DES Shift XOR register Sbox I Kim C
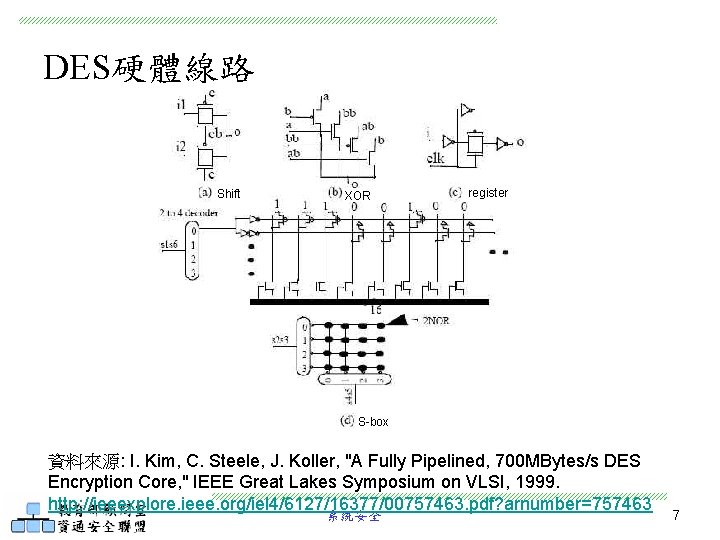
DES硬體線路 Shift XOR register S-box 資料來源: I. Kim, C. Steele, J. Koller, "A Fully Pipelined, 700 MBytes/s DES Encryption Core, " IEEE Great Lakes Symposium on VLSI, 1999. http: //ieeexplore. ieee. org/iel 4/6127/16377/00757463. pdf? arnumber=757463 系統安全 7
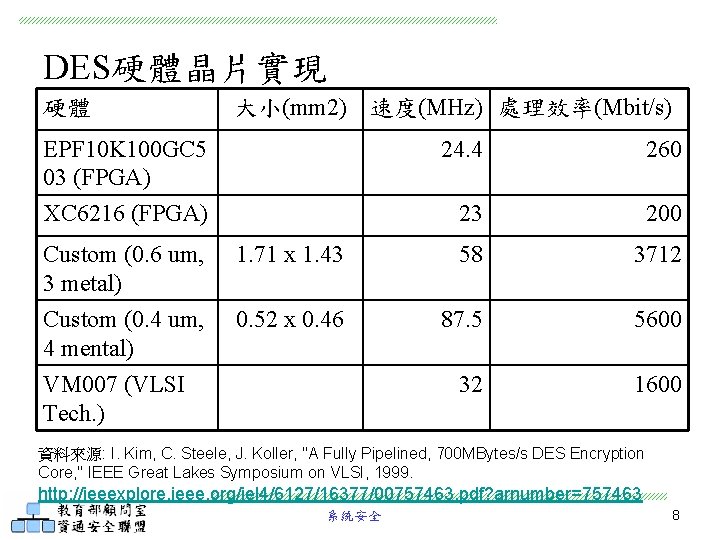
DES硬體晶片實現 硬體 大小(mm 2) 速度(MHz) 處理效率(Mbit/s) EPF 10 K 100 GC 5 03 (FPGA) 24. 4 260 XC 6216 (FPGA) 23 200 Custom (0. 6 um, 3 metal) 1. 71 x 1. 43 58 3712 Custom (0. 4 um, 4 mental) VM 007 (VLSI Tech. ) 0. 52 x 0. 46 87. 5 5600 32 1600 資料來源: I. Kim, C. Steele, J. Koller, "A Fully Pipelined, 700 MBytes/s DES Encryption Core, " IEEE Great Lakes Symposium on VLSI, 1999. http: //ieeexplore. ieee. org/iel 4/6127/16377/00757463. pdf? arnumber=757463 系統安全 8
