Dept of Homeland Security Science Technology Directorate Driving


- Slides: 40
Dept. of Homeland Security Science & Technology Directorate Driving Security Improvements in Existing Technologies 12 February 2008 and Emerging Systems EDUCAUSE Net@EDU Annual Mtg Tempe, AZ February 12, 2008 Douglas Maughan, Ph. D. Program Manager, CCI douglas. maughan@dhs. gov 202 -254 -6145 / 202 -360 -3170
Agenda l l 2007 Capitol Hill and Other WDC Activities DHS S&T Cyber Security R&D Program u PREDICT u Broad Agency Announcements (BAAs) u Outreach / Transition l l University Programs Cyber R&D Background and Government R&D Coordination 12 February 2008 2
Recent Hearings in Washington l Cyber Insecurity: Hackers are Penetrating Federal Systems and Critical Infrastructure u http: //homeland. house. gov/hearings/index. asp? ID=36 n l “These incidents have opened a lot of eyes in the halls of Congress. We need to get serious about this threat to our national security. ” Addressing the Nation’s Cybersecurity Challenges: Reducing Vulnerabilities Requires Strategic Investment and Immediate Action” u http: //homeland. house. gov/hearings/index. asp? ID=41 n “I am deeply troubled by the lack of foresight that this Administration has demonstrated. The Homeland Security Committee is working to demonstrate the importance of R&D funding to this Administration. ” 12 February 2008 3
Recent Hearings in Washington (cont’d) l House Homeland Security Committee investigation of DHS Networks u http: //homeland. house. gov/Site. Documents/Charbo. pdf u 13 questions to understand the security posture of DHS networks l Senate Hearing on Terrorist use of the Internet u http: //hsgac. senate. gov/index. cfm? Fuseaction=Hearings. De tail&Hearing. ID=441 12 February 2008 4
More recent activity l May 2007 – DDOS attack on Estonia u First example of “cyber warfare”? l l Sep 2007 - “Chinese hack the Pentagon” Sep 2007 – “China hacks UK government” Oct 2007 – “White House initiative to defend against hackers” Nov 2007 – “White House requests $154 M supplement for Cyber Initiative” 12 February 2008 5
(National) Cyber Initiative l l Baltimore Sun Article on Cyber Initiative – Oct. 24, 2007 House panel chief demands details of cybersecurity plan u http: //www. baltimoresun. com/technology/balte. cyber 24 oct 24, 0, 782050, full. story l Rep. Bennie Thompson, Chairman of the House Homeland Security Committee, called on the Bush administration to delay the planned launch of a multi-billion-dollar cybersecurity initiative so that Congress could have time to evaluate it. l Initiative mostly focused on fixing operational problems that exist across government infrastructure u l E. g. , Trusted Internet Connections (TIC) program announcement Small component of total effort is aimed at R&D 12 February 2008 6
