Distributed Collaborative Key Agreement and Authentication Protocols for
Distributed Collaborative Key Agreement and Authentication Protocols for Dynamic Peer Groups IEEE/ACM Trans. on Netw. , Vol. 14, No. 2, April 2006 Patrick P. C. Lee, at el. Hyeongseop Shim NS Lab, Div. of CS November 6, 2007 KAIST
Contents Introduction Tree-Based Group Diffie-Hellman (TGDH) Protocol Interval-Based Distributed Rekeying Algorithms Rebuild Algorithm Batch Algorithm Queue-Batch Algorithm Performance Evaluation Authenticated TGDH Conclusion 2
Introduction Emergence of group-oriented distributed applications Necessity to provide group communication privacy Distributed group key agreement Comparison with centralized group key management No centralized key server Increase in system reliability 3
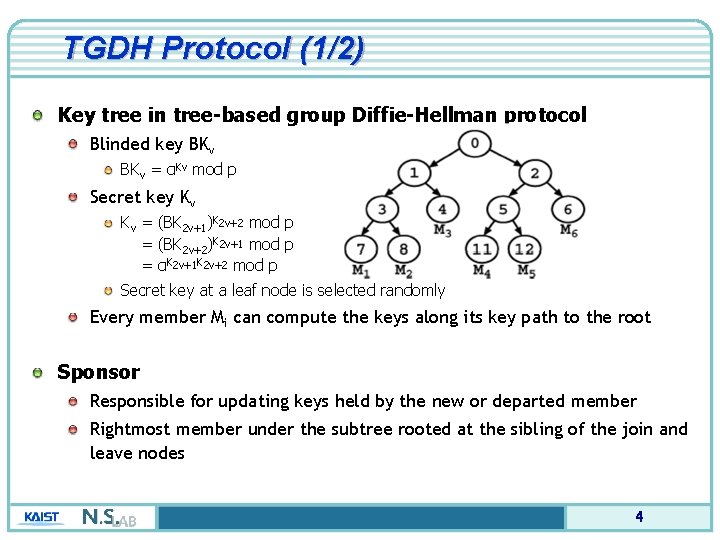
