Detecting and restoring the tampered images based on
Detecting and restoring the tampered images based on iteration-free fractal compression n n Source: The Journal of Systems and Software, Volume 67, Issue 2, pp. 131 - 140, Aug. 2003 Authors: Ching-Te Wnag, Tung-Shou Chen, Shao-Hau He Speaker: Yu-Zheng Wang Date: 2004/04/20 1
Outline n n n Introduction Iteration-free fractal image coding Proposed method Experimental results Conclusions 2
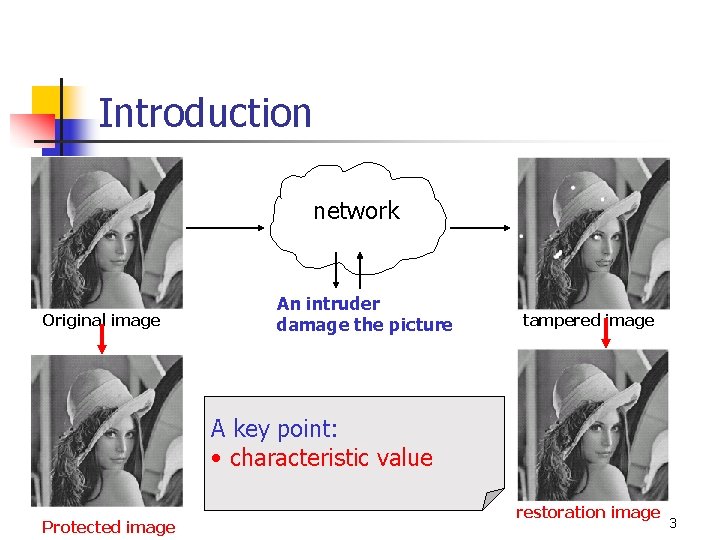
Introduction network Original image An intruder damage the picture tampered image A key point: • characteristic value Protected image restoration image 3
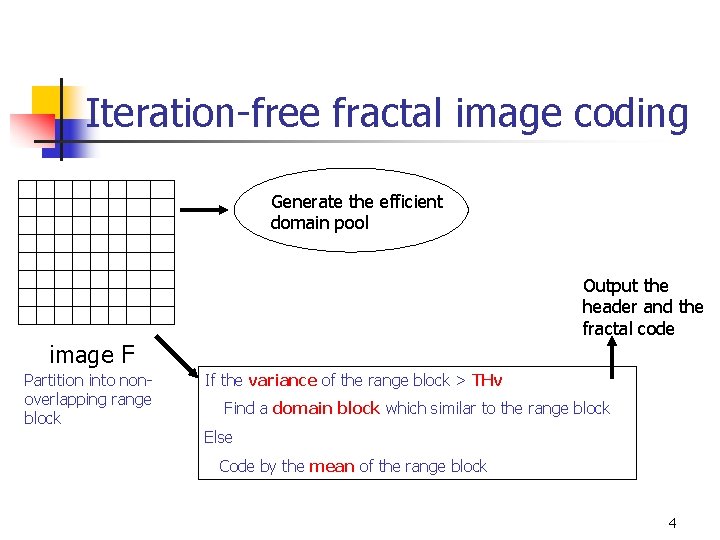
Iteration-free fractal image coding Generate the efficient domain pool Output the header and the fractal code image F Partition into