Digital Forensics and Demonstration of Basic Forensic Techniques
Digital Forensics and Demonstration of Basic Forensic Techniques Jim Gordon MSc MBCS Worcester University 12 th Nov 2012 Digital Infrastructure
Format of the Presentation One hour presentation Examples Followed by two hours ‘Hands On’ Review/Wash up
Basic Principles Association of Chief Police Officers (ACPO) Guidelines on Computer Evidence. Establish the basic principles of acquiring evidence from computer systems. These principles accepted by the courts in the United Kingdom.
ACPO Principle 1 No action taken by the Police or their agents should change the data held on a computer or other media. Where possible computer data must be ‘copied’ and the copy examined.
ACPO Principle 2 • In exceptional circumstances it maybe necessary to access the original data held on a target computer. • However it is imperative that the person doing so is competent and can account for their actions.
ACPO Principles 3 An audit trail must exist to show all the processes undertaken when examining computer data Many forensic tools record logs of processes performed and results obtained
ACPO Principle 4 The onus rests with the person in charge of the case to show that a computer has been correctly examined in accordance with the law and accepted practice
Forensic Imaging Process Make a bit wise image of the contents of digital media Store the original media and carry out forensic analysis using the copy image If necessary to switch on suspect machine; Restore image to another drive and install it in suspects machine Or mount and start in a Virtual Machine Retrieve evidence in a readable form
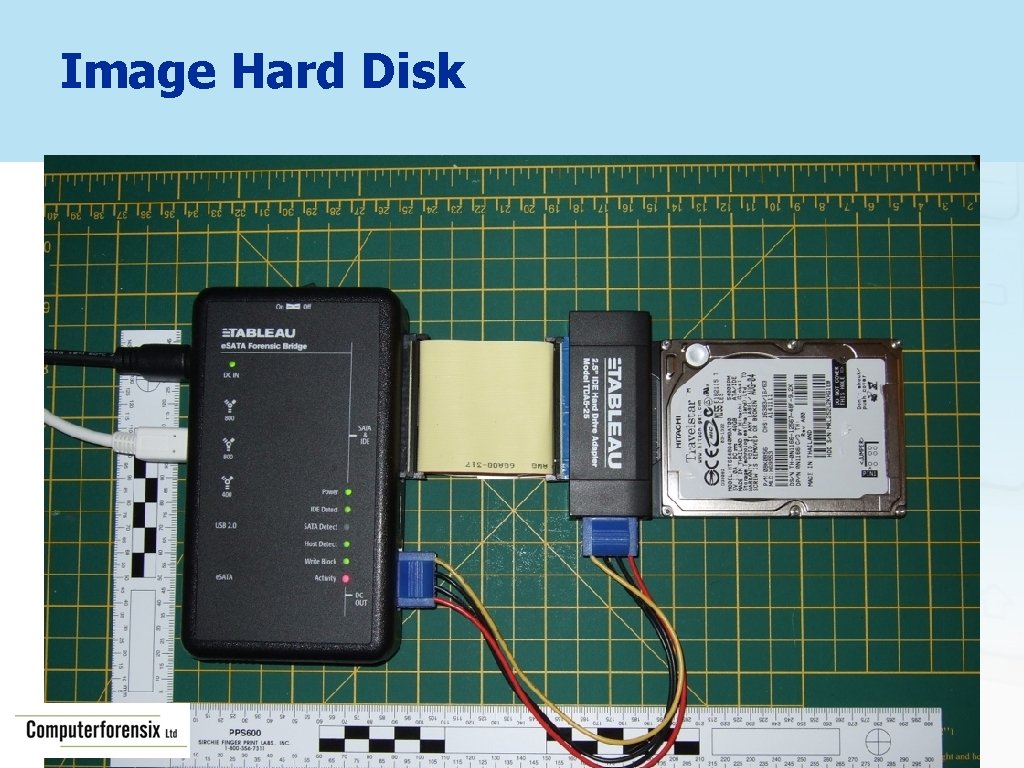
Image Hard Disk
Check BIOS Settings Disconnect hard drive(s) and switch on Check BIOS date and time Check machine specific settings

Image all other Storage Media
Mobile Phone and PDA Forensics Handset, Memory Card and SIM Card Examinations Handset Examination Logical Dump File System Dump Physical Dump JTAG Dump Chip OFF In certain cases, SIM Cloning a requirement

Global Positioning Systems Previous Destinations Sometimes a Route or Way Points Favourite Destinations Link to mobile phone - Bluetooth Contacts Addresses Phone numbers Owner Details - Home Address Unallocated - Previous Owners
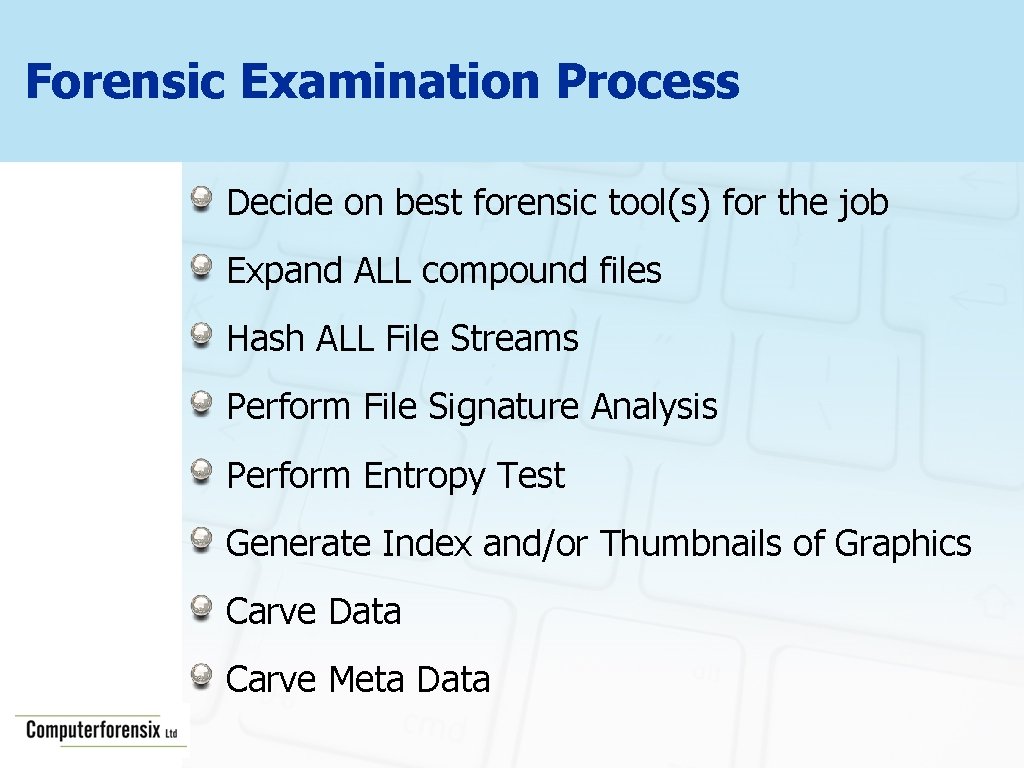
