DISCOVERY OF OPTIMAL STRUCTURAL HOLE SPANNERS IN COMMUNITY
![References � [1] Wenzheng Xu, "Efficient Algorithms for the Identification of Top-k Structural Hole References � [1] Wenzheng Xu, "Efficient Algorithms for the Identification of Top-k Structural Hole](https://slidetodoc.com/presentation_image_h2/9d543cf60ca9fc219d6b92caa6d6c0eb/image-17.jpg)
- Slides: 18
DISCOVERY OF OPTIMAL STRUCTURAL HOLE SPANNERS IN COMMUNITY BASED MODEL Guided by: Dr. P. Pabitha, Assistant Professor, Department of computer Technology, Anna University, MIT Campus, Chennai. Ramakrishnan R 2016658006 Master of Engineering- CSE Department of computer Technology
INTRODUCTION � Social networks already become a bridge to connect our daily physical life and the virtual web space. � When two separate clusters possess non-redundant information, there is said to be a structural hole between them. � The Community-Based Models is to maximize a utility function that measures the degree to which structural hole spanners communities. � Ego-centric social network analysis, structural holes theory, shortest paths and reduction structure hole (RSH) is used to build a comprehensible model to predict the structural hole
OBJECTIVE � Efficient yet scalable algorithms, by developing innovative filtering techniques that can filter out unlikely solutions as quickly as possible. � The proposed techniques are built up on fast estimations of the upper and lower bounds on the cost of an optimal solution and make use of articulation points in real social networks. � The “structural holes” influence matrix in degree reflects the node’s local and global information
