Doctoral Dissertation Research Proposal Anand Patwardhan e Biquity
Doctoral Dissertation Research Proposal Anand Patwardhan e. Biquity Research Group CSEE Dept. , UMBC Ph. D. Committee Dr. Anupam Joshi (Advisor and Chair), UMBC Dr. Timothy Finin, UMBC Dr. Yelena Yesha, UMBC Dr. Zary Segall, UMBC Dr. Bhavani Thuraisingham, UT Dallas Dr. Tom Karygiannis, NIST © Anand Patwardhan
Education • M. S. in Computer Science and Engineering, Oregon Graduate Institute, March 2002. (GPA 3. 74/4. 00) • B. E. in Computer Engineering, University of Pune, August 2000. (First Class with Distinction, all years) Publications • “Secure Routing and Intrusion Detection in Ad Hoc Networks, ” Proceedings of the 3 rd International Conference on Pervasive Computing and Communications, March 2005. • “Enforcing Policies in Pervasive Environments, ” Proceedings of the 1 st International Conference on Mobile and Ubiquitous Systems: Networking and Services, August 2004. © Anand Patwardhan
Outline • • © Anand Patwardhan Background Motivation Proposed Approach Research Issues Preliminary Work Timeline Summary
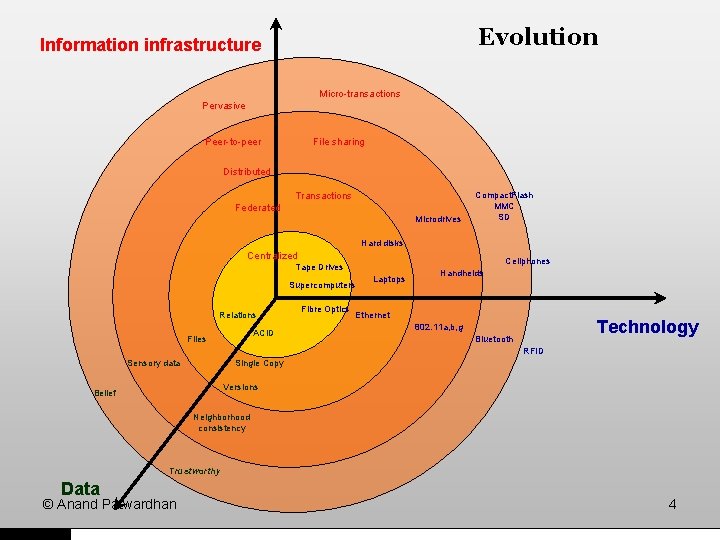
Evolution Information infrastructure Micro-transactions Pervasive Peer-to-peer File sharing Distributed Transactions Federated Microdrives Compact. Flash MMC SD Hard disks Centralized Cellphones Tape Drives Supercomputers Relations ACID Files Fibre Optics Laptops Handhelds Ethernet Technology 802. 11 a, b, g Bluetooth RFID Sensory data Single Copy Versions Belief Neighborhood consistency Trustworthy Data © Anand Patwardhan 4
