DHS SCIENCE AND TECHNOLOGY Applying Cyber Innovation for
DHS SCIENCE AND TECHNOLOGY Applying Cyber Innovation for More Resilient Health Systems November 1, 2017 Douglas Maughan Cyber Security Division Director
S&T MISSION To deliver effective and innovative insight, methods and solutions for the critical needs of the Homeland Security Enterprise. 2
DHS and Cybersecurity MISSION 4: SAFEGUARD AND SECURE CYBERSPACE Goal 1: Strengthen the Security and Resilience of Critical Infrastructure Goal 2: Secure the Federal Civilian Government Information Technology Enterprise Goal 3: Advance Law Enforcement, Incident Response, and Reporting Capabilities Goal 4: Strengthen the Ecosystem • Drive innovative/cost effective security products, services, and solutions in the cyber ecosystem; • Conduct and transition research and development enabling trustworthy cyber infrastructure; • Develop skilled cybersecurity professionals; • Enhance public awareness and promote cybersecurity best practices; and • Advance international engagement to promote capacity building, international standards, and cooperation. 3

Research Requirement Inputs DEPARTMENT INPUTS INTERAGENCY COLLABORATIOIN CYBERSECURITY R&D CRITICAL INFRASTRUCTURE SECTORS (PRIVATE SECTOR) WHITE HOUSE & NSS STATE & LOCAL INTERNATIONAL PARTNERS 4
CSD Mission & Strategy • • • Aviation Cybersecurity Cyber for Critical Infrastructure Cyber Physical Systems Security Cyber Risk Economics Cyber Security for Law Enforcement Cybersecurity Outreach Cyber. Gov Data Privacy Technologies Identity Management Homeland Security Open Source Technologies • Human Aspects of Cyber Security • Mobile Security • Next Gen. Cyber Infrastructure Apex Cyber for Critical Infrastructure Cyber Security for Law Enforcement • Network System Security Cybersecurity Outreach • Research Infrastructure Cyber Physical Systems • Silicon Valley Innovation Program Data Privacy Technologies • Software Assurance Identity Management Homeland Security Open Source Technologies • Transition to Practice § Develop and deliver new technologies, tools and techniques to defend and secure current and future systems and networks § Conduct and support technology transition efforts § Provide R&D leadership and coordination within the government, academia, private sector and international cybersecurity community 5