PROBLEM SCENARIO � Work relies heavily on communities while finding communities in a large social network is painstaking, and the quality of the solution delivered by their algorithm is fully determined by the found communities. � If the quality of the found communities are poor, the quality of the solution consisting of structural hole spanners will be low as well. � Key role in the shortest paths between the nodes in different communities and their removal can significantly increase the lengths between the other vertices.
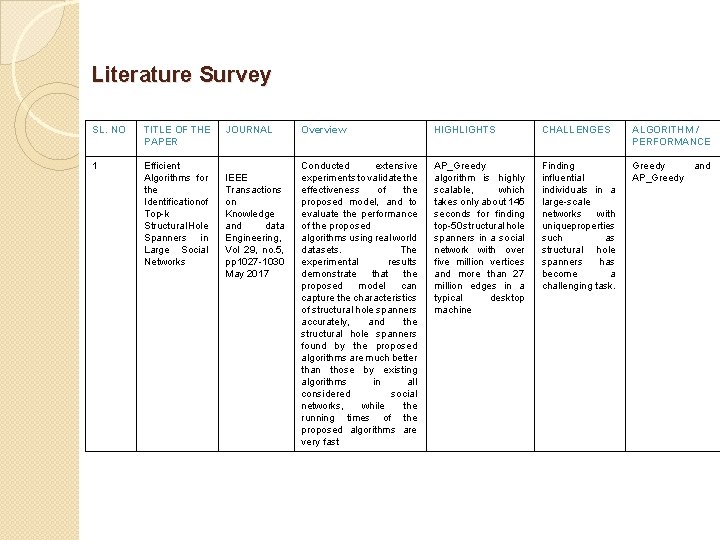
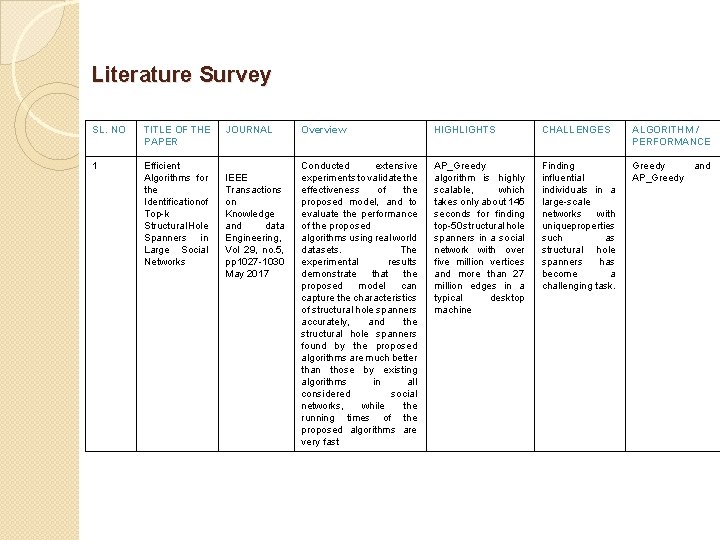
Literature Survey SL. NO TITLE OF THE PAPER 1 Efficient Algorithms for the Identificationof Top-k Structural Hole Spanners in Large Social Networks JOURNAL IEEE Transactions on Knowledge and data Engineering, Vol 29, no. 5, pp 1027 -1030 May 2017 Overview HIGHLIGHTS CHALLENGES ALGORITHM / PERFORMANCE Conducted extensive experiments to validate the effectiveness of the proposed model, and to evaluate the performance of the proposed algorithms using real world datasets. The experimental results demonstrate that the proposed model can capture the characteristics of structural hole spanners accurately, and the structural hole spanners found by the proposed algorithms are much better than those by existing algorithms in all considered social networks, while the running times of the proposed algorithms are very fast AP_Greedy algorithm is highly scalable, which takes only about 145 seconds for finding top-50 