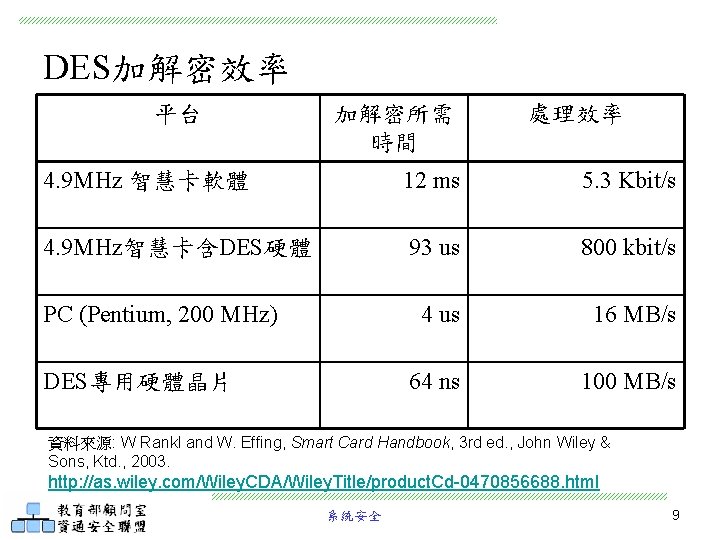
DES加解密效率 平台 加解密所需 時間 處理效率 4. 9 MHz 智慧卡軟體 12 ms 5. 3 Kbit/s 4. 9 MHz智慧卡含DES硬體 93 us 800 kbit/s 4 us 16 MB/s 64 ns 100 MB/s PC (Pentium, 200 MHz) DES專用硬體晶片 資料來源: W Rankl and W. Effing, Smart Card Handbook, 3 rd ed. , John Wiley & Sons, Ktd. , 2003. http: //as. wiley. com/Wiley. CDA/Wiley. Title/product. Cd-0470856688. html 系統安全 9
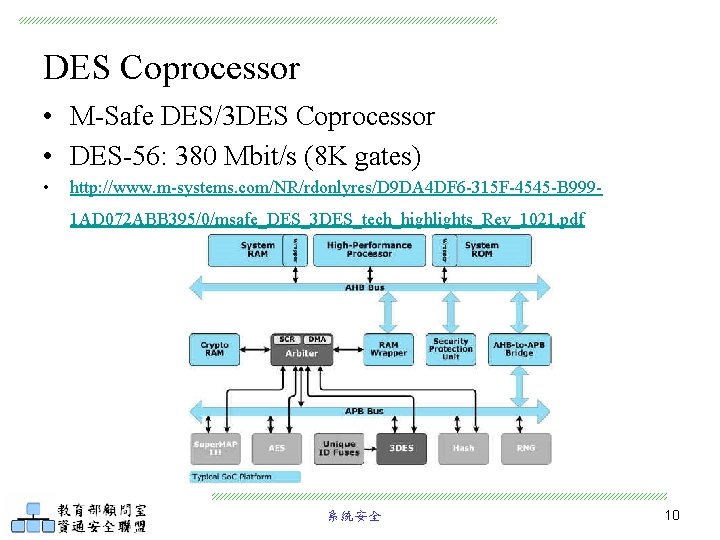
DES Coprocessor • M-Safe DES/3 DES Coprocessor • DES-56: 380 Mbit/s (8 K gates) • http: //www. m-systems. com/NR/rdonlyres/D 9 DA 4 DF 6 -315 F-4545 -B 9991 AD 072 ABB 395/0/msafe_DES_3 DES_tech_highlights_Rev_1021. pdf 系統安全 10

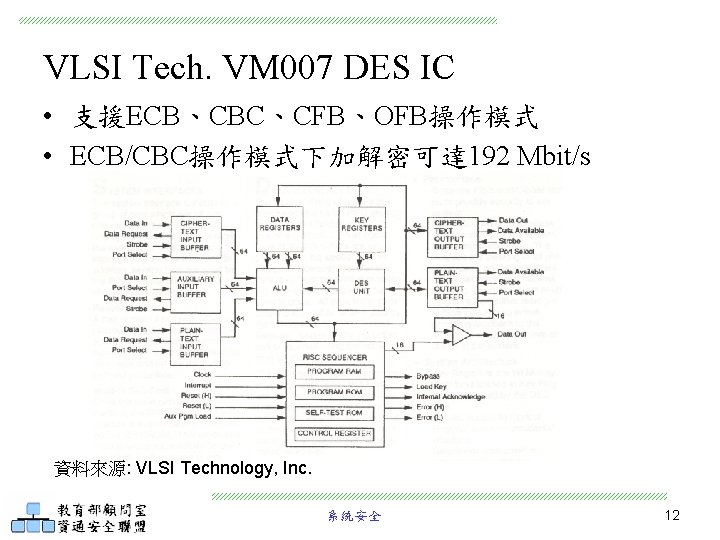
VLSI Tech. VM 007 DES IC • 支援ECB、CBC、CFB、OFB操作模式 • ECB/CBC操作模式下加解密可達 192 Mbit/s 資料來源: VLSI Technology, Inc. 系統安全 12