TGDH Protocol (1/2) Key tree in tree-based group Diffie-Hellman protocol Blinded key BKv = αKv mod p Secret key Kv Kv = (BK 2 v+1)K 2 v+2 mod p = (BK 2 v+2)K 2 v+1 mod p = αK 2 v+1 K 2 v+2 mod p Secret key at a leaf node is selected randomly Every member Mi can compute the keys along its key path to the root Sponsor Responsible for updating keys held by the new or departed member Rightmost member under the subtree rooted at the sibling of the join and leave nodes 4
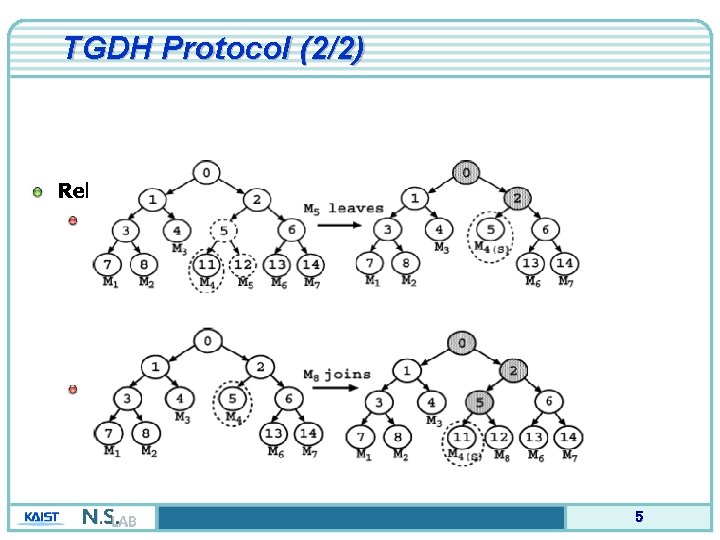
TGDH Protocol (2/2) Rekeying operation Single leave Single join 5
Interval-Based Rekeying Algorithms (1/4) Overview Constant rekeying frequency regardless of the dynamic join and leave Delay of the update of the group key Tradeoff of weakening both backward and forward secrecy Proposed algorithms Rebuild algorithm Batch algorithm Queue-batch algorithm 6
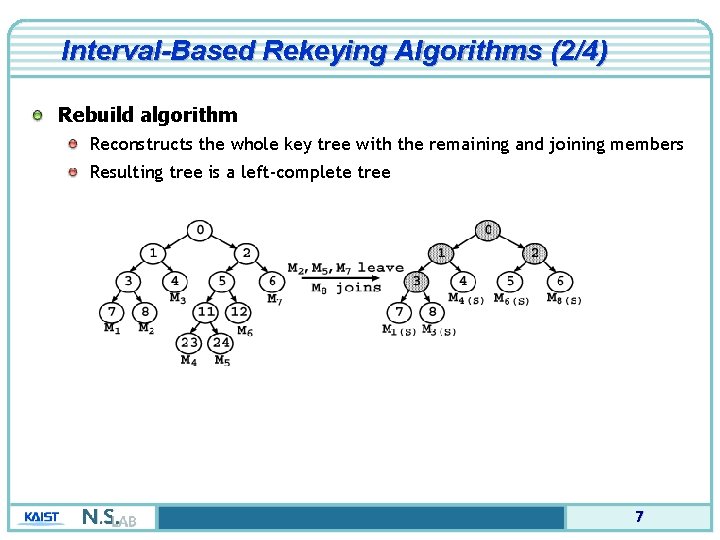
Interval-Based Rekeying Algorithms (2/4) Rebuild algorithm Reconstructs the whole key tree with the remaining and joining members Resulting tree is a left-complete tree 7
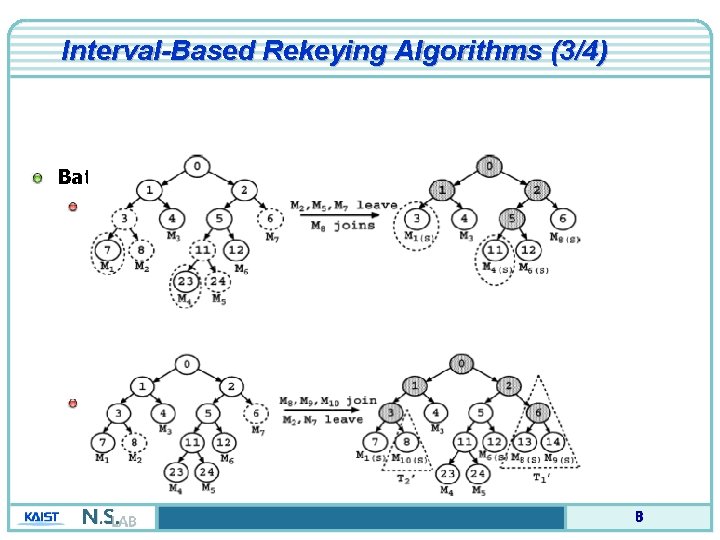