nonoverlapping range block If the variance of the range block > THv Find a domain block which similar to the range block Else Code by the mean of the range block 4
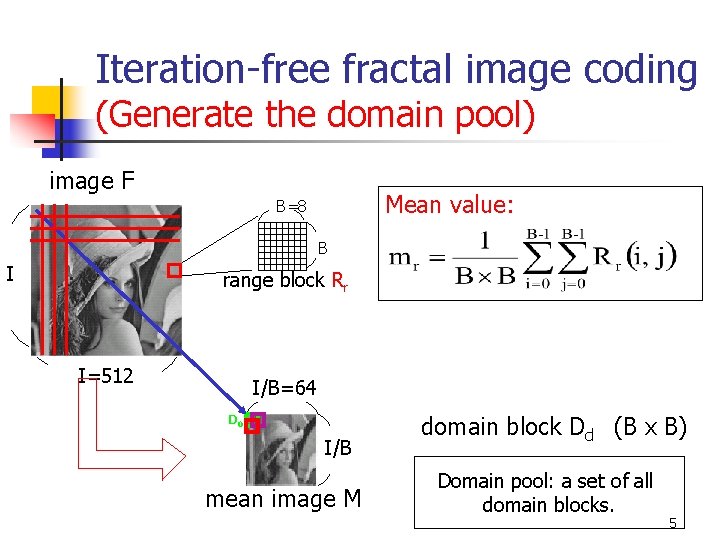
Iteration-free fractal image coding (Generate the domain pool) image F Mean value: B=8 B I range block Rr I=512 I/B=64 D 0 I/B mean image M domain block Dd (B x B) Domain pool: a set of all domain blocks. 5
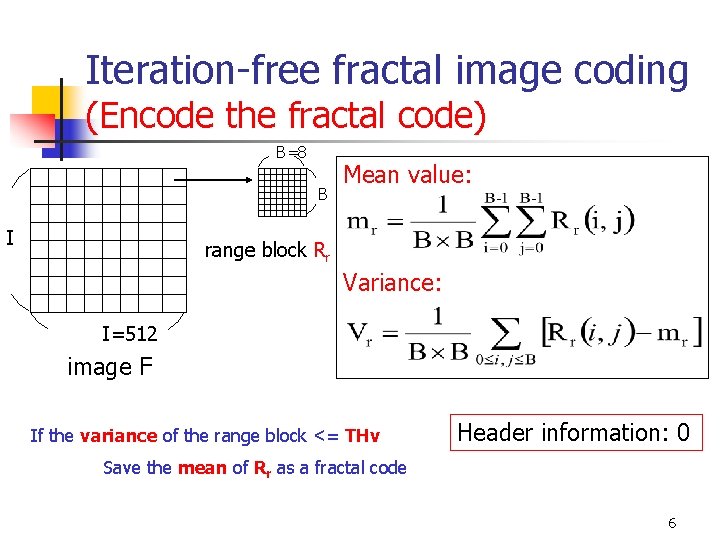
Iteration-free fractal image coding (Encode the fractal code) B=8 B I Mean value: range block Rr Variance: I=512 image F If the variance of the range block <= THv Header information: 0 Save the mean of Rr as a fractal code 6
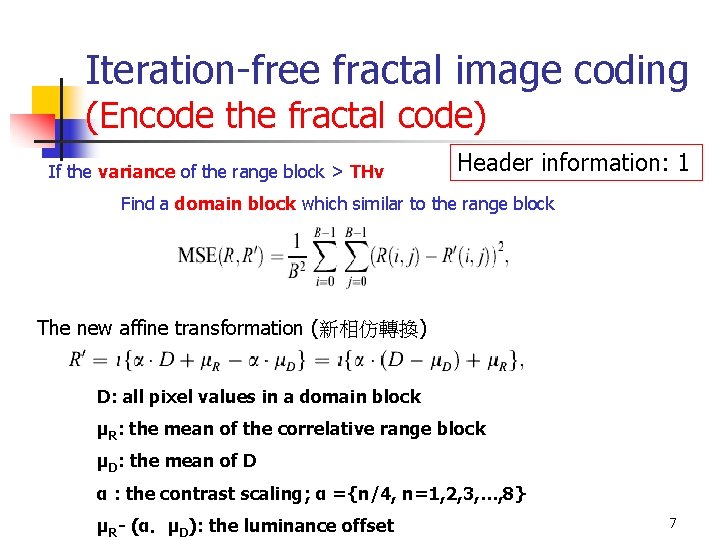
