Design and Analysis of an MST Based Topology
Design and Analysis of an MST -Based Topology Control Algorithm Ning Li and Jennifer Hou Department of Computer Science University of Illinois at Urbana-Champaign nli@cs. uiuc. edu, jhou@cs. uiuc. edu

Outline • Motivation • Topology Control • LMST: Local Minimum Spanning Tree • Simulation Study • Future Work 9/25/2020 2
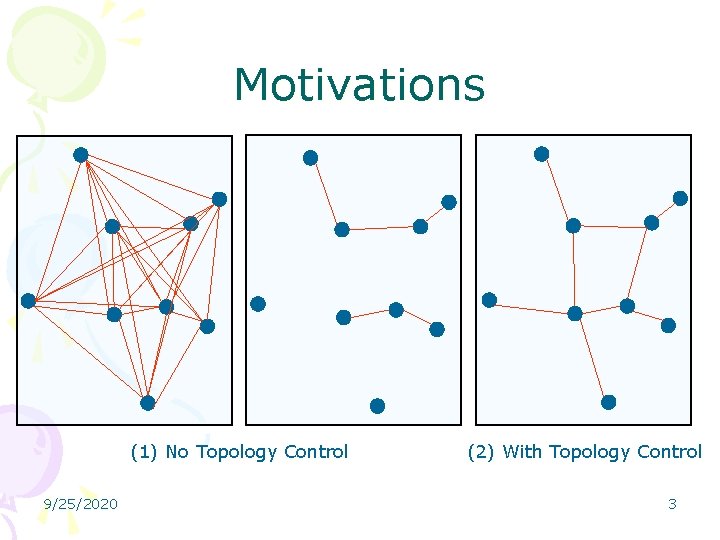
Motivations (1) No Topology Control 9/25/2020 (2) With Topology Control 3
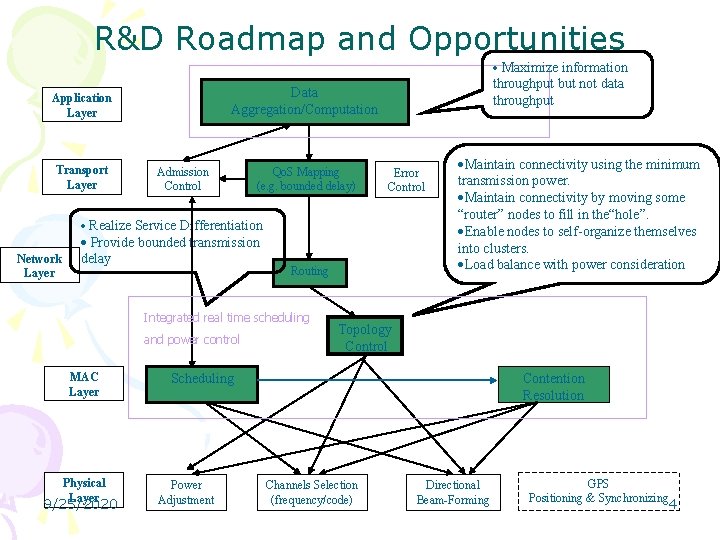
R&D Roadmap and Opportunities · Maximize information Transport Layer throughput but not data throughput Data Aggregation/Computation Application Layer Admission Control Qo. S Mapping (e. g. bounded delay) Error Control · Realize Service Differentiation Network Layer · Provide bounded transmission delay Routing Integrated real time scheduling and power control MAC Layer Physical Layer 9/25/2020 ·Maintain connectivity using the minimum transmission power. ·Maintain connectivity by moving some “router” nodes to fill in the“hole”. ·Enable nodes to self-organize themselves into clusters. ·Load balance with power consideration Topology Control Scheduling Power Adjustment Contention Resolution Channels Selection (frequency/code) Directional Beam-Forming GPS Positioning & Synchronizing 4
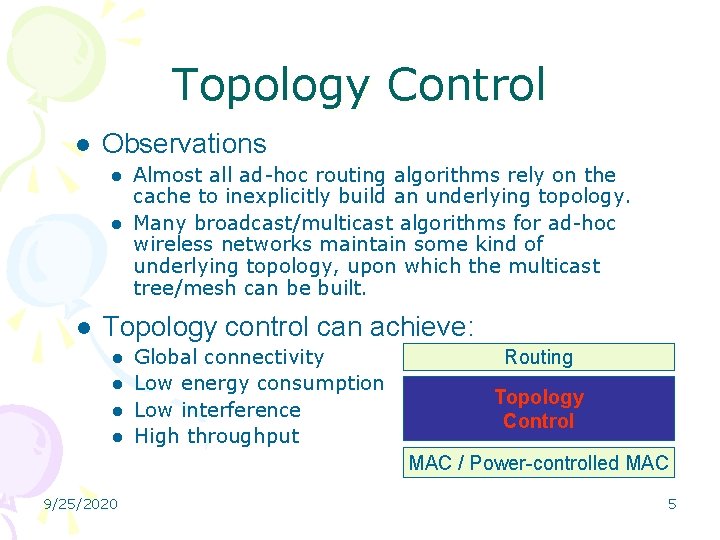