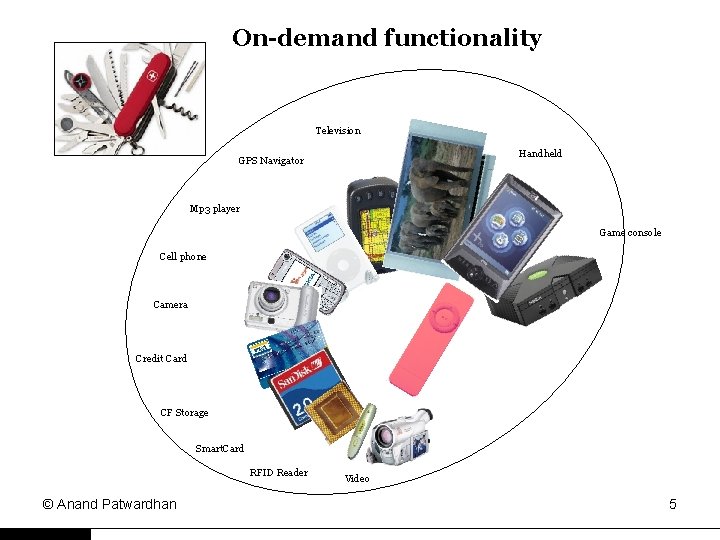
On-demand functionality Television Handheld GPS Navigator Mp 3 player Game console Cell phone Camera Credit Card CF Storage Smart. Card RFID Reader © Anand Patwardhan Video 5
Motivation • Portability and mobility – Wireless connectivity – Small form factors • Autonomy and collaboration – Personal goals – Collective goals © Anand Patwardhan • Abundant storage – Services To-Go – Reputation management • Evolving application scenarios – Omnipresent services – Peer-to-peer relations – Pervasive (distributed) trust 6
Research Challenges • Security for resources – Malicious behavior (Activity monitoring) – Misuse (Resource protection) – Response/recourse (Accountability) • Trust in other resources – Dependence on recommendations (Identities and Reputations) – Reliability of information © Anand Patwardhan
Challenges (contd. ) • Privacy – Anonymity (Surveillance) • Information sources – Local, distributed, and serendipitous – Response latency • Storage Management – Buffers and pro-active caching – Updates and consistency © Anand Patwardhan
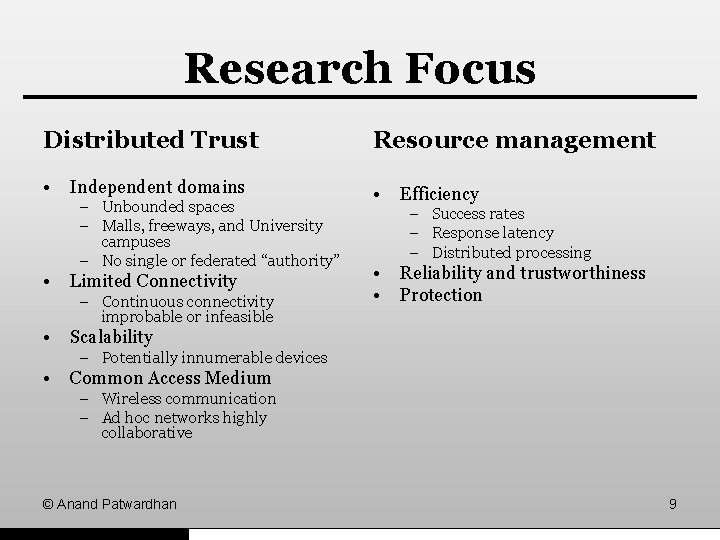
