Distributed Honeynet System Data Capture and Analysis CDAC
Distributed Honeynet System Data Capture and Analysis C-DAC Mohali
Overview � Honeynet/Honeypot Technology ◦ Honeypot/Honeynet Backgroud ◦ Type of Honeypots ◦ Deployment of Honeypots � Data Collection � Data Control � Data Analysis
Honeypot/Honeynet concepts ◦ A honeypot is an information system resource whose value lies in unauthorized or illicit use of that resource ◦ Has no production value, anything going to or from a honeypot is likely a probe, attack or compromise ◦ A highly controlled network where every packet entering or leaving the honeypot system and related system activities are monitored, captured analyzed. ◦ Primary value to most organizations is information”
Advantages � Fidelity – Information of high value � Reduced false positives � Reduced false negatives � Simple concept � Not resource intensive
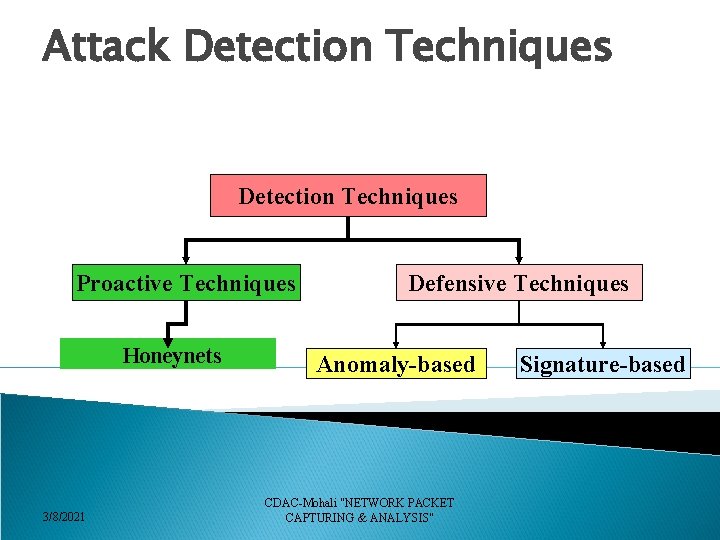
Attack Detection Techniques Proactive Techniques Honeynets 3/8/2021 Defensive Techniques Anomaly-based CDAC-Mohali "NETWORK PACKET CAPTURING & ANALYSIS" Signature-based
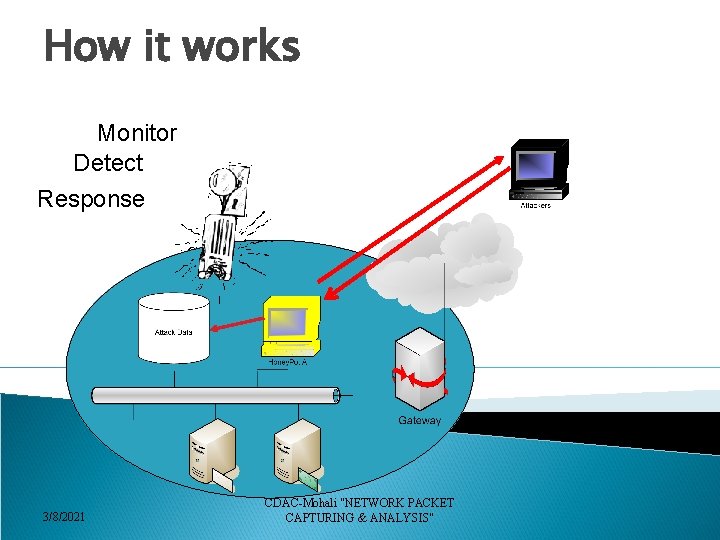
How it works Monitor Detect Response 3/8/2021 CDAC-Mohali "NETWORK PACKET CAPTURING & ANALYSIS"
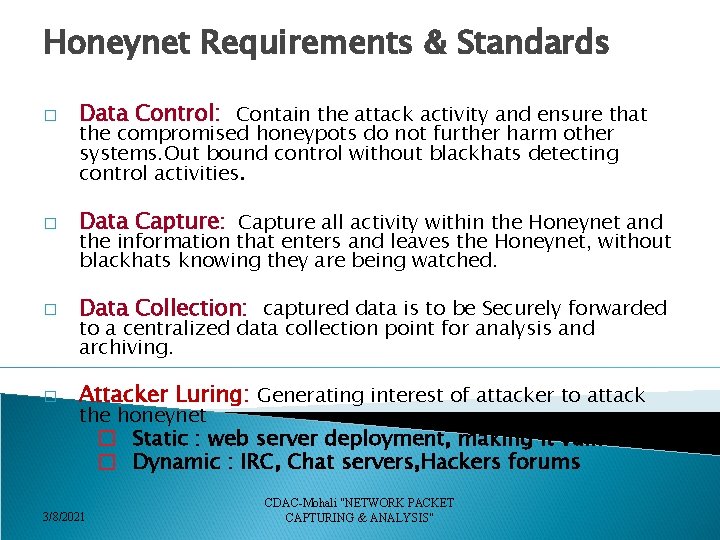
Honeynet Requirements & Standards � Data Control: Contain the attack activity and ensure that � Data Capture: Capture all activity within the Honeynet and � Data Collection: captured data is to be Securely forwarded � Attacker Luring: Generating interest of attacker to attack the compromised honeypots do not further harm other systems. Out bound control without blackhats detecting control activities. the information that enters and leaves the Honeynet, without blackhats knowing they are being watched. to a centralized data collection point for analysis and archiving. the honeynet � Static : web server deployment, making it vulnerable � Dynamic : IRC, Chat servers, Hackers forums 3/8/2021 CDAC-Mohali "NETWORK PACKET CAPTURING & ANALYSIS"
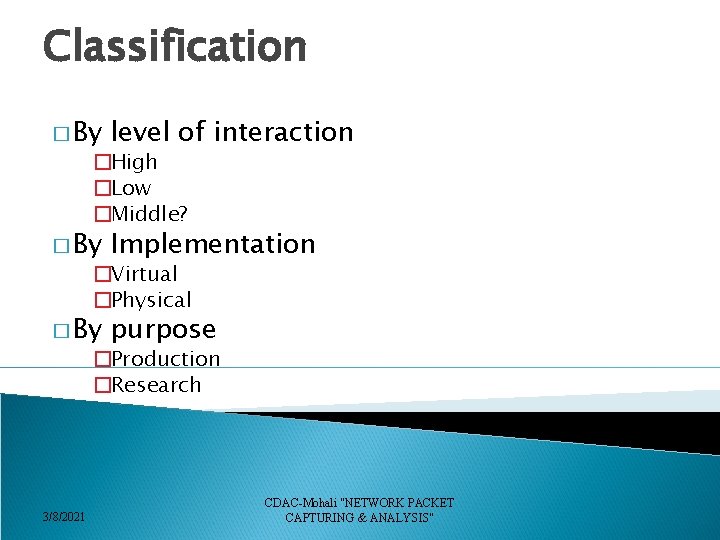
Classification � By level of interaction � By Implementation � By purpose �High �Low �Middle? �Virtual �Physical �Production �Research 3/8/2021 CDAC-Mohali "NETWORK PACKET CAPTURING & ANALYSIS"
Types of Honeypots � Low-interaction ◦ Emulates services and operating systems. ◦ Easy to deploy, minimal risk ◦ Captures limited information � High Interaction ◦ Provide real operating systems and services, no emulation. ◦ Complex to deploy, greater risk. ◦ Capture extensive information.