Forensic Examination Process Decide on best forensic tool(s) for the job Expand ALL compound files Hash ALL File Streams Perform File Signature Analysis Perform Entropy Test Generate Index and/or Thumbnails of Graphics Carve Data Carve Meta Data
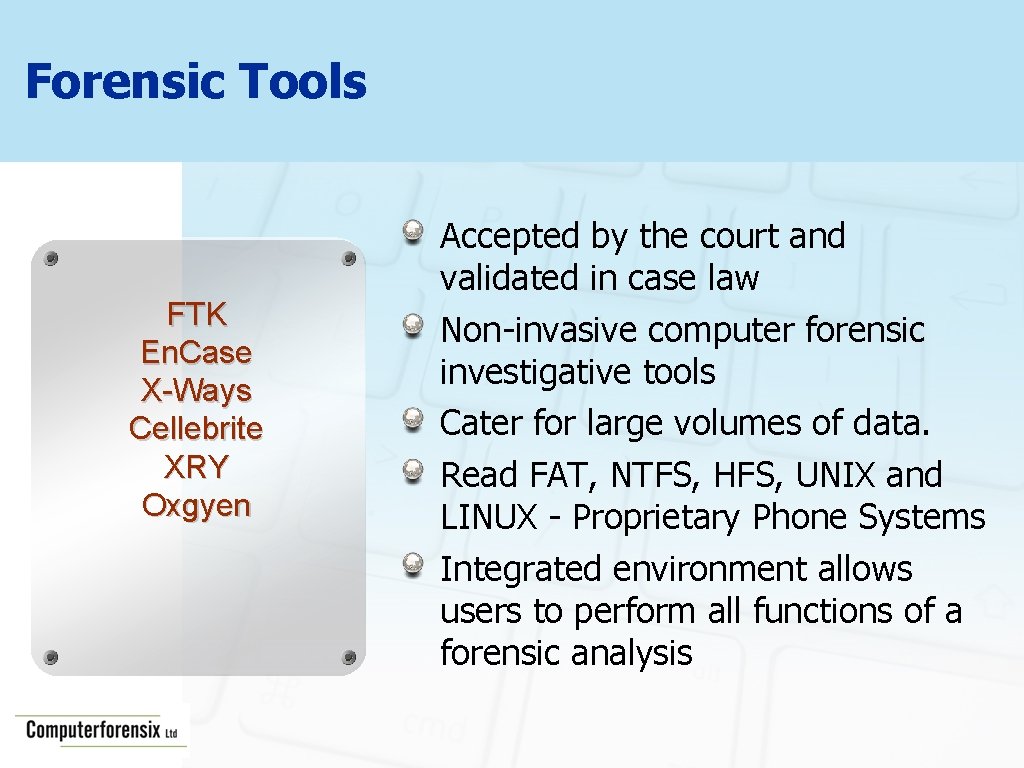
Forensic Tools FTK En. Case X-Ways Cellebrite XRY Oxgyen Accepted by the court and validated in case law Non-invasive computer forensic investigative tools Cater for large volumes of data. Read FAT, NTFS, HFS, UNIX and LINUX - Proprietary Phone Systems Integrated environment allows users to perform all functions of a forensic analysis
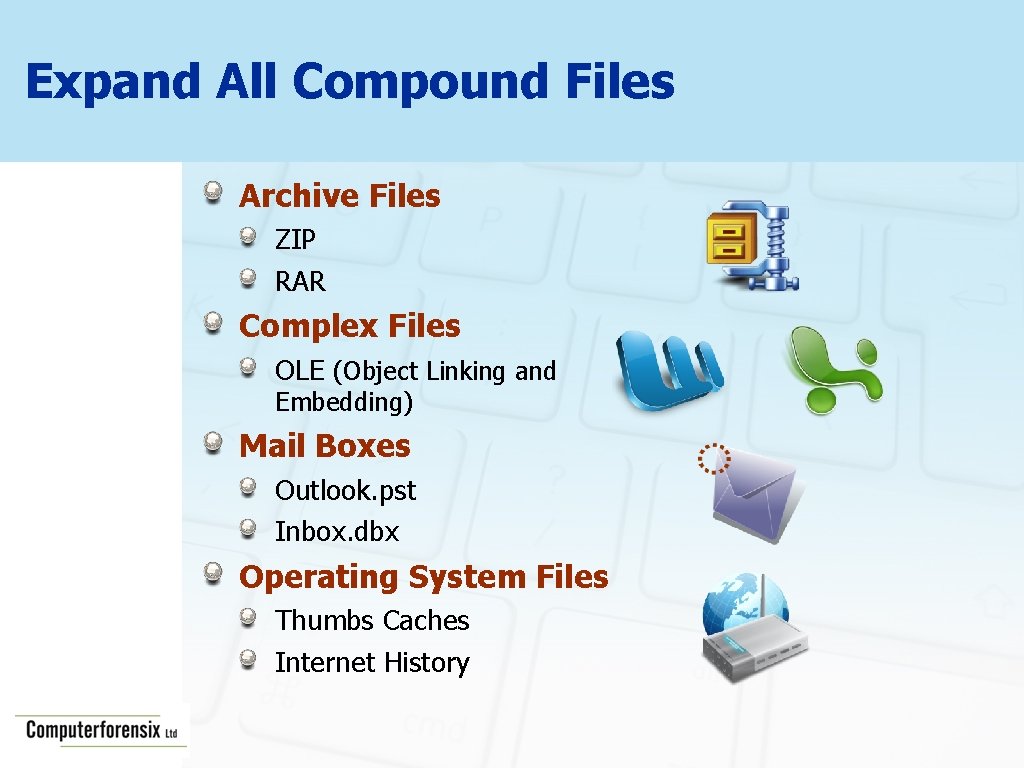
Expand All Compound Files Archive Files ZIP RAR Complex Files OLE (Object Linking and Embedding) Mail Boxes Outlook. pst Inbox. dbx Operating System Files Thumbs Caches Internet History
Hash All File Streams (Message “This. MD 5 is a small. Digest text 5) file. ” Generates a unique 128 Bit value for each file or data stream: Example MD 5 Hashes. MD 5 = a 08 a 8 cf 89436 f 18 ea 8084817357 a 59 c 1 MD 5 = 271979 ddf 56 c 38805 b 7562046984 fe 40 An MD 5 Hash can “This is a small text file” be used to: Identify Files to be ignored (OS Files). Identify Files of importance (Contraband Files).