structural hole spanners in a social network with over five million vertices and more than 27 million edges in a typical desktop machine Finding influential individuals in a large-scale networks with uniqueproperties such as structural hole spanners has become a challenging task. Greedy and AP_Greedy
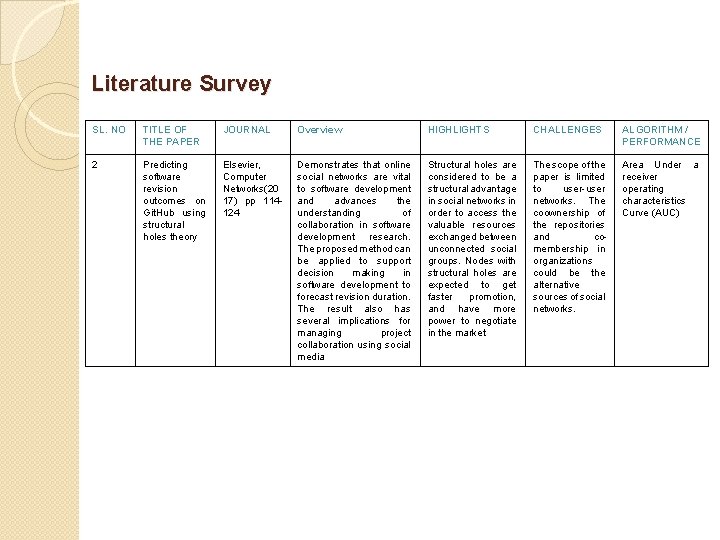
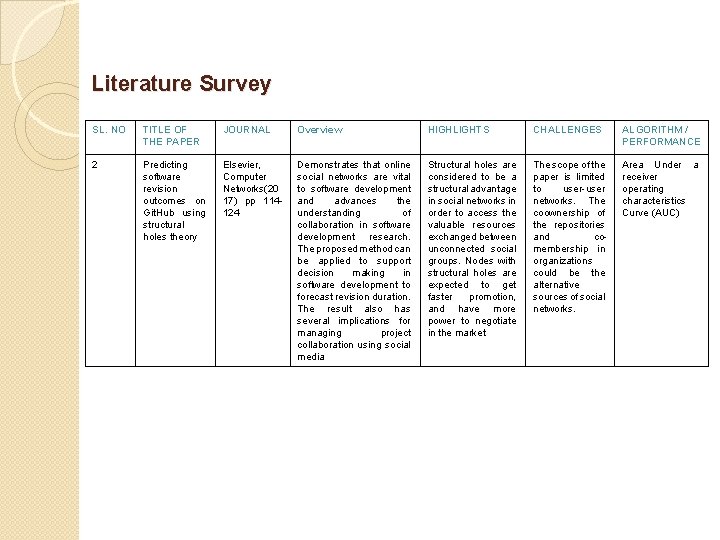
Literature Survey SL. NO TITLE OF THE PAPER JOURNAL Overview HIGHLIGHTS CHALLENGES ALGORITHM / PERFORMANCE 2 Predicting software revision outcomes on Git. Hub using structural holes theory Elsevier, Computer Networks(20 17) pp 114124 Demonstrates that online social networks are vital to software development and advances the understanding of collaboration in software development research. The proposed method can be applied to support decision making in software development to forecast revision duration. The result also has several implications for managing project collaboration using social media Structural holes are considered to be a structural advantage in social networks in order to access the valuable resources exchanged between unconnected social groups. Nodes with structural holes are expected to get faster promotion, and have more power to negotiate in the market The scope of the paper is limited to user-user networks. The coownership of the repositories and comembership in organizations could be the alternative sources of social networks. Area Under a receiver operating characteristics Curve (AUC)
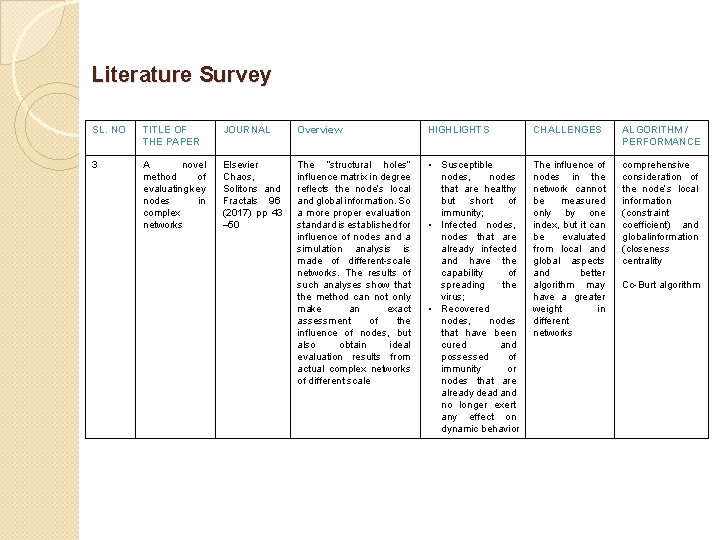