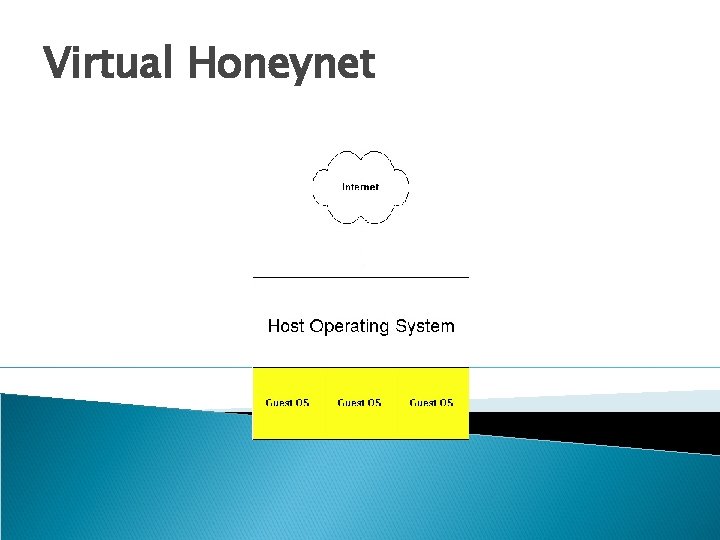
Virtual Honeynet
What Honeynet Achieves � Diverts attacker’s attention from the real network in a way that the main information resources are not compromised. � Captures samples of new viruses and worms for future study � Helps to build attacker’s profile in order to identify their preferred attack targets, methods. 3/8/2021 CDAC-Mohali "NETWORK PACKET CAPTURING & ANALYSIS"
What value Honeynet adds � Prevention of attacks �through deception and deterrence � Detection of attacks �By acting as a alarm � Response of attacks �By collecting data and evidence of an attacker’s activity 3/8/2021 CDAC-Mohali "NETWORK PACKET CAPTURING & ANALYSIS"
GEN III A highly controlled network where every packet entering or leaving is monitored, captured, and analyzed. v. Data Capture v. Data Control v. Data Analysis 3/8/2021 CDAC-Mohali "NETWORK PACKET CAPTURING & ANALYSIS"
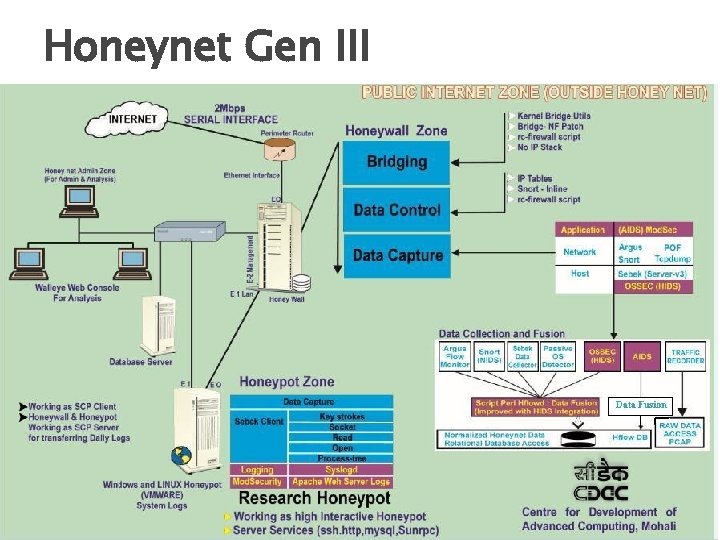
Honeynet Gen III 3/8/2021 CDAC-Mohali "NETWORK PACKET CAPTURING & ANALYSIS"
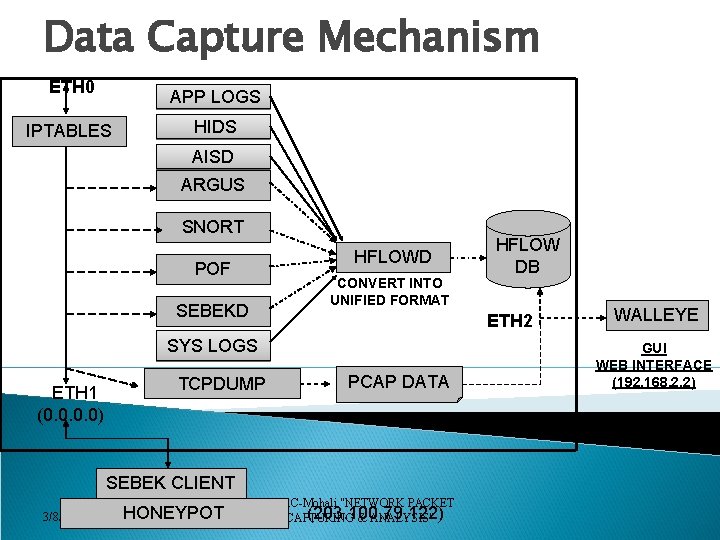
Data Capture Mechanism ETH 0 APP LOGS IPTABLES HIDS AISD ARGUS SNORT HFLOWD POF CONVERT INTO UNIFIED FORMAT SEBEKD ETH 2 SYS LOGS ETH 1 (0. 0) TCPDUMP PCAP DATA SEBEK CLIENT 3/8/2021 HONEYPOT HFLOW DB CDAC-Mohali "NETWORK PACKET (203. 100. 79. 122) CAPTURING & ANALYSIS" WALLEYE GUI WEB INTERFACE (192. 168. 2. 2)
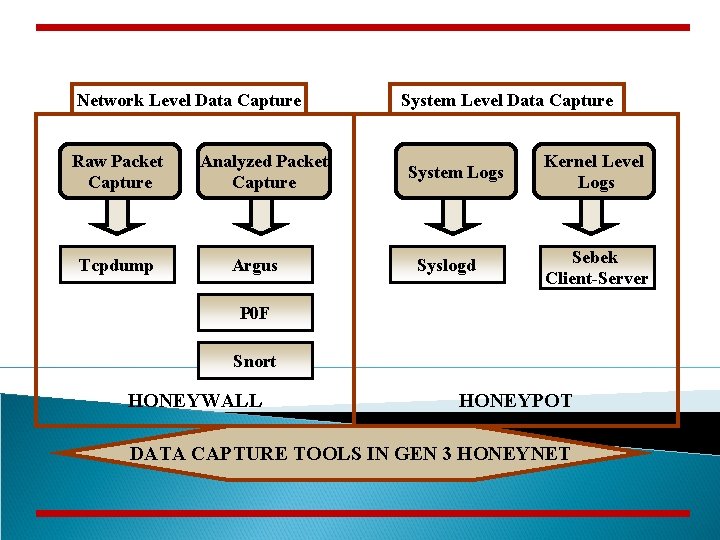
