Digital Evidence Stephen Mason Barrister Visiting Research Fellow
Digital Evidence • Stephen Mason, Barrister • Visiting Research Fellow • Director, Digital Evidence Research Programme • The content of this presentation is the copyright of Stephen Mason, 2006
The digital way we live now • The nature of our changing world • The effects on our lives • The nature of the evidence
The nature of our changing world
The meaning of words • The following definitions are taken from the Wikipedia
Analogue ‘An analog(ue) computer is a form of computer that uses electrical or mechanical phenomena to model the problem being solved by using one kind of physical quantity to represent another. ’ Examples: vinyl records, audio tape, photographic film, telephone calls made over the public switched telephone network, and human-readable paper documents
Digital ‘A digital system is one that uses discrete numbers, especially binary numbers, or non-numeric symbols such as letters or icons, for input, processing, transmission, storage, or display, rather than a continuous spectrum of values (an analog system)…. The word digital is most commonly used in computing and electronics, especially where real-world information is converted to binary numeric form as in digital audio and digital photography. Such data-carrying signals carry either one of two electronic or optical pulses, logic 1 (pulse present) or 0 (pulse absent). The term is often meant by the prefix “e-”, as in e-mail and ebook, even though not all electronics systems are digital. ’ Examples: anything that has been created or stored on a computer, or is made available by way of the internet, including CDs, DVDs, MP 3 s and digital broadcast radio
Electronic ‘Electronic document means any computer data (other than programs or system files) that are intended to be used in their computerized form, without being printed (although printing is usually possible). ’ ‘electronic’ includes any information, whether it is in analogue or digital form that is carried by an electrical conductor
The nature of evidence is changing • Increased use of computers in all their various forms • Introduction of networked communications and ubiquitous computing; trusted computing is not far away facsimile transmissions; voice over internet protocol (Vo. IP); e -mail; internet; computer to computer (P 2 P); instant messaging; MP 3 files; blogs; computers; laptop computers; newsgroups; chat networks; mobile telephones with text messaging and cameras; personal digital assistants; Blackberry; i. PAQ; content management systems, etc, etc
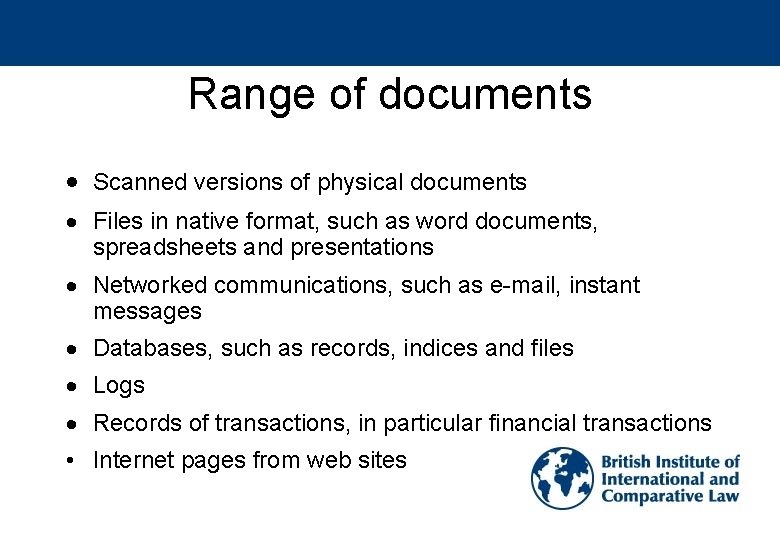
Range of documents Scanned versions of physical documents Files in native format, such as word documents, spreadsheets and presentations Networked communications, such as e-mail, instant messages Databases, such as records, indices and files Logs Records of transactions, in particular financial transactions • Internet pages from web sites
The effects on our lives