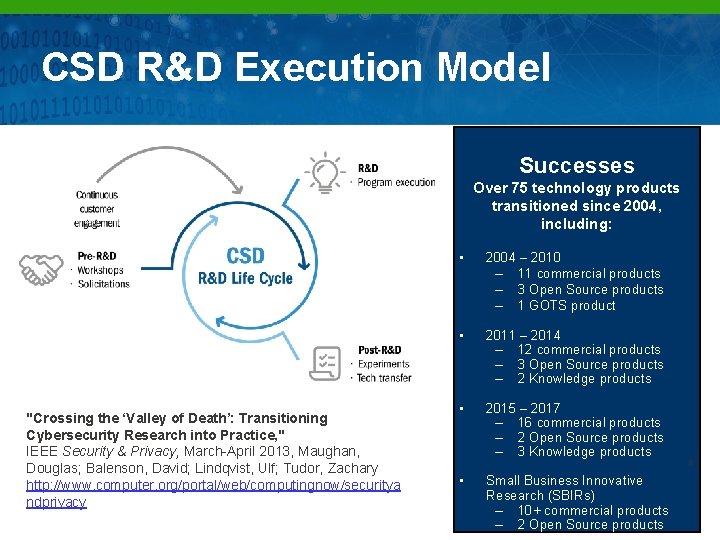
CSD R&D Execution Model Successes Over 75 technology products transitioned since 2004, including: "Crossing the ‘Valley of Death’: Transitioning Cybersecurity Research into Practice, " IEEE Security & Privacy, March-April 2013, Maughan, Douglas; Balenson, David; Lindqvist, Ulf; Tudor, Zachary http: //www. computer. org/portal/web/computingnow/securitya ndprivacy • 2004 – 2010 – 11 commercial products – 3 Open Source products – 1 GOTS product • 2011 – 2014 – 12 commercial products – 3 Open Source products – 2 Knowledge products • 2015 – 2017 – 16 commercial products – 2 Open Source products – 3 Knowledge products • Small Business Innovative Research (SBIRs) – 10+ commercial products – 2 Open Source products 6
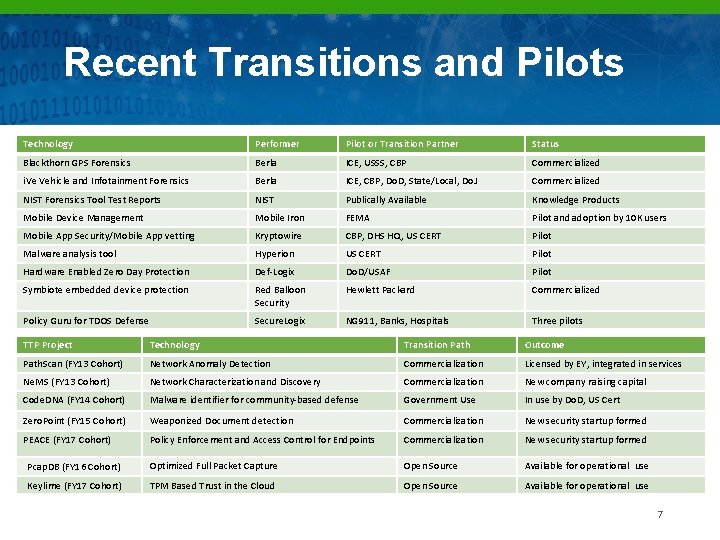
Recent Transitions and Pilots Technology Performer Pilot or Transition Partner Status Blackthorn GPS Forensics Berla ICE, USSS, CBP Commercialized i. Ve Vehicle and Infotainment Forensics Berla ICE, CBP, Do. D, State/Local, Do. J Commercialized NIST Forensics Tool Test Reports NIST Publically Available Knowledge Products Mobile Device Management Mobile Iron FEMA Pilot and adoption by 10 K users Mobile App Security/Mobile App vetting Kryptowire CBP, DHS HQ, US CERT Pilot Malware analysis tool Hyperion US CERT Pilot Hardware Enabled Zero Day Protection Def-Logix Do. D/USAF Pilot Symbiote embedded device protection Red Balloon Security Hewlett Packard Commercialized Policy Guru for TDOS Defense Secure. Logix NG 911, Banks, Hospitals Three pilots TTP Project Technology Transition Path Outcome Path. Scan (FY 13 Cohort) Network Anomaly Detection Commercialization Licensed by EY, integrated in services Ne. MS (FY 13 Cohort) Network Characterization and Discovery Commercialization New company raising capital Code. DNA (FY 14 Cohort) Malware identifier for