Network Level Data Capture Raw Packet Capture Tcpdump Analyzed Packet Capture Argus System Level Data Capture System Logs Syslogd Kernel Level Logs Sebek Client-Server P 0 F Snort HONEYWALL HONEYPOT DATA CAPTURE TOOLS IN GEN 3 HONEYNET
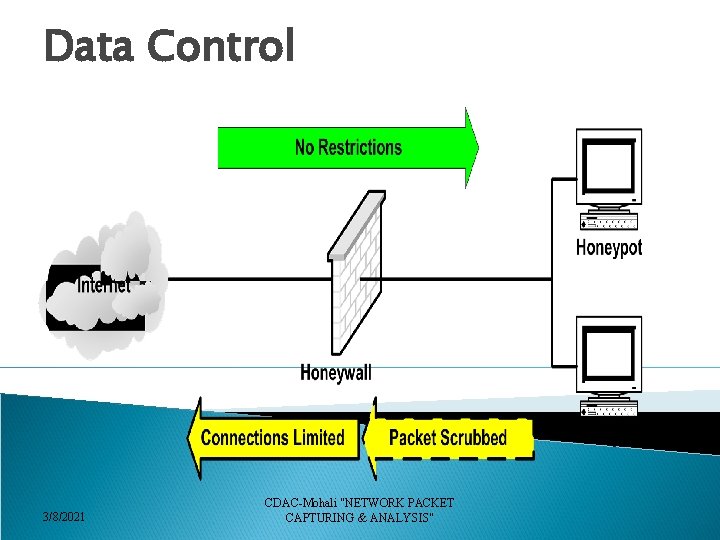
Data Control 3/8/2021 CDAC-Mohali "NETWORK PACKET CAPTURING & ANALYSIS"
DATA CONTROL PURPOSE: Mitigate risk of COMPROMISED Honeypot being used to harm nonhoneynet systems � Count outbound connections (Reverse Firewall) � IPS (Snort-Inline) � Bandwidth Throttling (Reverse Firewall)
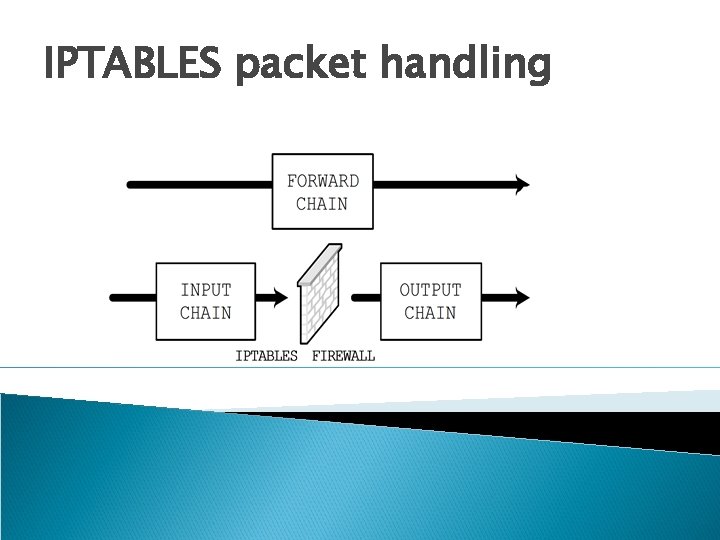
IPTABLES packet handling
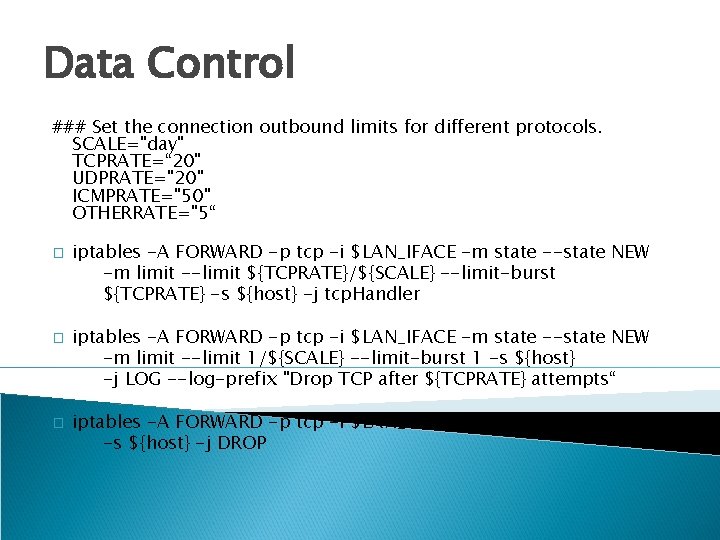
Data Control ### Set the connection outbound limits for different protocols. SCALE="day" TCPRATE=“ 20" UDPRATE="20" ICMPRATE="50" OTHERRATE="5“ � � � iptables -A FORWARD -p tcp -i $LAN_IFACE -m state --state NEW -m limit --limit ${TCPRATE}/${SCALE} --limit-burst ${TCPRATE} -s ${host} -j tcp. Handler iptables -A FORWARD -p tcp -i $LAN_IFACE -m state --state NEW -m limit --limit 1/${SCALE} --limit-burst 1 -s ${host} -j LOG --log-prefix "Drop TCP after ${TCPRATE} attempts“ iptables -A FORWARD -p tcp -i $LAN_IFACE -m state --state NEW -s ${host} -j DROP
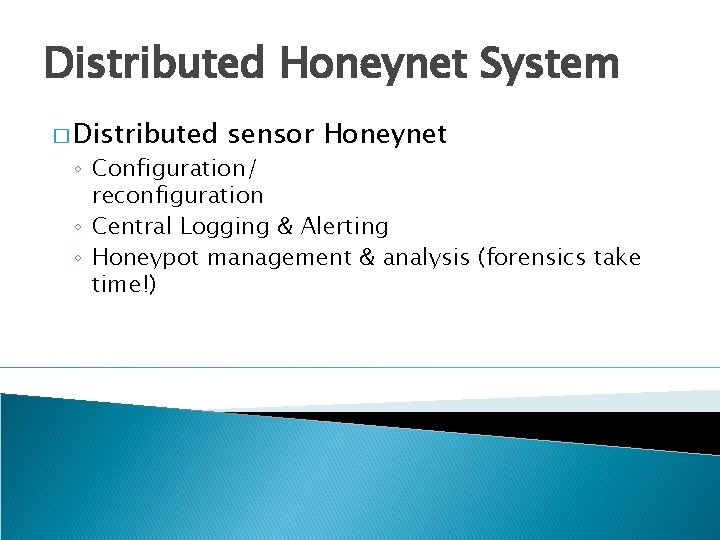
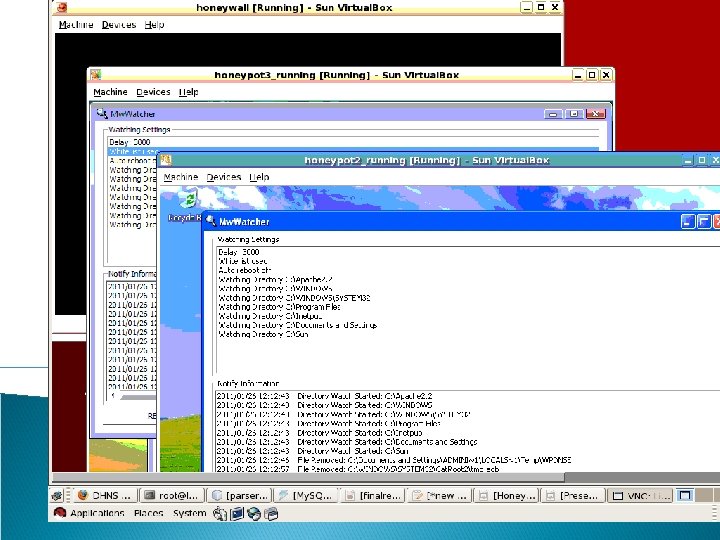
Distributed Honeynet System � Distributed sensor Honeynet ◦ Configuration/ reconfiguration ◦ Central Logging & Alerting ◦ Honeypot management & analysis (forensics take time!)