CSIS Commission for 44 th Presidency l l Goal: Identify a strategy and set of recommendations for the next administration to move ahead in securing cyberspace. The Commission will complete its work by December 2008. The Commission will be a bipartisan group composed of thirty to thirtyfive experts drawn from the cyber security policy community and from the private sector. u u l The proposed working groups are: u u l Co-chaired by leaders from Congress and the private sector Reinforced by a private sector advisory group composed of representatives from companies and associations (1) Federal Organization, Strategy and Doctrine; (2) Cybersecurity Norms and Authorities; (3) Budget and Acquisitions for Cybersecurity; (4) Government/Private Sector Interfaces and Engagement. The final product would be a well-supported package of recommendations for improving cyber security that could help to guide both a legislative agenda and Presidential policy documents. 12 February 2008 7

Homeland Security Mission l l l Lead unified national effort to secure America Prevent terrorist attacks within the U. S. Respond to threats and hazards to the nation Ensure safe and secure borders Welcome lawful immigrants and visitors Promote free flow of commerce 12 February 2008 8
DHS Goals: Secretary’s Priorities l Keep terrorists, criminals and unlawful entrants out of the U. S. l Prevent dangerous materials, weapons and illicit drugs from entering the country l Strengthen screening of workers/travelers l Secure critical infrastructure l Build nimble, effective emergency response system and culture of preparedness l Strengthen core management to ensure DHS is a great organization 12 February 2008 9
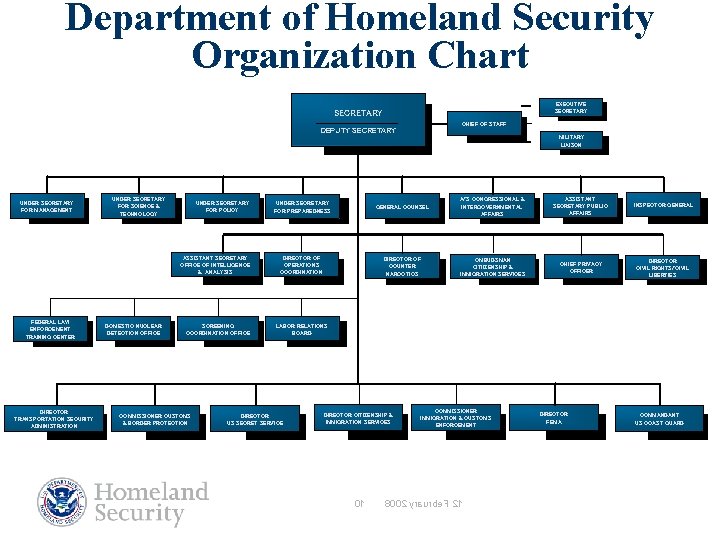
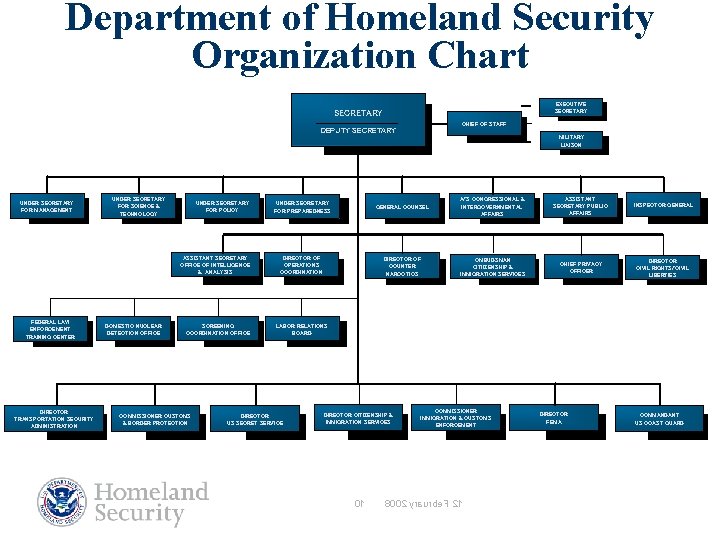
Department of Homeland Security Organization Chart EXECUTIVE SECRETARY CHIEF OF STAFF DEPUTY SECRETARY MILITARY LIAISON UNDER SECRETARY FOR MANAGEMENT UNDER SECRETARY FOR SCIENCE & TECHNOLOGY UNDER SECRETARY FOR POLICY ASSISTANT SECRETARY OFFICE OF INTELLIGENCE & ANALYSIS FEDERAL LAW ENFORCEMENT TRAINING CENTER DIRECTOR TRANSPORTATION SECURITY ADMINISTRATION DOMESTIC NUCLEAR DETECTION OFFICE SCREENING COORDINATION OFFICE COMMISSIONER CUSTOMS & BORDER PROTECTION UNDER SECRETARY FOR PREPAREDNESS GENERAL COUNSEL A/S CONGRESSIONAL & INTERGOVERNMENTAL AFFAIRS ASSISTANT SECRETARY PUBLIC AFFAIRS INSPECTOR GENERAL DIRECTOR OF OPERATIONS COORDINATION DIRECTOR OF COUNTER NARCOTICS OMBUDSMAN CITIIZENSHIP & IMMIGRATION SERVICES CHIEF PRIVACY OFFICER DIRECTOR CIVIL RIGHTS/CIVIL LIBERTIES LABOR RELATIONS BOARD DIRECTOR US SECRET SERVICE DIRECTOR CITIZENSHIP & IMMIGRATION SERVICES 01 COMMISSIONER IMMIGRATION & CUSTOMS ENFORCEMENT 8002 yraurbe. F 21 DIRECTOR FEMA COMMANDANT US COAST GUARD