Literature Survey SL. NO TITLE OF THE PAPER JOURNAL Overview HIGHLIGHTS CHALLENGES ALGORITHM / PERFORMANCE 3 A novel method of evaluating key nodes in complex networks Elsevier Chaos, Solitons and Fractals 96 (2017) pp 43 – 50 The “structural holes” influence matrix in degree reflects the node’s local and global information. So a more proper evaluation standard is established for influence of nodes and a simulation analysis is made of different-scale networks. The results of such analyses show that the method can not only make an exact assessment of the influence of nodes, but also obtain ideal evaluation results from actual complex networks of different scale • Susceptible nodes, nodes that are healthy but short of immunity; • Infected nodes, nodes that are already infected and have the capability of spreading the virus; • Recovered nodes, nodes that have been cured and possessed of immunity or nodes that are already dead and no longer exert any effect on dynamic behavior The influence of nodes in the network cannot be measured only by one index, but it can be evaluated from local and global aspects and better algorithm may have a greater weight in different networks comprehensive consideration of the node’s local information (constraint coefficient) and globalinformation (closeness centrality Cc-Burt algorithm
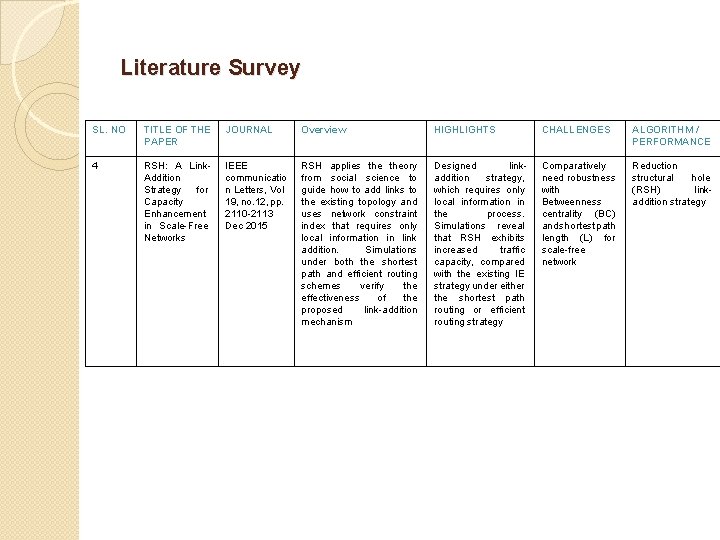
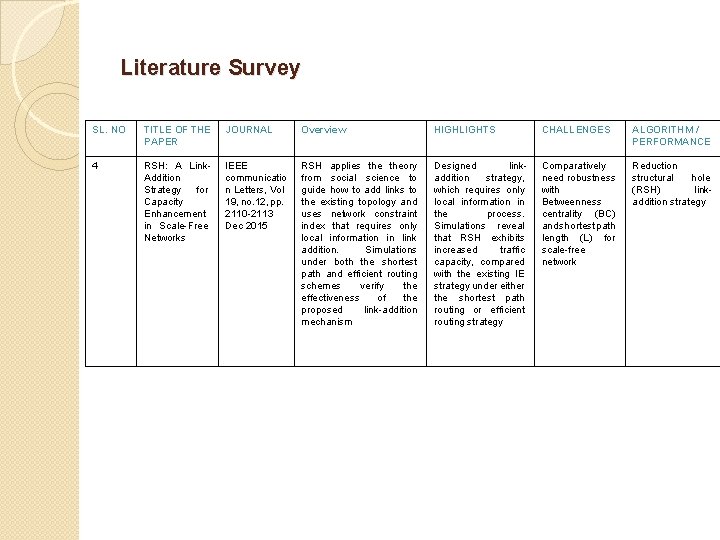
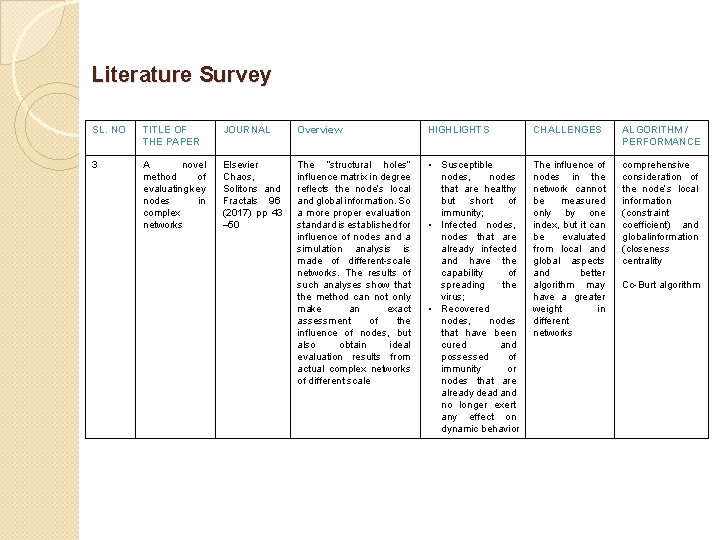
