DeviceIndependent Security of Quantum Key Distribution A Acn
Device-Independent Security of Quantum Key Distribution A. Acín, Stefano Pironio (ICFO, Barcelona) N. Brunner, N. Gisin (Geneva) S. Massar (Brussels) V. Scarani (Singapore) QIP 2008, New Delhi, December 2008
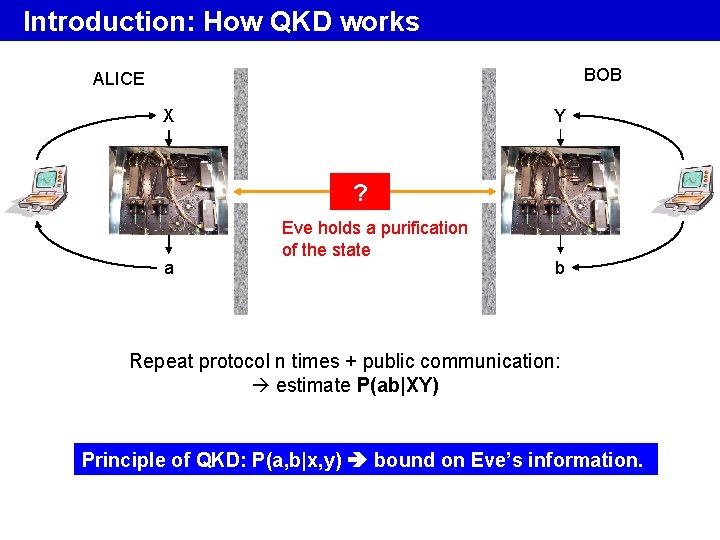
Introduction: How QKD works BOB ALICE Y X ? a Eve holds a purification of the state b Repeat protocol n times + public communication: estimate P(ab|XY) Principle of QKD: P(a, b|x, y) bound on Eve’s information.
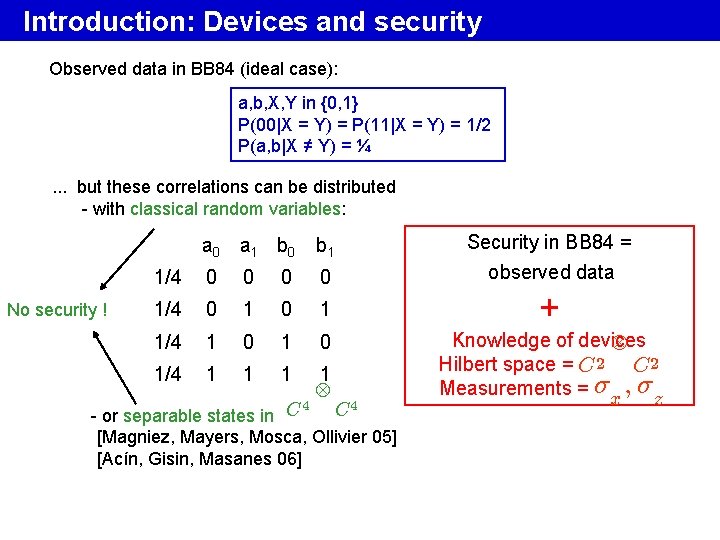
Introduction: Devices and security Observed data in BB 84 (ideal case): a, b, X, Y in {0, 1} P(00|X = Y) = P(11|X = Y) = 1/2 P(a, b|X ≠ Y) = ¼. . . but these correlations can be distributed - with classical random variables: No security ! a 0 a 1 b 0 b 1 1/4 0 0 1/4 0 1 1/4 1 0 1/4 1 1 4 Security in BB 84 = observed data + 4 C - or separable states in C [Magniez, Mayers, Mosca, Ollivier 05] [Acín, Gisin, Masanes 06] Knowledge of devices Hilbert space = C 2 Measurements = ¾x ; ¾z

Our scenario BOB ALICE Y X ? a ? ? b Aim: Prove security using observed data P(ab|XY) only • knowing that P(ab|XY) originates from a quantum process • but without assuming anything about its actual implementation: Hilbert space dimension? Measurements performed? . . .
