Depleted Uranium and attacks to Jugoslavia and Iraq






















































- Slides: 100
Depleted Uranium and attacks to Jugoslavia and Iraq Massimo Zucchetti Politecnico di Torino
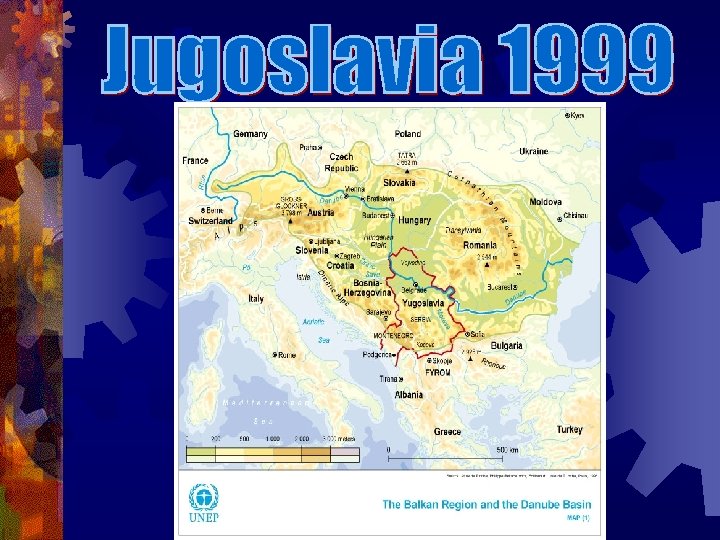
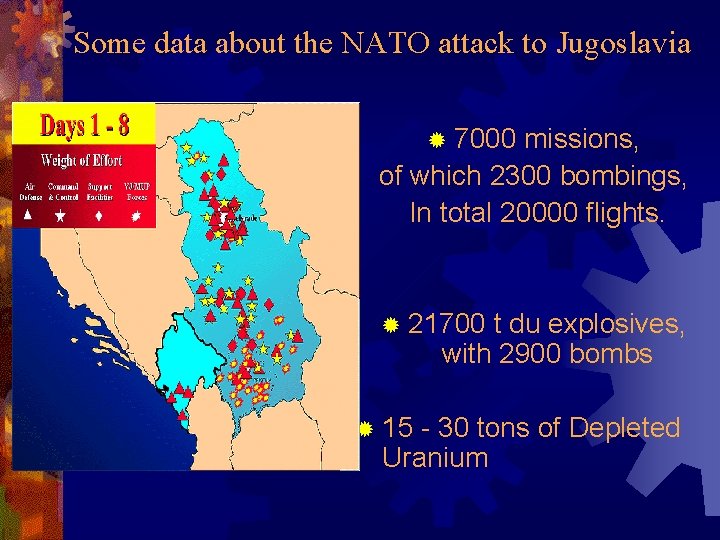
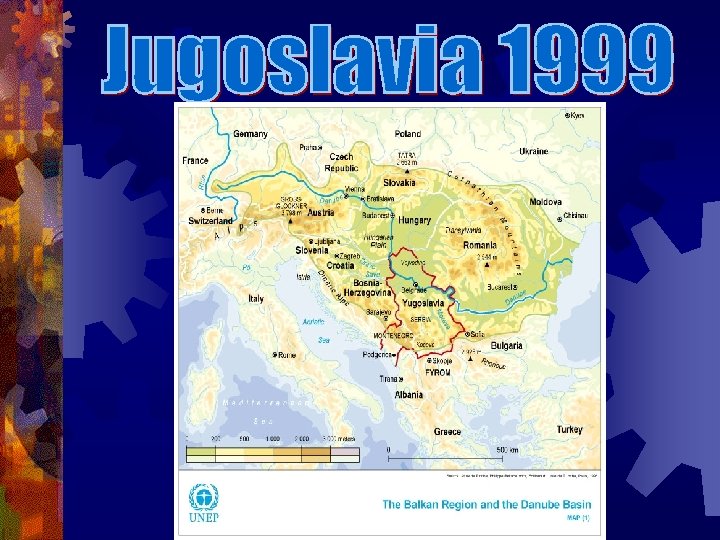
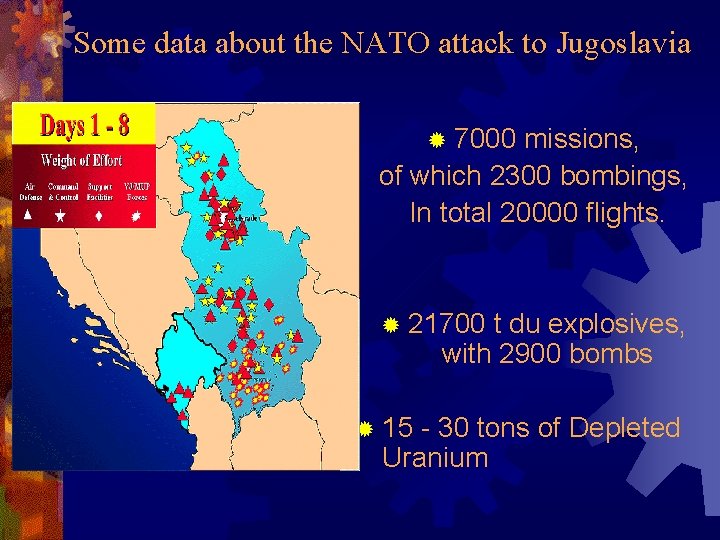
Some data about the NATO attack to Jugoslavia ® 7000 missions, of which 2300 bombings, In total 20000 flights. ® 21700 t du explosives, with 2900 bombs ® 15 - 30 tons of Depleted Uranium
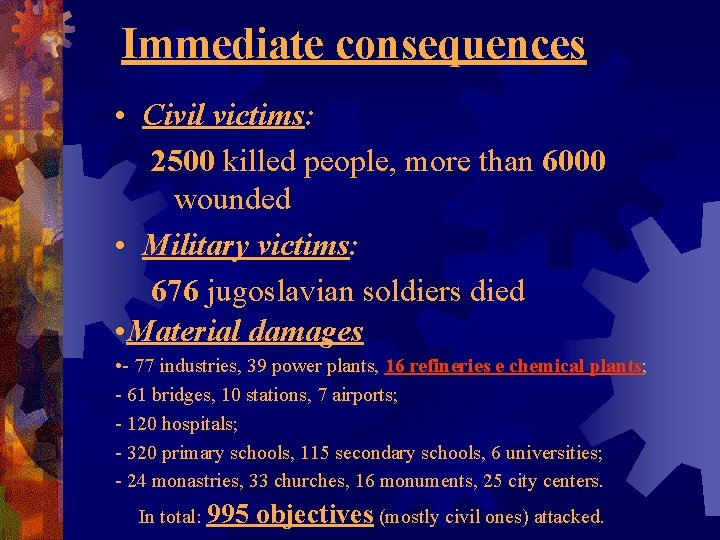
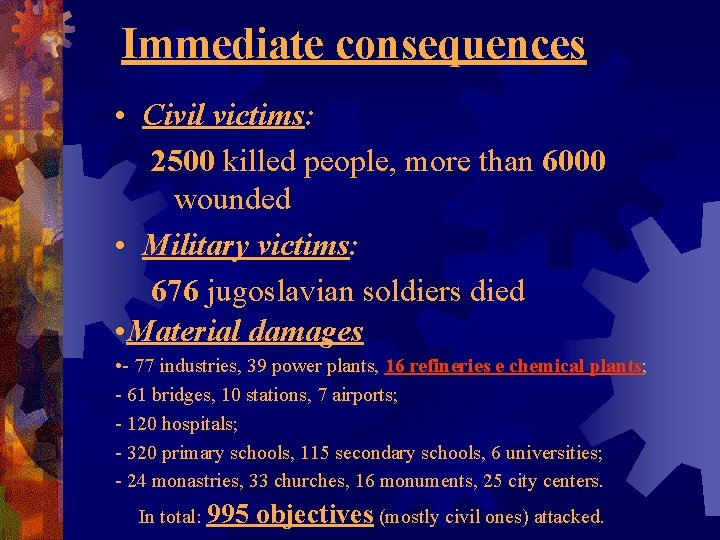
Immediate consequences • Civil victims: 2500 killed people, more than 6000 wounded • Military victims: 676 jugoslavian soldiers died • Material damages • - 77 industries, 39 power plants, 16 refineries e chemical plants; - 61 bridges, 10 stations, 7 airports; - 120 hospitals; - 320 primary schools, 115 secondary schools, 6 universities; - 24 monastries, 33 churches, 16 monuments, 25 city centers. In total: 995 objectives (mostly civil ones) attacked.