community-based defense Government Use In use by Do. D, US Cert Zero. Point (FY 15 Cohort) Weaponized Document detection Commercialization New security startup formed PEACE (FY 17 Cohort) Policy Enforcement and Access Control for Endpoints Commercialization New security startup formed Pcap. DB (FY 16 Cohort) Optimized Full Packet Capture Open Source Available for operational use Keylime (FY 17 Cohort) TPM Based Trust in the Cloud Open Source Available for operational use 7
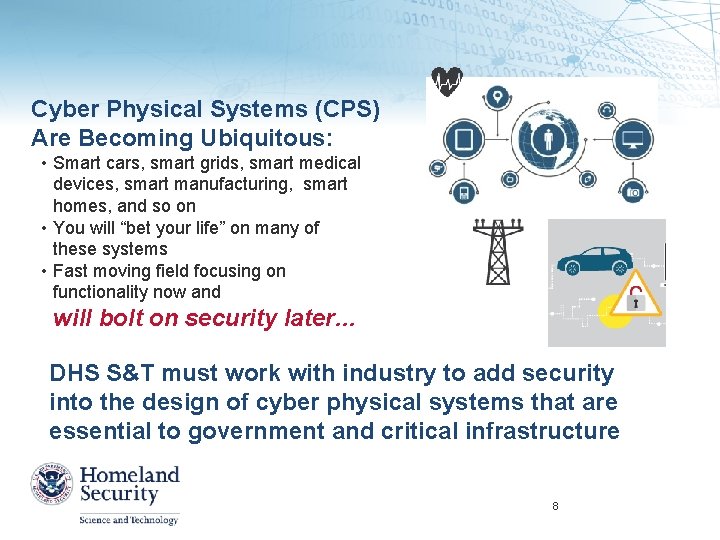
Cyber Physical Systems (CPS) Are Becoming Ubiquitous: • Smart cars, smart grids, smart medical devices, smart manufacturing, smart homes, and so on • You will “bet your life” on many of these systems • Fast moving field focusing on functionality now and will bolt on security later… DHS S&T must work with industry to add security into the design of cyber physical systems that are essential to government and critical infrastructure 8

CPS GAPS AND OPPORTUNITIES Internet Design Goals CPS Design Goals Being Set Now ARPAnet design goals (Clark, 1988) • Function despite loss of networks/gateways • Support multiple types of services • Accommodate a variety of networks • Distributed management of resources • Cost effective • Low level of effort to add a host • Provide accounting of resources used Security will NOT emerge on its own Led to today’s challenges in accounting (last goal) and lack of security (non-goal) Build Security In Promote security at onset Connect research and industry Enable security as an integral component 9
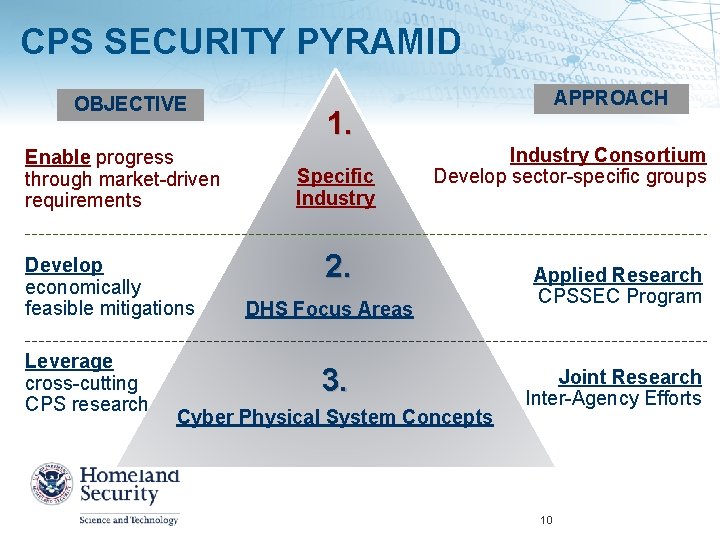
CPS SECURITY PYRAMID OBJECTIVE Enable progress through market-driven requirements Develop economically feasible mitigations Leverage cross-cutting CPS research APPROACH 1. Specific Industry Consortium Develop sector-specific groups 2. DHS Focus Areas 3. Cyber Physical System Concepts Applied Research CPSSEC Program Joint Research Inter-Agency Efforts 10