Before proceedings • Retention of documents: duties arising • Pre-proceedings: destruction of documents
![The tests: Australia Mc. Cabe v British American Tobacco Australia Services Ltd [2002] VSC The tests: Australia Mc. Cabe v British American Tobacco Australia Services Ltd [2002] VSC](http://slidetodoc.com/presentation_image/08d84b7ec7386eacd064b820d9eb1d6c/image-12.jpg)
The tests: Australia Mc. Cabe v British American Tobacco Australia Services Ltd [2002] VSC 73; [2002] VSCA 197 Where documents are destroyed before the commencement of litigation • They may attract a sanction (other than the drawing of adverse inferences) if that conduct amounts to: — an attempt to pervert the course of justice, or — (if open) contempt of court, meaning criminal contempt • ‘Such a test seems to sit well with what has been said in the United States as well as what has been said in England’
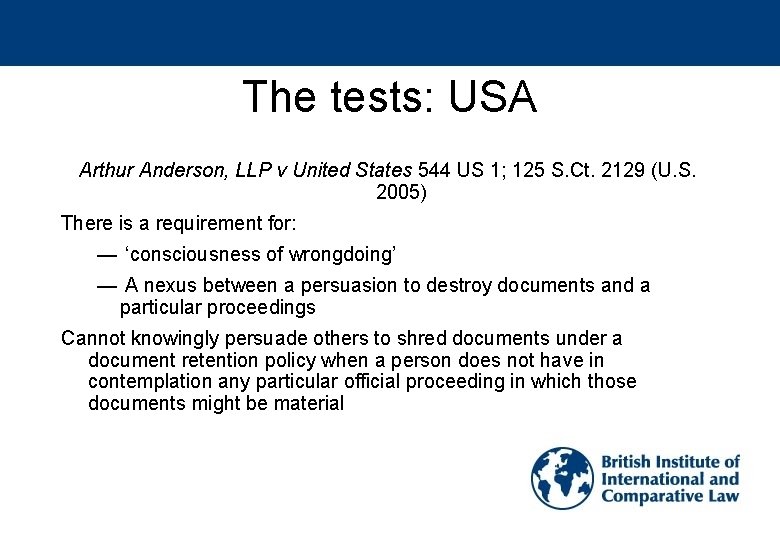
The tests: USA Arthur Anderson, LLP v United States 544 US 1; 125 S. Ct. 2129 (U. S. 2005) There is a requirement for: — ‘consciousness of wrongdoing’ — A nexus between a persuasion to destroy documents and a particular proceedings Cannot knowingly persuade others to shred documents under a document retention policy when a person does not have in contemplation any particular official proceeding in which those documents might be material
England Wales The decision in the Court of Appeal in Mc. Cabe was approved and followed by Mr Justice Lloyd in Douglas, Zeta-Jones and Northern Shell plc v Hello! Limited, Hola SA and others [2003] 1 All ER 1087; [2003] EWHC 55 (Ch)
When the duty arises • Cresswell Report: Electronic Disclosure (2004) – Once litigation is contemplated – When litigation has commenced • Follows US view and reflects the general practice of solicitors
Costs of electronic disclosure Zubulake v UBS Warburg LLC, 217 F. R. D. 309 (S. D. N. Y. 2003); 216 F. R. D. 280 (S. D. N. Y. 2003); Wiginton v. CB Richard Ellis Inc. , 229 F. R. D. 568 (N. D. Ill. 2004) 1. the likelihood of discovering critical information; 2. the availability of such information from other sources; 3. the amount in controversy as compared to the total cost of production; 4. the parties’ resources as compared to the total cost of production; 5. the relative ability of each party to control costs and its incentive to do so; 6. the importance of the issues at stake in the litigation; 7. the importance of the requested discovery in resolving the issues at stake in the litigation; and 8. the relative benefits to the parties of obtaining the information.
Suggested analysis by Judge Scheindlin 1. The adjudicator needs to thoroughly understand the responding party’s computer system, both with respect to active and stored data. 2. The sensible approach is to require the responding party to restore and produce documents from a small sample of back-up tapes. 3. In dealing with whether costs should be shifted between the parties, the seven-factor test should be considered, weighted in order of ascendancy.