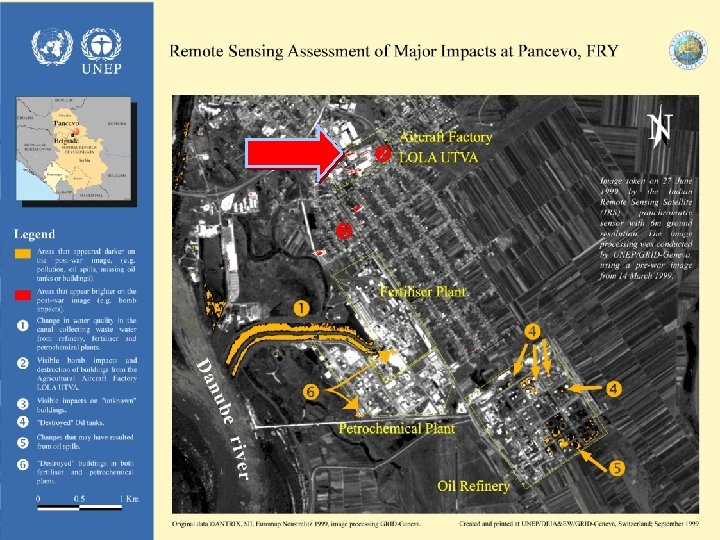
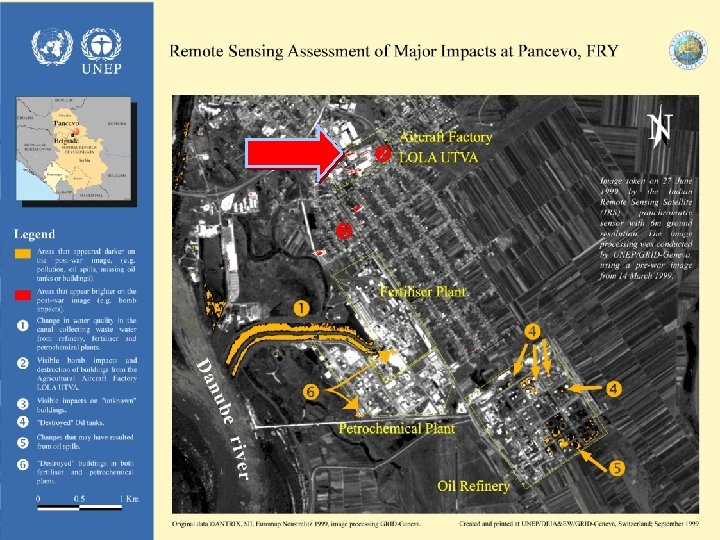
PANCEVO Petrochemical, Refinery, Fertilizers
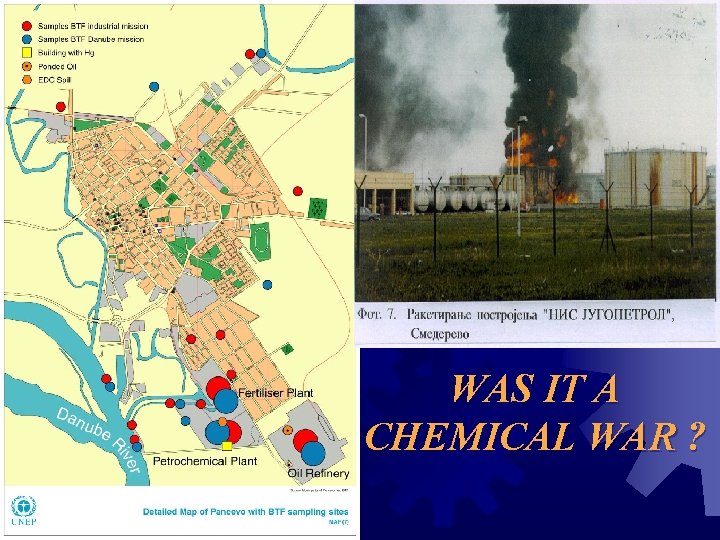
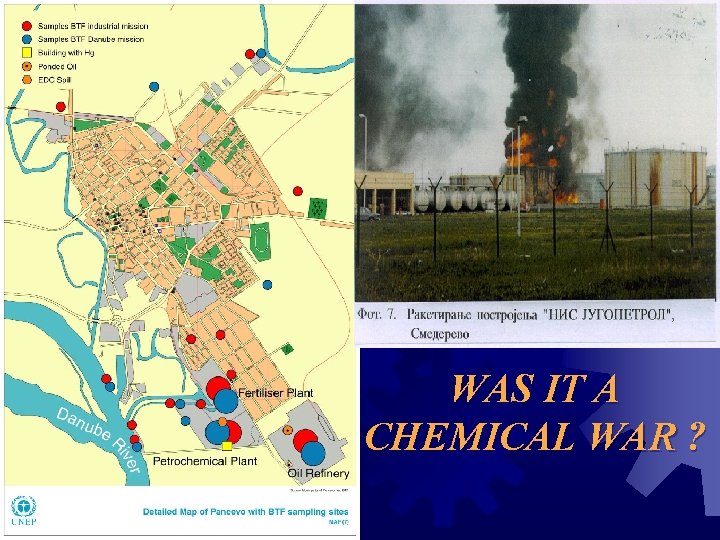
WAS IT A CHEMICAL WAR ?