Iteration-free fractal image coding (Encode the fractal code) If the variance of the range block > THv Header information: 1 Find a domain block which similar to the range block The new affine transformation (新相仿轉換) D: all pixel values in a domain block μR: the mean of the correlative range block μD: the mean of D α : the contrast scaling; α ={n/4, n=1, 2, 3, …, 8} μR- (α.μD): the luminance offset 7
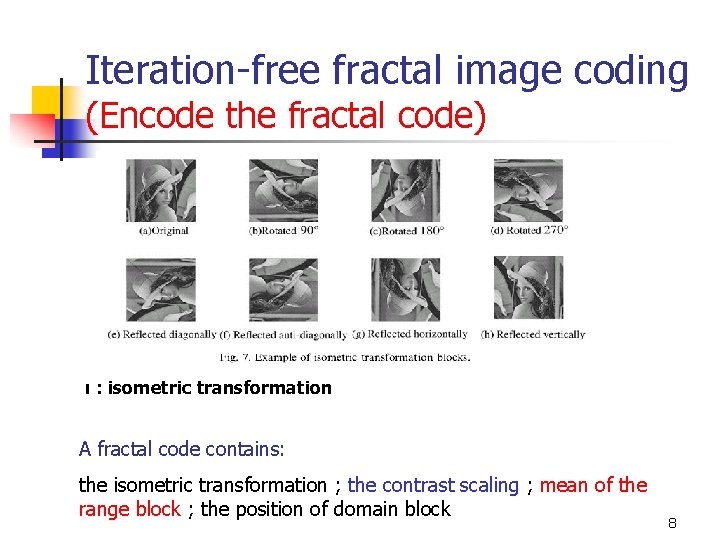
Iteration-free fractal image coding (Encode the fractal code) ι : isometric transformation A fractal code contains: the isometric transformation ; the contrast scaling ; mean of the range block ; the position of domain block 8
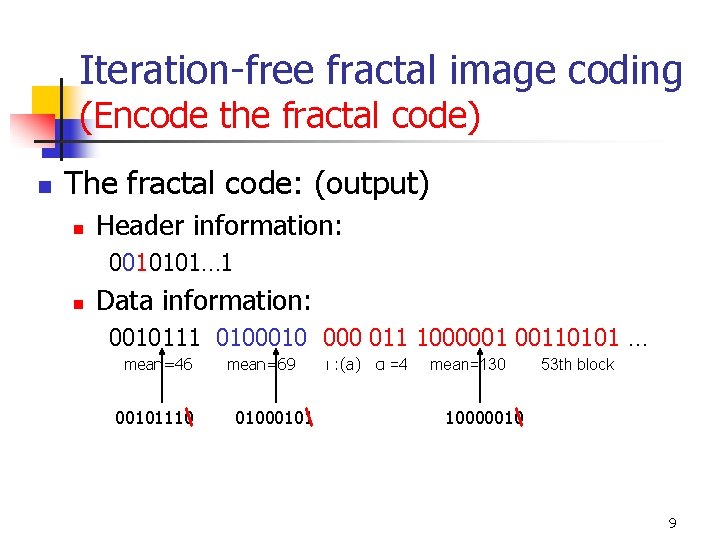
Iteration-free fractal image coding (Encode the fractal code) n The fractal code: (output) n Header information: 0010101… 1 n Data information: 0010111 0100010 000 011 1000001 00110101 … mean=46 00101110 mean=69 01000101 ι : (a) α =4 mean=130 53 th block 10000010 9