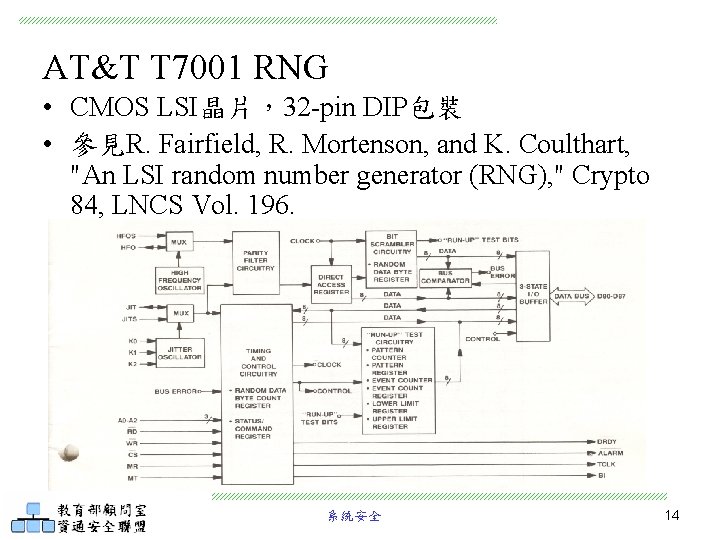
AT&T T 7001 RNG • CMOS LSI晶片,32 -pin DIP包裝 • 參見R. Fairfield, R. Mortenson, and K. Coulthart, "An LSI random number generator (RNG), " Crypto 84, LNCS Vol. 196. 系統安全 14

RSA硬體 • RSA演算法可用於加解密或數位簽章 • 80年代的Crypto或Euro. Crypto會議常見RSA晶片的 設計報告論文,例如:M. Kochanski, “Developing an RSA chip, ” Crypto’ 85 或 R. Rivest, “RSA chips (past/present/future), ” Euro. Crypt’ 84 • 於數位信號處理器(DSP)可採用Montgomery乘法 加速模指數計算,參見 Dusse and Kaliski, "A Cryptographic Library for the Motorola DSP 56000, " Proc. Eurocrypt'90. • 實務上常以中國剩餘定理(Chinese Remainder Theorem)來加速解密或簽章的產生 系統安全 16

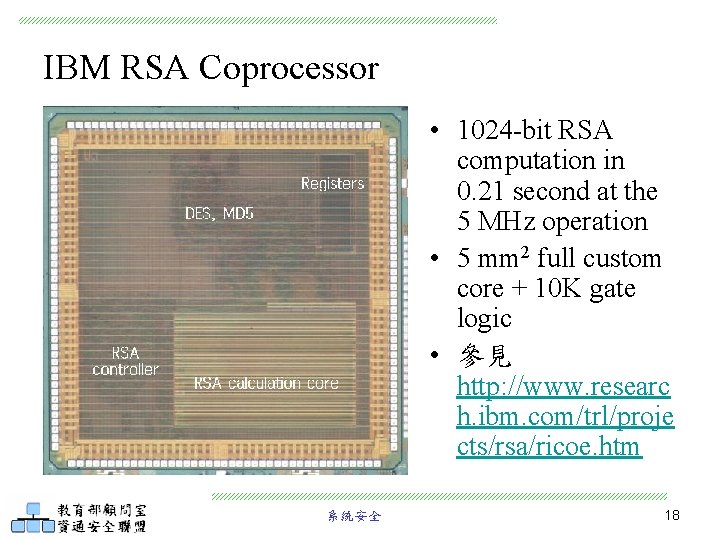
IBM RSA Coprocessor • 1024 -bit RSA computation in 0. 21 second at the 5 MHz operation • 5 mm 2 full custom core + 10 K gate logic • 參見 http: //www. researc h. ibm. com/trl/proje cts/rsa/ricoe. htm 系統安全 18