PRE-COMPETITIVE AUTOMOTIVE CYBERSECURITY RESEARCH § Automotive Cybersecurity Industry Consortium (ACIC) § Voluntary and technology-oriented Public Private Partnership (PPP) consortium § Automotive OEMs with support from DHS S&T CSD and the DOT-Volpe Center § OEMs can pool resources and leverage them with government funding § Cooperative “Pre-Competitive Research” (PCR) to improve the level of cybersecurity in automobiles § Projects identified and selected by consortium members provide mutual benefit by reducing the threat of cybersecurity risks 11
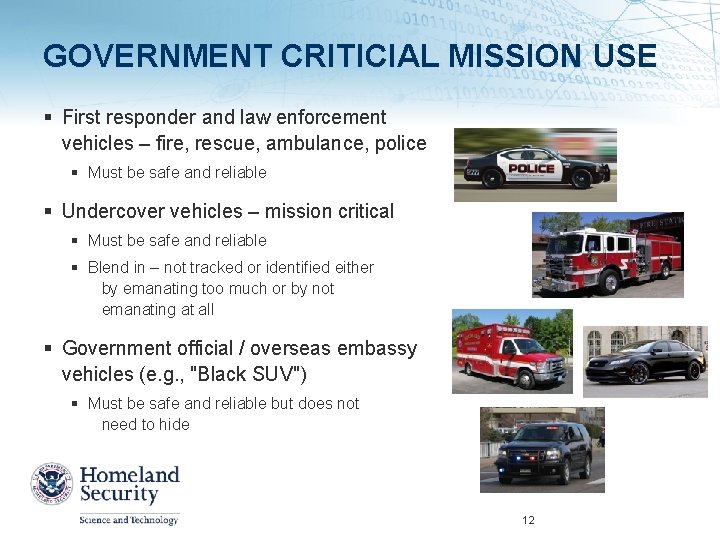
GOVERNMENT CRITICIAL MISSION USE § First responder and law enforcement vehicles – fire, rescue, ambulance, police § Must be safe and reliable § Undercover vehicles – mission critical § Must be safe and reliable § Blend in – not tracked or identified either by emanating too much or by not emanating at all § Government official / overseas embassy vehicles (e. g. , "Black SUV") § Must be safe and reliable but does not need to hide 12
Government Vehicle Telematics § All US Federal Government Vehicles Are Being Equipped with Telematics! § Save fuel, reduce maintenance costs, monitor vehicle use including locations § Security and privacy are essential § Telematics are not new in the heavy vehicle space § Extensively used in commercial trucking for well over a decade § Security of telematics has not been a focus § Telematics are coming to all vehicles § Every major automaker has a service that brings the vehicle online § Example use include emergency calls after a crash and vehicle diagnostic data § Again security has not been a primary focus § DHS and Do. T Volpe are Evaluating the Security Properties § More details in the Do. T Volpe talk to follow 13
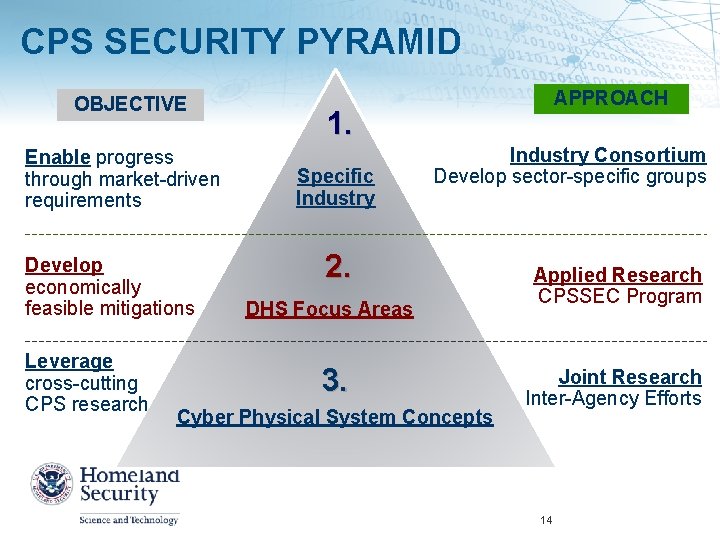
CPS SECURITY PYRAMID OBJECTIVE Enable progress through market-driven requirements Develop economically feasible mitigations Leverage cross-cutting CPS research APPROACH 1. Specific Industry Consortium Develop sector-specific groups 2. DHS Focus Areas 3. Cyber Physical System Concepts Applied Research CPSSEC Program Joint Research Inter-Agency Efforts 14

CYBER PHYSICAL SYSTEM SECURITY BAA Automotive Cyber Security Medical Device Cyber Security Building Infrastructure Cyber Security 15