Research Focus Distributed Trust Resource management • • Independent domains – Unbounded spaces – Malls, freeways, and University campuses – No single or federated “authority” • Limited Connectivity – Continuous connectivity improbable or infeasible • Efficiency – Success rates – Response latency – Distributed processing • • Reliability and trustworthiness Protection Scalability – Potentially innumerable devices • Common Access Medium – Wireless communication – Ad hoc networks highly collaborative © Anand Patwardhan 9
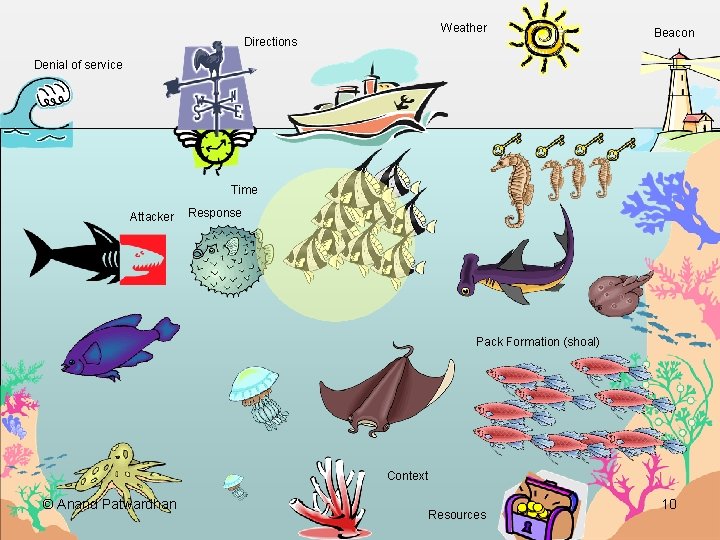
Weather Directions Beacon Denial of service Time Attacker Response Pack Formation (shoal) Context © Anand Patwardhan Resources 10
Thesis Statement • Pervasive trust can be achieved by collaboration and reputation management. • Pack formations will enable reliable and trustworthy Resource Management Frameworks for Pervasive Environments. © Anand Patwardhan
![Proposed Approach • Pervasive Trust – Persistent Identities • SUCV [Mo 02], CGA[Au 04] Proposed Approach • Pervasive Trust – Persistent Identities • SUCV [Mo 02], CGA[Au 04]](http://slidetodoc.com/presentation_image_h2/4ee88d797e2ba47de43828a91d787f5a/image-12.jpg)
Proposed Approach • Pervasive Trust – Persistent Identities • SUCV [Mo 02], CGA[Au 04] – Reputations • Resource management – Pack formation – Search © Anand Patwardhan • Activity monitoring – Recommendations – Accusations [Pa 05] • Proactive and reactionary measures – Dominions – Immediate response – Exclusion 12
![Related Work • Mo. GATU, UMBC [Pe 02] – Profile based data management – Related Work • Mo. GATU, UMBC [Pe 02] – Profile based data management –](http://slidetodoc.com/presentation_image_h2/4ee88d797e2ba47de43828a91d787f5a/image-13.jpg)