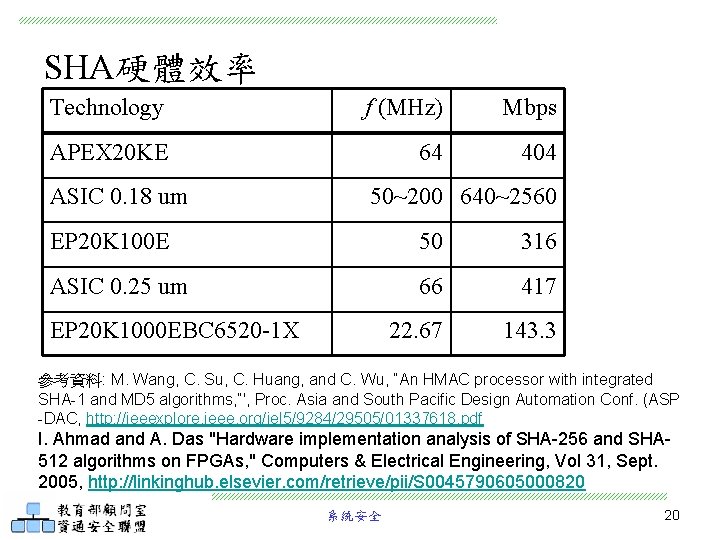
SHA硬體效率 Technology f (MHz) Mbps APEX 20 KE 64 404 ASIC 0. 18 um 50~200 640~2560 EP 20 K 100 E 50 316 ASIC 0. 25 um 66 417 22. 67 143. 3 EP 20 K 1000 EBC 6520 -1 X 參考資料: M. Wang, C. Su, C. Huang, and C. Wu, “An HMAC processor with integrated SHA-1 and MD 5 algorithms, ”', Proc. Asia and South Pacific Design Automation Conf. (ASP -DAC, http: //ieeexplore. ieee. org/iel 5/9284/29505/01337618. pdf I. Ahmad and A. Das "Hardware implementation analysis of SHA-256 and SHA 512 algorithms on FPGAs, " Computers & Electrical Engineering, Vol 31, Sept. 2005, http: //linkinghub. elsevier. com/retrieve/pii/S 0045790605000820 系統安全 20
DSA硬體 • 1994年美國正式公佈數位簽章演算法(Digital Signature Algorithm,DSA) • DSA的實現可參考密碼模組檢驗, http: //csrc. nist. gov/cryptval/dss/dsaval. htm 系統安全 21