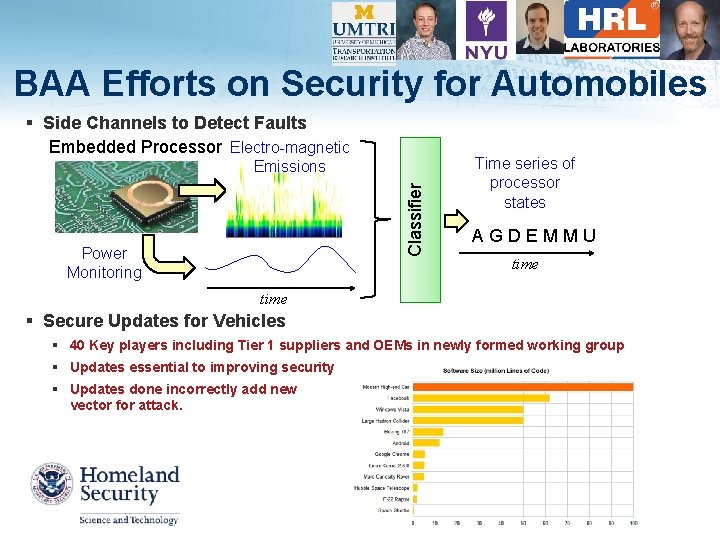
BAA Efforts on Security for Automobiles § Side Channels to Detect Faults Embedded Processor Electro-magnetic Classifier Emissions Power Monitoring Time series of processor states A G D E M M U time § Secure Updates for Vehicles § 40 Key players including Tier 1 suppliers and OEMs in newly formed working group § Updates essential to improving security § Updates done incorrectly add new vector for attack. • 16
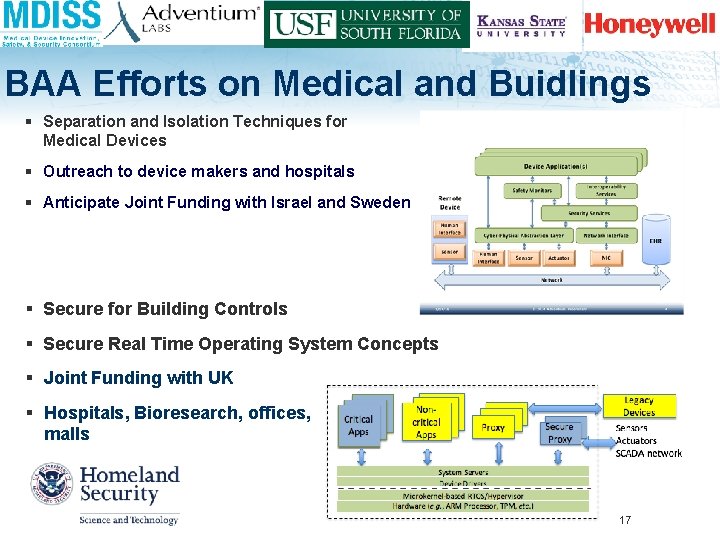
BAA Efforts on Medical and Buidlings § Separation and Isolation Techniques for Medical Devices § Outreach to device makers and hospitals § Anticipate Joint Funding with Israel and Sweden § Secure for Building Controls § Secure Real Time Operating System Concepts § Joint Funding with UK § Hospitals, Bioresearch, offices, malls 17
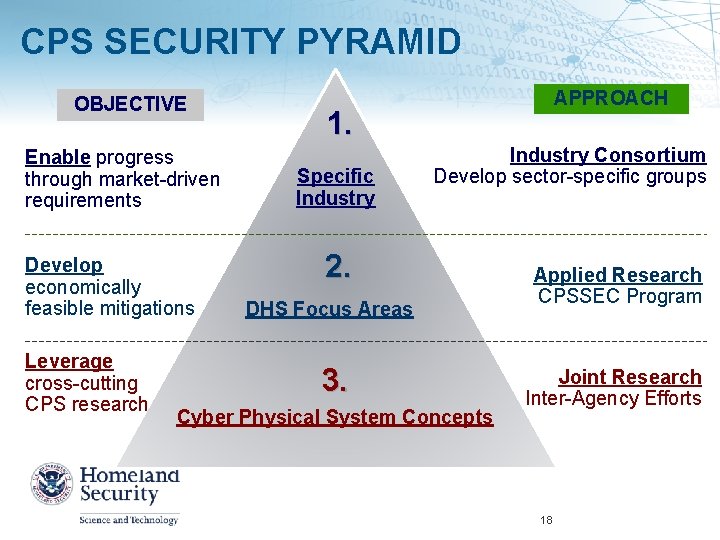
CPS SECURITY PYRAMID OBJECTIVE Enable progress through market-driven requirements Develop economically feasible mitigations Leverage cross-cutting CPS research APPROACH 1. Specific Industry Consortium Develop sector-specific groups 2. DHS Focus Areas 3. Cyber Physical System Concepts Applied Research CPSSEC Program Joint Research Inter-Agency Efforts 18

JOINT RESEARCH WITH US NATIONAL SCIENCE FOUNDATION NSF Joint Solicitation Efforts Researchers submit proposals that the NSF fundamental science mission with the DHS applied research and transition to practice mission SCADA/Energy Testbed Manimaran Govindarasu Smart Grid Security Lalitha Sankar & Robin Podmore Smart Manufacturing Jamie Camelio & Jules White Security and Safety of Io. T Atul Prakash • 19

Accelerating innovation for DHS and the homeland security enterprise to safeguard the American people, the homeland our values. Silicon Valley Innovation Program

What We Do To keep pace with the innovation community and tackle the hardest problems faced by DHS’s operational missions, we EDUCATE Help investors and entrepreneurs understand DHS’s hard problems FUND Provide accelerated non-dilutive funding (up to $800 K US) for product development to address DHS’s needs STREAMLINE TEST Provide test environments and pilot opportunities LEVERAGE Avg Time to Award: 45 days 100: 1 $400+M Private Sector 21