Related Work • Mo. GATU, UMBC [Pe 02] – Profile based data management – Beliefs, Desires, and Intentions • Telegraph Project, UCB [Ch 02] – Streaming data – Queries over streaming data • PGP – Distributed trust – Key management © Anand Patwardhan
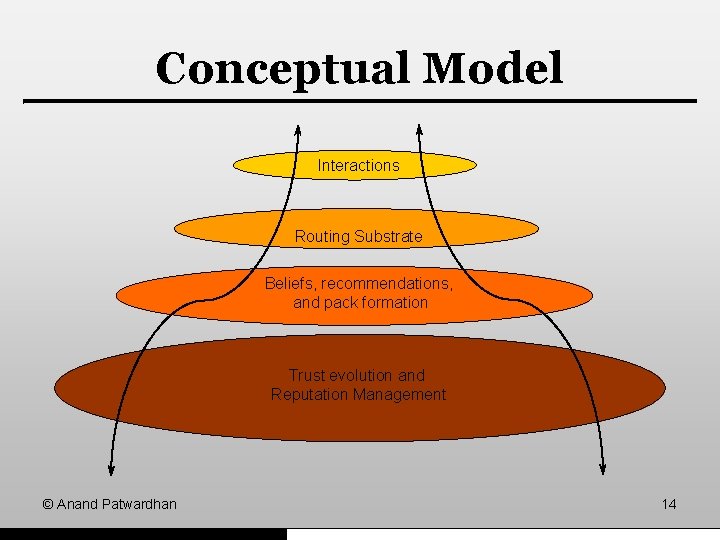
Conceptual Model Interactions Routing Substrate Beliefs, recommendations, and pack formation Trust evolution and Reputation Management © Anand Patwardhan 14
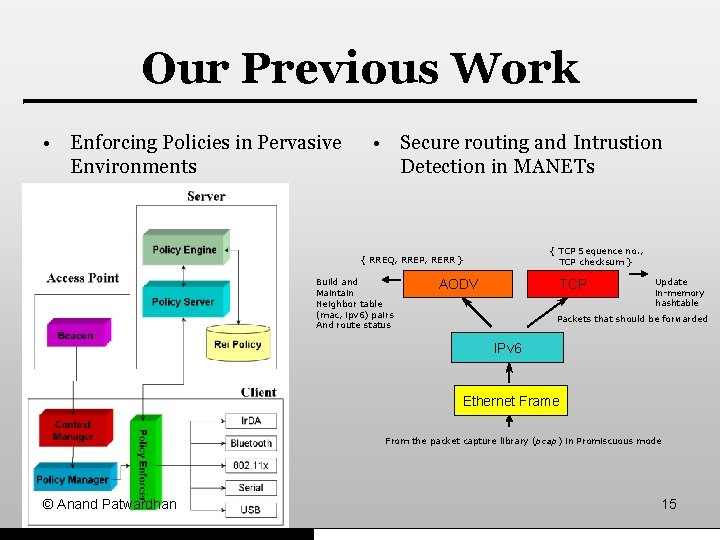
Our Previous Work • Enforcing Policies in Pervasive Environments • Secure routing and Intrustion Detection in MANETs { TCP Sequence no. , TCP checksum } { RREQ, RREP, RERR } Build and Maintain Neighbor table (mac, ipv 6) pairs And route status AODV TCP Update in-memory hashtable Packets that should be forwarded IPv 6 Ethernet Frame From the packet capture library (pcap) in Promiscuous mode © Anand Patwardhan 15
Trust Evolution and Reputation Management • Mechanisms – Activity monitoring – Recommendations – Social networks – Context • Benefits – Protect connectivity (routes) – Reliability and accuracy of data © Anand Patwardhan
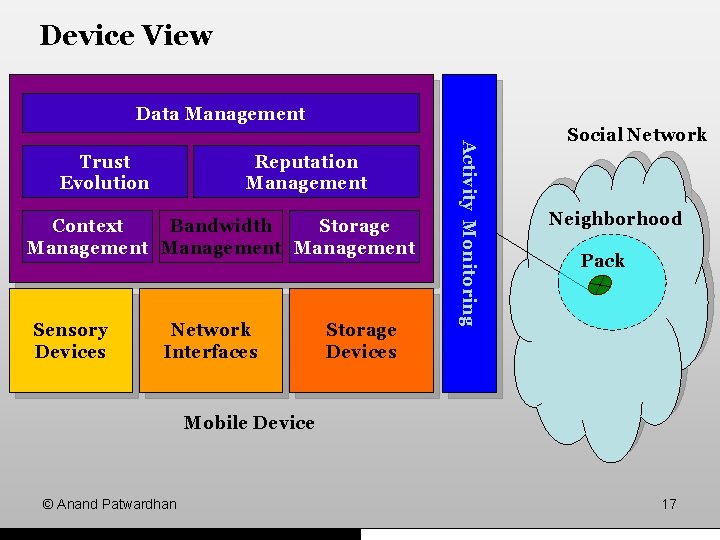
Device View Data Management Reputation Management Context Bandwidth Storage Management Sensory Devices Network Interfaces Storage Devices Activity Monitoring Trust Evolution Social Network Neighborhood Pack Mobile Device © Anand Patwardhan 17