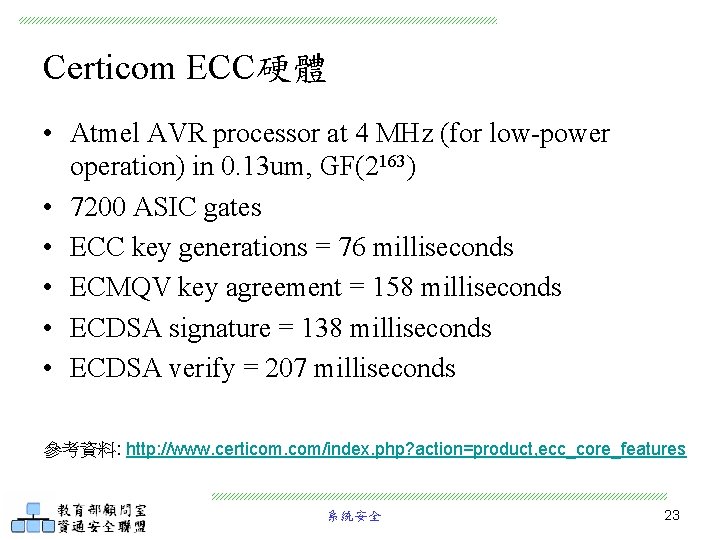
Certicom ECC硬體 • Atmel AVR processor at 4 MHz (for low-power operation) in 0. 13 um, GF(2163) • 7200 ASIC gates • ECC key generations = 76 milliseconds • ECMQV key agreement = 158 milliseconds • ECDSA signature = 138 milliseconds • ECDSA verify = 207 milliseconds 參考資料: http: //www. certicom. com/index. php? action=product, ecc_core_features 系統安全 23


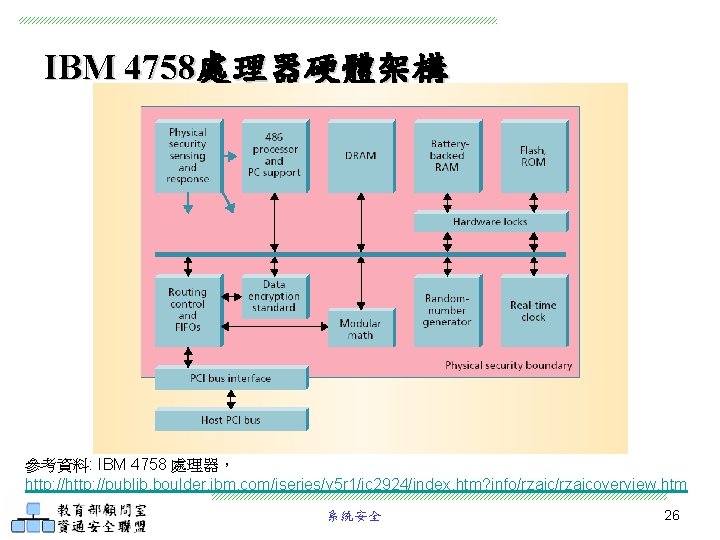
IBM 4758處理器硬體架構 參考資料: IBM 4758 處理器, http: //publib. boulder. ibm. com/iseries/v 5 r 1/ic 2924/index. htm? info/rzajcoverview. htm 系統安全 26
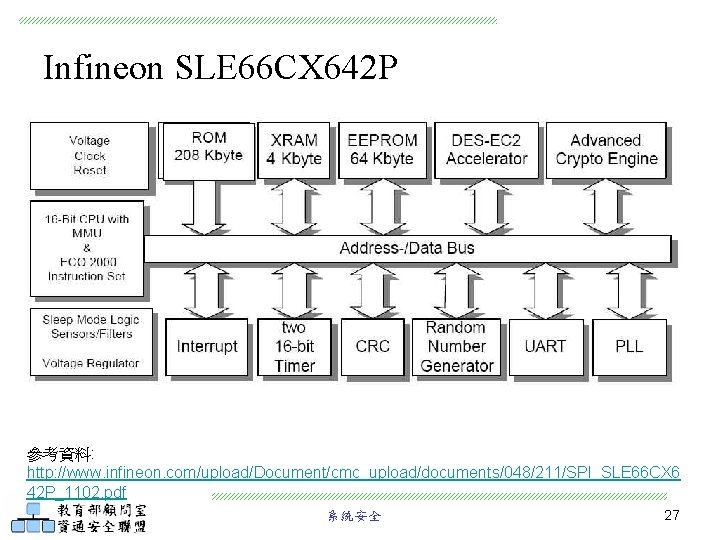
Infineon SLE 66 CX 642 P 參考資料: http: //www. infineon. com/upload/Document/cmc_upload/documents/048/211/SPI_SLE 66 CX 6 42 P_1102. pdf 系統安全 27
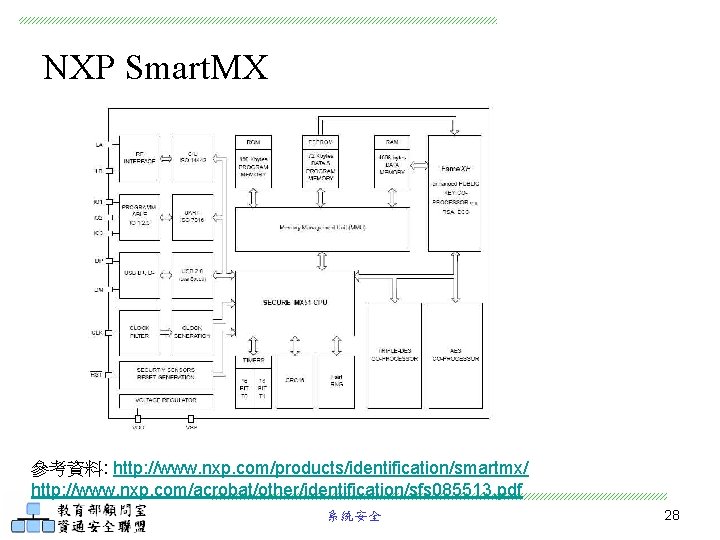
