DIGITAL FORENSICS AND LEGALITIES By Tyler Watson Overview
DIGITAL FORENSICS AND LEGALITIES By: “Tyler” Watson
Overview � � � What is digital forensics? Where is it used? What is the digital forensics process? How can data be hidden? How does the law view and handle encryption?
What is Digital Forensics? � � Recovery and investigation of material found in digital devices, often in relation to computer crime. Digital devices includes: � Hard drives � CDs and DVDs � Flash drives � Mobile phones � Basically anything which contains digital data
Where is Digital Forensics Used? � � U. S Secret Service Federal Bureau of Investigation State and Local Police departments Many other companies in the private sector
Digital Forensic Process � � � Step 1. ) Seizure – Collect the data. Step 2. ) Acquisition – Create an exact duplication of the data seized. Step 3. ) Analysis – Examine the copy and identify evidence that pertains to the case. Step 4. ) Reporting – Information regarding the investigation is written into a report. Number one rule: Preserve the Evidence!
How Can Data Be Hidden? � � Steganography – Images or other information hidden inside of a “carrier” image. Hidden Partitions – Small partitions in between other partitions. Encryption – Using an algorithm and key (aka: password) to change the data into an unreadable form. Advanced Techniques – Hex editors, securely deleting data, etc.

Spot the Difference
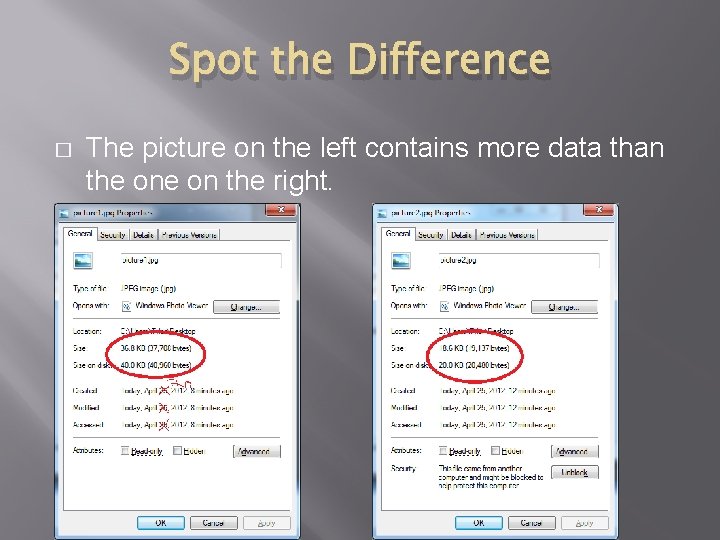
Spot the Difference � The picture on the left contains more data than the on the right.
Spot the Difference � Using super secret tools and a nearly unbreakable password (hint: it’s 1234) another picture was encrypted and hidden inside.
Legal Aspect � The government cannot force you to decrypt your personal files. � Falls � � under 5 th Amendment: “No self-incrimination” Some argue that this prevents law enforcement from doing their jobs. However, a recent case has begun to challenge this.
US v Fricosu � � � Ramona Fricosu – Colorado woman accused of fraudulent real estate transactions Government seized an encrypted laptop from her home Court was asked to compel Fricosu to turn over a decrypted version of her data. Court agreed and she was forced to decrypt her data by March 1, 2012. Is this ethical? Isn’t this against the 5 th Amendment?
Results of the Case � � Fricosu claimed she had forgotten the password. She did not decrypt the laptop by March 1, 2012. The feds decrypted the drive themselves using a brute force method. Although the court order ended up not being needed, a precedent was close to being set. Had the drive not been decrypted, Fricosu would have been found in contempt of court.
What do you think? � � Should the government be able to force you to decrypt your files? Is this against the 5 th Amendment of no selfincrimination?
References � � � TSM 441 – Dr. Bowman http: //www. cbsnews. com/stories/2005/03/04/national/main 67 8013. shtml http: //www. msnbc. msn. com/id/6988048/ns/us_newscrime_and_courts/t/computer-disk-may-have-cracked-btkcase/ http: //news. cnet. com/8301 -31921_3 -20078312 -281/doj-wecan-force-you-to-decrypt-that-laptop http: //www. huffingtonpost. com/2012/02/21/ramona-fricosucomputer-password_n_1291567. html http: //www. wired. com/threatlevel/2012/02/decryption-flapmooted/? utm_source=feedburner&utm_medium=feed&utm_ campaign=Feed%3 A+wired%2 Findex+%28 Wired%3 A+Inde x+3+%28 Top+Stories+2%29%29
- Slides: 14