Applying the law and relevant principles • Electronic signatures
Contract and e-signatures: computer documents Wilkens v Iowa Insurance Commissioner, Wilkens v Allstate Insurance 457 N. W. 2 d (Iowa App. 1990) An insurance agent, Larry Hertel, issued policies of insurance and provided a signature by typing his name into the policy document on the computer Held: Typing a name into a document on a computer was determined to be a signature under the provisions of the Iowa Code section 4. 1(17)
Contract and e-signatures: e-mail Hall v Cognos Limited Case No 1803325/97 Cognos had a policy: all expenses over 6 months old would not be paid Mr Hall failed to submit his expenses on time By January 1997 he wanted paying, and a series of e-mails were exchanged between him, HR and his line manager Mr Hall asked is late submission was “OK with you? ” and his line manager replied “Yes, it is OK” Inflating his claim, Cognos dismissed him without paying his expenses He made a claim for unfair dismissal
Stretching the boundaries? United States of America USA v Siddiqui, 235 F. 3 d 1138 (11 th Cir. 2000) Greece 1327/2001 – Payment Order Australia Mc. Guren v Simpson [2004] NSWSC 35 Italy Tribunale Mondovì, 7 giugno 2004, n. 375 (decr. ), Giur. It. 2005, 1026 Singapore SM Integrated Transware Ltd v Schenker Singapore (Pte) Ltd [2005] 2 SLR 651, [2005] SGHC 58 England Wales J Pereira Fernandes SA v Mehta [2006] 1 WLR 1543, [2006] 2 All ER 891, Ch D, [2006] 1 All ER (Comm) 885, [2006] All ER (D) 264 (Apr), [2006] IP & T 546, The Times 16 May 2006, [2006] EWHC 813 (Ch)
The nature of digital evidence
Justifying an investigation Miseroy v Barclays Bank plc Case No 1201894/2004 E-mails were exchanged between Mr Miseroy and a manager about buying cannabis “I’ve brought it with me. Fag-break about 10. 30? ” Mr Miseroy also carried out quality assurance: In an e-mail sent on 18 February, he asked “quality ok? ” Mr Miseroy also disclosed confidential information regarding Barclay’s operations and customers
Preliminary stage • Practical issue: whether to call in an expert • Whether expert evidence will be tested • Determining guidance to parties in searching for relevant documents at the disclosure stage • Dealing with claims of cost in disclosure exercises • How to prepare for disclosure - should it agreed between the parties through their lawyers? • Type of format required - is the format in issue?
In court • Presenting the evidence to the jury, if a criminal trial • Explaining the evidence • Dealing with defences, such as the Trojan horse defence • Challenging the evidence of the expert and the underlying software used in the process of examining the computer • Challenging the effect that the method of presentation might have on a jury
Laying the foundations In re Vee Vinhnee, Debtor American Express Travel Related Services Company, Inc. v Vee Vinhnee 336 B. R. 437 (9 th Cir. BAP 2005) • The trial judge declined to admit the plaintiff’s computerized business records • The records were not adequately authenticated at trial: – The witness was not qualified sufficiently – The witness did not have the requisite degree of expertise in a range of areas relating to the nature of the computer equipment and software – There was no evidence that the business conducted its operations in reliance upon the accuracy of the computer in retaining and retrieving the information in question • The technical and organizational issues were not addressed • American Express failed, when offered the opportunity, to rectify the lack of evidential foundations
Pertinent observations • The primary authenticity issue in the context of business records is on what has, or may have, happened to the record in the interval between when it was placed in the files and the time of trial • In other words, the record being proffered must be shown to continue to be an accurate representation of the record that was originally created • The focus is on the circumstances of the preservation of the record during the time it is in the file, to provide assurance that the document being proffered is the same as the document that was originally created
The difference in format is irrelevant • Evidence may be required to demonstrate that the record is what it purports to be • The logical questions extend beyond the identification of the particular computer equipment and programs used • Pertinent points to determine whether records have been changed since their creation include: – Relevant policies and procedures for the use of the equipment, database, and programs – How access to the pertinent database is controlled – How access to the specific program is controlled – How changes in the database are logged or recorded – The structure and implementation of backup systems and audit procedures for assuring the continuing integrity of the database
Judicial notice • American Express contended that the court was required, as a matter of law, of taking judicial notice of the accuracy and reliability of their computer systems • However, in the USA, the Manual for Complex Litigation(4 th edn) § 11. 446 (2004) notes that a judge should ‘consider the accuracy and reliability of computerized evidence’ and that a ‘proponent of computerized evidence has the burden of laying a proper foundation by establishing its accuracy’ • Observation by the appellate judges (Klein, Montali, and Perris, Bankruptcy Judges): it is becoming recognized that early versions of computer foundations were too cursory
Suggested framework • The evidence needs to be assessed with respect to: – Reliability – Integrity – Useability Each of which can provide for the authenticity • Which in turn needs to take into account: – The machine – Operating and Application software – Storage medium – Retrieval – Alteration and detection of alteration – Management of dependencies
Stephen Mason • British Institute of International and Comparative Law • • • Main publications: Electronic Signatures in Law (Lexis. Nexis Butterworths, 2003) E-mail, networks and the internet: a concise guide to compliance with the law (xpl publications, 6 th edn, 2006) • General Editor of the Digital Evidence Journal incorporating the e-Signature Law Journal http: //www. digitalevidencejournal. org Litigation Management: E is for E-disclosure http: //www. legalit. net/View. Item. asp? id=25185 http: //www. biicl. org stephenmason@stephenmason. co. uk • • •
- Slides: 31