Science and Technology (S&T) Mission Conduct, stimulate, and enable research, development, test, evaluation and timely transition of homeland security capabilities to federal, state and local operational end-users. 12 February 2008 11
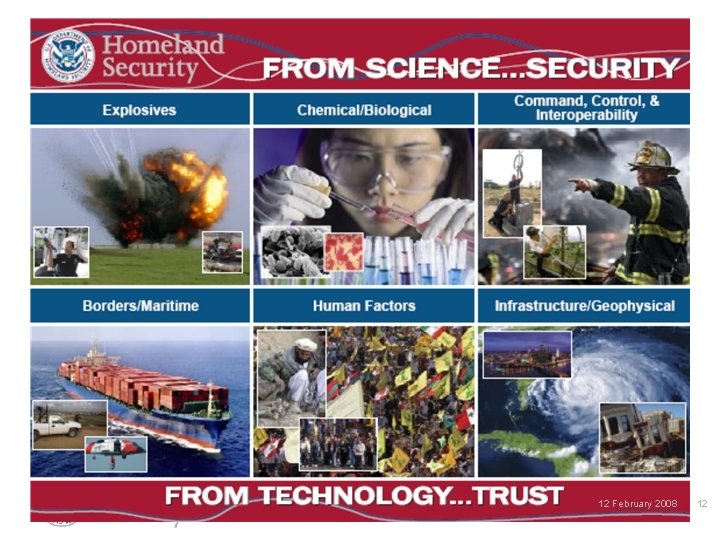
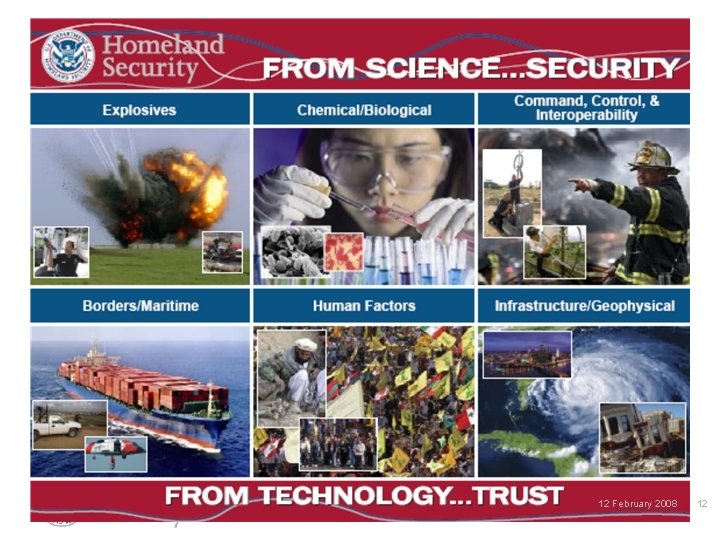
12 February 2008 12
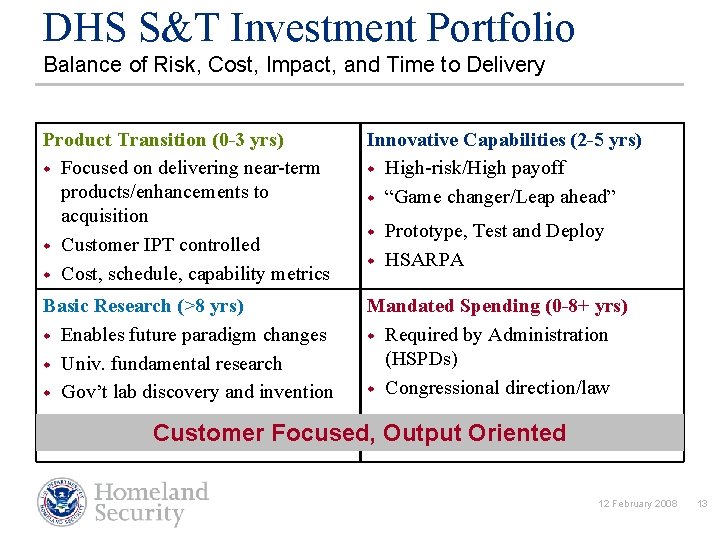
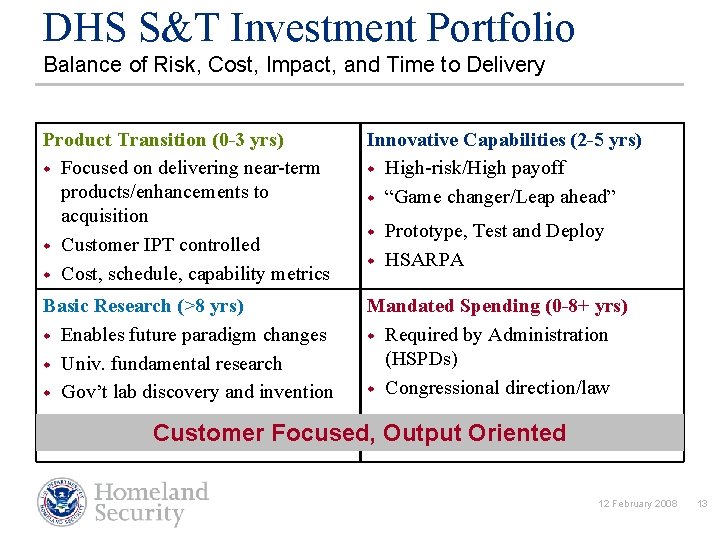
DHS S&T Investment Portfolio Balance of Risk, Cost, Impact, and Time to Delivery Product Transition (0 -3 yrs) w Focused on delivering near-term products/enhancements to acquisition w Customer IPT controlled w Cost, schedule, capability metrics Innovative Capabilities (2 -5 yrs) w High-risk/High payoff w “Game changer/Leap ahead” Basic Research (>8 yrs) w Enables future paradigm changes w Univ. fundamental research w Gov’t lab discovery and invention Mandated Spending (0 -8+ yrs) w Required by Administration (HSPDs) w Congressional direction/law w w Prototype, Test and Deploy HSARPA Customer Focused, Output Oriented 12 February 2008 13
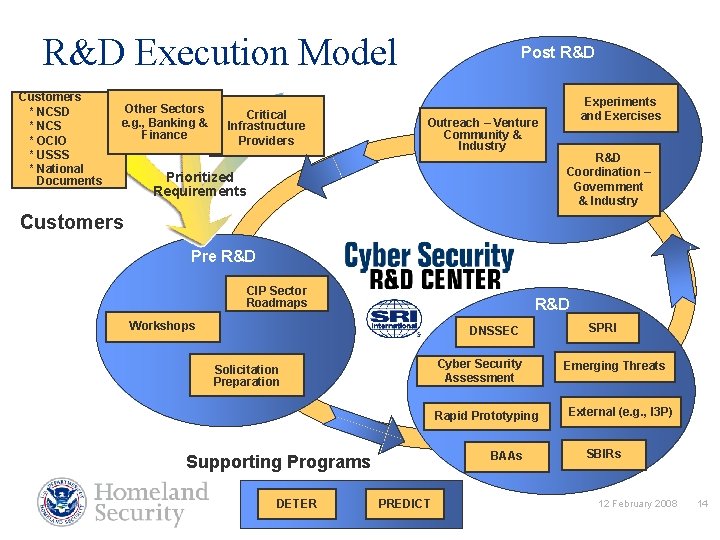
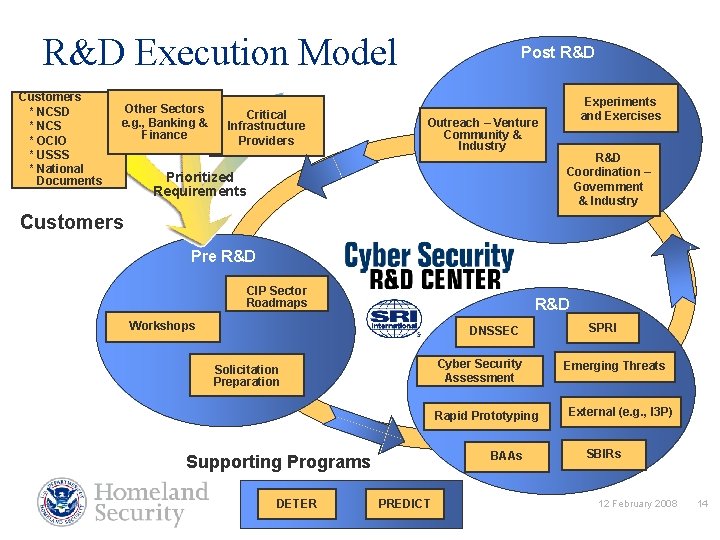
R&D Execution Model Customers * NCSD * NCS * OCIO * USSS * National Documents Other Sectors e. g. , Banking & Finance Critical Infrastructure Providers Post R&D Outreach – Venture Community & Industry Prioritized Requirements Experiments and Exercises R&D Coordination – Government & Industry Customers Pre R&D CIP Sector Roadmaps R&D Workshops DNSSEC Cyber Security Assessment Solicitation Preparation Rapid Prototyping BAAs Supporting Programs DETER PREDICT SPRI Emerging Threats External (e. g. , I 3 P) SBIRs 12 February 2008 14
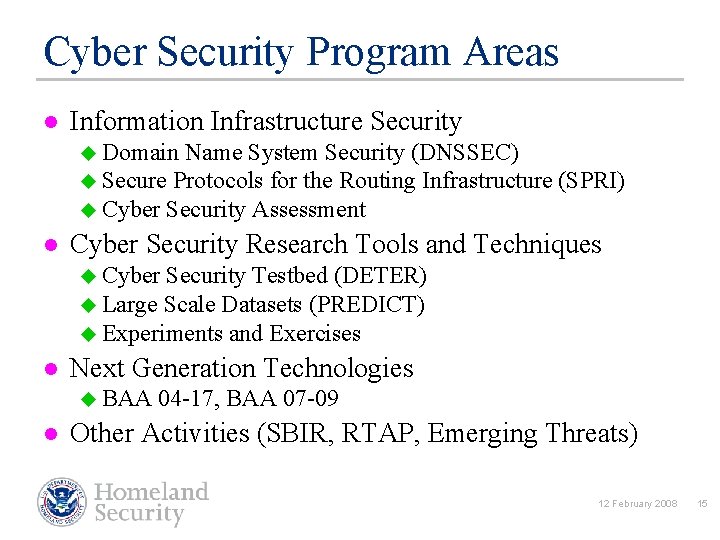
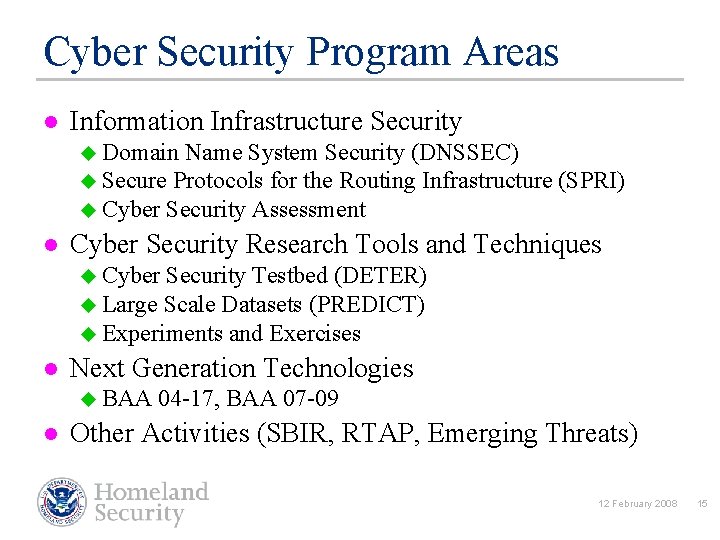
Cyber Security Program Areas l Information Infrastructure Security u Domain Name System Security (DNSSEC) u Secure Protocols for the Routing Infrastructure (SPRI) u Cyber Security Assessment l Cyber Security Research Tools and Techniques u Cyber Security Testbed (DETER) u Large Scale Datasets (PREDICT) u Experiments and Exercises l Next Generation Technologies u BAA 04 -17, BAA 07 -09 l Other Activities (SBIR, RTAP, Emerging Threats) 12 February 2008 15