Interval-Based Rekeying Algorithms (3/4) Batch algorithm L>J>0 J>L>0 8
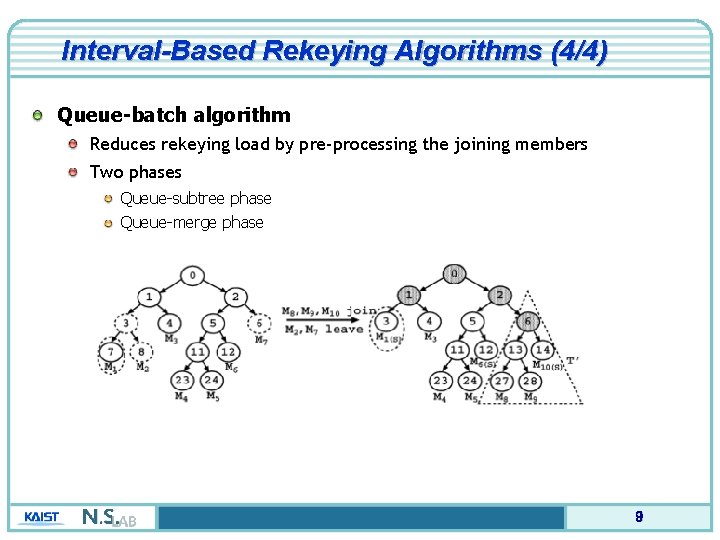
Interval-Based Rekeying Algorithms (4/4) Queue-batch algorithm Reduces rekeying load by pre-processing the joining members Two phases Queue-subtree phase Queue-merge phase 9
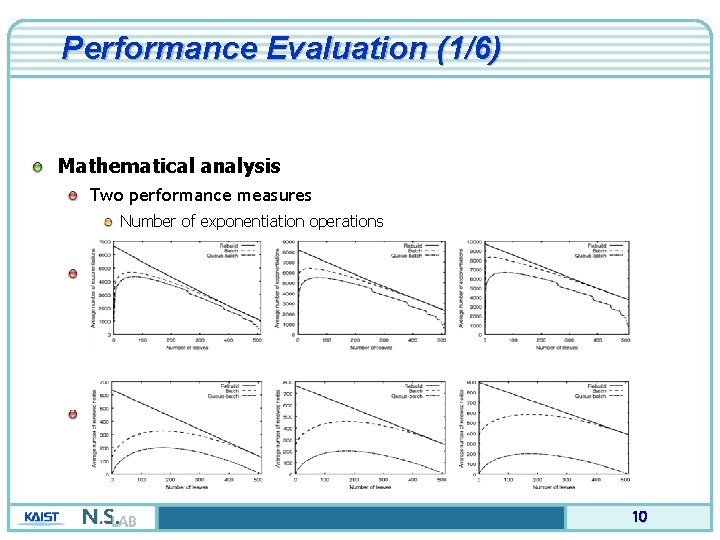
Performance Evaluation (1/6) Mathematical analysis Two performance measures Number of exponentiation operations Number of renewed nodes Average numbers of exponentiation (J = 128 / 256 / 384) Average number of renewed nodes (J = 128 / 256 / 384) 10
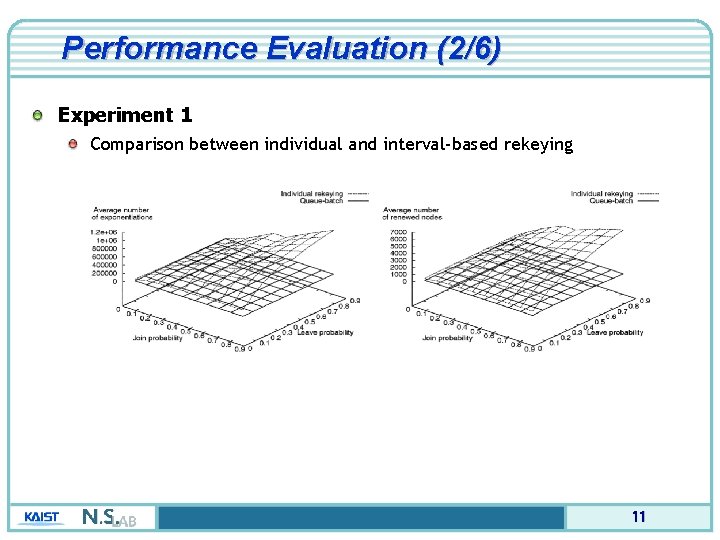
Performance Evaluation (2/6) Experiment 1 Comparison between individual and interval-based rekeying 11
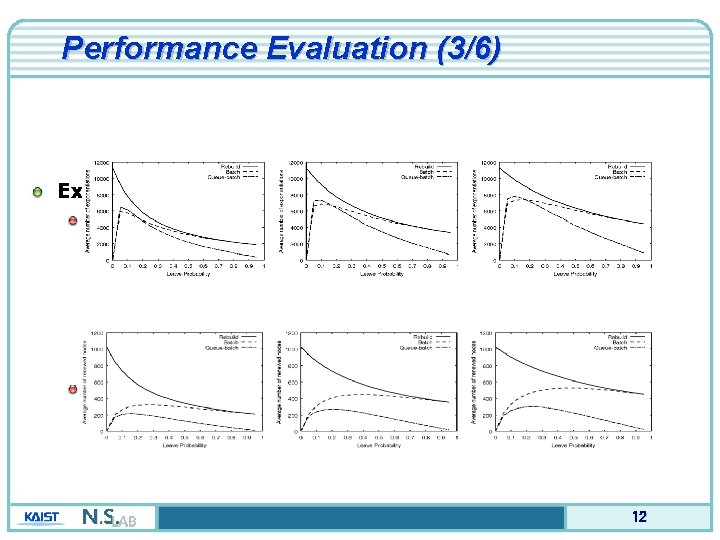
Performance Evaluation (3/6) Experiment 2 Average number of exponentiation (PJ = 0. 25 / 0. 75) Average number of renewed nodes (PJ = 0. 25 / 0. 75) 12
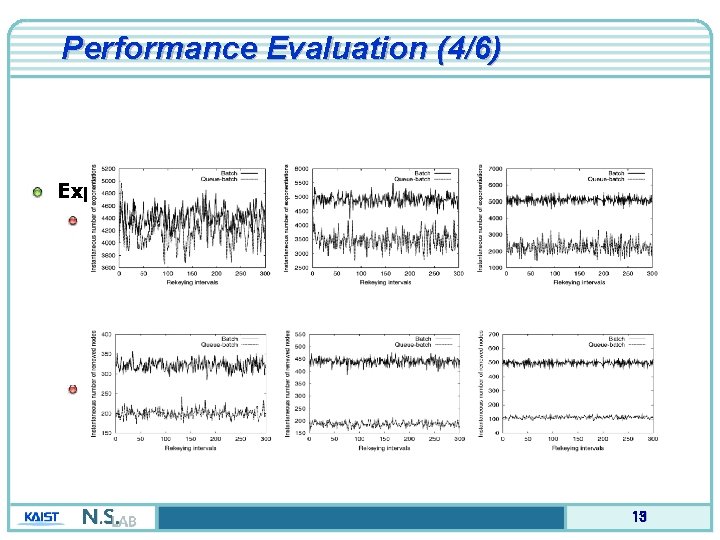