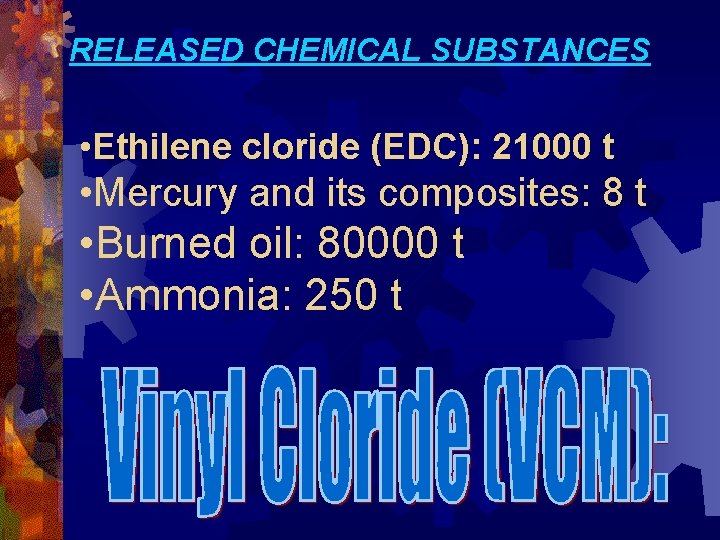
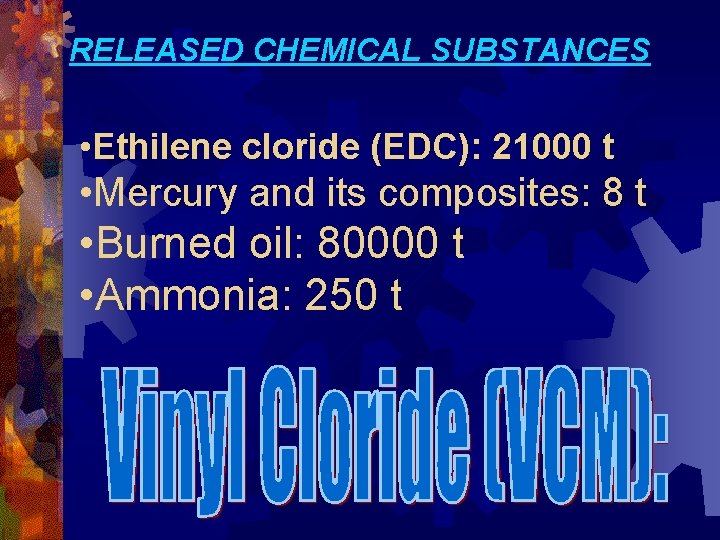
RELEASED CHEMICAL SUBSTANCES • Ethilene cloride (EDC): 21000 t • Mercury and its composites: 8 t • Burned oil: 80000 t • Ammonia: 250 t
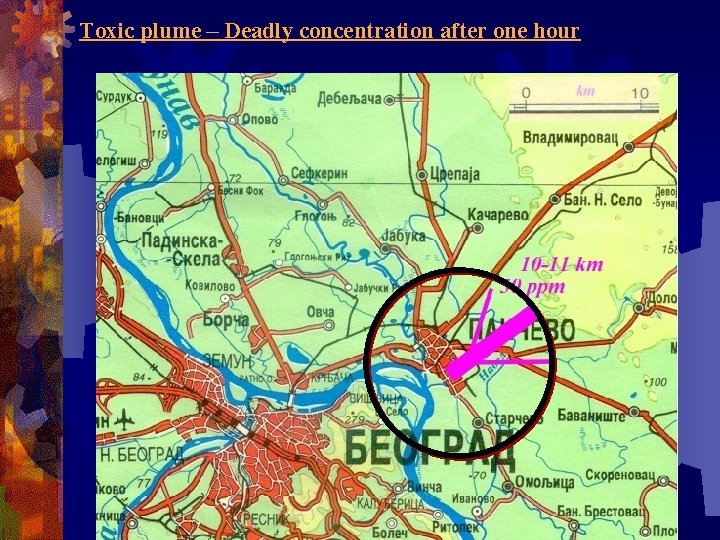
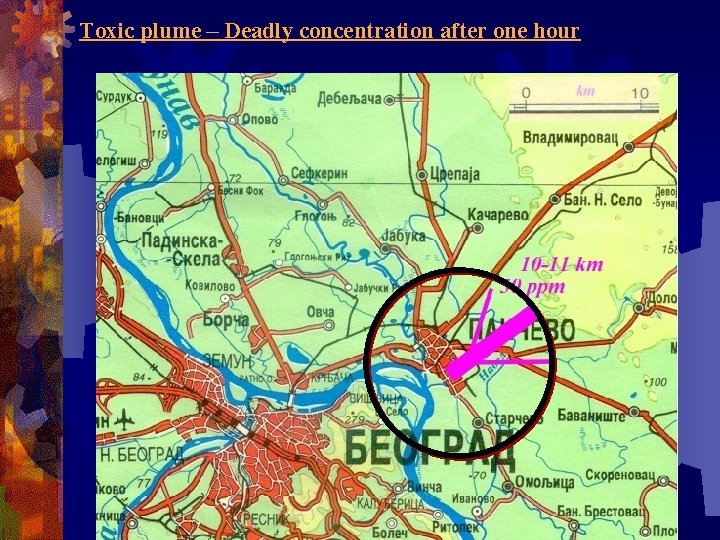
Toxic plume – Deadly concentration after one hour
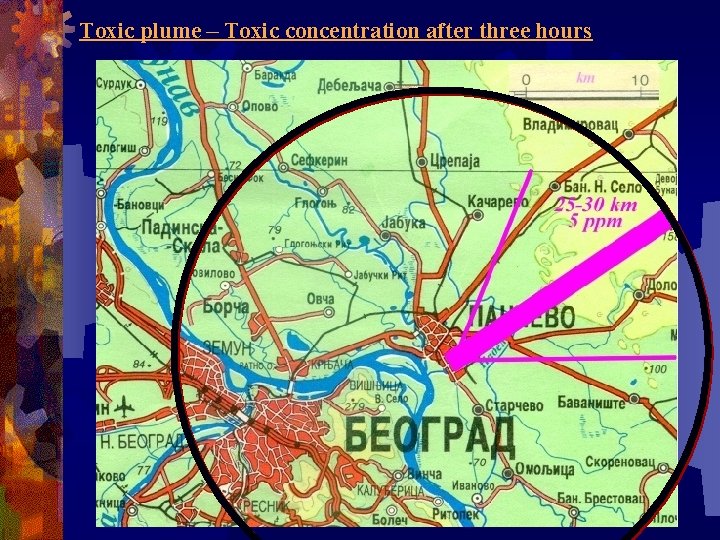
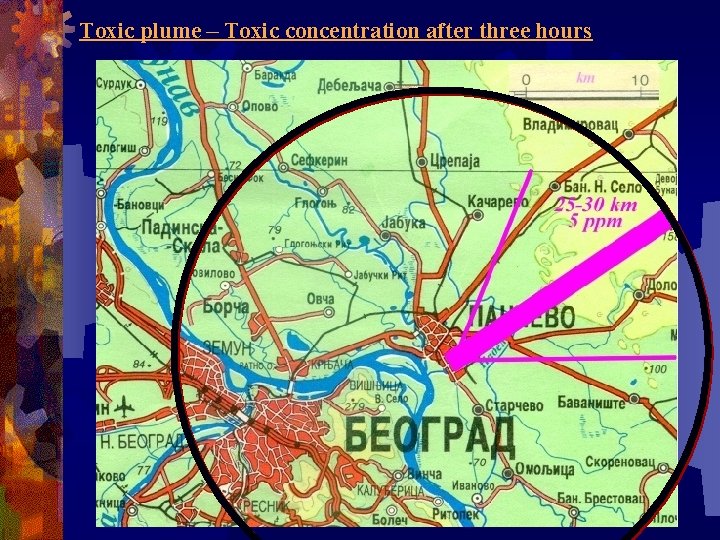
Toxic plume – Toxic concentration after three hours







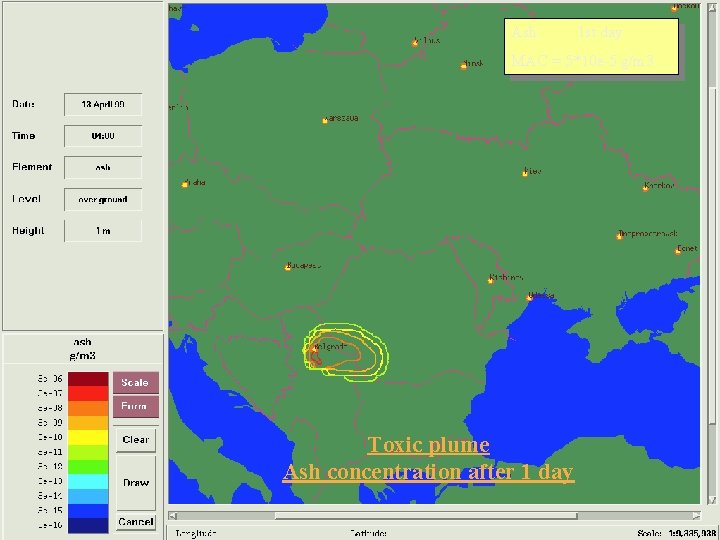
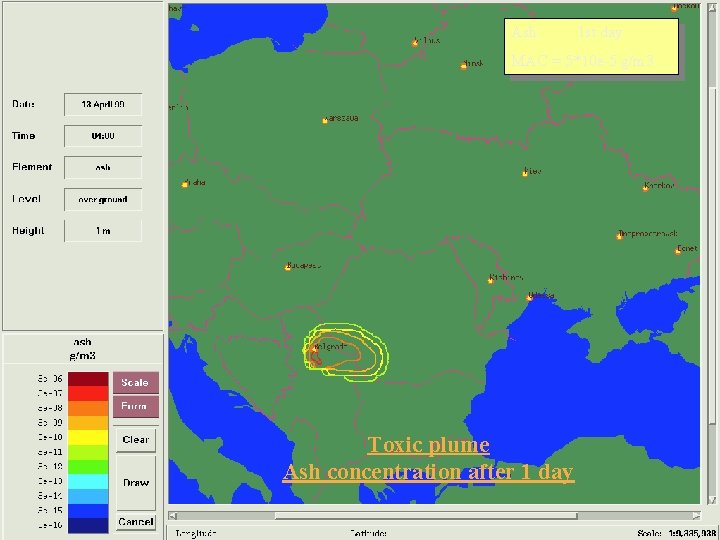