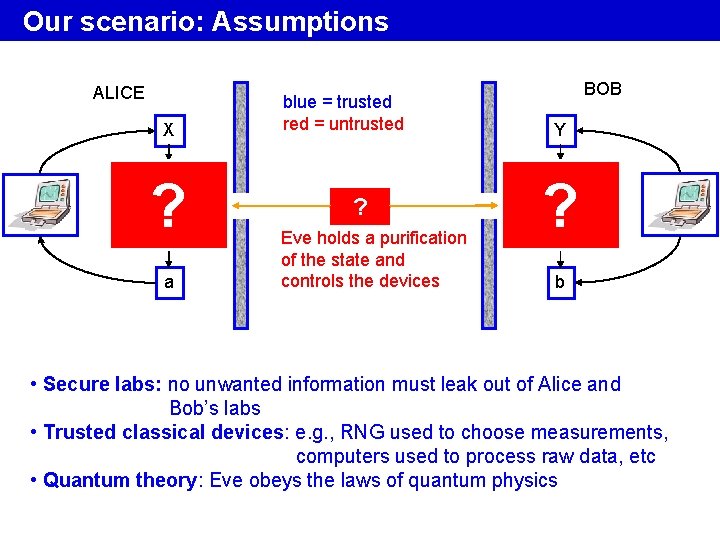
Our scenario: Assumptions ALICE X ? a blue = trusted red = untrusted ? Eve holds a purification of the state and controls the devices BOB Y ? b • Secure labs: no unwanted information must leak out of Alice and Bob’s labs • Trusted classical devices: e. g. , RNG used to choose measurements, computers used to process raw data, etc • Quantum theory: Eve obeys the laws of quantum physics
Our scenario: Motivation • Fundamental: base QKD on minimal set of assumptions • Side-channels: information leaked in other part of the spectrum, number of photons not controled, etc. • Q devices may be untrusted: for instance, if provided by a malevolent party
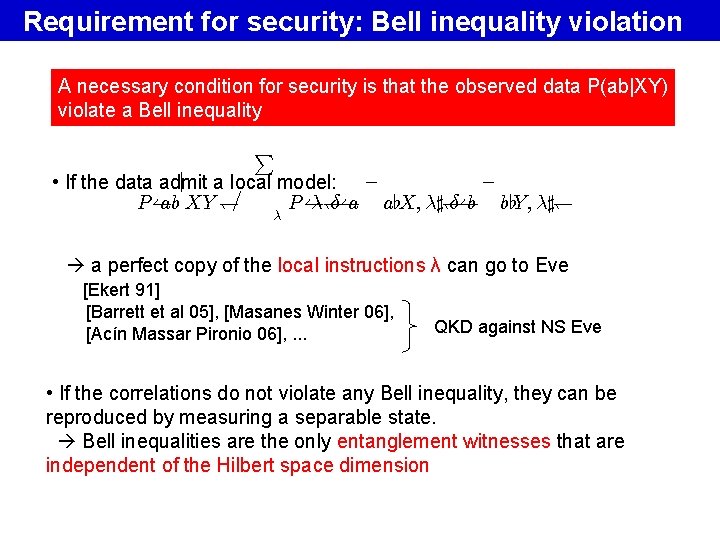
Requirement for security: Bell inequality violation A necessary condition for security is that the observed data P(ab|XY) violate a Bell inequality P ¡ j a local model: ¡ • If the data admit ab XY )= ¸) ±( a a[X; ¸]) ±( b b[Y; ¸]) P( P( ¸ a perfect copy of the local instructions λ can go to Eve [Ekert 91] [Barrett et al 05], [Masanes Winter 06], [Acín Massar Pironio 06], . . . QKD against NS Eve • If the correlations do not violate any Bell inequality, they can be reproduced by measuring a separable state. Bell inequalities are the only entanglement witnesses that are independent of the Hilbert space dimension
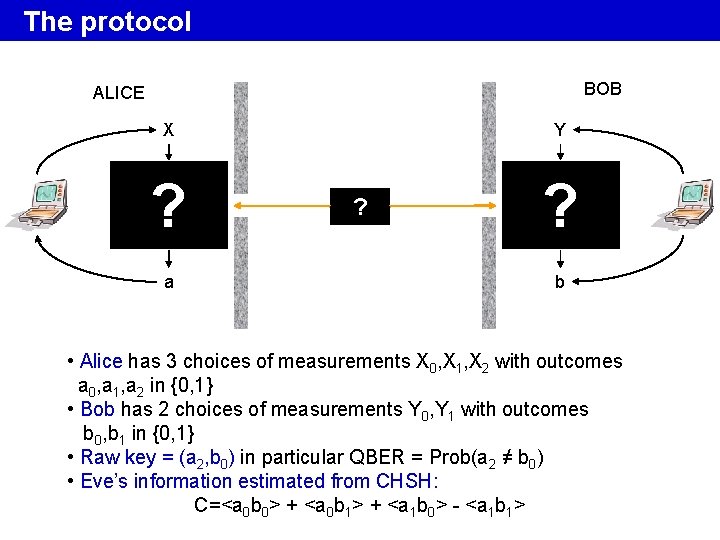