Literature Survey SL. NO TITLE OF THE PAPER JOURNAL Overview HIGHLIGHTS CHALLENGES ALGORITHM / PERFORMANCE 4 RSH: A Link. Addition Strategy for Capacity Enhancement in Scale-Free Networks IEEE communicatio n Letters, Vol 19, no. 12, pp. 2110 -2113 Dec 2015 RSH applies theory from social science to guide how to add links to the existing topology and uses network constraint index that requires only local information in link addition. Simulations under both the shortest path and efficient routing schemes verify the effectiveness of the proposed link-addition mechanism Designed linkaddition strategy, which requires only local information in the process. Simulations reveal that RSH exhibits increased traffic capacity, compared with the existing IE strategy under either the shortest path routing or efficient routing strategy Comparatively need robustness with Betweenness centrality (BC) and shortest path length (L) for scale-free network Reduction structural hole (RSH) linkaddition strategy
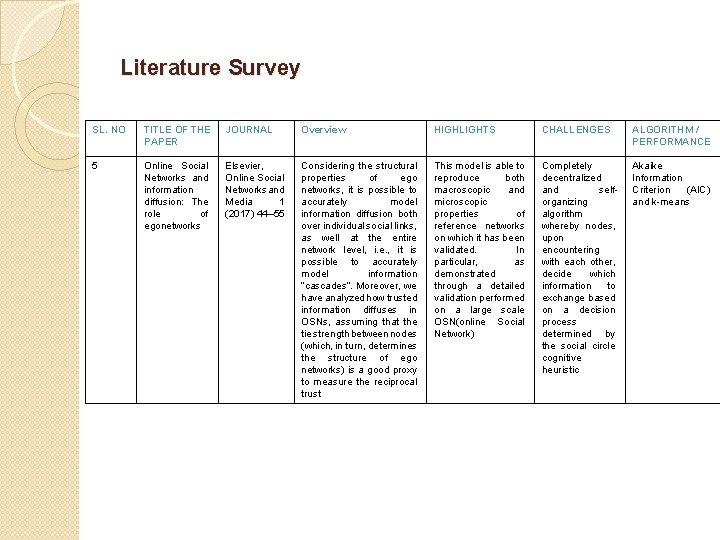
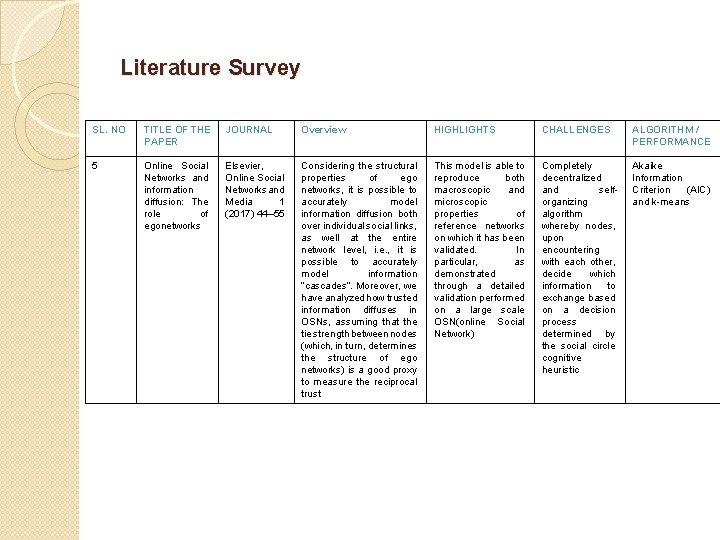
Literature Survey SL. NO TITLE OF THE PAPER JOURNAL Overview HIGHLIGHTS CHALLENGES ALGORITHM / PERFORMANCE 5 Online Social Networks and information diffusion: The role of egonetworks Elsevier, Online Social Networks and Media 1 (2017) 44– 55 Considering the structural properties of ego networks, it is possible to accurately model information diffusion both over individual social links, as well at the entire network level, i. e. , it is possible to accurately model information “cascades”. Moreover, we have analyzed how trusted information diffuses in OSNs, assuming that the tie strength between nodes (which, in turn, determines the structure of ego networks) is