Ash: 1 st day MAC = 5*10 e-5 g/m 3 Toxic plume Ash concentration after 1 day
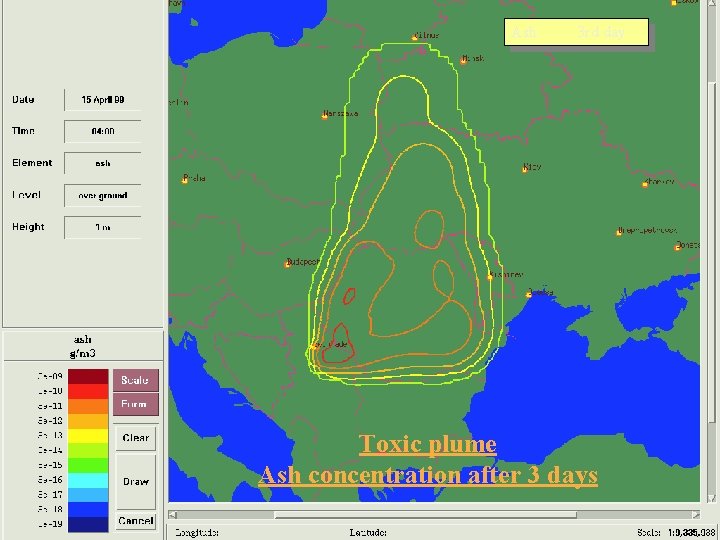
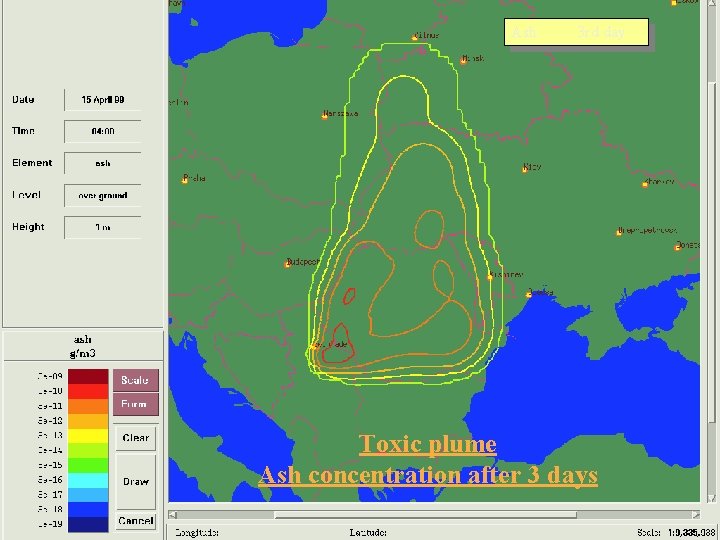
Ash: 3 rd day Toxic plume Ash concentration after 3 days
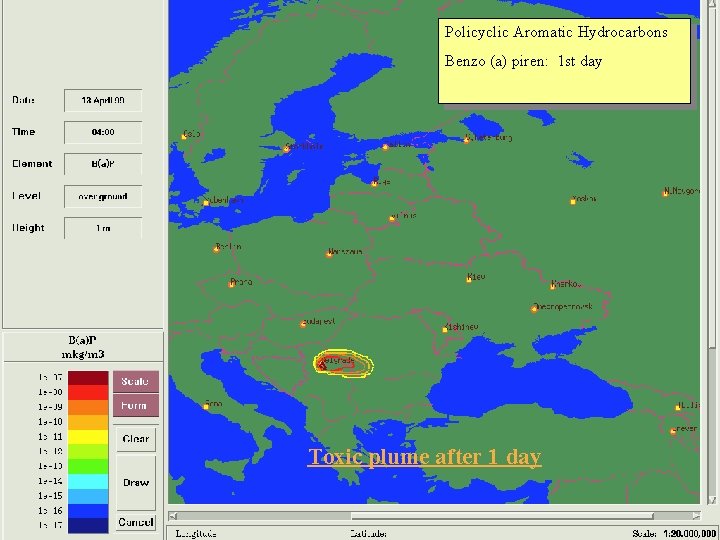
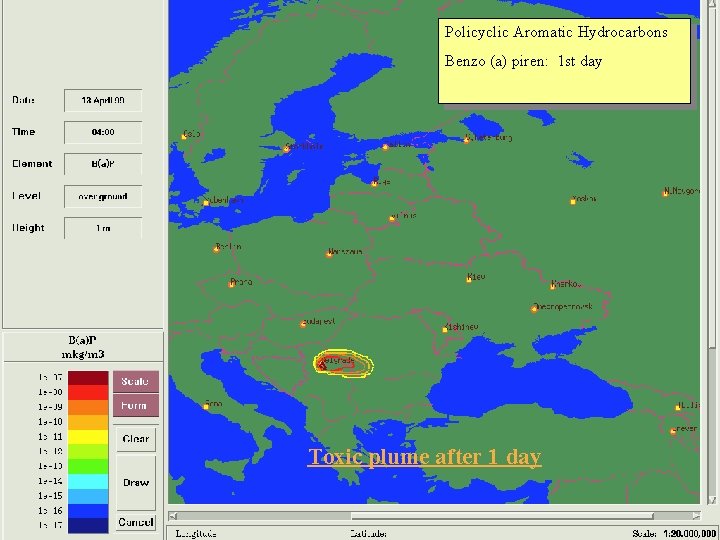
Policyclic Aromatic Hydrocarbons Benzo (a) piren: 1 st day Toxic plume after 1 day
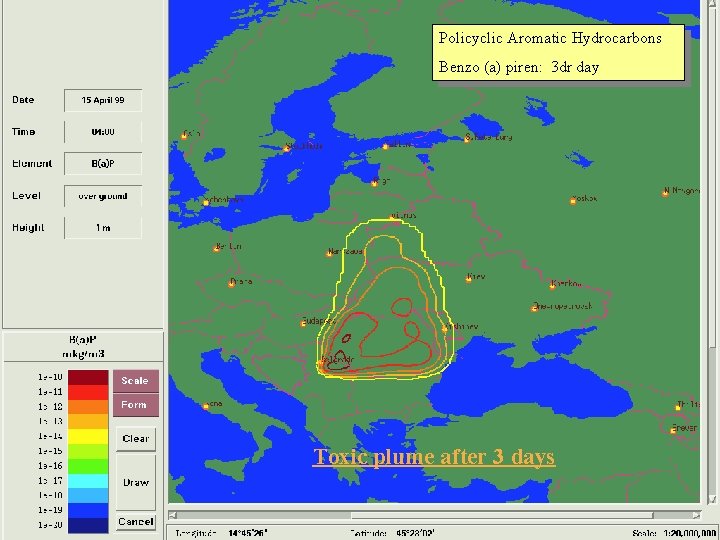
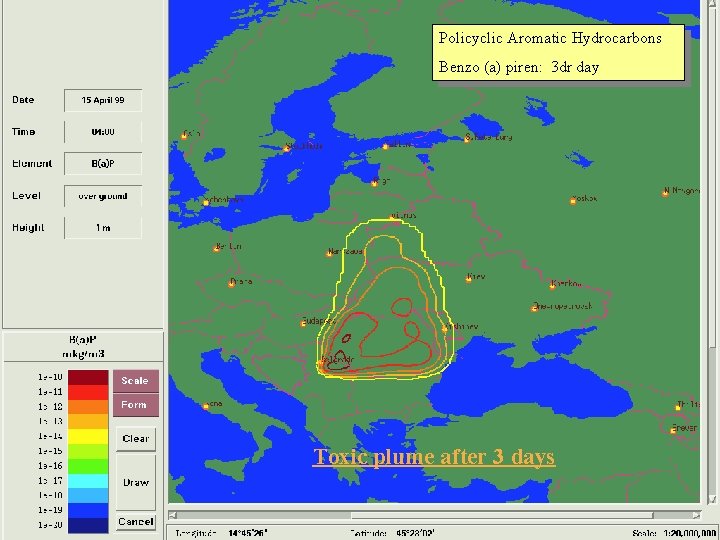
Policyclic Aromatic Hydrocarbons Benzo (a) piren: 3 dr day Toxic plume after 3 days
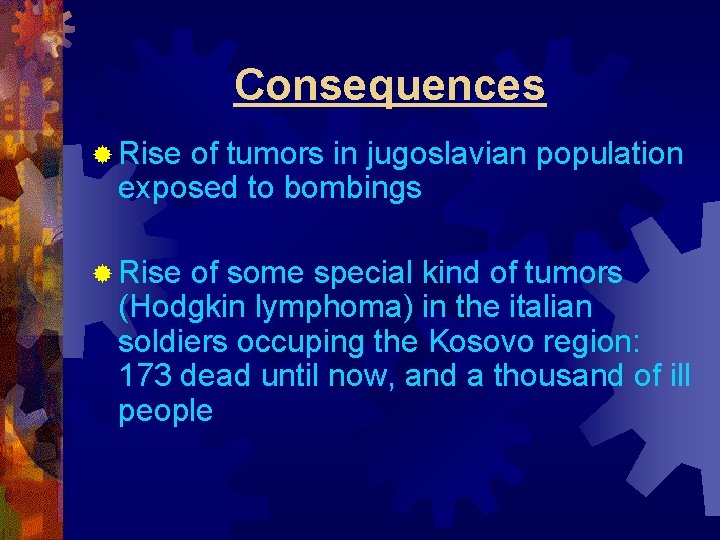