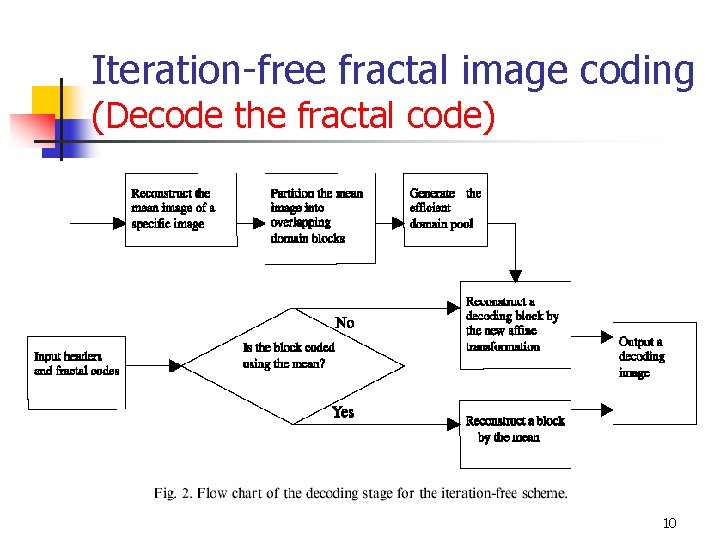
Iteration-free fractal image coding (Decode the fractal code) 10
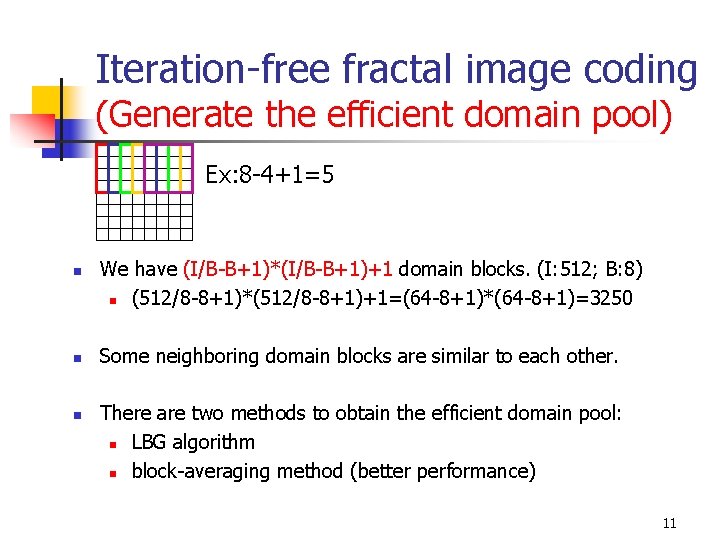
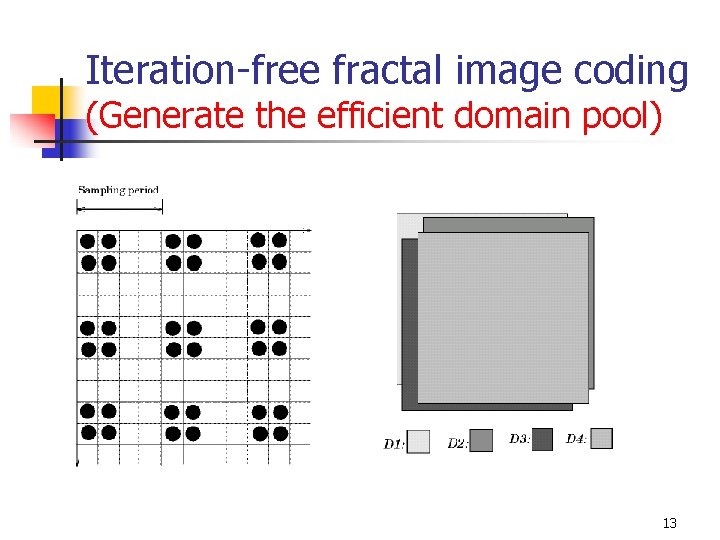
Iteration-free fractal image coding (Generate the efficient domain pool) Ex: 8 -4+1=5 n n n We have (I/B-B+1)*(I/B-B+1)+1 domain blocks. (I: 512; B: 8) n (512/8 -8+1)*(512/8 -8+1)+1=(64 -8+1)*(64 -8+1)=3250 Some neighboring domain blocks are similar to each other. There are two methods to obtain the efficient domain pool: n LBG algorithm n block-averaging method (better performance) 11
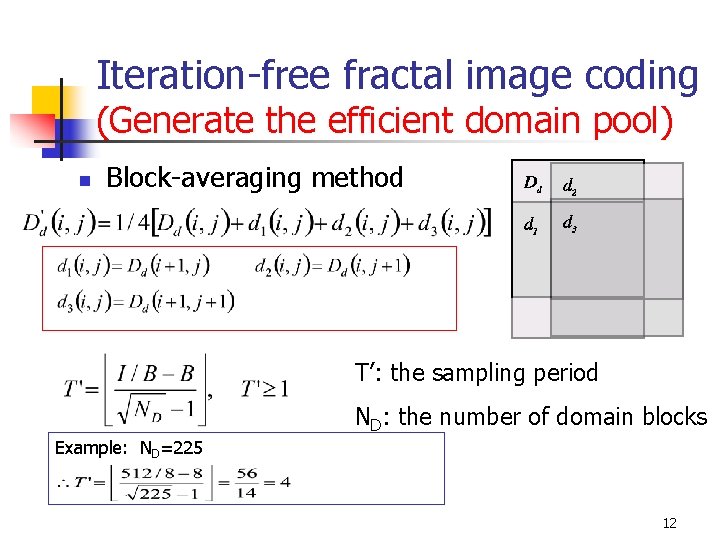
Iteration-free fractal image coding (Generate the efficient domain pool) n Block-averaging method T’: the sampling period ND: the number of domain blocks Example: ND=225 12