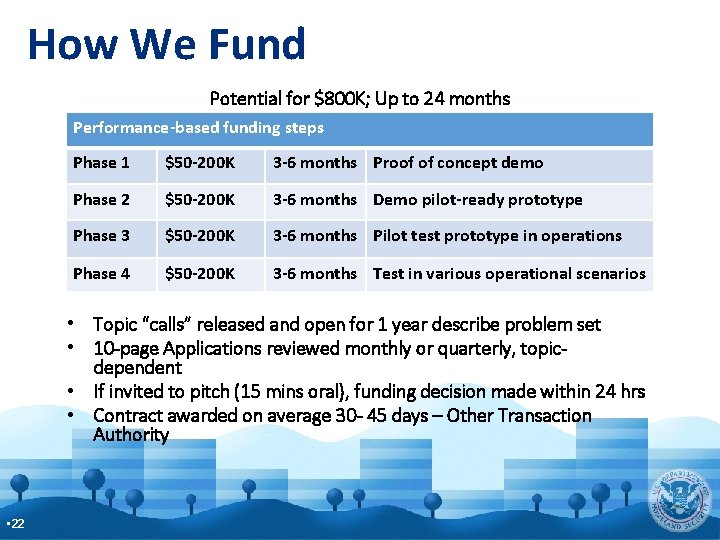
How We Fund Potential for $800 K; Up to 24 months Performance-based funding steps Phase 1 $50 -200 K 3 -6 months Proof of concept demo Phase 2 $50 -200 K 3 -6 months Demo pilot-ready prototype Phase 3 $50 -200 K 3 -6 months Pilot test prototype in operations Phase 4 $50 -200 K 3 -6 months Test in various operational scenarios • Topic “calls” released and open for 1 year describe problem set • 10 -page Applications reviewed monthly or quarterly, topicdependent • If invited to pitch (15 mins oral), funding decision made within 24 hrs • Contract awarded on average 30 - 45 days – Other Transaction Authority • 22
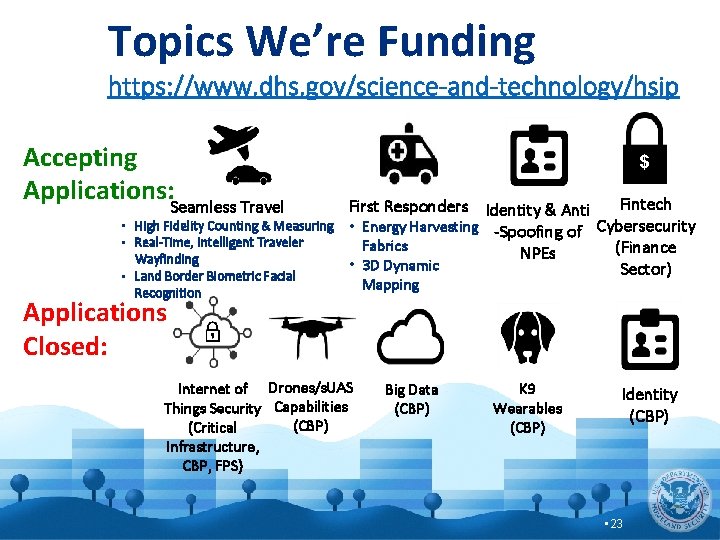
Topics We’re Funding https: //www. dhs. gov/science-and-technology/hsip Accepting Applications: Seamless Travel • High Fidelity Counting & Measuring • Real-Time, Intelligent Traveler Wayfinding • Land Border Biometric Facial Recognition $ Fintech First Responders Identity & Anti • Energy Harvesting -Spoofing of Cybersecurity Fabrics (Finance NPEs • 3 D Dynamic Sector) Mapping Applications Closed: Internet of Drones/s. UAS Things Security Capabilities (CBP) (Critical Infrastructure, CBP, FPS) Big Data (CBP) K 9 Wearables (CBP) Identity (CBP) • 23
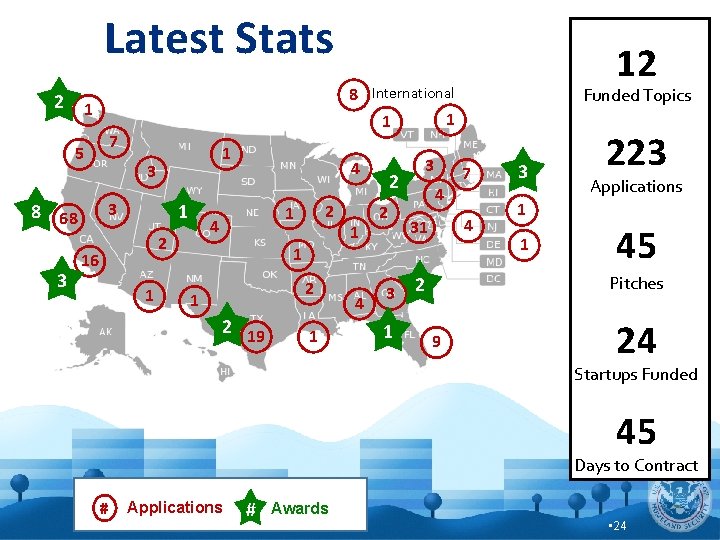
Latest Stats 8 International 1 1 2 1 5 3 7 1 3 3 8 68 12 1 1 2 1 4 2 16 4 1 2 2 3 4 1 2 19 1 4 3 1 7 4 31 1 2 Funded Topics 3 1 1 223 Applications 45 Pitches 2 9 24 Startups Funded 45 Days to Contract # Applications # Awards • 24

Portfolio Companies Halo. Lights, LLC |Halo. Lights™

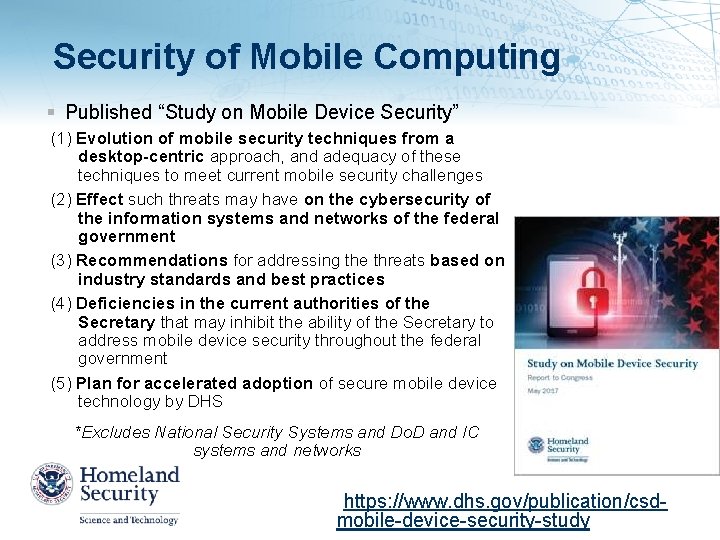
Security of Mobile Computing § Published “Study on Mobile Device Security” (1) Evolution of mobile security techniques from a desktop-centric approach, and adequacy of these techniques to meet current mobile security challenges (2) Effect such threats may have on the cybersecurity of the information systems and networks of the