Use a widely-deployed, well-accepted technology Delegation of Access rights Secure protocol interoperability Ease of use w/o impact on security Support of secure data persistence Secure manufacturer interoperability Interoperable end-2 -end-security Every met. Almostrequirement every requirement 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 33
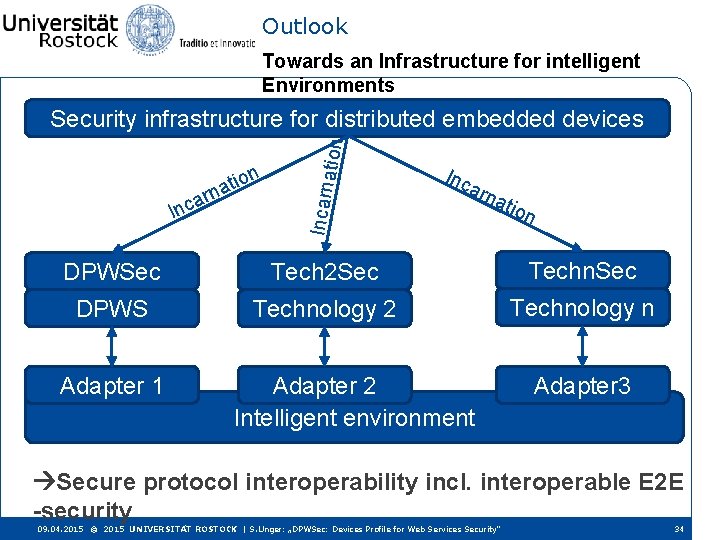
Outlook Towards an Infrastructure for intelligent Environments a Incarn n tio a n r ation Security infrastructure for distributed embedded devices Inc arn atio n DPWSec Tech 2 Sec Techn. Sec DPWS Technology 2 Technology n Adapter 1 Adapter 2 Intelligent environment Adapter 3 Secure protocol interoperability incl. interoperable E 2 E -security 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 34
Future Work Adapt to second Base Technology Near future: Second technology next to DPWS Isolate requirements Actually port DPWSec Far future: Research secure protocol interoperability Employ adapter / translator concept Research emerging issues esp. regarding interoperable E 2 E-security 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 35
![Bibliography [1] A. Muller et al. , “An assisted device registration and service access Bibliography [1] A. Muller et al. , “An assisted device registration and service access](http://slidetodoc.com/presentation_image_h2/b66bd1c6e3057a2efb1dc97412c5e889/image-36.jpg)
Bibliography [1] A. Muller et al. , “An assisted device registration and service access system for future home networks, ” in Wireless Days (WD), 2009 2 nd. IFIP, Dezember 2009, p. 5. [2] V. Hernández et al. , “Security Framework for DPWS Compliant Devices, ” Third International Conference on Emerging Security Information, Systems and Technologies, 2009. [3] J. -F. Martínez et al. , “A security architectural approach for DPWS-based devices, ” Coll. ECTe. R Iberoamérica, 2008. [4] S. Unger et al. , “Extending the devices profile for web services for secure mobile device communication, ” in Internet of Things Conference - TIo. PTS Workshop, 2010. [5] S. Unger, S. Pfeiffer, and D. Timmermann, “Dethroning transport layer security in the embedded world, ” in 5 th International Conference on New Technologies, Mobility and Security (NTMS), 2012. [6] S. Unger and D. Timmermann, “Bridging the gap for authentication in smart environments, ” in Computers and Communications (IEEE ISCC 2014), 19 th IEEE Symposium on, Funchal, [7] https: //gitlab. amd. e-technik. uni-rostock. de/sebastian. unger/ws 4 d-mobile-authenticator/wikis/home
Thank you! Questions? Thank you very much for your attention! Any questions? Sebastian Unger Institute for Applied Microelectronics and Computer Engineering, University of Rostock, Germany sebastian. unger@uni-rostock. de 09. 04. 2015 © 2015 UNIVERSITÄT ROSTOCK | S. Unger: „DPWSec: Devices Profile for Web Services Security“ 37
- Slides: 37