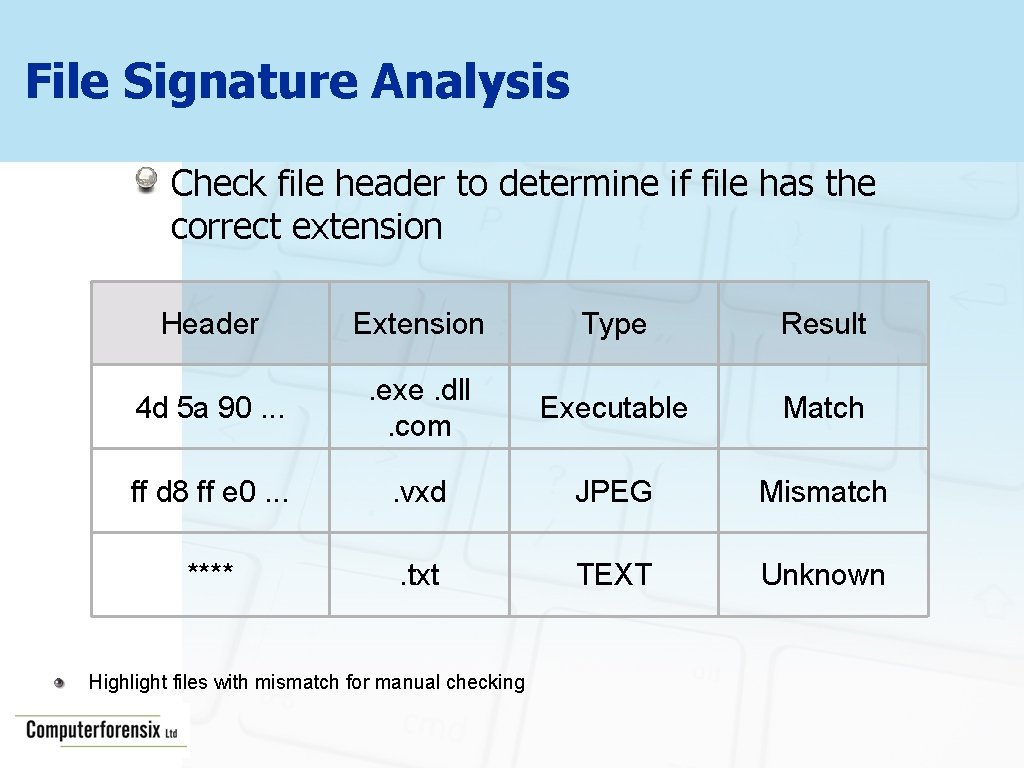
File Signature Analysis Check file header to determine if file has the correct extension Header Extension Type Result 4 d 5 a 90. . exe. dll. com Executable Match ff d 8 ff e 0. . vxd JPEG Mismatch **** . txt TEXT Unknown Highlight files with mismatch for manual checking
Entropy Test Can identify files that may be encrypted or compressed An automated frequency analysis algorithm is used to determine if file content is encrypted Files identified are then exported from the image and transferred to specialist decryption software
Generate Index Generate an index of all strings of characters in the disk image Speed up subsequent searches of suspect image Index can be used as a dictionary for password cracking
GREP (General Regular Expressions) GREP can be utilised for ‘fuzzy’ searching or pattern matching <[456]ddd([- ]? dd){3}> Above expression will find credit card numbers
Optical Character Recognition Making Text in Pictures Searchable