a good proxy to measure the reciprocal trust This model is able to reproduce both macroscopic and microscopic properties of reference networks on which it has been validated. In particular, as demonstrated through a detailed validation performed on a large scale OSN(online Social Network) Completely decentralized and selforganizing algorithm whereby nodes, upon encountering with each other, decide which information to exchange based on a decision process determined by the social circle cognitive heuristic Akaike Information Criterion (AIC) and k-means
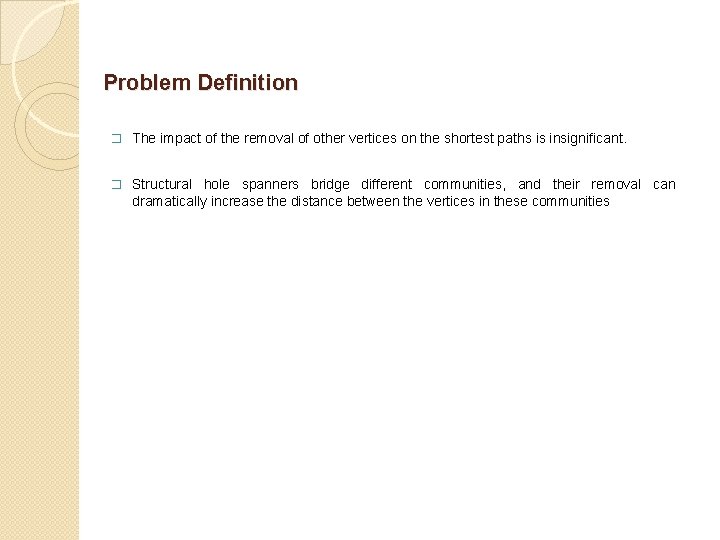
Problem Definition � The impact of the removal of other vertices on the shortest paths is insignificant. � Structural hole spanners bridge different communities, and their removal can dramatically increase the distance between the vertices in these communities
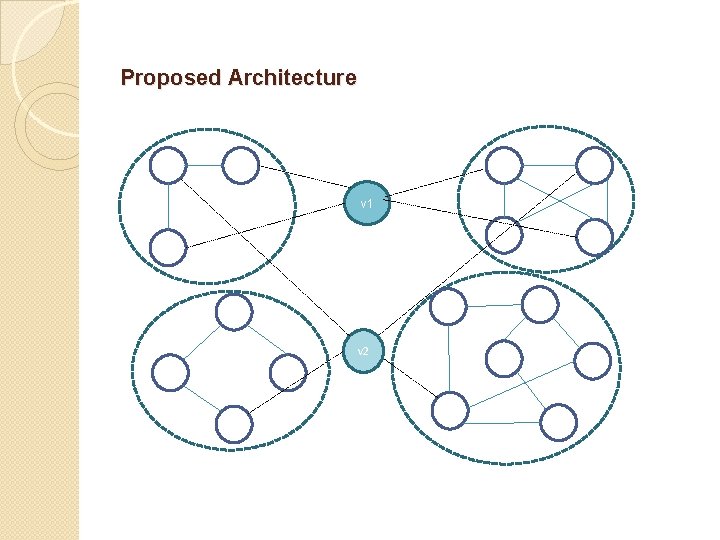
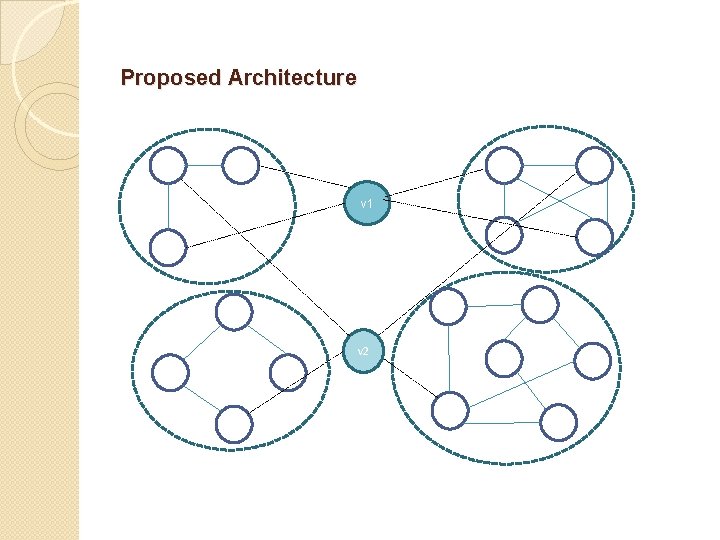
Proposed Architecture v 1 v 2
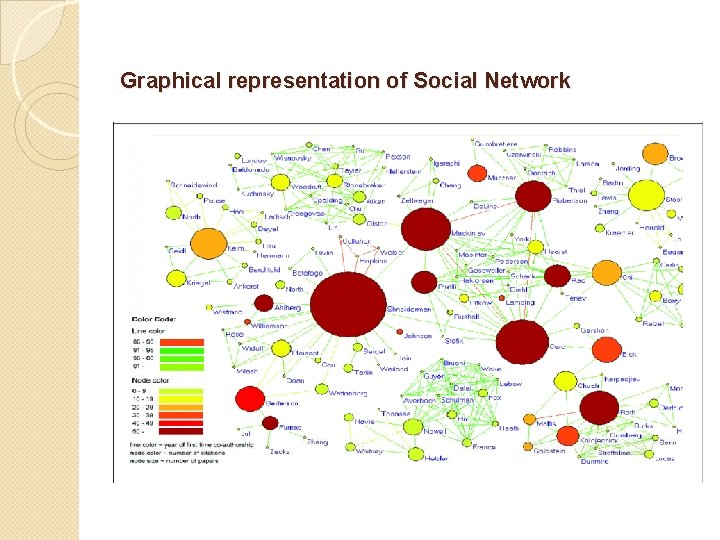
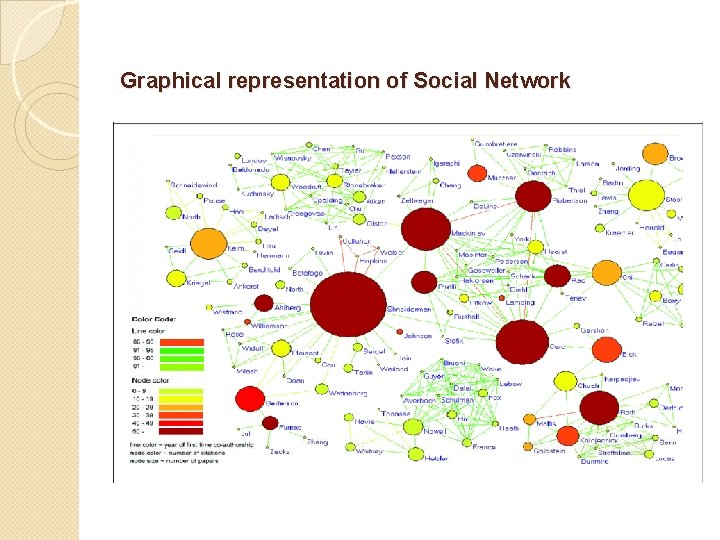
Graphical representation of Social Network
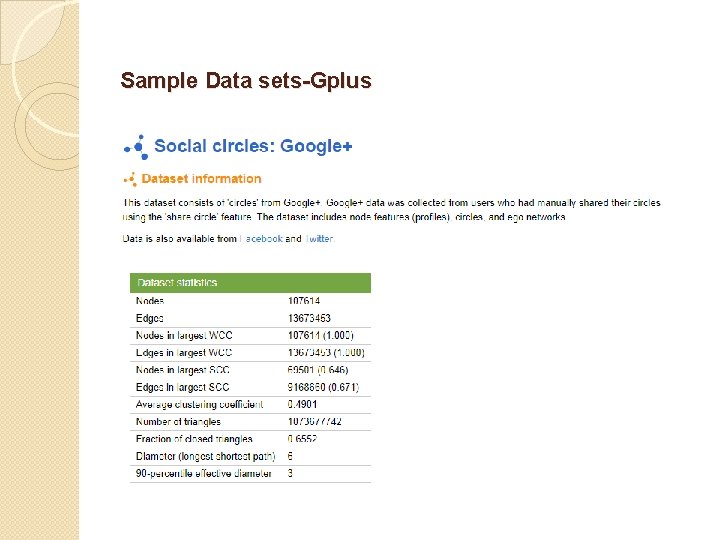
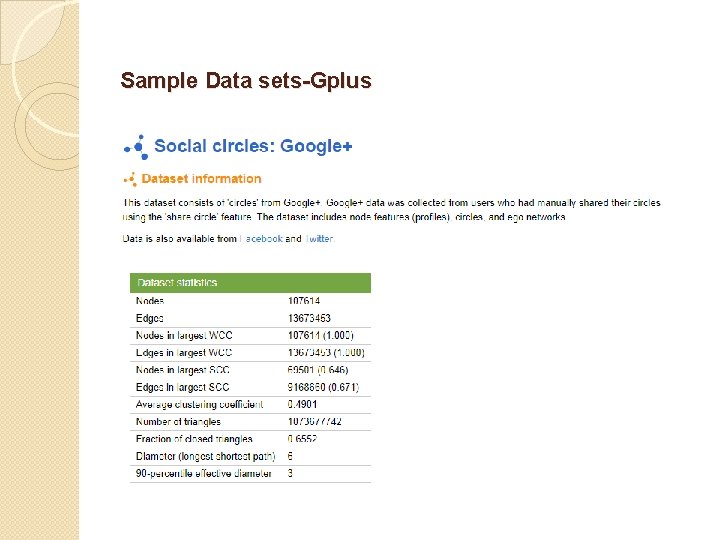
Sample Data sets-Gplus
Algorithm � Greedy algorithm: Greedy algorithms try to find a localized optimum solution, which may eventually lead to globally optimized solutions � Structure-hole-based influence maximization algorithm: The intuition behind SHIM is opinion leaders play a key role in spreading information within a community, while structure hole spanners are more important for spreading information between communities