DHS / NSF Cyber Security Testbed l l “Justification and Requirements for a National DDOS Defense Technology Evaluation Facility”, July 2002 We still lack large-scale deployment of security technology sufficient to protect our vital infrastructures u l l Recent investment in research on cyber security technologies by government agencies (NSF, DARPA, armed services) and industry. One important reason is the lack of an experimental infrastructure and rigorous scientific methodologies for developing and testing next-generation defensive cyber security technology The goal is to create, operate, and support a researcher-andvendor-neutral experimental infrastructure that is open to a wide community of users and produce scientifically rigorous testing frameworks and methodologies to support the development and demonstration of next-generation cyber defense technologies 12 February 2008 16
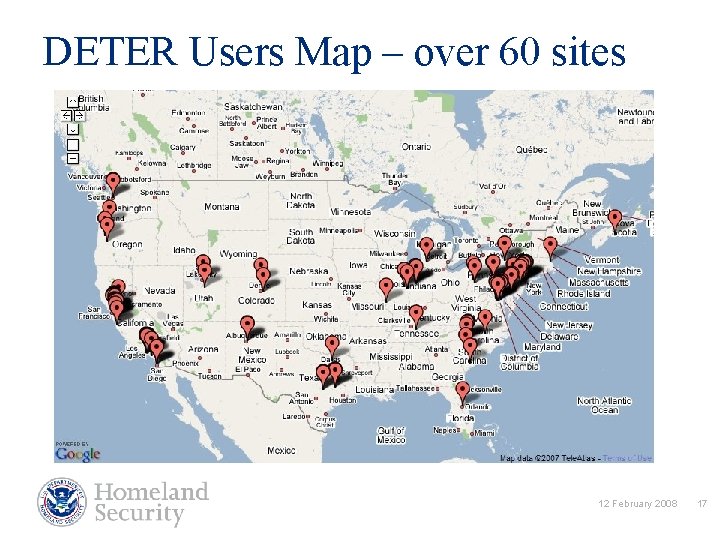
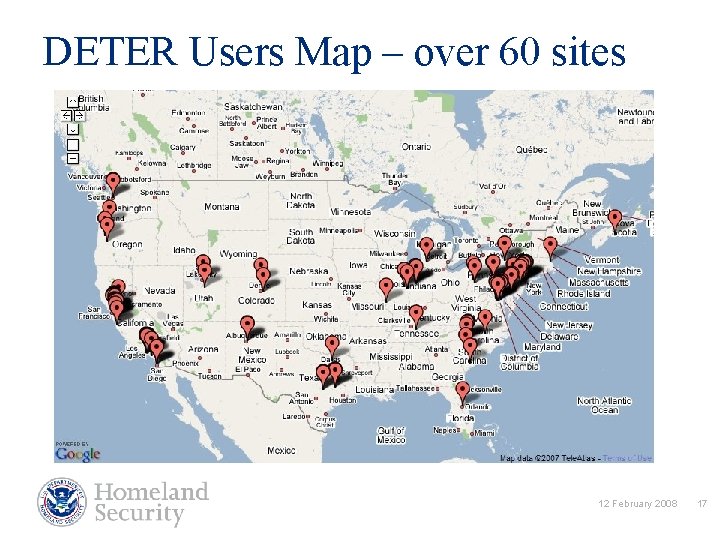
DETER Users Map – over 60 sites 12 February 2008 17
A Protected REpository for Defense of Infrastructure against Cyber Threats l PREDICT Program Objective “To advance the state of the research and commercial development (of network security ‘products’) we need to produce datasets for information security testing and evaluation of maturing networking technologies. ” l Rationale / Background / Historical: u u Researchers with insufficient access to data unable to adequately test their research prototypes Government technology decision-makers with no data to evaluate competing “products” End Goal: Improve the quality of defensive cyber security technologies 12 February 2008 18
PREDICT Information l https: //www. predict. org 12 February 2008 19
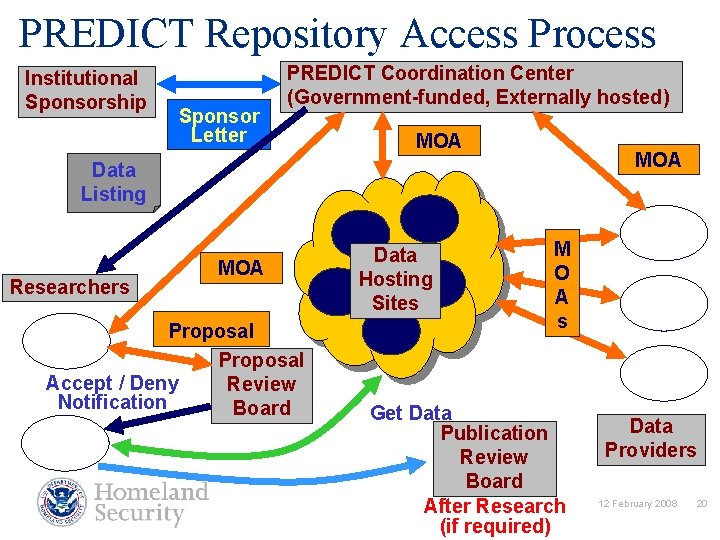
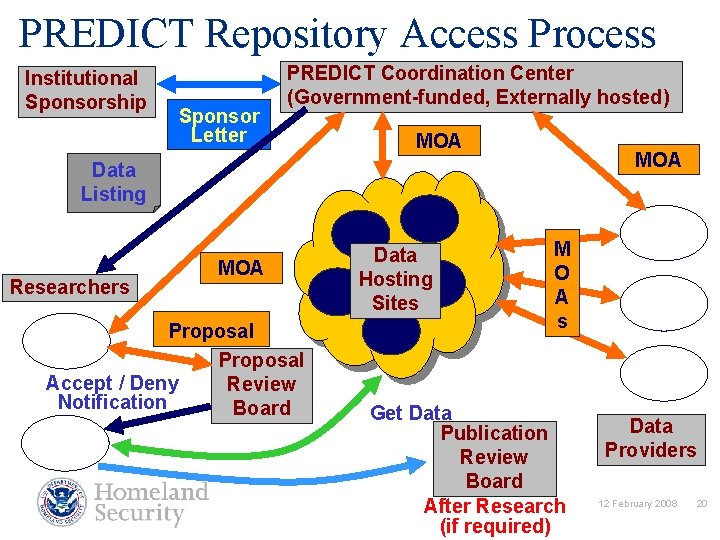
PREDICT Repository Access Process Institutional Sponsorship Sponsor Letter PREDICT Coordination Center (Government-funded, Externally hosted) MOA Data Listing Researchers MOA Proposal Accept / Deny Review Notification Board Data Hosting Sites M O A s Get Data Publication Review Board After Research (if required) Data Providers 12 February 2008 20
Data Collection Activities l Classes of data that are interesting, people want collected, and seem reasonable to collect u Netflow u Packet traces – headers and full packet (context dependent) u Critical infrastructure – BGP and DNS data u Topology data u IDS / firewall logs u Performance data u Network management data (i. e. , SNMP) u Vo. IP (2200 IP-phone network) u Blackhole Monitor traffic 12 February 2008 21
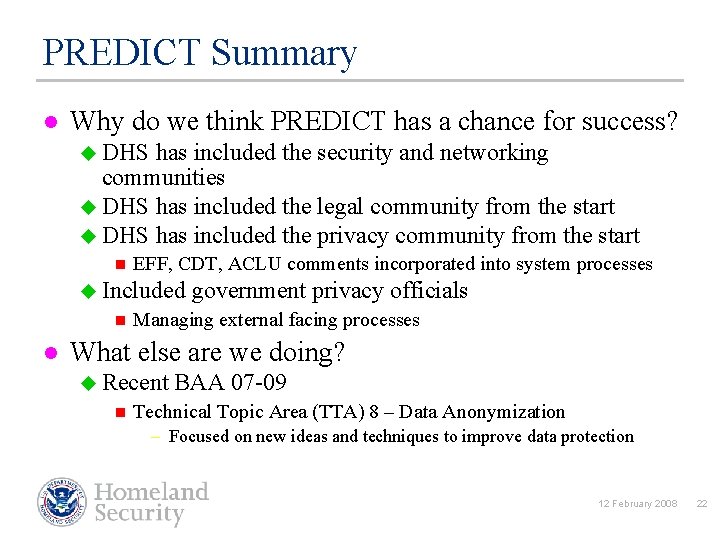