Performance Evaluation (4/6) Experiment 3 Instantaneous number of exponentiation (PJ = PL = 0. 25 / 0. 75) Instantaneous number of renewed nodes (PJ = PL = 0. 25 / 0. 75) 13
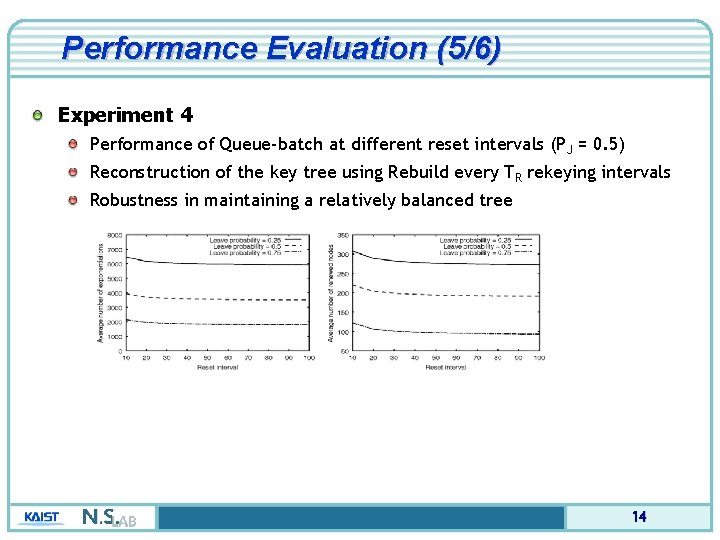
Performance Evaluation (5/6) Experiment 4 Performance of Queue-batch at different reset intervals (PJ = 0. 5) Reconstruction of the key tree using Rebuild every TR rekeying intervals Robustness in maintaining a relatively balanced tree 14
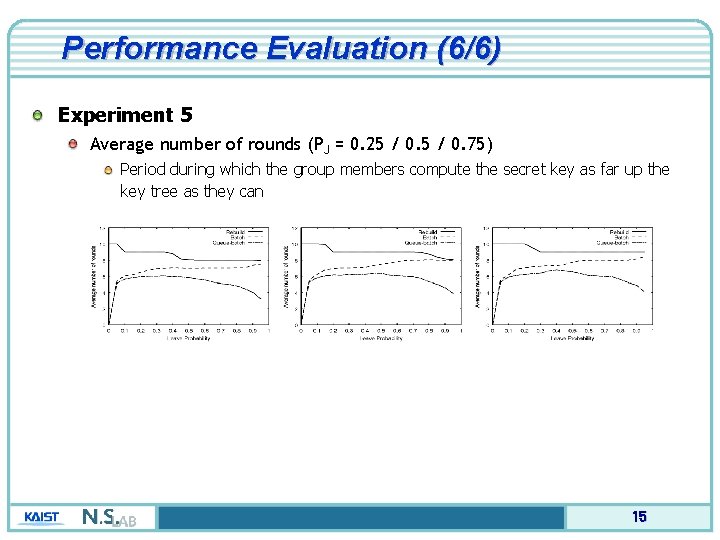
Performance Evaluation (6/6) Experiment 5 Average number of rounds (PJ = 0. 25 / 0. 75) Period during which the group members compute the secret key as far up the key tree as they can 15
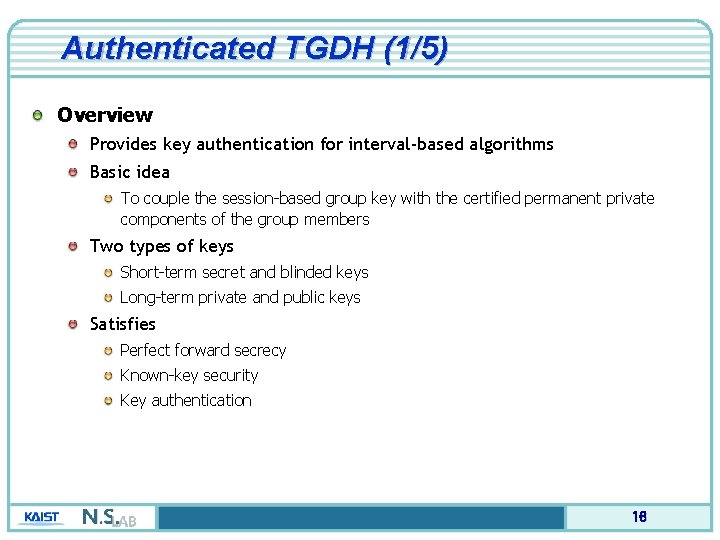
Authenticated TGDH (1/5) Overview Provides key authentication for interval-based algorithms Basic idea To couple the session-based group key with the certified permanent private components of the group members Two types of keys Short-term secret and blinded keys Long-term private and public keys Satisfies Perfect forward secrecy Known-key security Key authentication 16