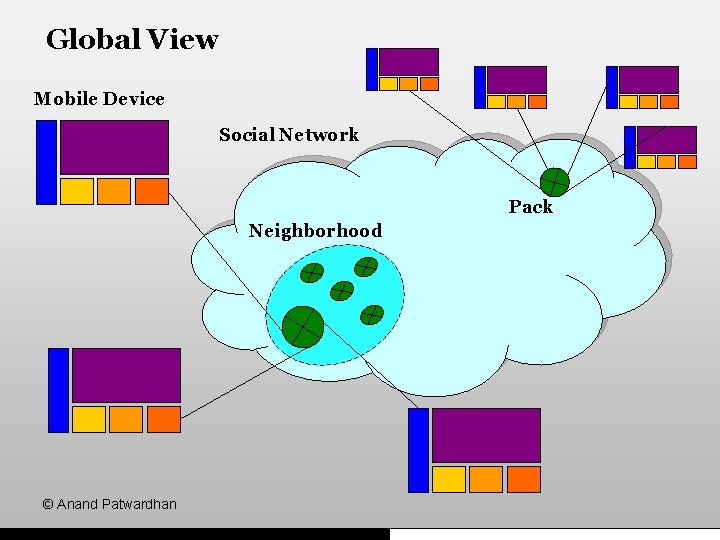
Global View Mobile Device Social Network Pack Neighborhood © Anand Patwardhan
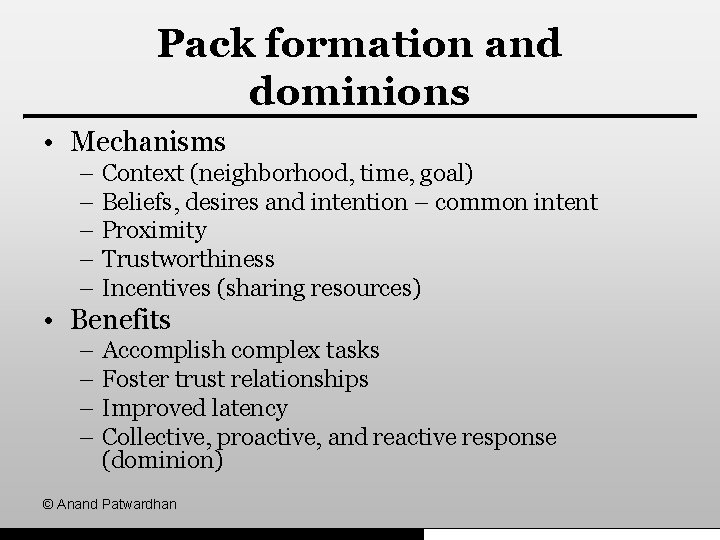
Pack formation and dominions • Mechanisms – Context (neighborhood, time, goal) – Beliefs, desires and intention – common intent – Proximity – Trustworthiness – Incentives (sharing resources) • Benefits – Accomplish complex tasks – Foster trust relationships – Improved latency – Collective, proactive, and reactive response (dominion) © Anand Patwardhan
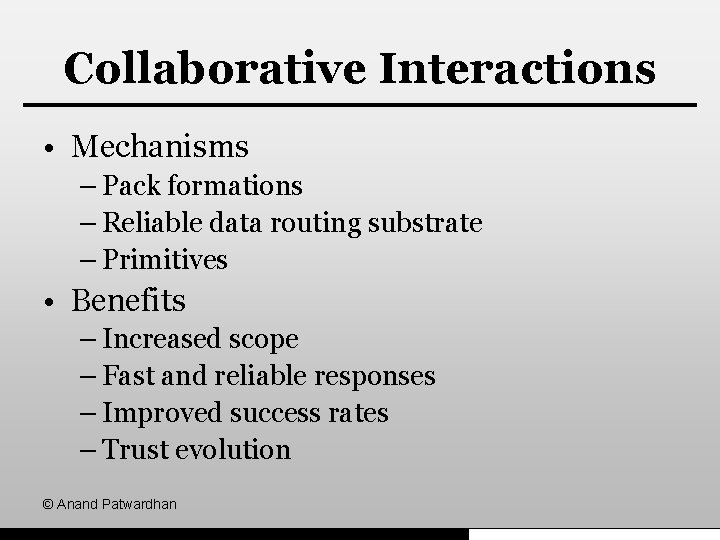
Collaborative Interactions • Mechanisms – Pack formations – Reliable data routing substrate – Primitives • Benefits – Increased scope – Fast and reliable responses – Improved success rates – Trust evolution © Anand Patwardhan
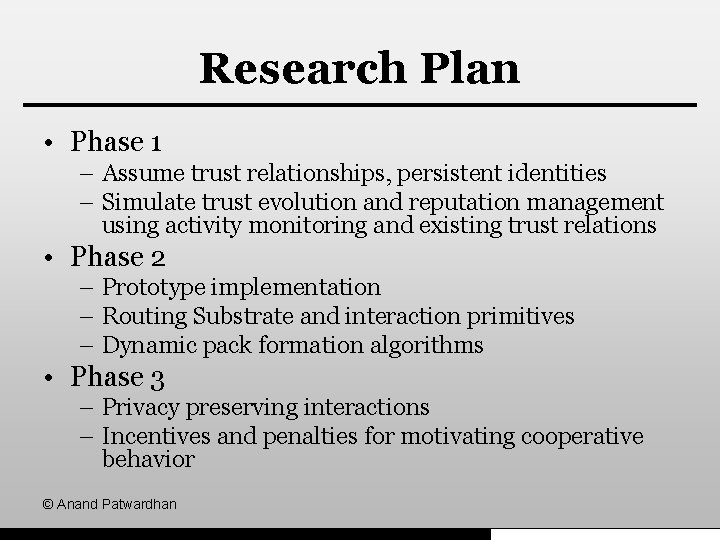
Research Plan • Phase 1 – Assume trust relationships, persistent identities – Simulate trust evolution and reputation management using activity monitoring and existing trust relations • Phase 2 – Prototype implementation – Routing Substrate and interaction primitives – Dynamic pack formation algorithms • Phase 3 – Privacy preserving interactions – Incentives and penalties for motivating cooperative behavior © Anand Patwardhan
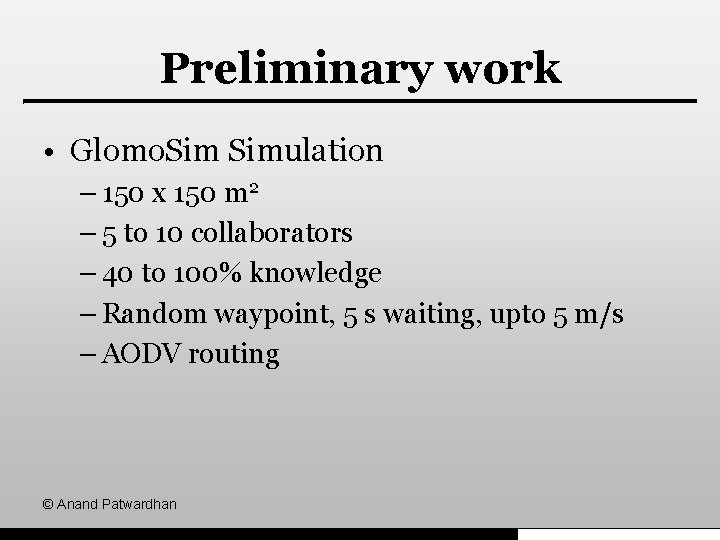