PREDICT Summary l Why do we think PREDICT has a chance for success? u DHS has included the security and networking communities u DHS has included the legal community from the start u DHS has included the privacy community from the start n EFF, CDT, ACLU comments incorporated into system processes u Included government privacy officials n l Managing external facing processes What else are we doing? u Recent BAA 07 -09 n Technical Topic Area (TTA) 8 – Data Anonymization – Focused on new ideas and techniques to improve data protection 12 February 2008 22
Cyber Security R&D Broad Agency Announcement (BAA) l A critical area of focus for DHS is the development and deployment of technologies to protect the nation’s cyber infrastructure including the Internet and other critical infrastructures that depend on computer systems for their mission. The goals of the Cyber Security Research and Development (CSRD) program are: u u u l To perform research and development (R&D) aimed at improving the security of existing deployed technologies and to ensure the security of new emerging systems; To develop new and enhanced technologies for the detection of, prevention of, and response to cyber attacks on the nation’s critical information infrastructure. To facilitate the transfer of these technologies into the national infrastructure as a matter of urgency. http: //www. hsarpabaa. com 12 February 2008 23
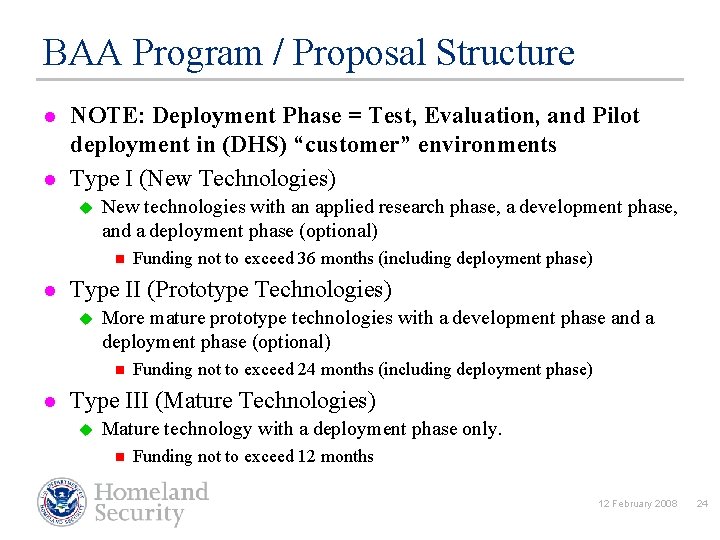
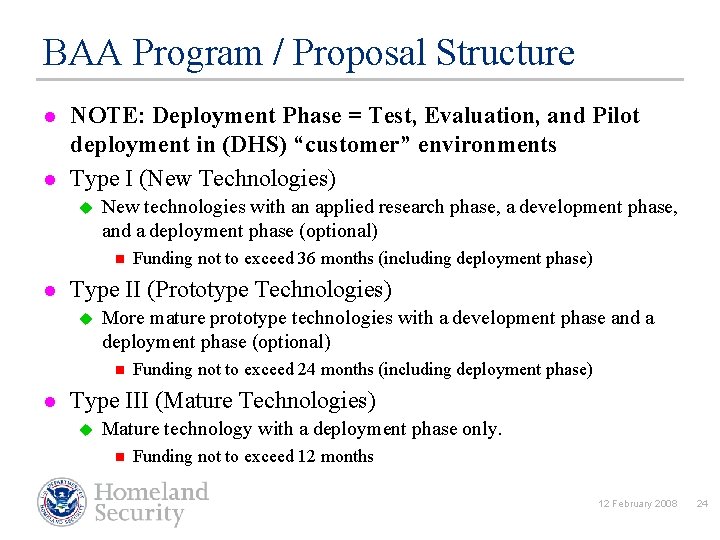
BAA Program / Proposal Structure l l NOTE: Deployment Phase = Test, Evaluation, and Pilot deployment in (DHS) “customer” environments Type I (New Technologies) u New technologies with an applied research phase, a development phase, and a deployment phase (optional) n l Type II (Prototype Technologies) u More mature prototype technologies with a development phase and a deployment phase (optional) n l Funding not to exceed 36 months (including deployment phase) Funding not to exceed 24 months (including deployment phase) Type III (Mature Technologies) u Mature technology with a deployment phase only. n Funding not to exceed 12 months 12 February 2008 24
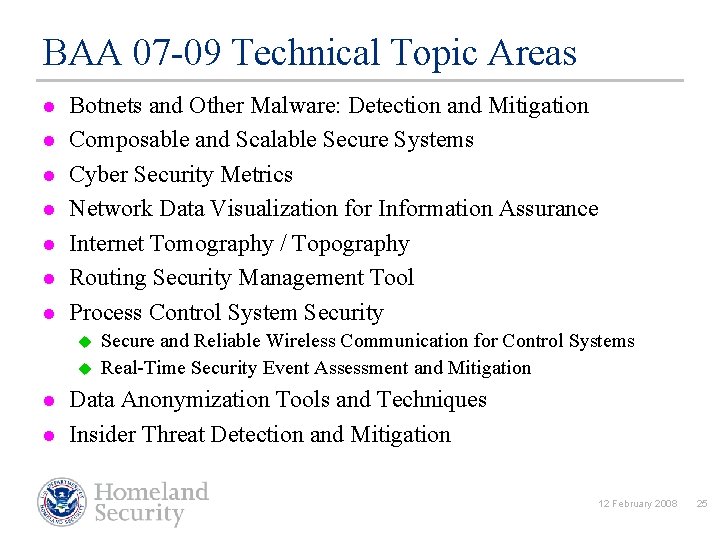
BAA 07 -09 Technical Topic Areas l l l l Botnets and Other Malware: Detection and Mitigation Composable and Scalable Secure Systems Cyber Security Metrics Network Data Visualization for Information Assurance Internet Tomography / Topography Routing Security Management Tool Process Control System Security u u l l Secure and Reliable Wireless Communication for Control Systems Real-Time Security Event Assessment and Mitigation Data Anonymization Tools and Techniques Insider Threat Detection and Mitigation 12 February 2008 25