Expected outcomes � The purposed method will identify the model that can capture the characteristics of structural hole spanners efficiently and decrease the link maintenance cost in the largescale networks. � Using k-means, SHIM found the optimal characteristics of structural hole spanners.
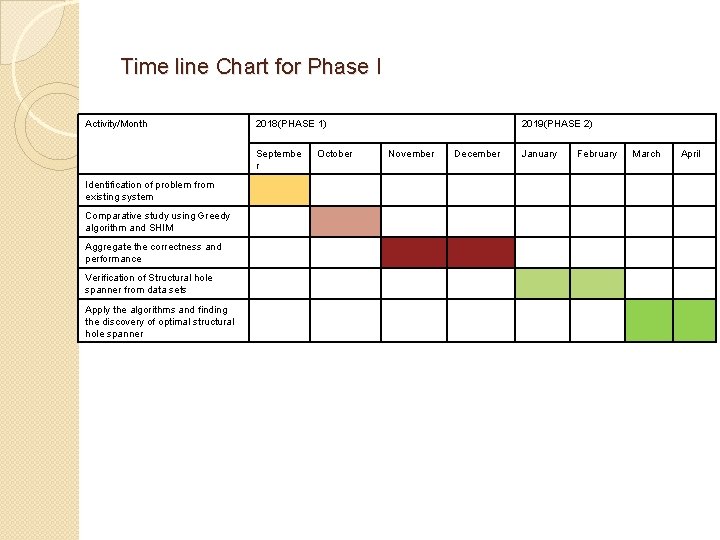
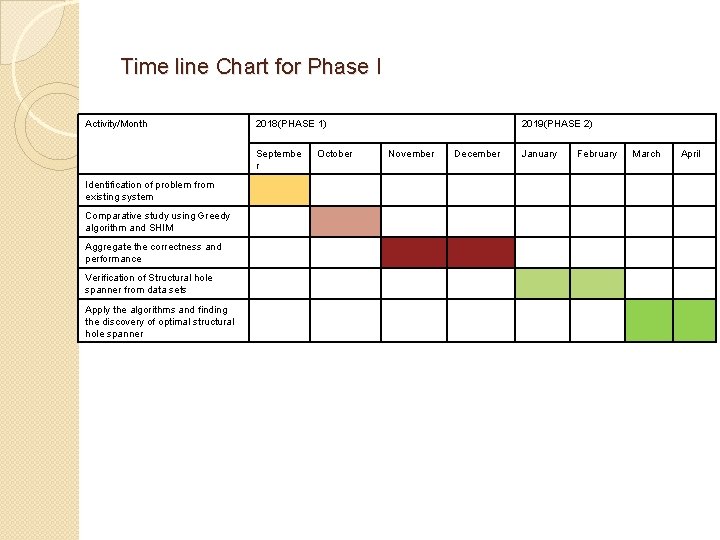
Time line Chart for Phase I Activity/Month 2018(PHASE 1) Septembe r Identification of problem from existing system Comparative study using Greedy algorithm and SHIM Aggregate the correctness and performance Verification of Structural hole spanner from data sets Apply the algorithms and finding the discovery of optimal structural hole spanner October 2019(PHASE 2) November December January February March April
![References 1 Wenzheng Xu Efficient Algorithms for the Identification of Topk Structural Hole References � [1] Wenzheng Xu, "Efficient Algorithms for the Identification of Top-k Structural Hole](https://slidetodoc.com/presentation_image_h2/9d543cf60ca9fc219d6b92caa6d6c0eb/image-17.jpg)
References � [1] Wenzheng Xu, "Efficient Algorithms for the Identification of Top-k Structural Hole Spanners in Large Social Networks" IEEE Transactions on Knowledge and data Engineering, Vol 29, no. 5, pp. 1027 -1030 May 2017 � [2] Libo Li, Frank Goethals, Bart Baesens, Monique Snoecka, "Predicting software revision outcomes on Git. Hub using structural holes theory" Elsevier, Computer Networks(2017) pp. 114 -124 � [3] Canshi Zhua, Xiaoyang Wang, Lin Zhuc, "A novel method of