Consequences ® Rise of tumors in jugoslavian population exposed to bombings ® Rise of some special kind of tumors (Hodgkin lymphoma) in the italian soldiers occuping the Kosovo region: 173 dead until now, and a thousand of ill people
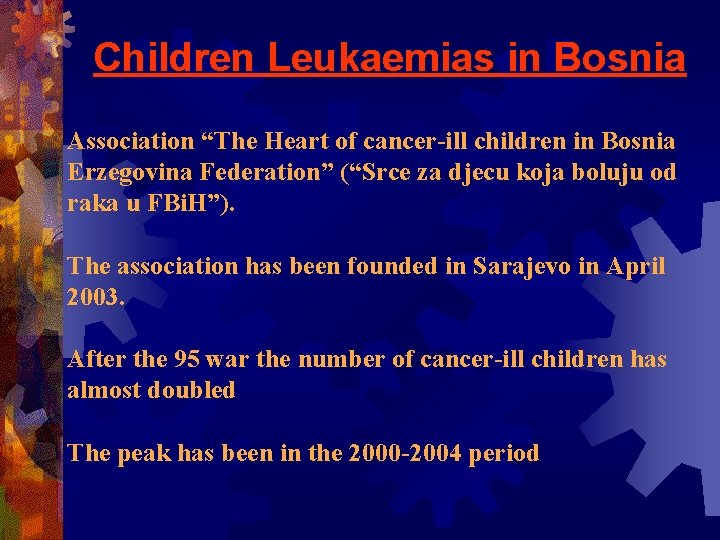
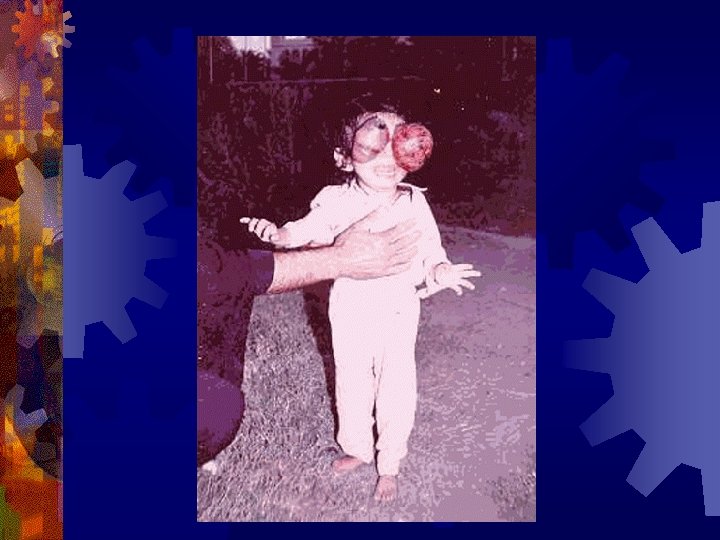
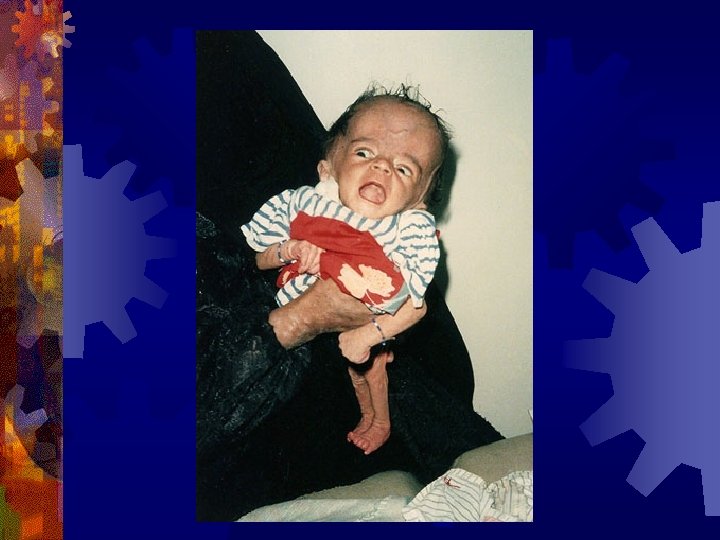
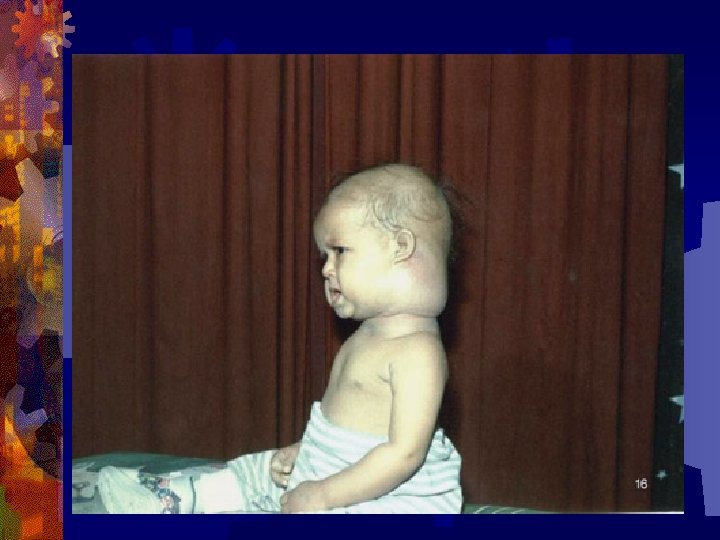
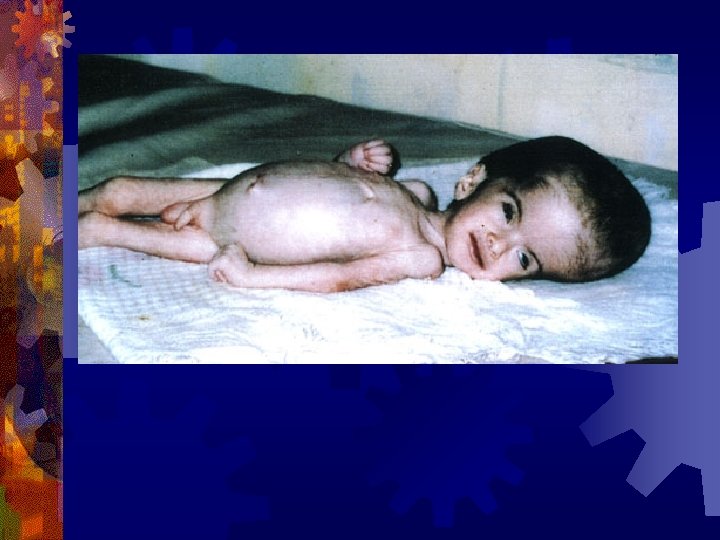
Children Leukaemias in Bosnia Association “The Heart of cancer-ill children in Bosnia Erzegovina Federation” (“Srce za djecu koja boluju od raka u FBi. H”). The association has been founded in Sarajevo in April 