The protocol BOB ALICE Y X ? a ? ? b • Alice has 3 choices of measurements X 0, X 1, X 2 with outcomes a 0, a 1, a 2 in {0, 1} • Bob has 2 choices of measurements Y 0, Y 1 with outcomes b 0, b 1 in {0, 1} • Raw key = (a 2, b 0) in particular QBER = Prob(a 2 ≠ b 0) • Eve’s information estimated from CHSH: C=<a 0 b 0> + <a 0 b 1> + <a 1 b 0> - <a 1 b 1>
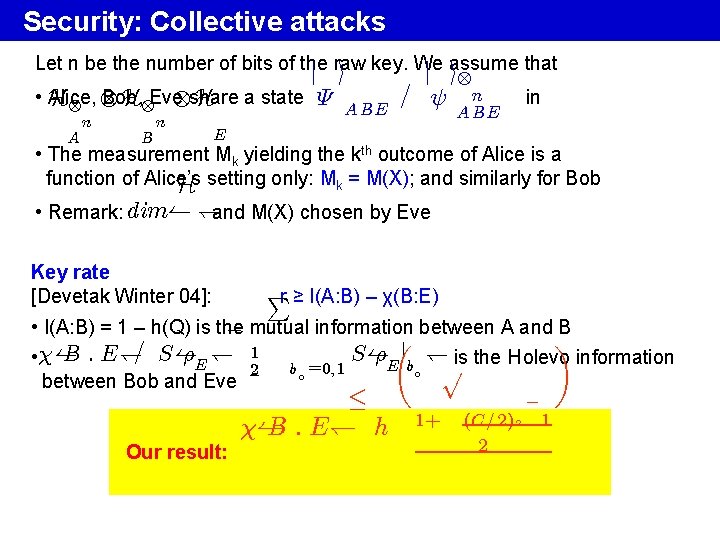
Security: Collective attacks Let n be the number of bits of the j raw i key. We j iassume that • Alice, Bob, H H Eve share H a state ª A B E = Ã n A n B n AB E in E • The measurement Mk yielding the kth outcome of Alice is a function of Alice’s H setting only: Mk = M(X); and similarly for Bob • Remark: dim( )and M(X) chosen by Eve Key rate [Devetak Winter 04]: Pr ≥ I(A: B) – χ(B: E) • I(A: B) = 1 – h(Q) is the ¡ mutual information between A and B µj ¶ = 1 B : E) S( S( ½E ) ½E b ) is the Holevo information • ( p b 0 =0; 1 2 0 between Bob and Eve · ( B : E) h Our result: 1+ (C =2)2 2 ¡ 1
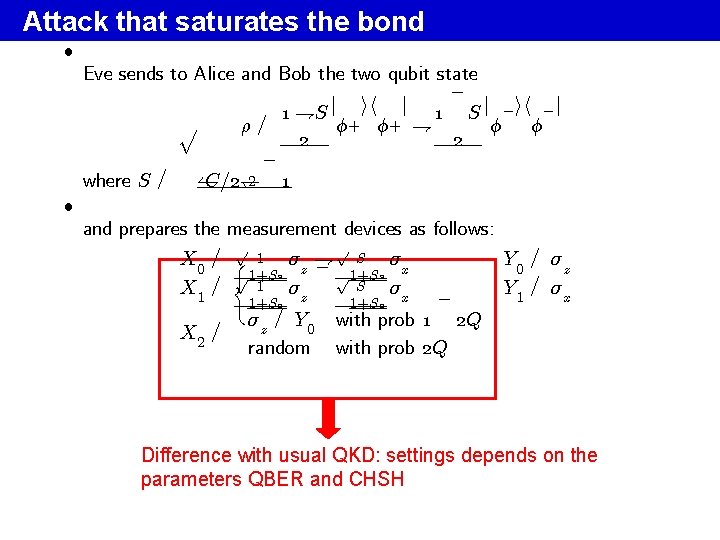
Attack that saturates the bond ² ² Eve sends to Alice and Bob the two qubit state ¡ j ih j 1 +S 1 S j ¡ ih ¡ j p Á+ Á+ + Á Á ½= 2 2 ¡ 2 1 C=2) ( where S = and prepares the measurement devices as follows: p p S X 0 = ( 1 ¾z + ¾x Y 0 = ¾z ¡ p 1+S 2 = 1 S X 1 Y 1 = ¾x ¾z ¾x ¡ 1+S 2 ¾z = Y 0 with prob 1 2 Q X 2 = random with prob 2 Q Difference with usual QKD: settings depends on the parameters QBER and CHSH