Iteration-free fractal image coding (Generate the efficient domain pool) 13
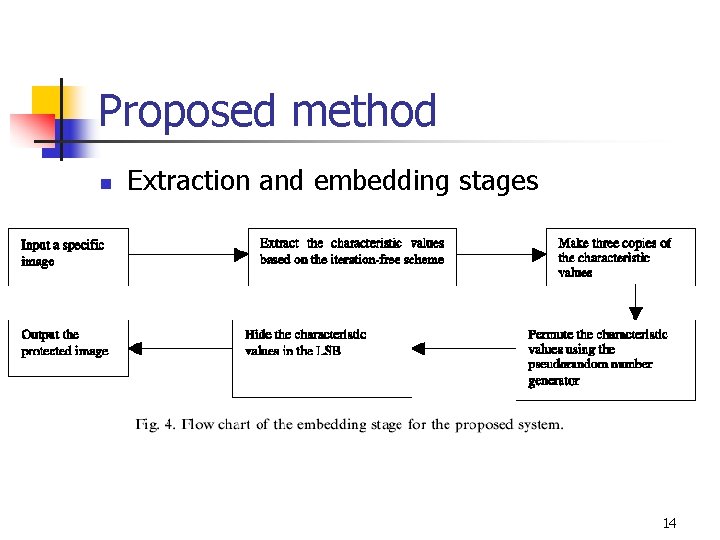
Proposed method n Extraction and embedding stages 14
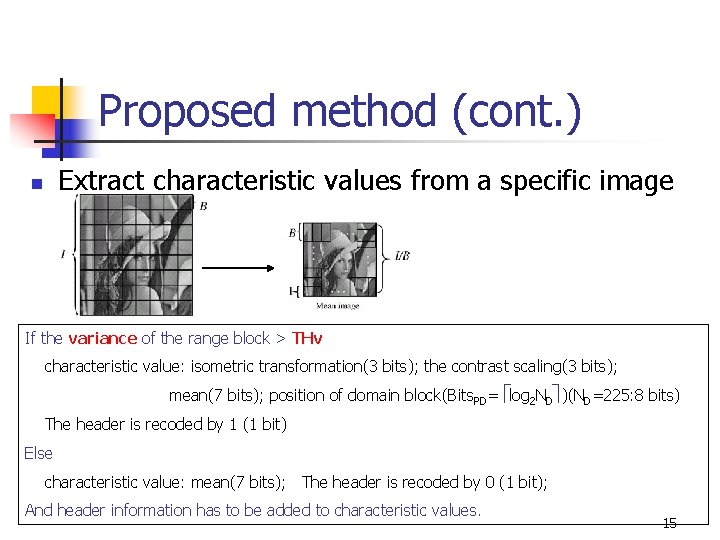
Proposed method (cont. ) Extract characteristic values from a specific image n If the variance of the range block > THv characteristic value: isometric transformation(3 bits); the contrast scaling(3 bits); mean(7 bits); position of domain block(Bits. PD= log 2 ND )(ND=225: 8 bits) The header is recoded by 1 (1 bit) Else characteristic value: mean(7 bits); The header is recoded by 0 (1 bit); And header information has to be added to characteristic values. 15
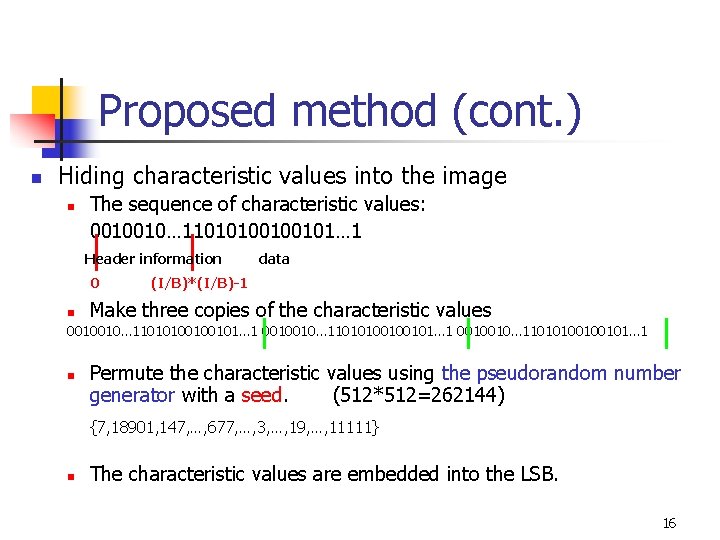