federal government (3) Recommendations for addressing the threats based on industry standards and best practices (4) Deficiencies in the current authorities of the Secretary that may inhibit the ability of the Secretary to address mobile device security throughout the federal government (5) Plan for accelerated adoption of secure mobile device technology by DHS *Excludes National Security Systems and Do. D and IC systems and networks • https: //www. dhs. gov/publication/csdmobile-device-security-study
Report Recommendations § Threats to the government’s use of mobile devices are real and exist across all elements of the mobile ecosystem. § Recommend: § Adopt a framework for mobile device security based on existing standards and best practices. § Enhance Federal Information Security Modernization Act (FISMA) metrics to focus on securing mobile devices, applications, and network infrastructure. § Include mobility within the Continuous Diagnostics and Mitigation program to address the security of mobile devices and applications with capabilities that are at parity with other network devices (e. g. , workstations and servers). § Continue the DHS S&T applied research program in Mobile Application Security to enable the secure use of mobile applications for government use. § Several other recommendations 29
Summary / Conclusions § Cybersecurity research is a key area of innovation to support our global economic and national security futures § CSD continues with an aggressive cyber security research agenda to solve the cyber security problems of our current and future infrastructure and systems § Ever-increasing speed of technology change § Scope/complexity of the different areas of the problem § The balance of near-term versus longer-term R&D § Will continue strong emphasis on technology transition § Will impact cyber education, training, and awareness of our current and future cybersecurity workforce § Will continue to work internationally to find and deploy the best ideas and solutions to real-world problems 30