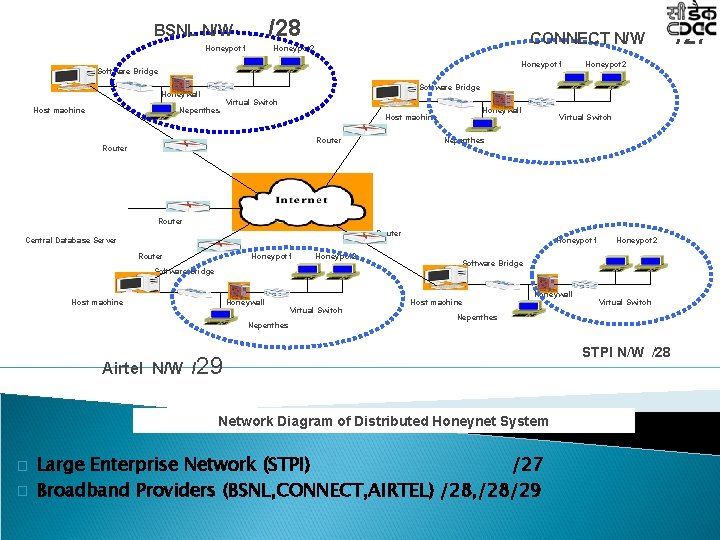
/28 BSNL N/W Honeypot 1 CONNECT N/W Honeypot 2 Honeypot 1 Software Bridge Honeywall Host machine Honeypot 2 Nepenthes Virtual Switch Honeywall Host machine Nepenthes Router Virtual Switch Router Central Database Server Router Honeypot 1 Honeypot 2 Software Bridge Host machine Honeywall Nepenthes Virtual Switch Honeypot 1 Software Bridge Host machine Honeywall Network Diagram of Distributed Honeynet System � Virtual Switch Nepenthes Airtel N/W /29 � Honeypot 2 Large Enterprise Network (STPI) /27 Broadband Providers (BSNL, CONNECT, AIRTEL) /28, /28/29 STPI N/W /28 /27
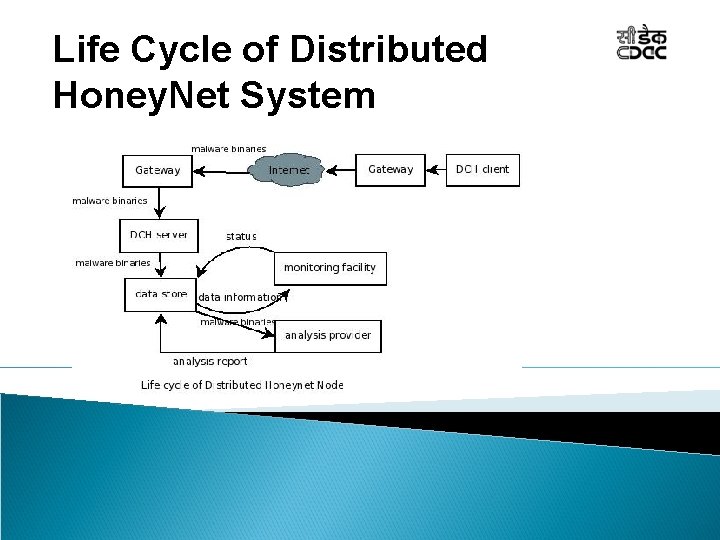
Life Cycle of Distributed Honey. Net System
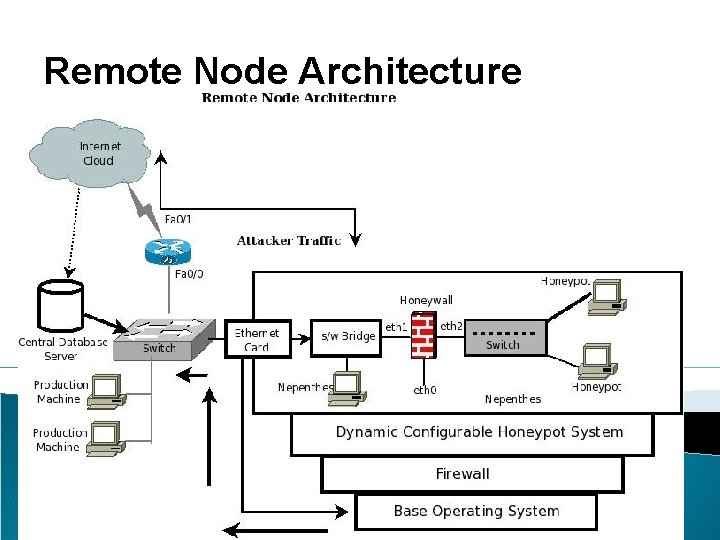
Remote Node Architecture

Malware Analysis
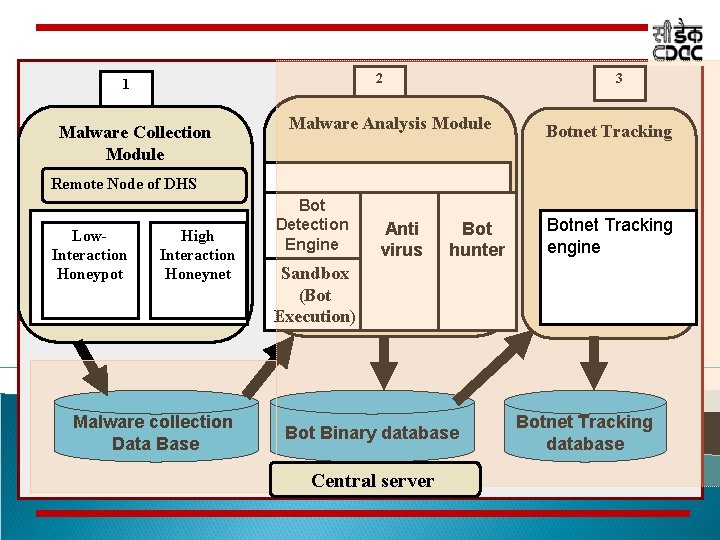
2 1 Malware Collection Module 3 Malware Analysis Module Botnet Tracking Remote Node of DHS Low. Interaction Honeypot High Interaction Honeynet Malware collection Data Base Bot Detection Engine Anti virus Bot hunter Botnet Tracking engine Sandbox (Bot Execution) Bot Binary database Central server Botnet Tracking database
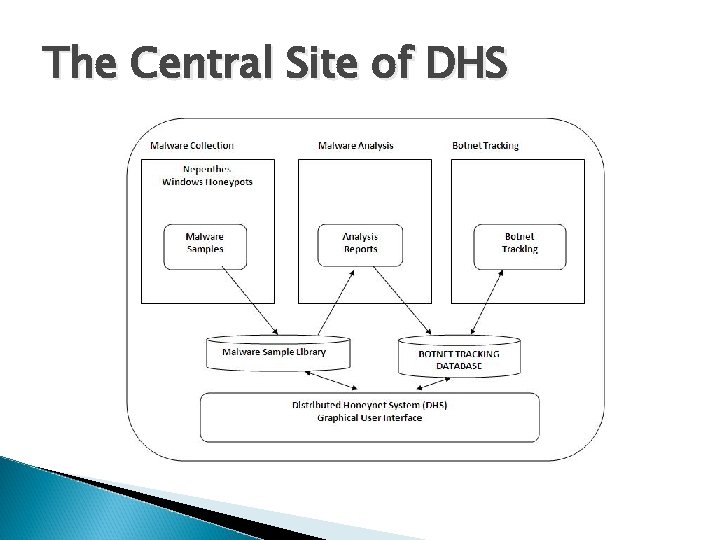
The Central Site of DHS
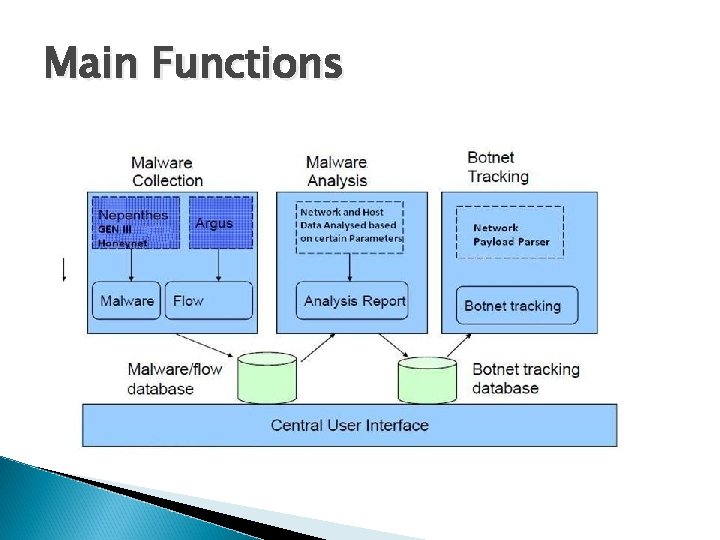
Main Functions
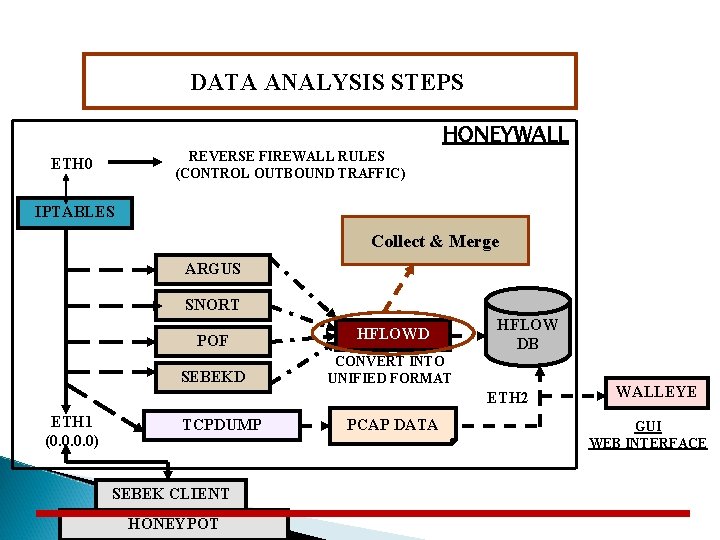
DATA ANALYSIS STEPS REVERSE FIREWALL RULES (CONTROL OUTBOUND TRAFFIC) ETH 0 HONEYWALL IPTABLES Collect & Merge ARGUS SNORT POF HFLOWD SEBEKD CONVERT INTO UNIFIED FORMAT HFLOW DB ETH 2 ETH 1 (0. 0) TCPDUMP SEBEK CLIENT HONEYPOT PCAP DATA WALLEYE GUI WEB INTERFACE
Walleye Web Interface � “Eye on the Honeywall” is a web based interface for Honeywall Configuration, Administration and Data analysis