Preliminary work • Glomo. Simulation – 150 x 150 m 2 – 5 to 10 collaborators – 40 to 100% knowledge – Random waypoint, 5 s waiting, upto 5 m/s – AODV routing © Anand Patwardhan
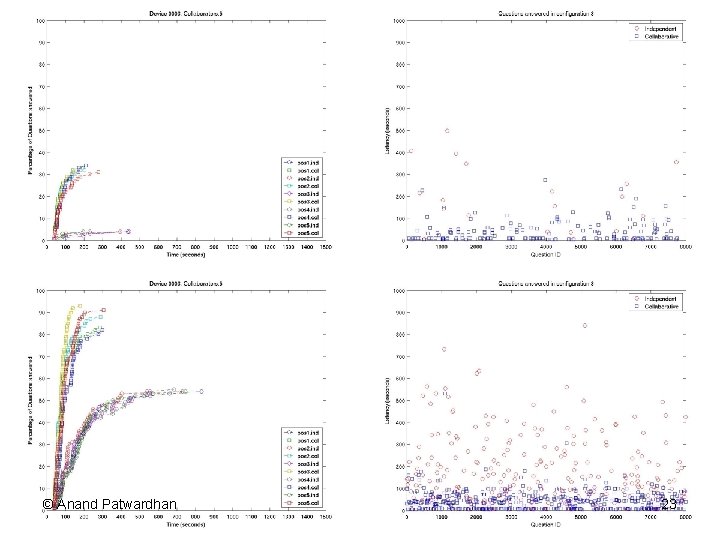
© Anand Patwardhan 23
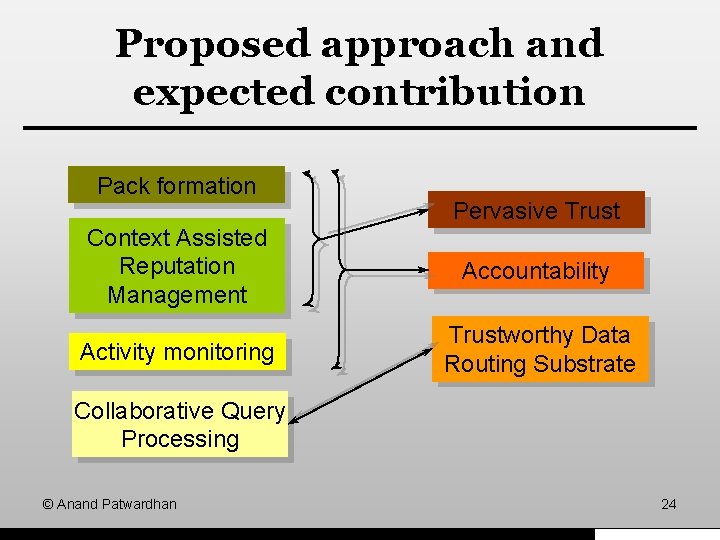
Proposed approach and expected contribution Pack formation Pervasive Trust Context Assisted Reputation Management Accountability Activity monitoring Trustworthy Data Routing Substrate Collaborative Query Processing © Anand Patwardhan 24
Expected Contributions • Context assisted trust evolution • Pack formation – Primitives – Algorithms • Reputation management system • Trustworthy data routing substrate • Collaborative query processing framework © Anand Patwardhan
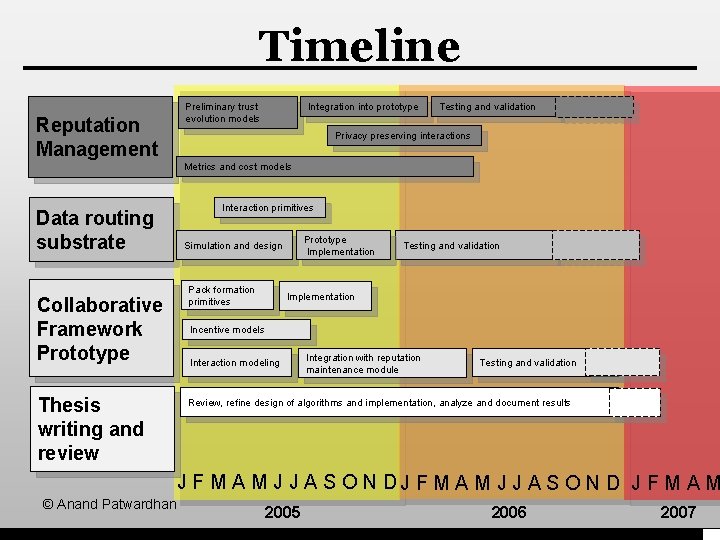
Timeline Reputation Management Preliminary trust evolution models Integration into prototype Testing and validation Privacy preserving interactions Metrics and cost models Data routing substrate Collaborative Framework Prototype Thesis writing and review Interaction primitives Prototype Implementation Simulation and design Pack formation primitives Testing and validation Implementation Incentive models Interaction modeling Integration with reputation maintenance module Testing and validation Review, refine design of algorithms and implementation, analyze and document results J F M A M J J A S O N D J F M A M © Anand Patwardhan 2005 2006 2007