Proposed method (cont. ) n Hiding characteristic values into the image n The sequence of characteristic values: 0010010… 11010100100101… 1 Header information 0 n data (I/B)*(I/B)-1 Make three copies of the characteristic values 0010010… 11010100100101… 1 n Permute the characteristic values using the pseudorandom number generator with a seed. (512*512=262144) {7, 18901, 147, …, 677, …, 3, …, 19, …, 11111} n The characteristic values are embedded into the LSB. 16
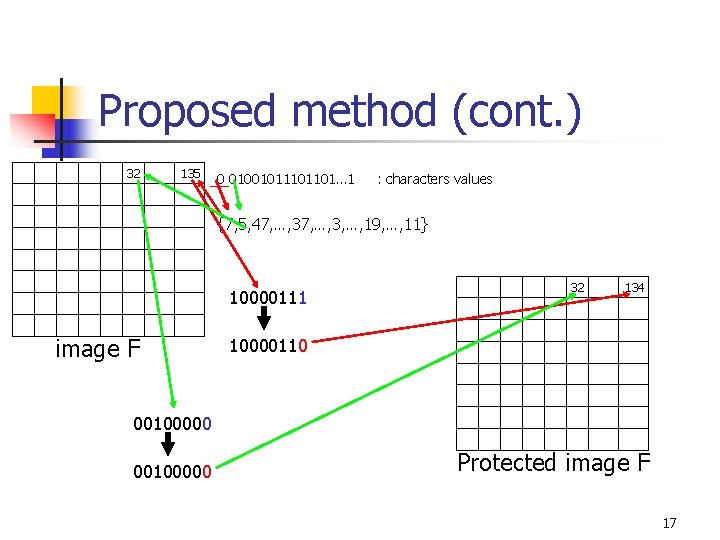
Proposed method (cont. ) 32 135 0 0100101101… 1 : characters values {7, 5, 47, …, 3, …, 19, …, 11} 10000111 image F 32 134 10000110 00100000 Protected image F 17
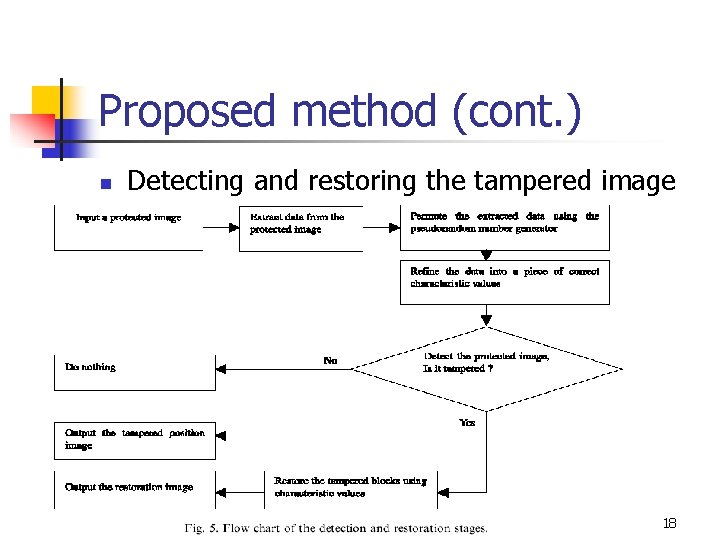
Proposed method (cont. ) n Detecting and restoring the tampered image 18
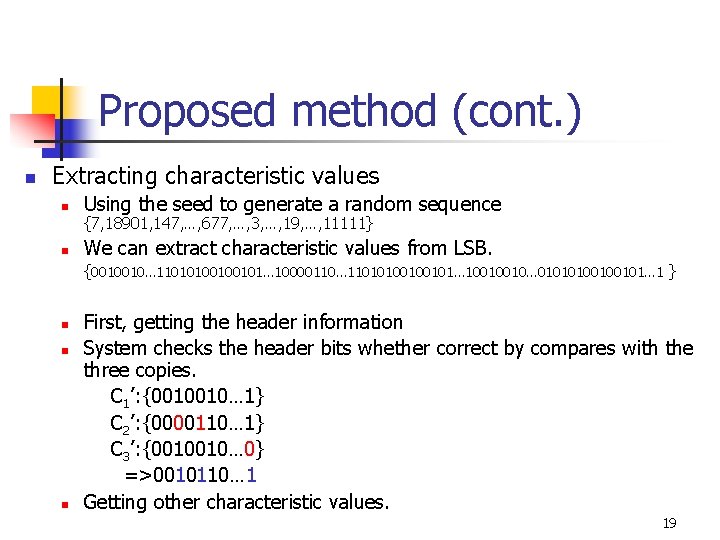