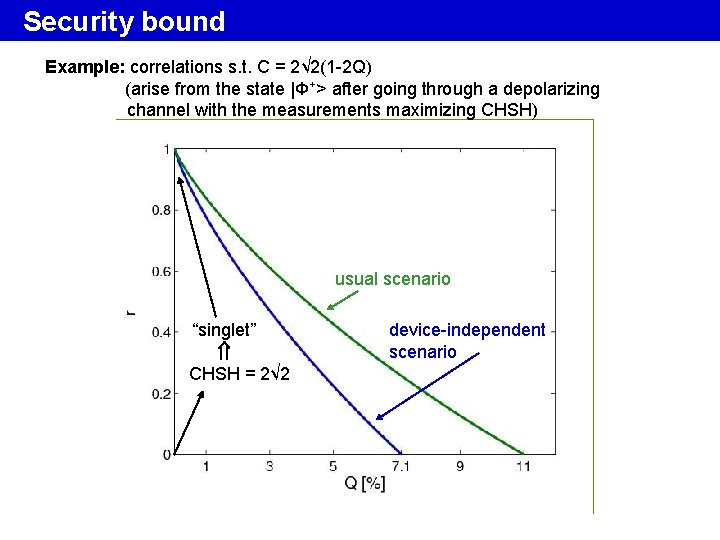
Security bound Example: correlations s. t. C = 2√ 2(1 -2 Q) (arise from the state |Φ+> after going through a depolarizing channel with the measurements maximizing CHSH) usual scenario “singlet” CHSH = 2√ 2 device-independent scenario
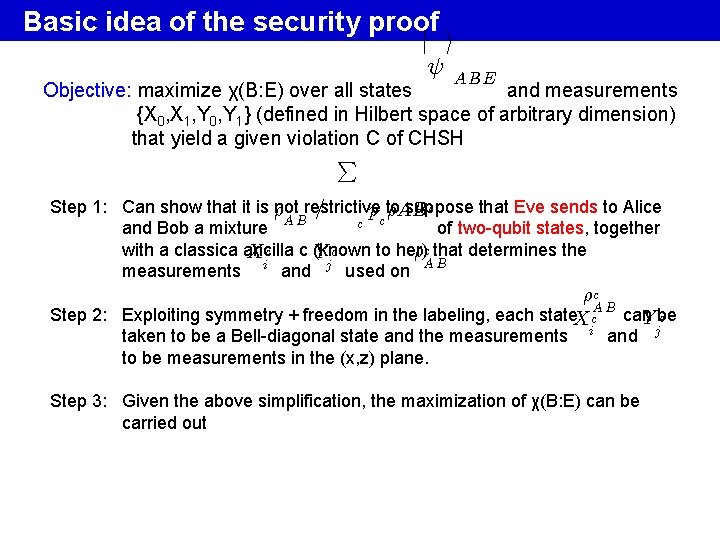
Basic idea of the security proof j i à AB E Objective: maximize χ(B: E) over all states and measurements {X 0, X 1, Y 0, Y 1} (defined in Hilbert space of arbitrary dimension) that yield a given violation C of CHSH P Step 1: Can show that it is ½ not restrictive suppose that Eve sends to Alice c = pc to ½AB AB c and Bob a mixture of two-qubit states, together with a classica ancilla to her) ½c that determines the X c c (known Yc AB measurements i and j used on ½c Step 2: Exploiting symmetry + freedom in the labeling, each state. X c. A B can c Y be j taken to be a Bell-diagonal state and the measurements to be measurements in the (x, z) plane. i and Step 3: Given the above simplification, the maximization of χ(B: E) can be carried out
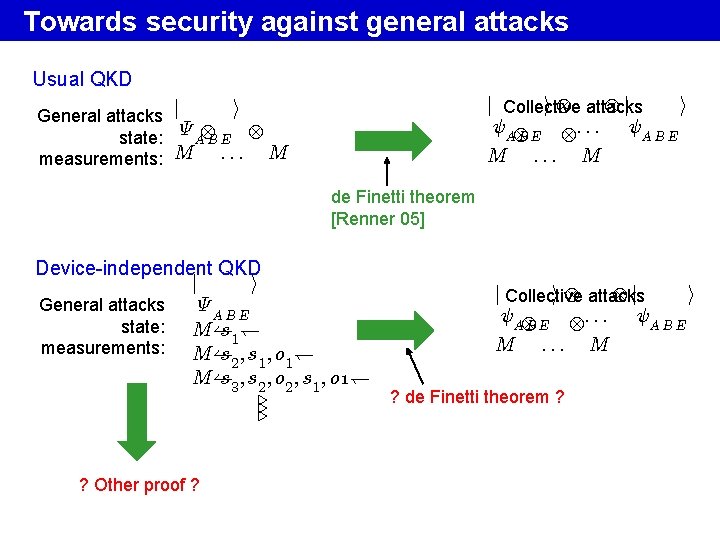