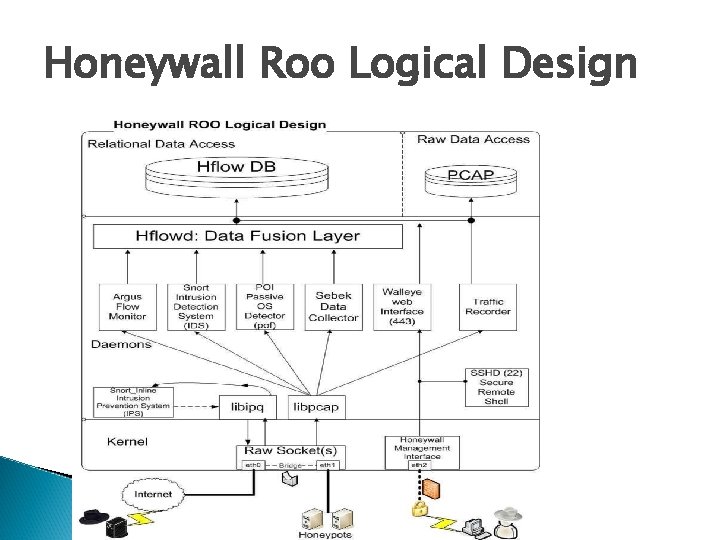
Honeywall Roo Logical Design
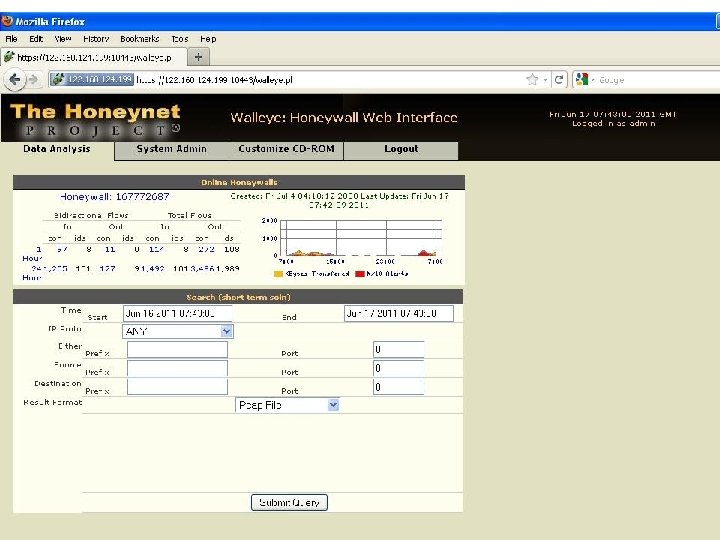
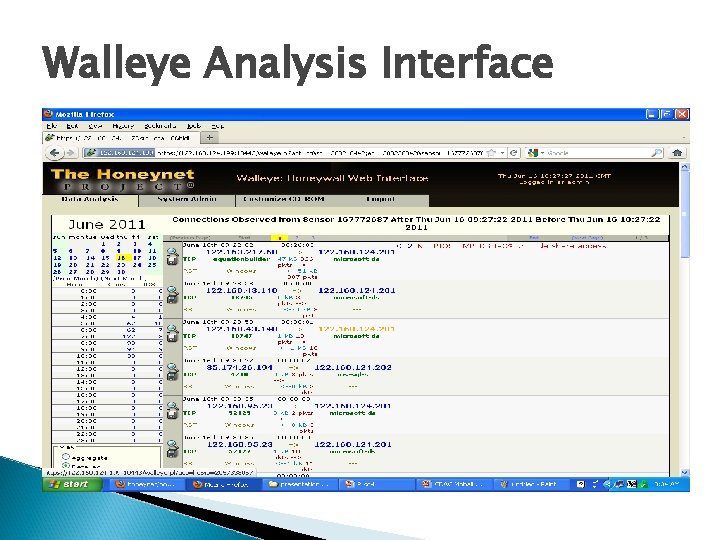
Walleye Analysis Interface
Botnet Detection
Introduction Botnet Problem Typical Botnet Life Cycle How Botnet Grows Challenges for Botnet detection Roadmap to Detection system Botnet Detection Approaches Our Implemented Approach Experiments and results
What Is a Bot/Botnet? Bot A malware instance that runs autonomously and automatically on a compromised computer (zombie) without owner’s consent Profit-driven, professionally written, widely propagated Botnet (Bot Army): network of bots controlled by criminals Definition: “A coordinated group of malware instances that are controlled by a botmaster via some C&C channel” Architecture: centralized (e. g. , IRC, HTTP), distributed (e. g. , P 2 P)
Botnets are used for … All DDo. S attacks Spam Click fraud Information theft Phishing attacks Distributing other malware, e. g. , spyware. PCs are part of a botnet!”
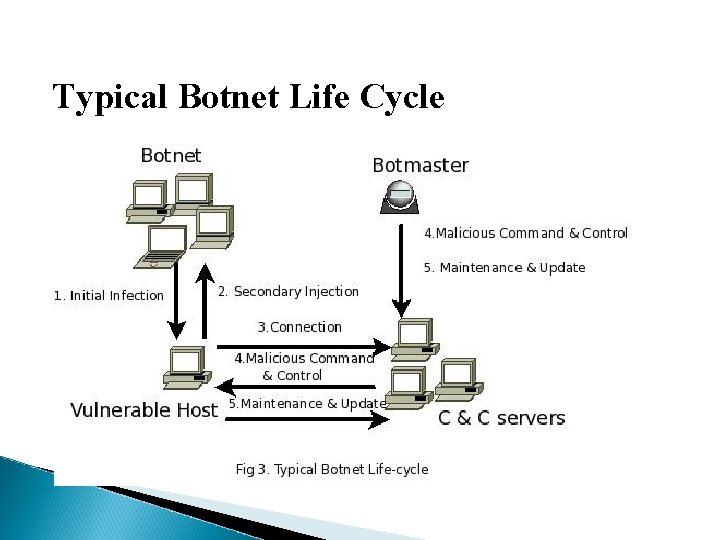
Typical Botnet Life Cycle
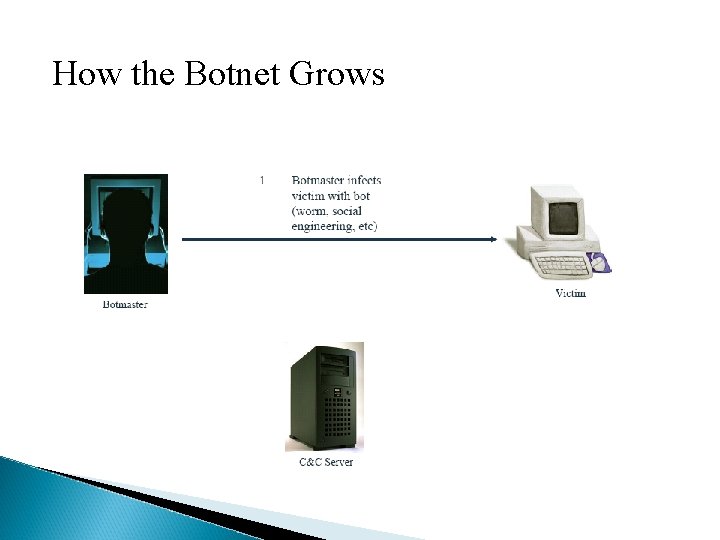
How the Botnet Grows
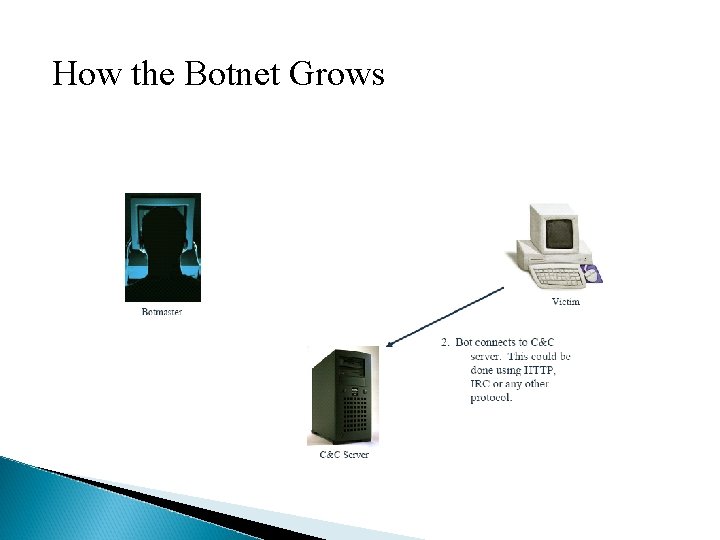
How the Botnet Grows
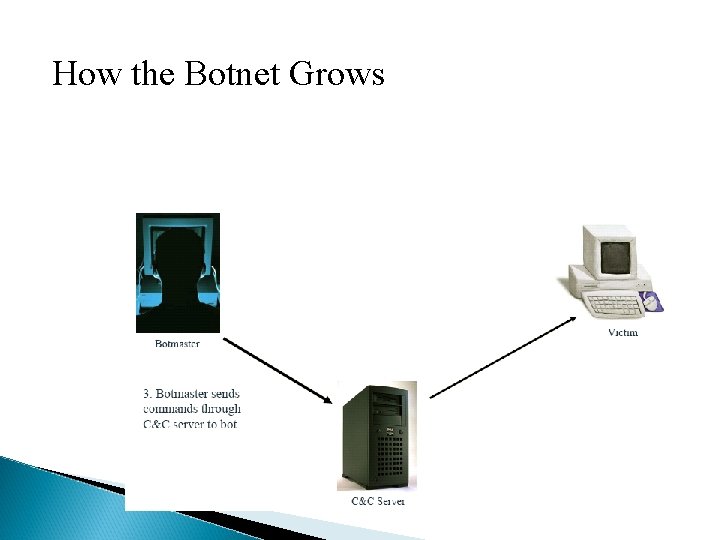
How the Botnet Grows
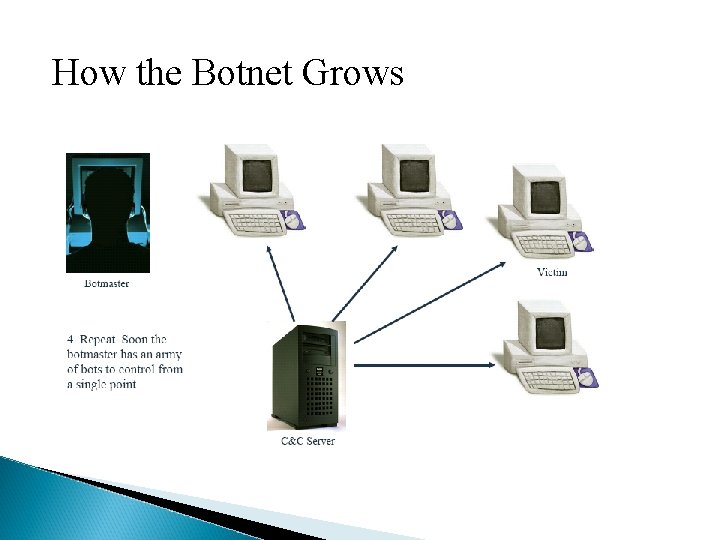
How the Botnet Grows
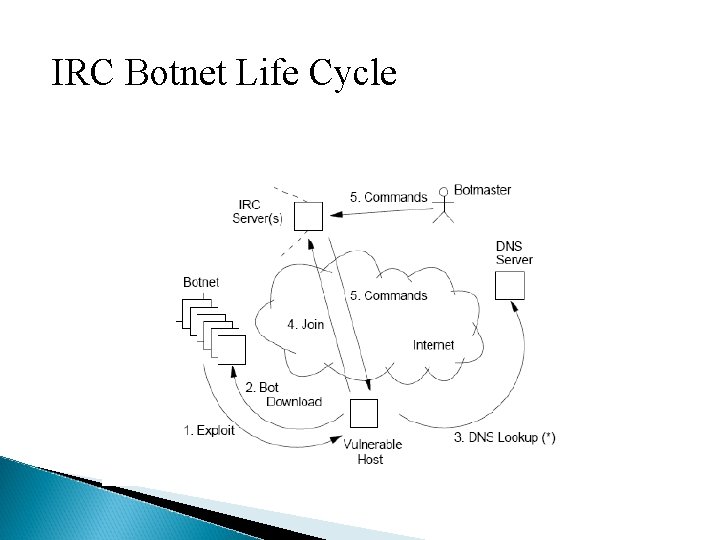
IRC Botnet Life Cycle
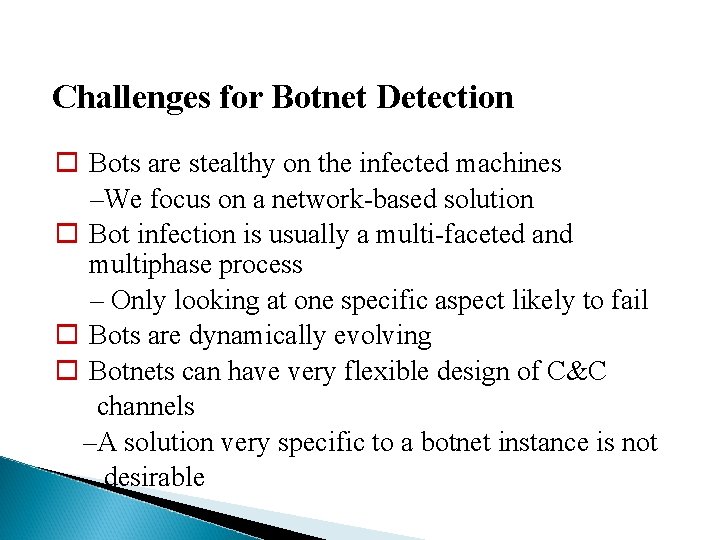
Challenges for Botnet Detection Bots are stealthy on the infected machines –We focus on a network-based solution Bot infection is usually a multi-faceted and multiphase process – Only looking at one specific aspect likely to fail Bots are dynamically evolving Botnets can have very flexible design of C&C channels –A solution very specific to a botnet instance is not desirable