Proposed method (cont. ) n Extracting characteristic values n Using the seed to generate a random sequence n We can extract characteristic values from LSB. {7, 18901, 147, …, 677, …, 3, …, 19, …, 11111} {0010010… 11010100100101… 10000110… 11010100100101… 10010010… 01010100100101… 1 } n n n First, getting the header information System checks the header bits whether correct by compares with the three copies. C 1’: {0010010… 1} C 2’: {0000110… 1} C 3’: {0010010… 0} =>0010110… 1 Getting other characteristic values. 19
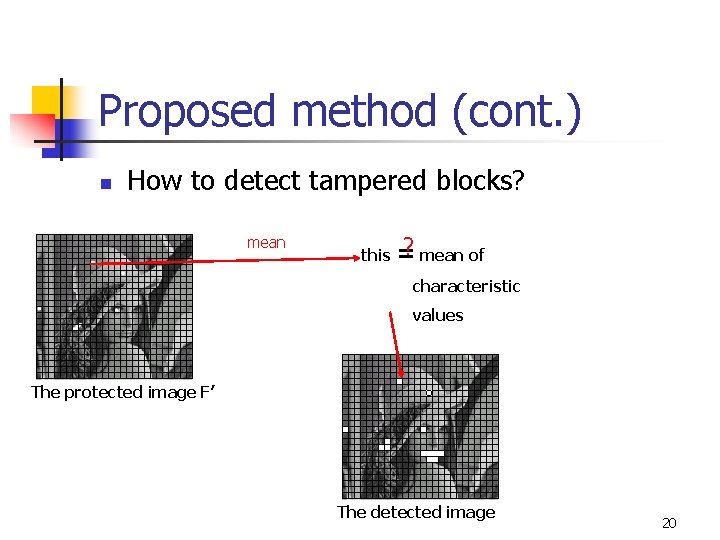
Proposed method (cont. ) n How to detect tampered blocks? mean of this = characteristic values The protected image F’ The detected image 20
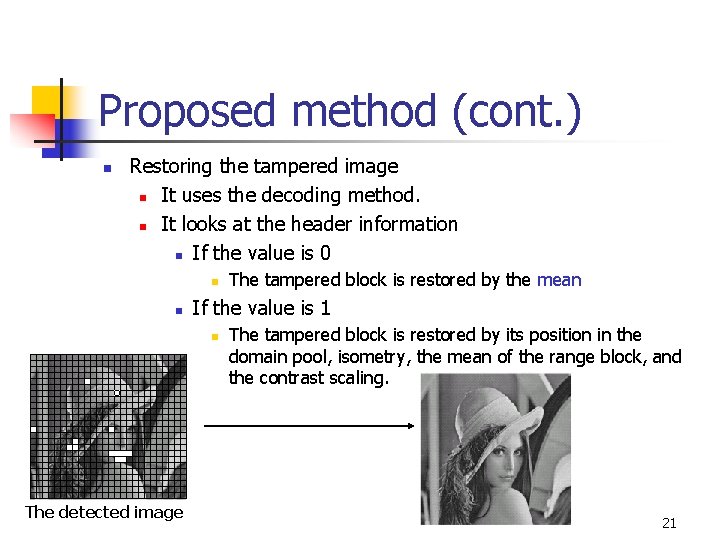
Proposed method (cont. ) n Restoring the tampered image n It uses the decoding method. n It looks at the header information n If the