Partnership l Project LOGIIC is a model for government-industry technology integration and demonstration efforts to address critical R&D needs l Industry contributes u u u l Requirements and operational expertise Project management Product vendor channels DHS S&T contributes u u National Security Perspective on threats Access to long term security research Independent researchers with technical expertise Testing facilities 12 February 2008 26
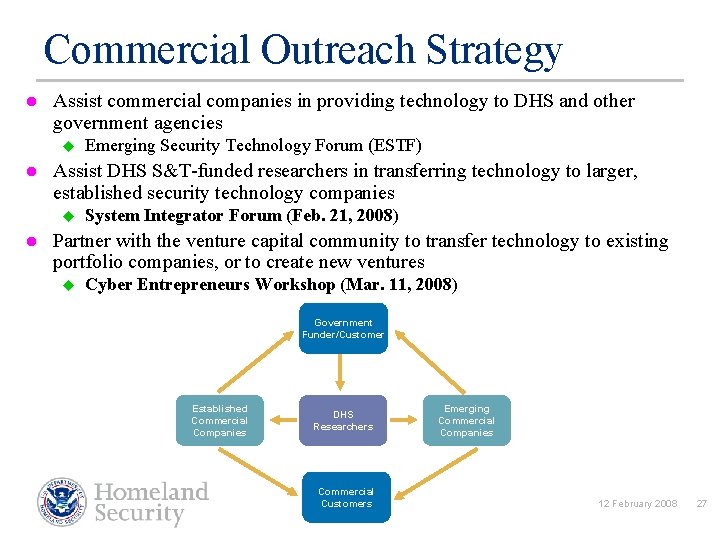
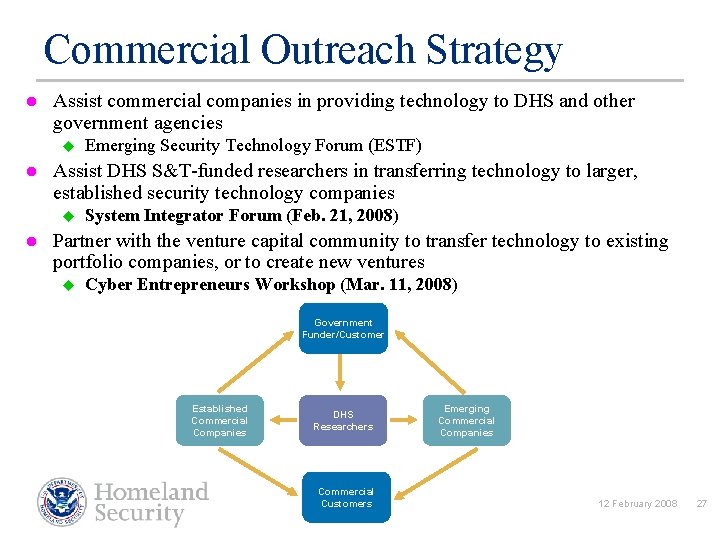
Commercial Outreach Strategy l Assist commercial companies in providing technology to DHS and other government agencies u l Assist DHS S&T-funded researchers in transferring technology to larger, established security technology companies u l Emerging Security Technology Forum (ESTF) System Integrator Forum (Feb. 21, 2008) Partner with the venture capital community to transfer technology to existing portfolio companies, or to create new ventures u Cyber Entrepreneurs Workshop (Mar. 11, 2008) Government Funder/Customer Established Commercial Companies DHS Researchers Commercial Customers Emerging Commercial Companies 12 February 2008 27
System Integrator Forum 2008 l Iron. Key, Palo Alto, CA u l HBGary, Chevy Chase, MD u l Network Vulnerability Analysis/Discovery Endeavor Systems, Arlington, VA u l Software Analysis (Binary and Source) George Mason Univ, Fairfax, VA u l Malware Discovery Tool Grammatech, Ithaca, NY u l Secure USB Token Pattern Recognition and Signature Analysis 2008 SIF – February 21 in WDC (see website) 12 February 2008 28
IT Security Entrepreneur Forum (ITSEF) l l l l Hot Topics - Current Market Trends and Conditions How to Optimize Having the Government as Your Partner Communicating Your Value Proposition The Risks and Rewards of Selling to the Government Navigating the Government Procurement Process from A to Z Financing Your Startup in the Information Security Space through Government Funds 2008 ITSEF – March 11 @ Stanford u http: //www. publicprivatepartnerships. org 12 February 2008 29
University Programs Centers of Excellence (COE) l Program Goals u Develop the management and communications infrastructure to produce, share and transition Centers’ research results, data and technology to analysts and policymakers u Align existing Centers and establish new Centers and initiatives to align with S&T Divisions’ research and development activities, and address additional DHS needs u Deliver the Centers’ advanced research products, technology and educated workforce that DHS will need to protect the country for the foreseeable future 12 February 2008 30