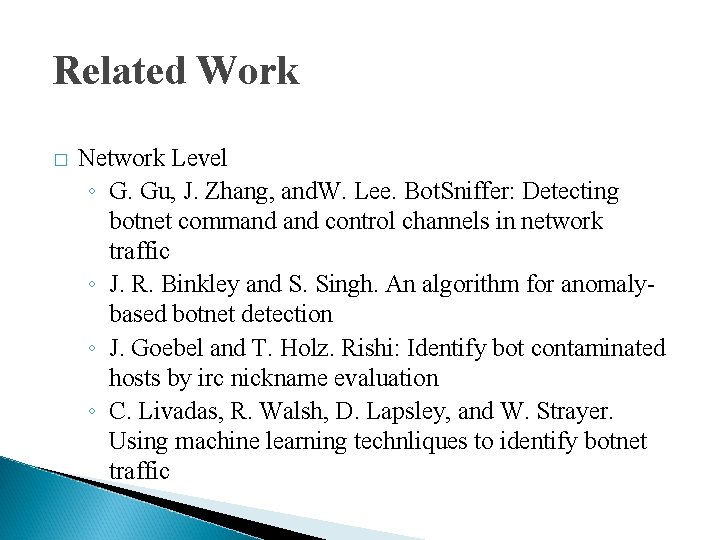
Related Work � Network Level ◦ G. Gu, J. Zhang, and. W. Lee. Bot. Sniffer: Detecting botnet command control channels in network traffic ◦ J. R. Binkley and S. Singh. An algorithm for anomalybased botnet detection ◦ J. Goebel and T. Holz. Rishi: Identify bot contaminated hosts by irc nickname evaluation ◦ C. Livadas, R. Walsh, D. Lapsley, and W. Strayer. Using machine learning technliques to identify botnet traffic
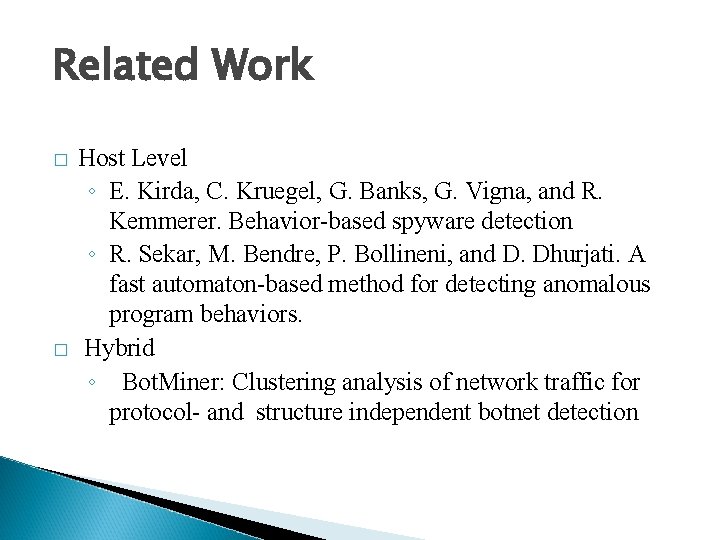
Related Work � � Host Level ◦ E. Kirda, C. Kruegel, G. Banks, G. Vigna, and R. Kemmerer. Behavior-based spyware detection ◦ R. Sekar, M. Bendre, P. Bollineni, and D. Dhurjati. A fast automaton-based method for detecting anomalous program behaviors. Hybrid ◦ Bot. Miner: Clustering analysis of network traffic for protocol- and structure independent botnet detection
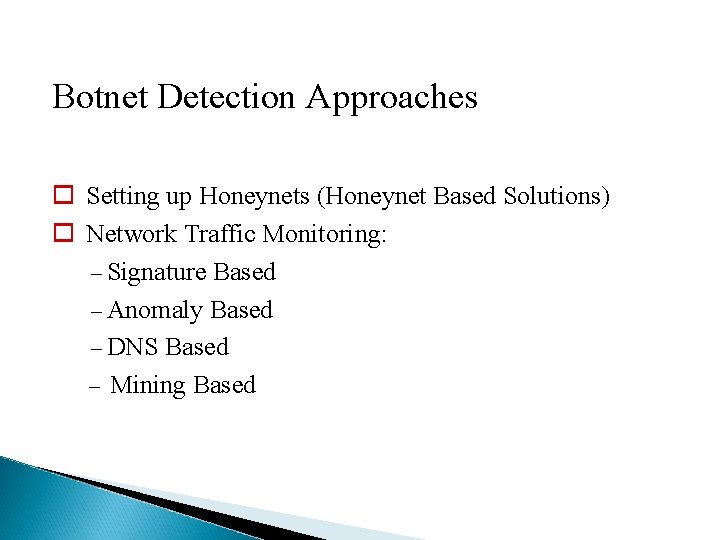
Botnet Detection Approaches Setting up Honeynets (Honeynet Based Solutions) Network Traffic Monitoring: – Signature Based – Anomaly Based – DNS Based – Mining Based
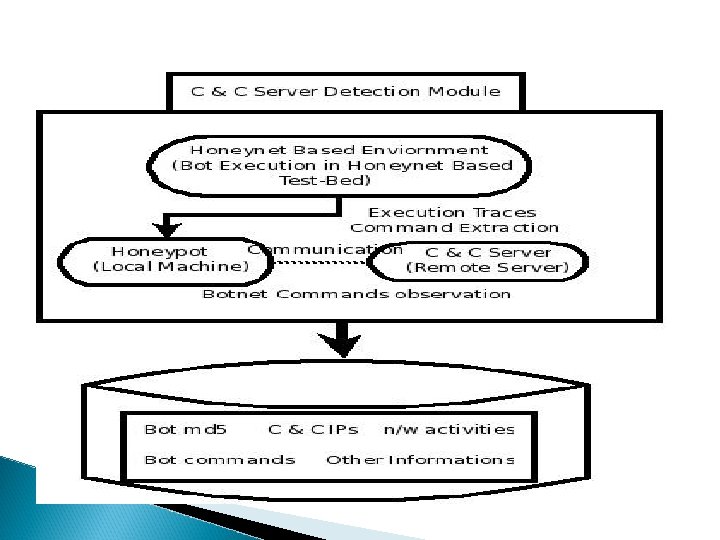
Honeynet Based Solution It enable us to isolate the bot from network and monitor its traffic in more controlled way, instead of waiting to be infected and then monitor the t traffic – Bot execution in Honeynet test bed – Monitor the traffic generated by bots Open Analysis : – Provides connection to Internet – More flexible than closed analysis. l