Towards security against general attacks Usual QKD j j Collective i attacks i ÃAB E : : : ÃAB E M : : : M i General attacks j state: ª A B E measurements: M : : : M de Finetti theorem [Renner 05] Device-independent QKD j i General attacks ª AB E state: M ( s 1 ) measurements: M ( s 2 ; s 1 ; o 1 ) M( s 3 ; s 2 ; o 2 ; s 1 ; o 1). . . ? Other proof ? j j Collective i attacks i ÃAB E : : : ÃAB E M : : : M ? de Finetti theorem ?
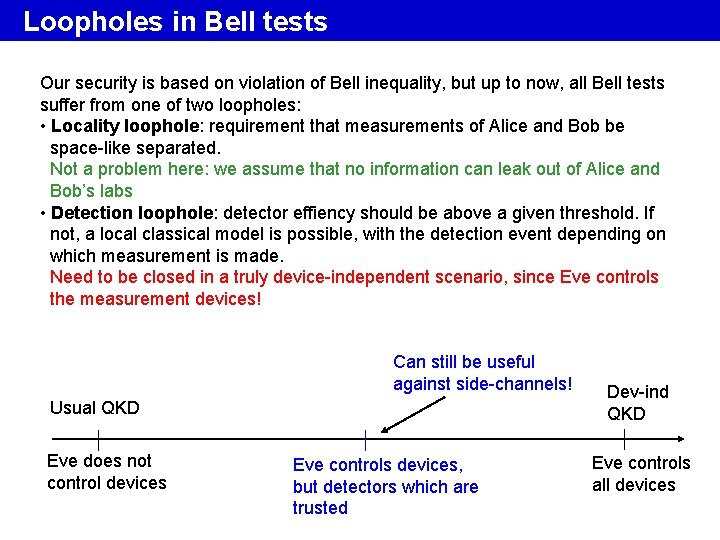
Loopholes in Bell tests Our security is based on violation of Bell inequality, but up to now, all Bell tests suffer from one of two loopholes: • Locality loophole: requirement that measurements of Alice and Bob be space-like separated. Not a problem here: we assume that no information can leak out of Alice and Bob’s labs • Detection loophole: detector effiency should be above a given threshold. If not, a local classical model is possible, with the detection event depending on which measurement is made. Need to be closed in a truly device-independent scenario, since Eve controls the measurement devices! Can still be useful against side-channels! Usual QKD Eve does not control devices Eve controls devices, but detectors which are trusted Dev-ind QKD Eve controls all devices
SUMMARY • Usual QKD security scenario: assume knowledge of Hilbert space and measurements; devices are under control • Device-independent security can be defined, based on the violation of a Bell inequality • We have proved security against collective attaks ar. Xiv: quant-ph/0702152
- Slides: 15