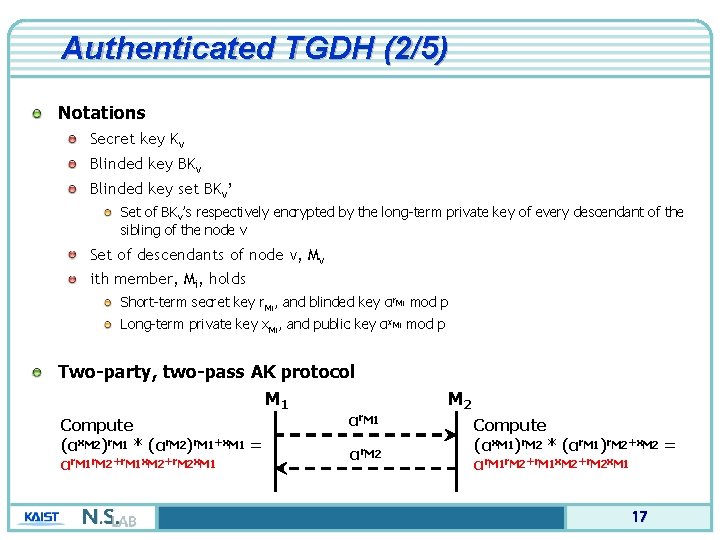
Authenticated TGDH (2/5) Notations Secret key Kv Blinded key BKv Blinded key set BKv’ Set of BKv’s respectively encrypted by the long-term private key of every descendant of the sibling of the node v Set of descendants of node v, Mv ith member, Mi, holds Short-term secret key r. Mi, and blinded key αr. Mi mod p Long-term private key x. Mi, and public key αx. Mi mod p Two-party, two-pass AK protocol M 1 Compute (αx. M 2)r. M 1 * (αr. M 2)r. M 1+x. M 1 = αr. M 1 r. M 2+r. M 1 x. M 2+r. M 2 x. M 1 αr. M 2 Compute (αx. M 1)r. M 2 * (αr. M 1)r. M 2+x. M 2 = αr. M 1 r. M 2+r. M 1 x. M 2+r. M 2 x. M 1 17
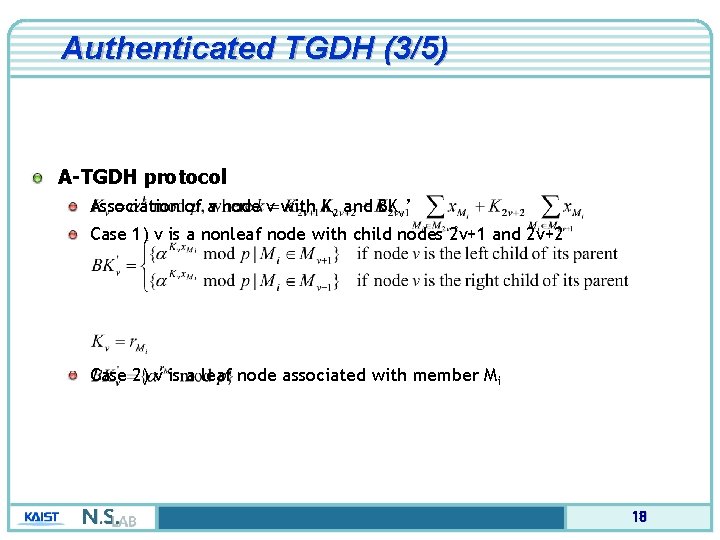
Authenticated TGDH (3/5) A-TGDH protocol Association of a node v with Kv and BKv’ Case 1) v is a nonleaf node with child nodes 2 v+1 and 2 v+2 Case 2) v is a leaf node associated with member Mi 18