Our Implemented Approach • Honeynet Based Solution – Achievements • • Approach Implemented Honeynet Based Bot Analysis Architecture Payload Parser Web GUI and report generation
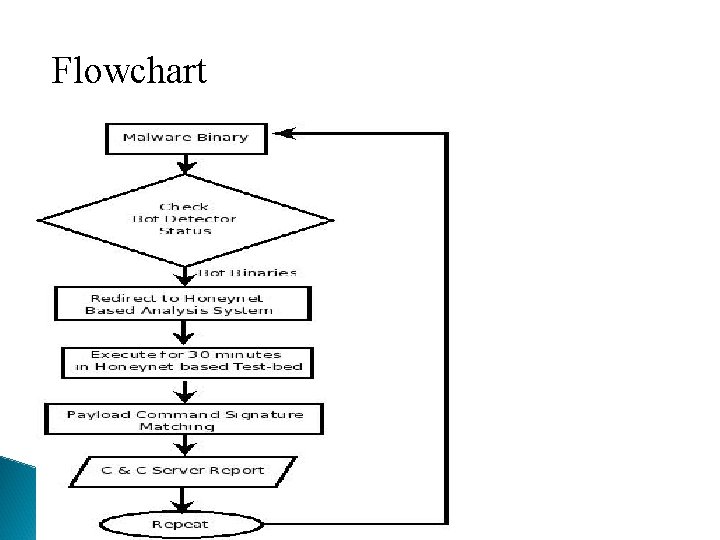
Flowchart
Features Systematically collect and analyze bot traffic over internet Provides controlled connection to Internet: rate limit the outbound connections. It uses network-based anomaly detection to identify C & C command sequences
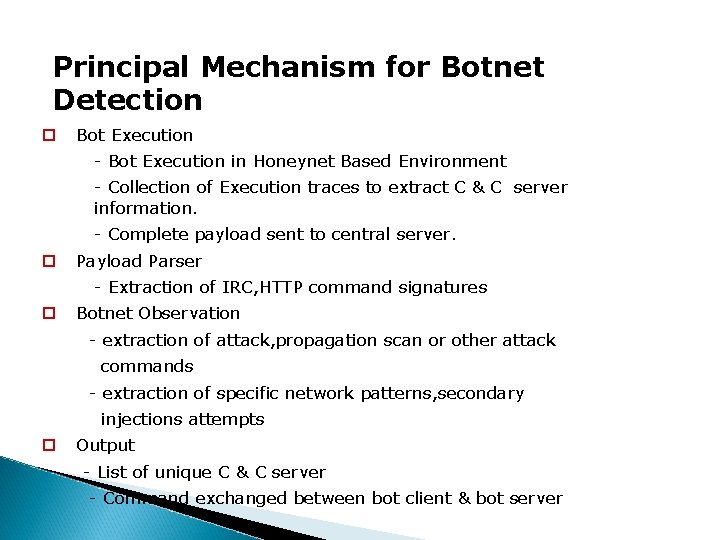
Principal Mechanism for Botnet Detection Bot Execution - Bot Execution in Honeynet Based Environment - Collection of Execution traces to extract C & C server information. - Complete payload sent to central server. Payload Parser - Extraction of IRC, HTTP command signatures Botnet Observation - extraction of attack, propagation scan or other attack commands - extraction of specific network patterns, secondary injections attempts Output - List of unique C & C server - Command exchanged between bot client & bot server
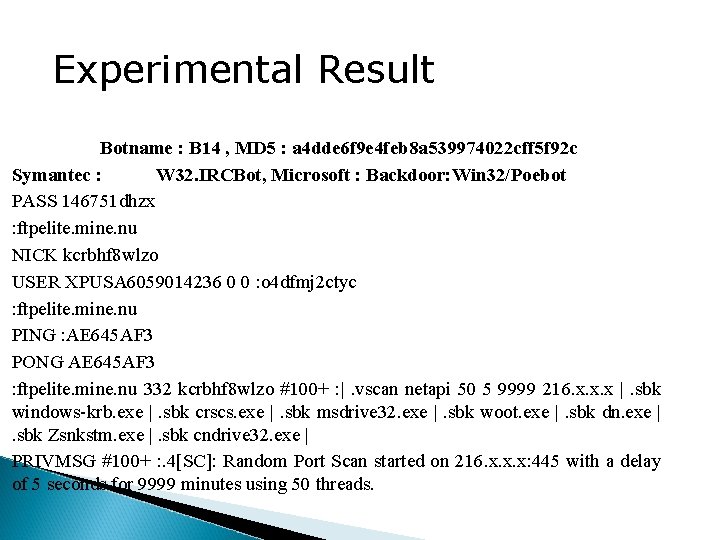
Experimental Result Botname : B 14 , MD 5 : a 4 dde 6 f 9 e 4 feb 8 a 539974022 cff 5 f 92 c Symantec : W 32. IRCBot, Microsoft : Backdoor: Win 32/Poebot PASS 146751 dhzx : ftpelite. mine. nu NICK kcrbhf 8 wlzo USER XPUSA 6059014236 0 0 : o 4 dfmj 2 ctyc : ftpelite. mine. nu PING : AE 645 AF 3 PONG AE 645 AF 3 : ftpelite. mine. nu 332 kcrbhf 8 wlzo #100+ : |. vscan netapi 50 5 9999 216. x. x. x |. sbk windows-krb. exe |. sbk crscs. exe |. sbk msdrive 32. exe |. sbk woot. exe |. sbk dn. exe |. sbk Zsnkstm. exe |. sbk cndrive 32. exe | PRIVMSG #100+ : . 4[SC]: Random Port Scan started on 216. x. x. x: 445 with a delay of 5 seconds for 9999 minutes using 50 threads.