2003. After the 95 war the number of cancer-ill children has almost doubled The peak has been in the 2000 -2004 period
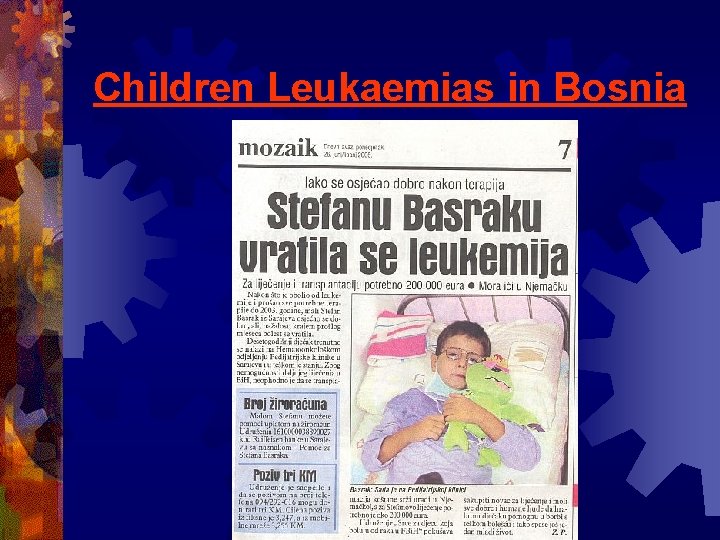
Children Leukaemias in Bosnia
Children Leukaemias in Bosnia
Children Leukaemias in Bosnia
Children Leukaemias in Bosnia
Depleted Uranium ® Depleted Uranium is a nuclear material known since the forties ® It has been used in the Gulf War (1991), in the Balkans (Bosnia 1995 e Kosovo 1999), in Afghanistan e again in Iraq in 2003. ® DU is mainly composed by U-238, it is a radioactive material with extremely long halflife, and it is an emitter.