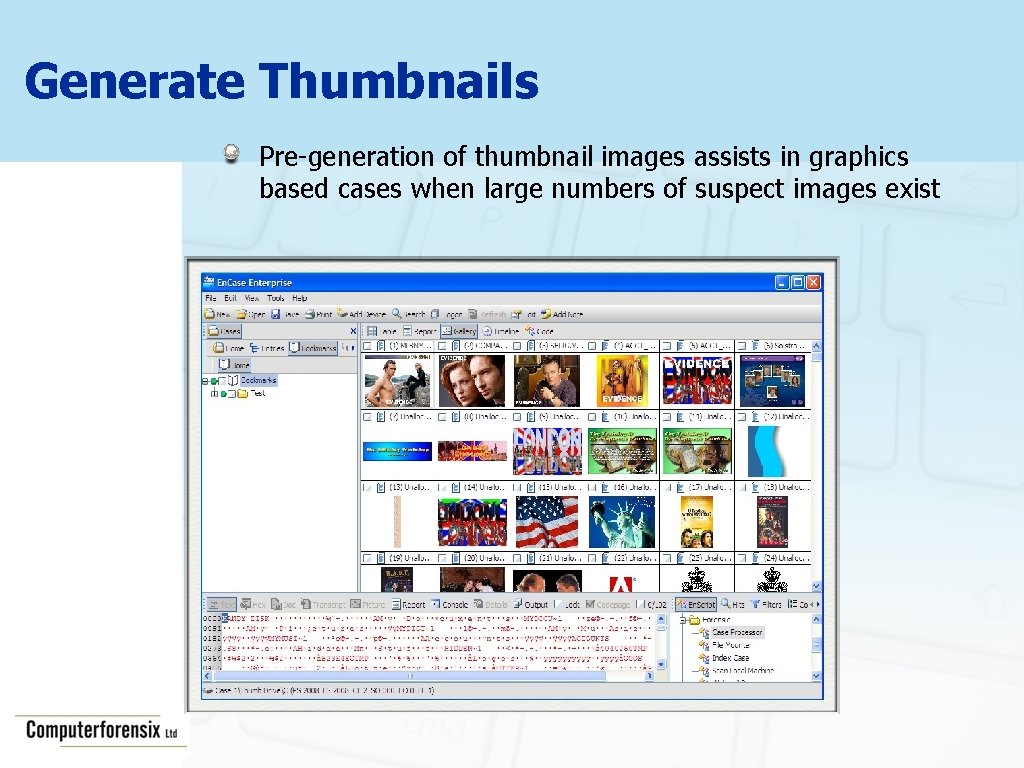
Generate Thumbnails Pre-generation of thumbnail images assists in graphics based cases when large numbers of suspect images exist
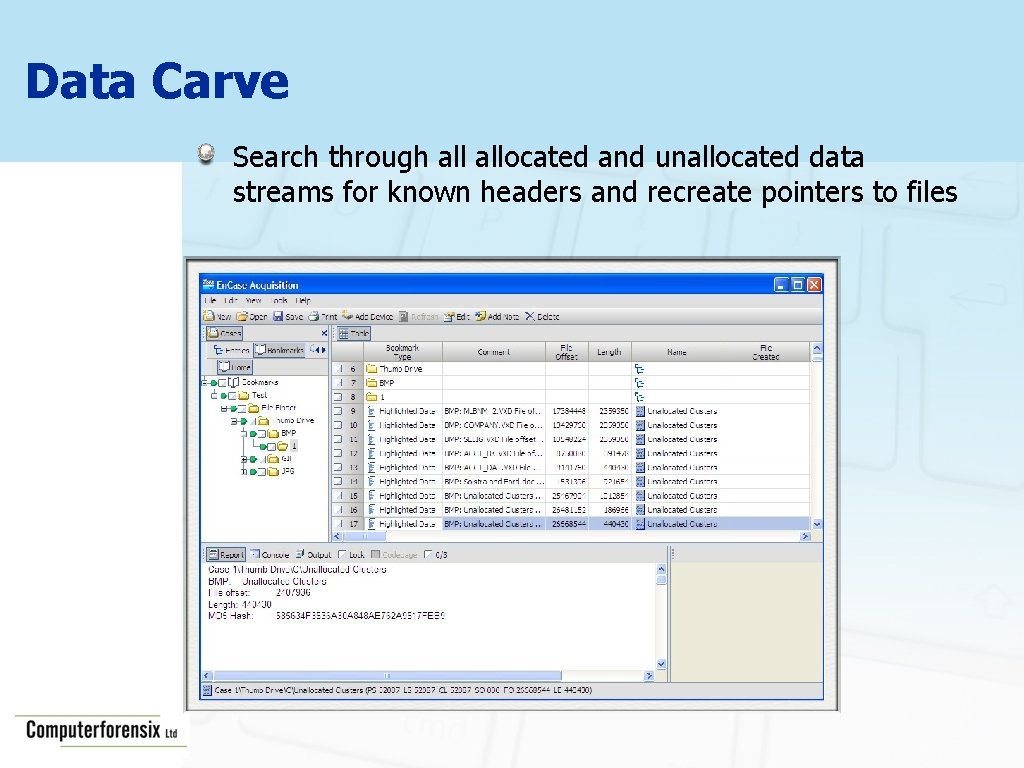
Data Carve Search through allocated and unallocated data streams for known headers and recreate pointers to files
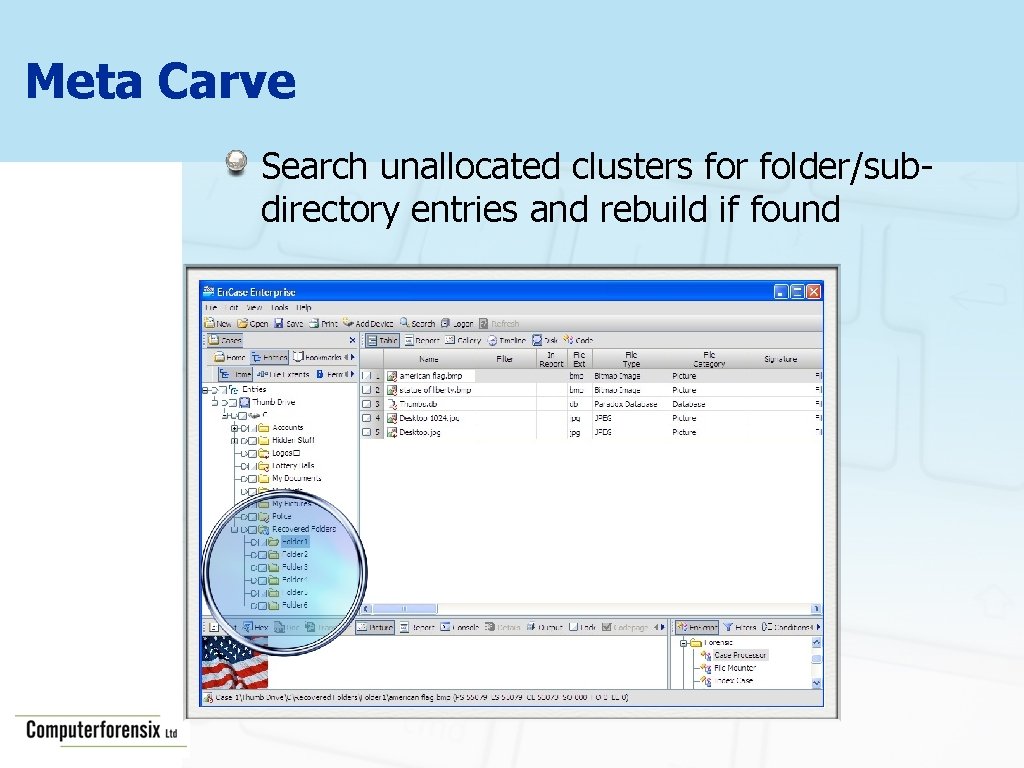
Meta Carve Search unallocated clusters for folder/subdirectory entries and rebuild if found
What happens when a file is deleted? The Windows operating system tracks files (user data) using either a File Allocation Table or a Master File Table. In simple terms, the FAT or MFT tells the computer where the file begins and ends. Macintosh uses a similar system known as Nodes.
What happens when a file is deleted? When a file is deleted, the operating system deletes the pointers to the file and in the FAT or MFT the space occupied by the file is mark as available. The computer does not delete the actual data that was contained in the file.
Recycle Bin Forensics Hidden System Folder Win 95/98 called Recycled Win 2 K, NT/XP/2003 called Recycler Hidden system file named INFO 2 contains Original Filename, Deleted Date & Time Vista/Win 7 $Recycle. bin Original Filename, Deleted Date & Time contained in separate files for each deleted record
Examination of the Recycle Bin Most forensic tools will parse the data from the INFO 2 file
FDISK What happens when someone FDisks drive to remove a Partition? The 16 bytes for the partition entry within the MBR are zeroed The actual partition including its data are untouched
FDISK Partition recovery is simple Locate VBR Forensic Software will recover the Partition including directory structure
Re. Format What happens when you reformat a drive to delete data?
Digital Forensics and Demonstration of Basic Forensic Techniques Jim Gordon MSc MBCS Worcester University 12 th Nov 2012 Digital Infrastructure
- Slides: 33