evaluating key nodes in complex networks" Elsevier Chaos, Solitons and Fractals 96 (2017) pp 43– 50 � [4] Dong Wang, Erwu Liu, Dong Liu, Xinyu Qu, Rufei Ma, Ping Wang, and Xingcheng Liu , "RSH: A Link-Addition Strategy for Capacity Enhancement in Scale-Free Networks", IEEE communication Letters, Vol 19, no. 12, pp. 2110 -2113 Dec 2015 � [5] Valerio Arnaboldi, Marco Conti, Andrea Passarellaa, Robin I. M. Dunbar, "Online Social Networks and information diffusion: The role of egonetworks", Elsevier, Online Social Networks and Media 1 (2017) pp. 44– 55 � [6] V. Arnaboldi, M. La Gala, A. Passarella, M. Conti, Information diffusion in distributed OSN: the impact of trusted relationships, Peer-to. Peer Netw. Appl. 9(6) (2016 a) 1195– 1208 � [7] J. Yang and J. Leskovec, “Defining and evaluating network communities based on ground-truth, ” Knowl. Inf. Syst. , vol. 42, pp. 181– 213, 2015. � [8] Y. Yu, H. Wang, V. Filkov, P. Devanbu, B. Vasilescu, Wait for it: determinants of pull request evaluation latency on Git. Hub, in: 2015 IEEE/ACM 12 th Working Conference on Mining Software Repositories (MSR), IEEE, 2015, pp. 367– 371. � [9] Y. Tang, Y. Shi, and X. Xiao, “Influence maximization in nearlinear time: A martingale approach, ” in Proc. 2015 ACM Int. Conf. Manage. Data, 2015, pp. 1539– 1554 � [10] F. Wang, H. Wang, K. Xu, Diffusive logistic model towards predicting information diffusion in online social networks, in: Proceedings of International Conference on Distributed Computing Systems, ICDCS Workshops, 2012, pp. 133– 139.
Appendix � https: //snap. stanford. edu/data/