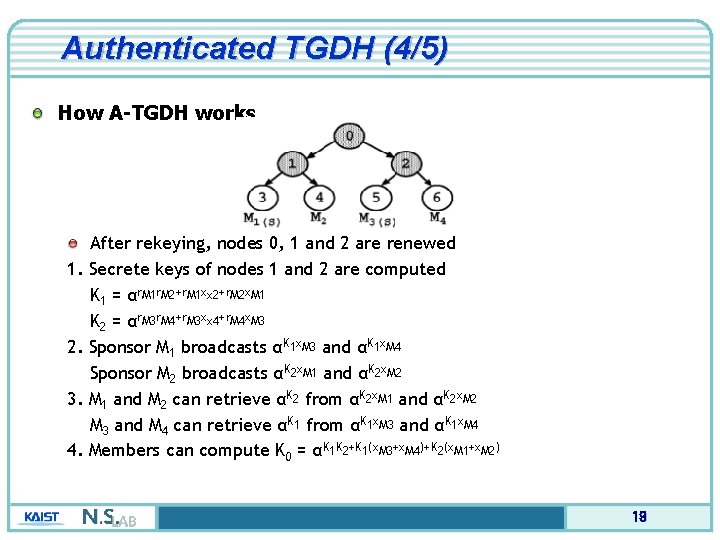
Authenticated TGDH (4/5) How A-TGDH works 1. 2. 3. 4. After rekeying, nodes 0, 1 and 2 are renewed Secrete keys of nodes 1 and 2 are computed K 1 = αr. M 1 r. M 2+r. M 1 xx 2+r. M 2 x. M 1 K 2 = αr. M 3 r. M 4+r. M 3 xx 4+r. M 4 x. M 3 Sponsor M 1 broadcasts αK 1 x. M 3 and αK 1 x. M 4 Sponsor M 2 broadcasts αK 2 x. M 1 and αK 2 x. M 2 M 1 and M 2 can retrieve αK 2 from αK 2 x. M 1 and αK 2 x. M 2 M 3 and M 4 can retrieve αK 1 from αK 1 x. M 3 and αK 1 x. M 4 Members can compute K 0 = αK 1 K 2+K 1(x. M 3+x. M 4)+K 2(x. M 1+x. M 2) 19
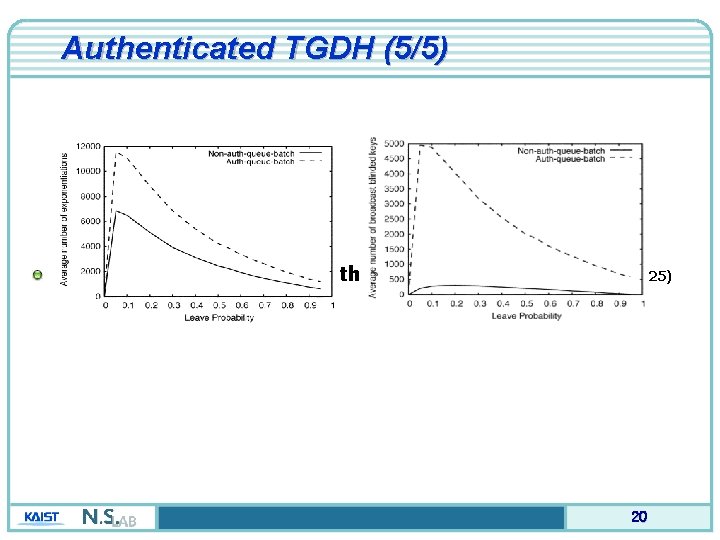
Authenticated TGDH (5/5) Comparison between nonauth and auth Queue-batch (Pj = 0. 25) 20
Conclusion Interval-based distributed rekeying algorithms Rebuild Batch algorithm Queue-batch algorithm Evaluation of interval-based algorithms Authenticated group key agreement protocol 21
- Slides: 21