NXP Smart. MX 參考資料: http: //www. nxp. com/products/identification/smartmx/ http: //www. nxp. com/acrobat/other/identification/sfs 085513. pdf 系統安全 28
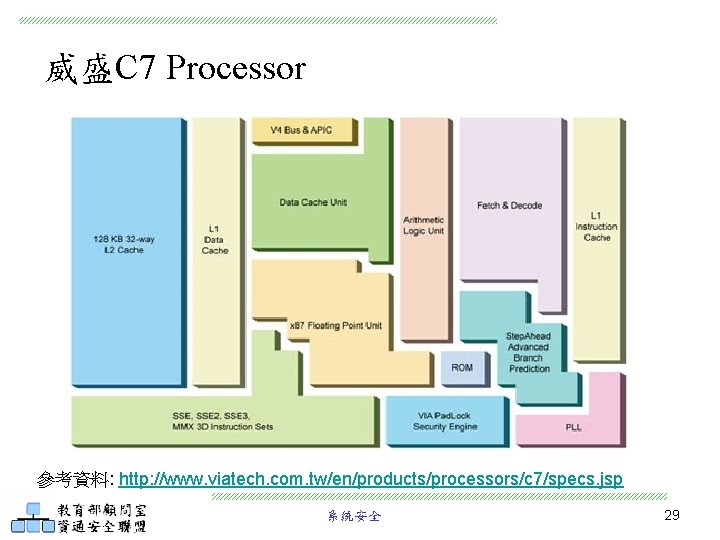
威盛C 7 Processor 參考資料: http: //www. viatech. com. tw/en/products/processors/c 7/specs. jsp 系統安全 29
參考資料 • NIST, FIPS 140 -2, Security Requirements for Cryptographic Modules, June 2001. http: //csrc. nist. gov/publications/fips 140 -2/fips 1402. pdf • NIST, Validated FIPS 140 -1 and FIPS 140 -2 Cryptographic Modules, http: //csrc. nist. gov/cryptval/140 -1/1401 val. htm • L. Batina, S. Ors, B. Preneel, and J. Vandewalle, “Hardware Architectures for Public Key Cryptography, ” http: //www. cosic. esat. kuleuven. be/publications/article-31. pdf • RSA Conference, http: //www. rsaconference. com/ 系統安全 30
- Slides: 30