Current Centers of Excellence w Center for Risk & Economic Analysis of Terrorism Events (CREATE) Based at the Univ. of Southern California w National Center for Food Protection & Defense (NCFPD) Based at the Univ. of Minnesota w National Center for Foreign Animal & Zoonotic Disease Defense (FAZD) Based at Texas A&M Univ. w National Consortium for the Study of Terrorism & Responses to Terrorism (START) Based at the Univ. of Maryland w National Center for Preparedness & Catastrophic Event Response (PACER) Based at Johns Hopkins Univ. 12 February 2008 31

Centers of Excellence, cont. w Center for Advancing Microbial Risk Assessment (CAMRA) Based at Michigan State Univ. , in Partnership with U. S. EPA w Univ. Affiliate Centers to the Institute for Discrete Sciences (IDS-UACs) In Partnership with Lawrence Livermore National Laboratory: Rutgers Univ. (Lead Center), Univ. of Southern California, Univ. of Illinois at Urbana-Champaign, Univ. of Pittsburgh w Regional Visualization & Analytics Centers (RVACs) In Partnership with National VAC at Pacific Northwest National Laboratory: Penn State Univ. , Purdue Univ. , Stanford Univ. , Univ. of North Carolina at Charlotte, Univ. of Washington Other University Research Initiatives w Southeast Regional Research Initiative (SERRI) w Kentucky Critical Infrastructure Protection Institute (KCI) 12 February 2008 32
New Centers Beginning in FY 2007 -08 • COE for Explosives Detection, Mitigation and Response (Funded FY 2007) • COE for Border Security and Immigration (Funded FY 2007) Northern Forest Borders • Southwest Desert Borders • • COE for Maritime, Island & Remote/Extreme Environment Security (Funded FY 2007) • COE for Natural Disasters, Coastal Infrastructure and Emergency Management (Funded FY 2008) 12 February 2008 33
Education Programs l l l Individual Scholarships and Fellowships Institutional Scholarships & Fellowships Summer Internships AAAS/AVMA Visiting Scholars Post-Doc Program 12 February 2008 34
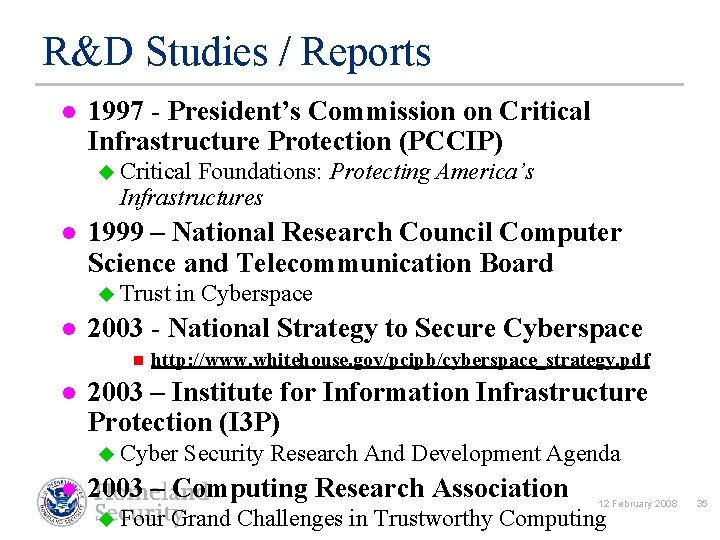
R&D Studies / Reports l 1997 - President’s Commission on Critical Infrastructure Protection (PCCIP) u Critical Foundations: Protecting Infrastructures l America’s 1999 – National Research Council Computer Science and Telecommunication Board u Trust in Cyberspace l 2003 - National Strategy to Secure Cyberspace n l http: //www. whitehouse. gov/pcipb/cyberspace_strategy. pdf 2003 – Institute for Information Infrastructure Protection (I 3 P) u Cyber Security Research And Development Agenda l 2003 – Computing Research Association 12 February 2008 u Four Grand Challenges in Trustworthy Computing 35