Summary • Pervasive trust – Distributed – Autonomy • Reputation management – Social networks and contexts – Pack formation – Activity monitoring • Data routing substrate – Reliable and trustworthy data © Anand Patwardhan
![References [Mo 02] G. Montenegro and C. Castelluccia. Statistically Unique and Cryptographically Verifiable(SUCV) identifiers References [Mo 02] G. Montenegro and C. Castelluccia. Statistically Unique and Cryptographically Verifiable(SUCV) identifiers](http://slidetodoc.com/presentation_image_h2/4ee88d797e2ba47de43828a91d787f5a/image-28.jpg)
References [Mo 02] G. Montenegro and C. Castelluccia. Statistically Unique and Cryptographically Verifiable(SUCV) identifiers and addresses. citeseer. ist. psu. edu/montenegro 02 statistically. html, 2002. [Au 04] T. Aura. Internet Draft: Cryptographically Generated Addresses (CGA). http: //www. ietf. org/proceedings/04 mar/I-D/draft-ietf-send-cga-05. txt, February 2004. [Pa 05] A. Patwardhan, J. Parker, A. Joshi, M. Iorga, and T. Karygiannis. Secure Routing and Intrusion Detection in Ad Hoc Networks. In Proceedings of the 3 rd International Conference on Pervasive Computing and Communications (to appear), Kauai Island, Hawaii, March 2005. [Pe 01] F. Perich. Mo. GATU: Data Management in Pervasive Computing Enviroments. http: //mogatu. umbc. edu/, 2001 -2005. [Ch 02] S. Chandrasekaran and M. J. Franklin. Streaming Queries over Streaming Data. In Proceedings of the 28 th VLDB conference, 2002. © Anand Patwardhan
- Slides: 28