Topology Control l Observations l l l Almost all ad-hoc routing algorithms rely on the cache to inexplicitly build an underlying topology. Many broadcast/multicast algorithms for ad-hoc wireless networks maintain some kind of underlying topology, upon which the multicast tree/mesh can be built. Topology control can achieve: l l Global connectivity Low energy consumption Low interference High throughput Routing Topology Control MAC / Power-controlled MAC 9/25/2020 5
Design Guidelines • Network connectivity should be preserved. • Bi-directional links are preferred. • Algorithms should be distributed. • To be immune to the impact of mobility, the algorithm should depend on local information. 9/25/2020 6
LMST: Local Minimum Spanning Tree • Static wireless multihop networks. • Transmission power can be adjusted. • Each node knows its own position. • Each node will build its own minimum spanning tree in its neighborhood and only retain those one-hop neighbors on the tree as its neighbors in the final topology. 9/25/2020 7
LMST • Visible neighborhood: the set of nodes that node u can reach by using the maximum transmission power. • Information collection: Each node broadcast periodically a Hello message using its maximal transmission power. • Topology construction – Each node applies Prim’s algorithm independently to obtain its local minimum spanning tree. – Each node takes all the one-hop, on-tree nodes as its neighbors. – The network topology under LMST is all the nodes in V and their individually perceived neighbor relations. • Determination of transmission power: a node transmits using the power that can reach its farthest neighbor. 9/25/2020 8
LMST Properties • The resulting topology preserves the connectivity. • After removal of asymmetric links, all links are bi-directional and the connectivity is still preserved. • The degree of any node is bounded by 6. 9/25/2020 9
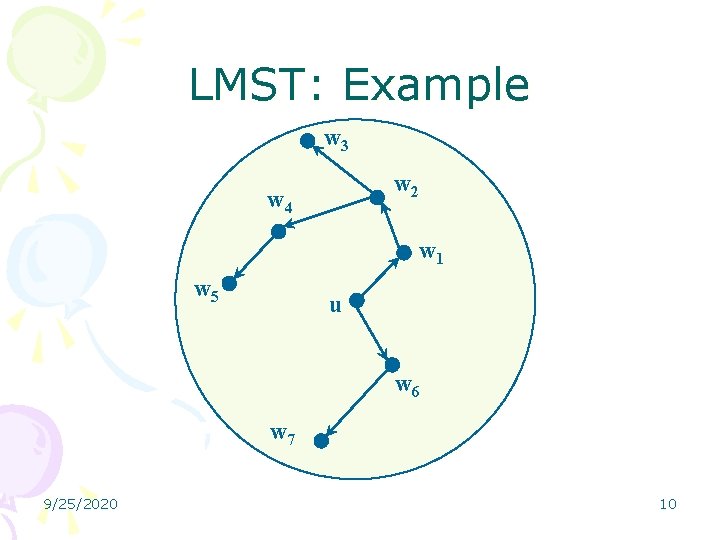
LMST: Example w 3 w 2 w 4 w 1 w 5 u w 6 w 7 9/25/2020 10
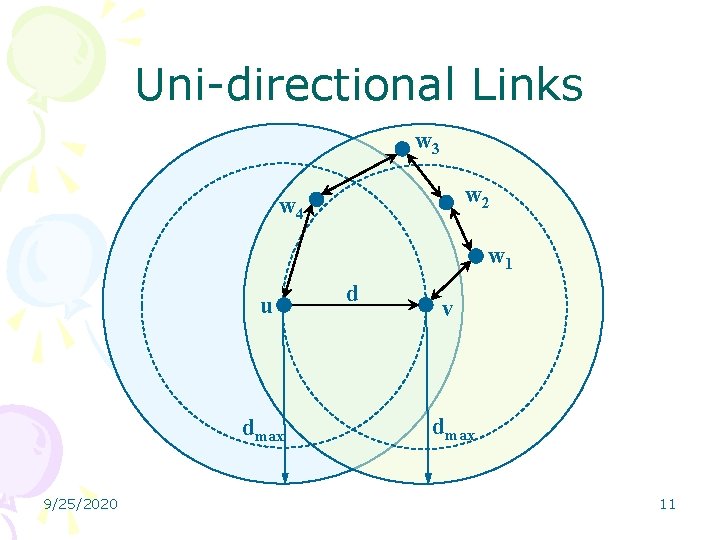
Uni-directional Links w 3 w 2 w 4 w 1 u dmax 9/25/2020 d v dmax 11
Connectivity • G 0 is connected with some unidirectional links. • We can either add extra links into G 0 so that all uni-directional links become bi-directional or delete all uni-directional links in G 0. • Both approaches give us connected graph with bi-directional links. 9/25/2020 12
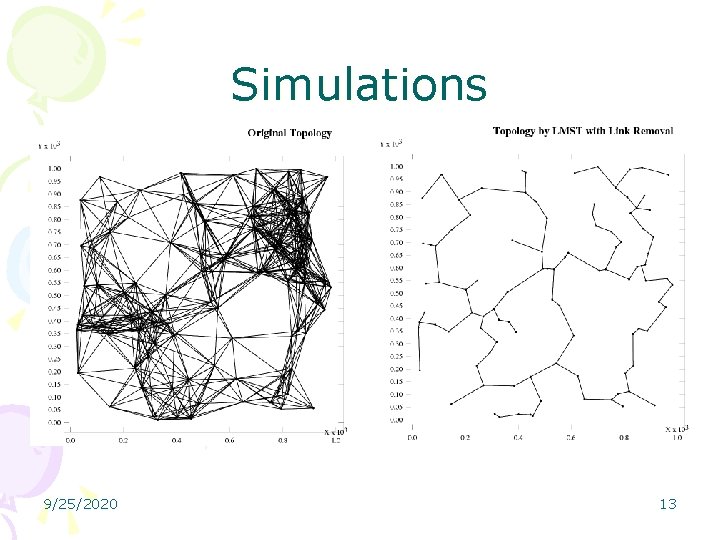
Simulations 9/25/2020 13
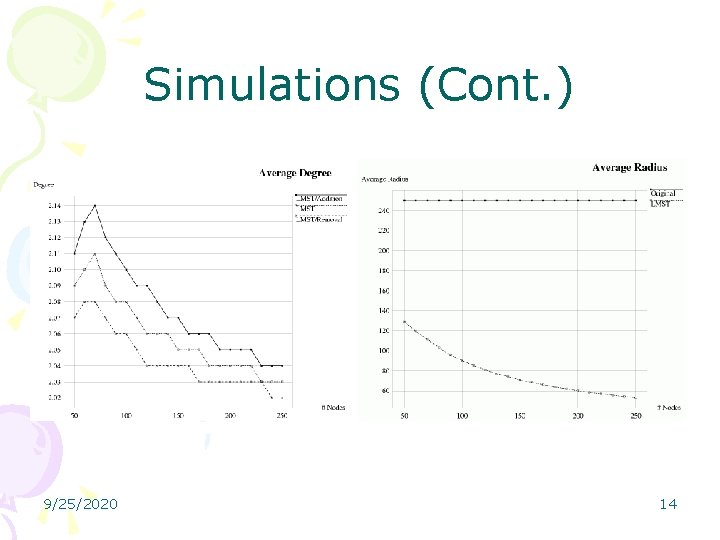
Simulations (Cont. ) 9/25/2020 14
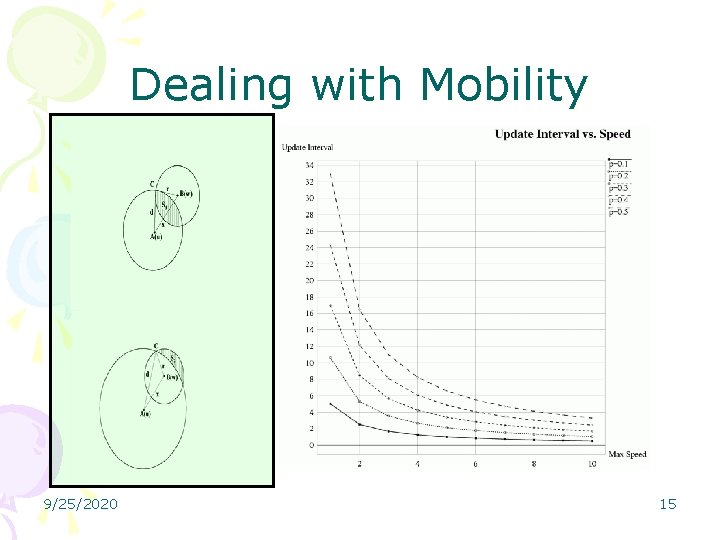
Dealing with Mobility 9/25/2020 15
Future Work • Extend LMST to mobile networks. • Build the multicast/broadcast protocol upon LMST. • Implement LMST on a Motes testbed at UIUC. 9/25/2020 16
- Slides: 16