value is 0 n n If the value is 1 n The detected image The tampered block is restored by the mean The tampered block is restored by its position in the domain pool, isometry, the mean of the range block, and the contrast scaling. 21
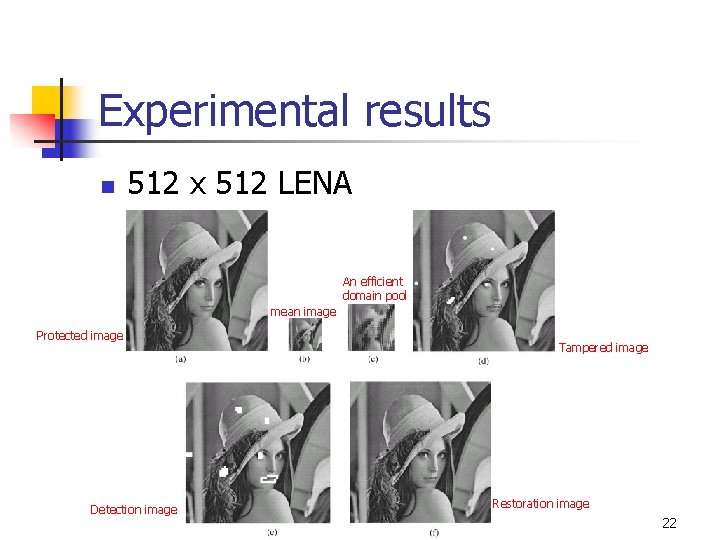
Experimental results n 512 x 512 LENA An efficient domain pool mean image Protected image Detection image Tampered image Restoration image 22
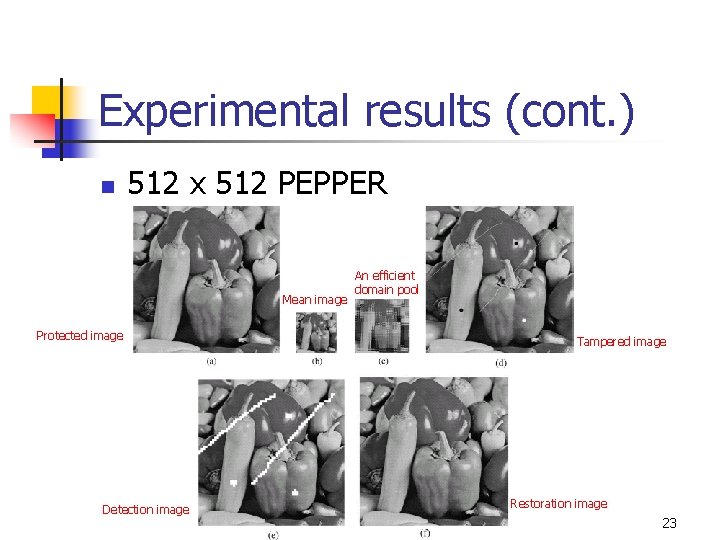
Experimental results (cont. ) n 512 x 512 PEPPER Mean image Protected image Detection image An efficient domain pool Tampered image Restoration image 23
Conclusions n n This paper has proposed a detection and restoration system for tampered image based on iteration-free fractal compression. The restoration technique don’t need the source image. 24
- Slides: 24