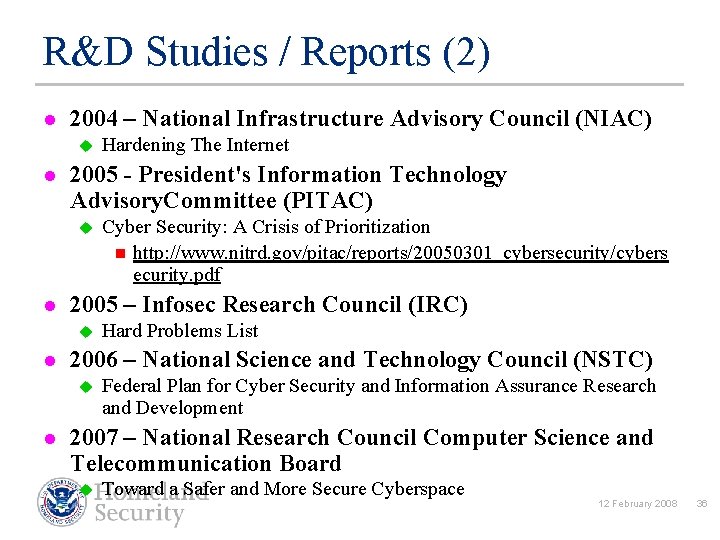
R&D Studies / Reports (2) l 2004 – National Infrastructure Advisory Council (NIAC) u l 2005 - President's Information Technology Advisory. Committee (PITAC) u l Hard Problems List 2006 – National Science and Technology Council (NSTC) u l Cyber Security: A Crisis of Prioritization n http: //www. nitrd. gov/pitac/reports/20050301_cybersecurity/cybers ecurity. pdf 2005 – Infosec Research Council (IRC) u l Hardening The Internet Federal Plan for Cyber Security and Information Assurance Research and Development 2007 – National Research Council Computer Science and Telecommunication Board u Toward a Safer and More Secure Cyberspace 12 February 2008 36
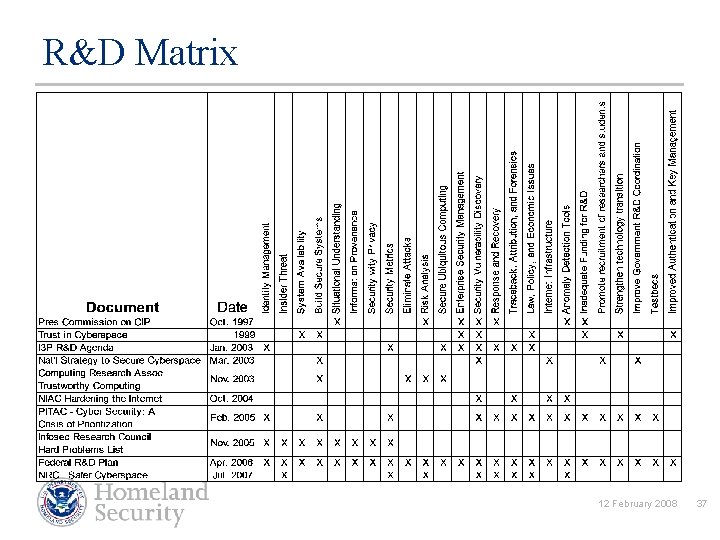
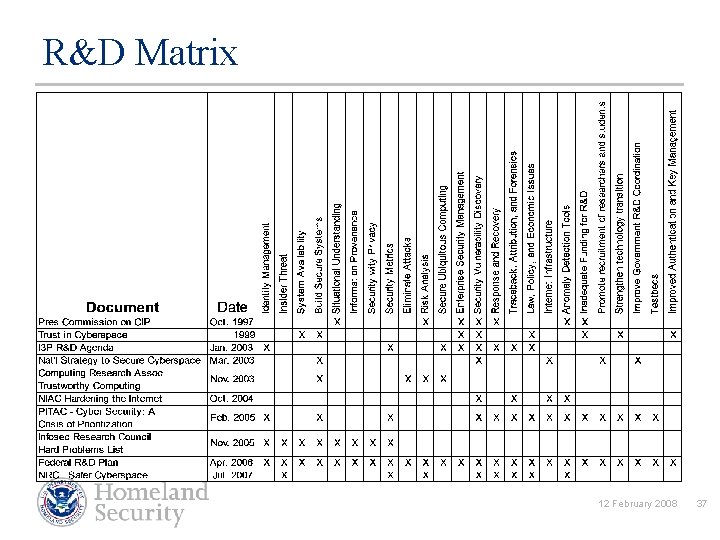
R&D Matrix 12 February 2008 37
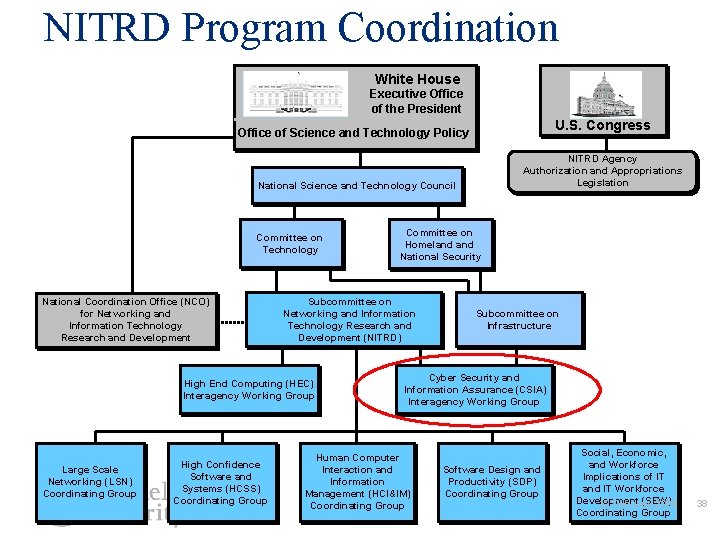
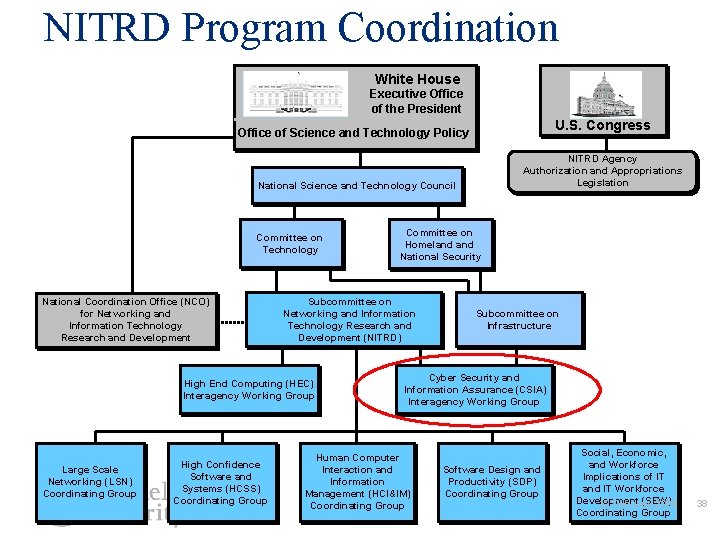
NITRD Program Coordination White House Executive Office of the President U. S. Congress Office of Science and Technology Policy NITRD Agency Authorization and Appropriations Legislation National Science and Technology Council Committee on Technology National Coordination Office (NCO) for Networking and Information Technology Research and Development Subcommittee on Networking and Information Technology Research and Development (NITRD) High End Computing (HEC) Interagency Working Group Large Scale Networking (LSN) Coordinating Group High Confidence Software and Systems (HCSS) Coordinating Group Committee on Homeland National Security Subcommittee on Infrastructure Cyber Security and Information Assurance (CSIA) Interagency Working Group Human Computer Interaction and Information Management (HCI&IM) Coordinating Group Software Design and Productivity (SDP) Coordinating Group Social, Economic, and Workforce Implications of IT and IT Workforce Development (SEW) 12 February 2008 Coordinating Group 38
Tackling Cyber Security R&D Challenges: Not Business as Usual l Key people (i. e. , Congress) now paying attention Close coordination with other Federal agencies Outreach to communities outside of the Federal government u Building public-private partnerships (the industry- government *dance* is a new tango) l l l Need a stronger emphasis on technology diffusion and technology transfer Migration paths to a more secure infrastructure Awareness of economic realities 12 February 2008 39
Douglas Maughan, Ph. D. Program Manager, CCI douglas. maughan@dhs. gov 202 -254 -6145 / 202 -360 -3170 For more information, visit http: //www. cyber. st. dhs. gov 12 February 2008 40