DU HAZARDS ® DU is known to be dangerous since the fifties, when ihalation of DU dust caused illness in workers of the nuclear industry, and in particular of fuel fabrication plants ® Pathologies caused by DU are essentially tumors; in particular, to lymph-nodes (Hodgkin and Non-hodgkin lymphomas), leukaemia, lung tumors
USE OF DU ® Du has been used for military purposes, in order to increase the weight of bullets and in armours. ® The greatest attack has been that to Iraq, both in 1991 and in 2003.
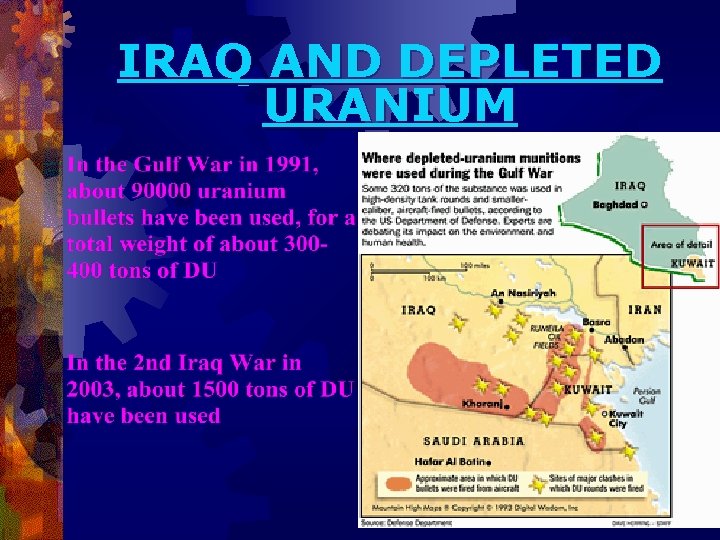
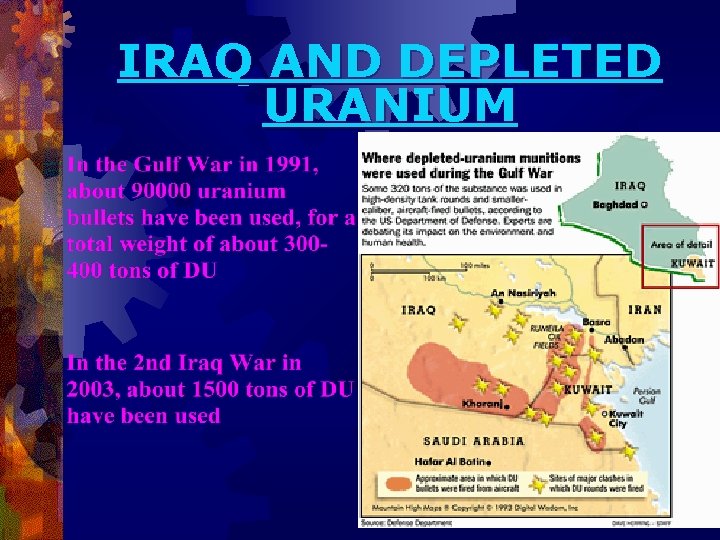
IRAQ AND DEPLETED URANIUM
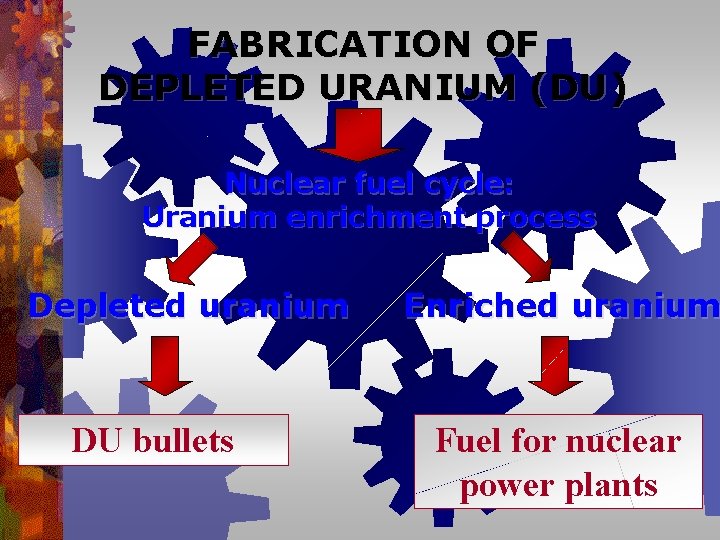
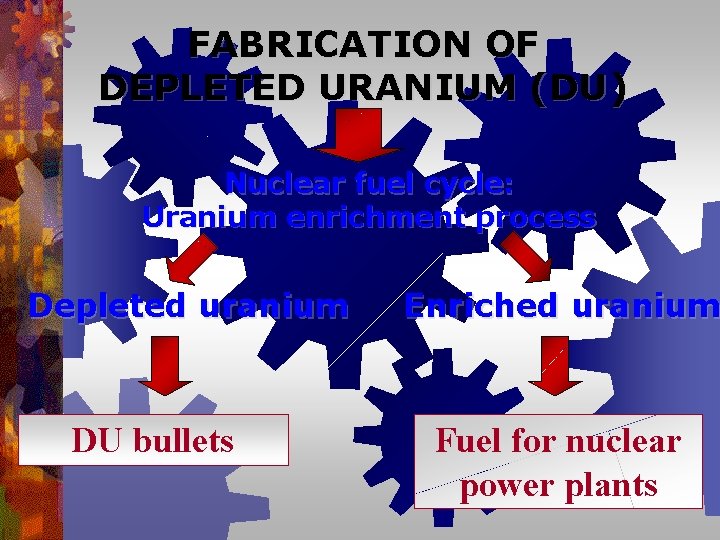
FABRICATION OF DEPLETED URANIUM (DU) Nuclear fuel cycle: Uranium enrichment process Depleted uranium DU bullets Enriched uranium Fuel for nuclear power plants