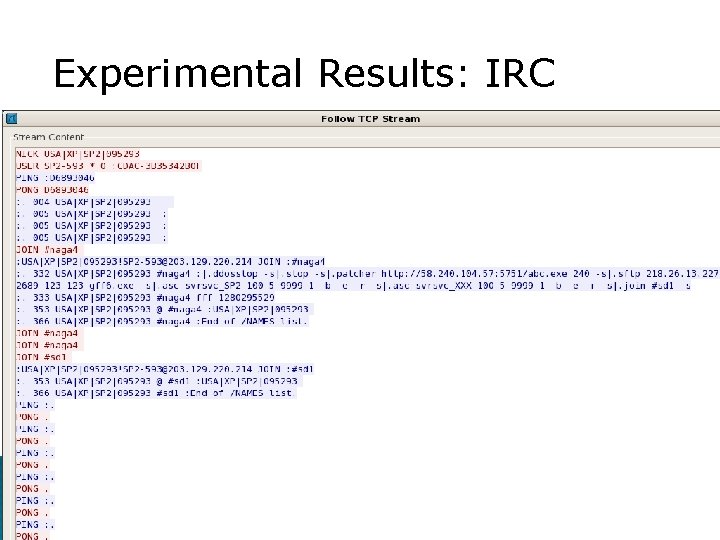
Experimental Results: IRC
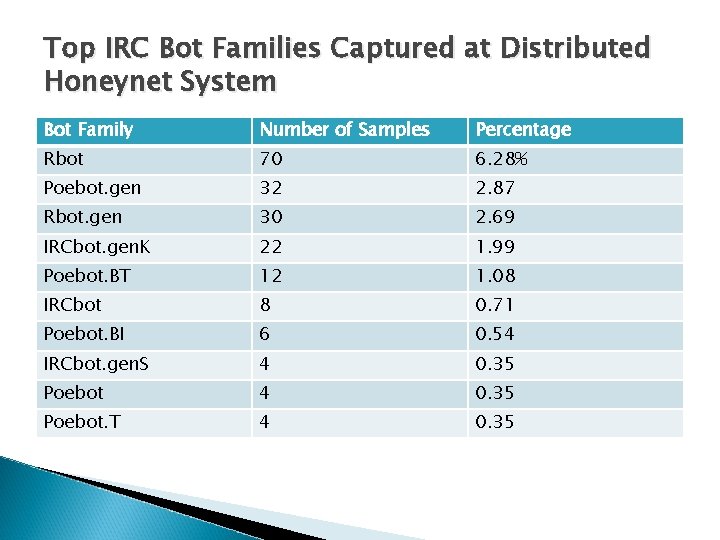
Top IRC Bot Families Captured at Distributed Honeynet System Bot Family Number of Samples Percentage Rbot 70 6. 28% Poebot. gen 32 2. 87 Rbot. gen 30 2. 69 IRCbot. gen. K 22 1. 99 Poebot. BT 12 1. 08 IRCbot 8 0. 71 Poebot. BI 6 0. 54 IRCbot. gen. S 4 0. 35 Poebot. T 4 0. 35
IRC Based Botnet Measurement � In total we could identify 99 IRC-based bot binaries , a rate of 8. 25% of the overall binaries in 12 months
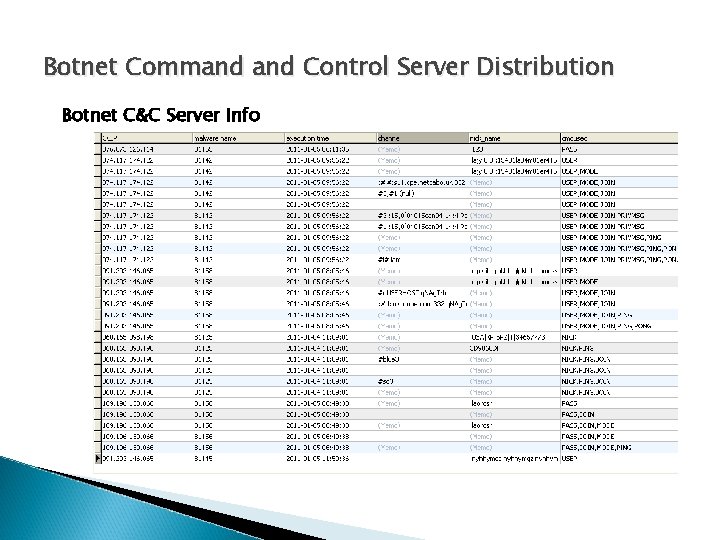
Botnet Command Control Server Distribution Botnet C&C Server Info
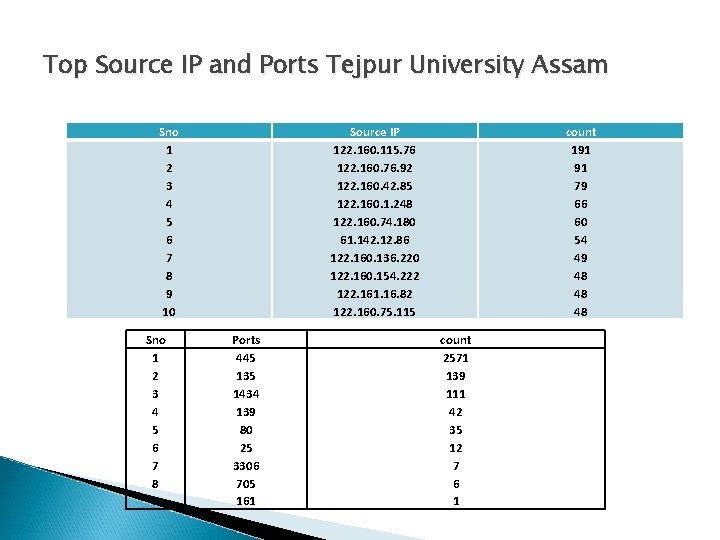
Top Source IP and Ports Tejpur University Assam Sno 1 2 3 4 5 6 7 8 9 10 Sno 1 2 3 4 5 6 7 8 9 Source IP 122. 160. 115. 76 122. 160. 76. 92 122. 160. 42. 85 122. 160. 1. 248 122. 160. 74. 180 61. 142. 12. 86 122. 160. 136. 220 122. 160. 154. 222 122. 161. 16. 82 122. 160. 75. 115 Ports 445 135 1434 139 80 25 3306 705 161 count 191 91 79 66 60 54 49 48 48 48 count 2571 139 111 42 35 12 7 6 1
Thank You
- Slides: 61