Douglas Maughan, Ph. D. Division Director Cyber Security Division Homeland Security Advanced Research Projects Agency (HSARPA) douglas. maughan@dhs. gov 202 -254 -6145 / 202 -360 -3170 / 202 -836 -3278 For more information, visit http: //www. dhs. gov/cyber-research 31
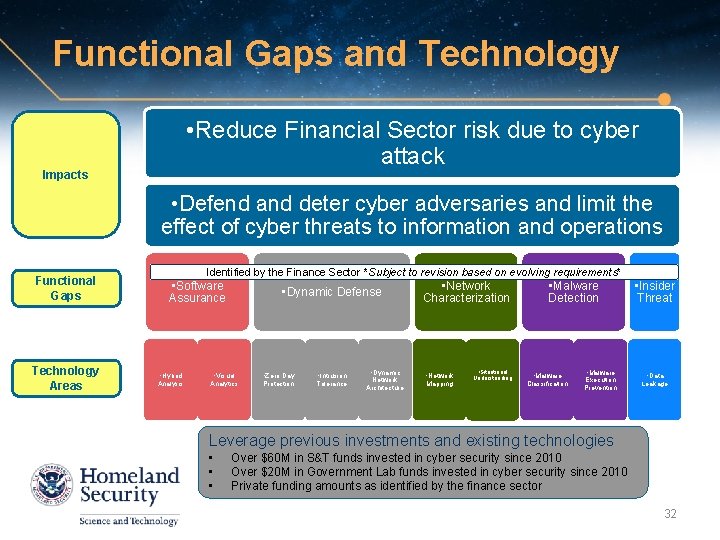
Functional Gaps and Technology • Reduce Financial Sector risk due to cyber attack Impacts • Defend and deter cyber adversaries and limit the effect of cyber threats to information and operations Functional Gaps Technology Areas Identified by the Finance Sector *Subject to revision based on evolving requirements* • Software Assurance • Hybrid Analysis • Dynamic Defense • Visual Analytics • Zero Day Protection • Intrusion Tolerance • Dynamic Network Architecture • Network Characterization • Network Mapping • Situational Understanding • Malware Detection • Malware Classification • Malware Execution Prevention • Insider Threat • Data Leakage Leverage previous investments and existing technologies • • • Over $60 M in S&T funds invested in cyber security since 2010 Over $20 M in Government Lab funds invested in cyber security since 2010 Private funding amounts as identified by the finance sector 32
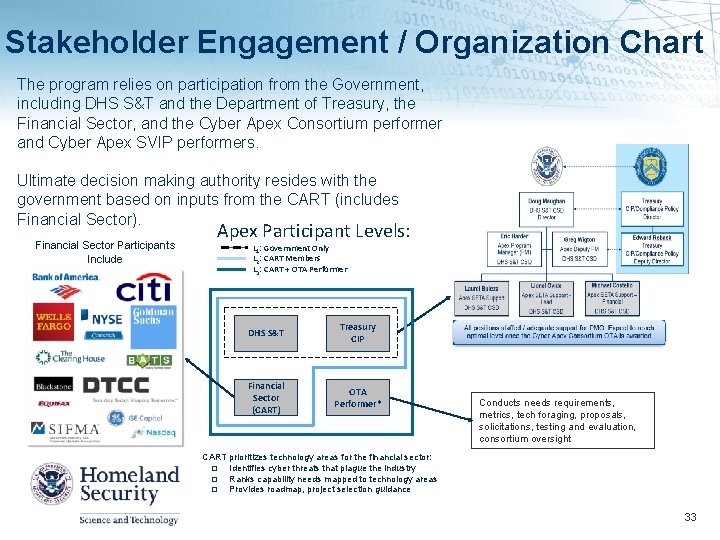
Stakeholder Engagement / Organization Chart The program relies on participation from the Government, including DHS S&T and the Department of Treasury, the Financial Sector, and the Cyber Apex Consortium performer and Cyber Apex SVIP performers. Ultimate decision making authority resides with the government based on inputs from the CART (includes Financial Sector). Financial Sector Participants Include Apex Participant Levels: L 1: Government Only L 2: CART Members L 3: CART + OTA Performer DHS S&T Treasury CIP Financial Sector (CART) OTA Performer* Conducts needs requirements, metrics, tech foraging, proposals, solicitations, testing and evaluation, consortium oversight CART prioritizes technology areas for the financial sector: q Identifies cyber threats that plague the industry q Ranks capability needs mapped to technology areas q Provides roadmap, project selection guidance 33
- Slides: 33