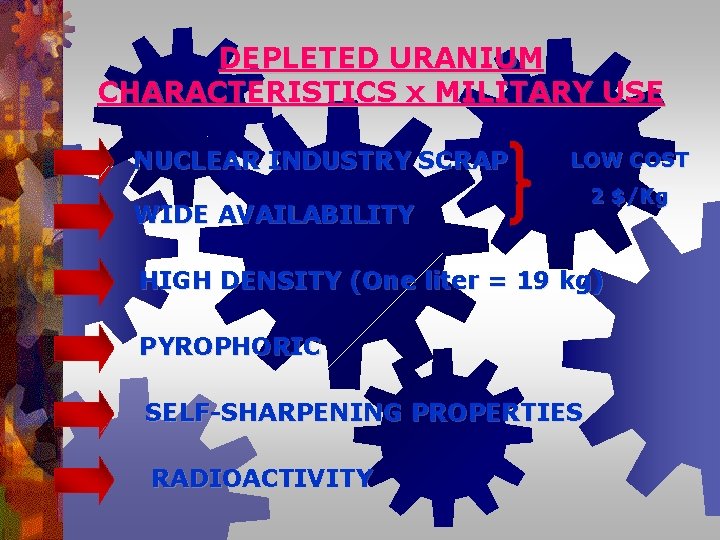
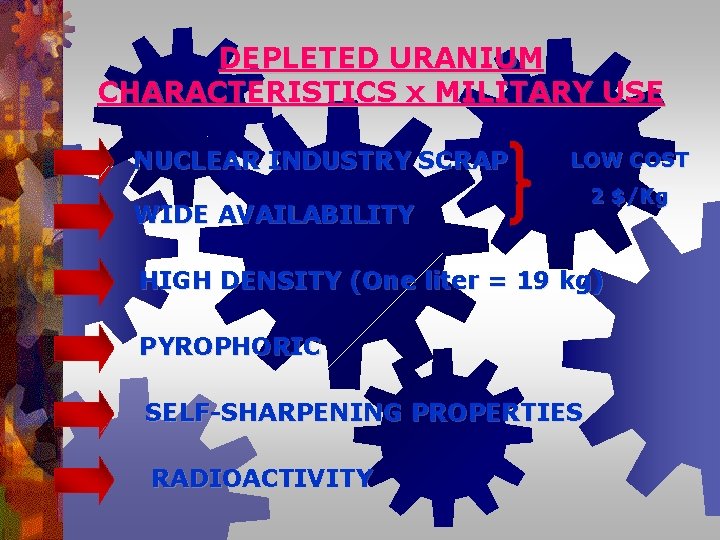
DEPLETED URANIUM CHARACTERISTICS x MILITARY USE NUCLEAR INDUSTRY SCRAP LOW COST WIDE AVAILABILITY 2 $/Kg HIGH DENSITY (One liter = 19 kg) PYROPHORIC SELF-SHARPENING PROPERTIES RADIOACTIVITY
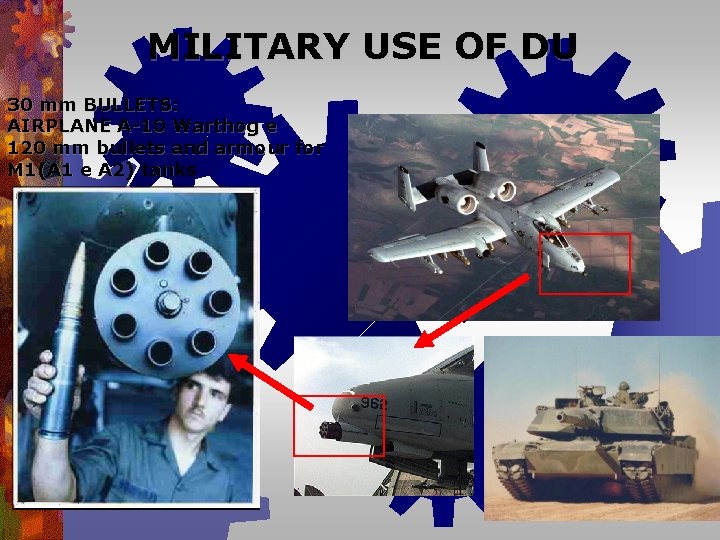
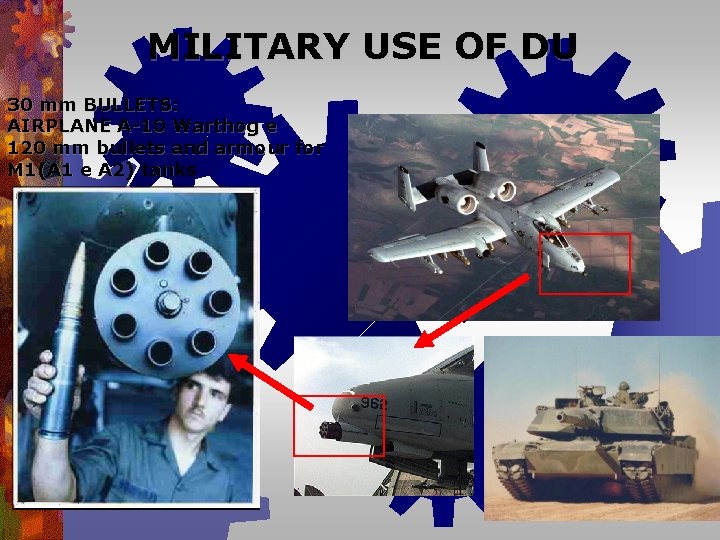
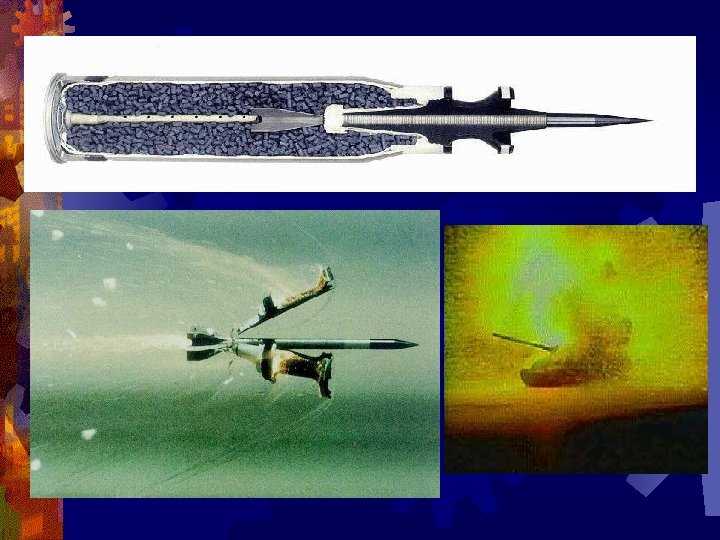
MILITARY USE OF DU 30 mm BULLETS: AIRPLANE A-10 Warthog e 120 mm bullets and armour for M 1(A 1 e A 2) tanks

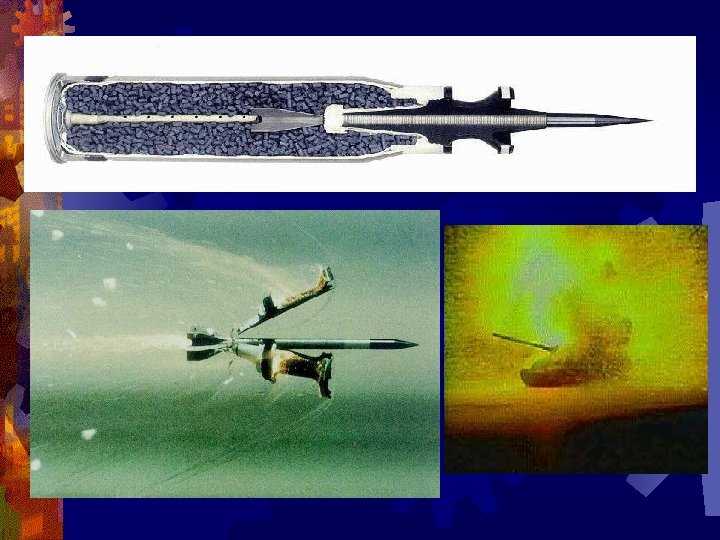
WHAT HAPPENS WHEN A DU BULLET IMPACTS ON TARGET? TARGET DISTRUCTION FIRE: OXIDATION AND PULVERIZATION ATMOSPHERICAL DISPERSION DEPOSIT TO SOIL: EVEN AT LONG DISTANCE RADIOACTIVE CONTAMINATION
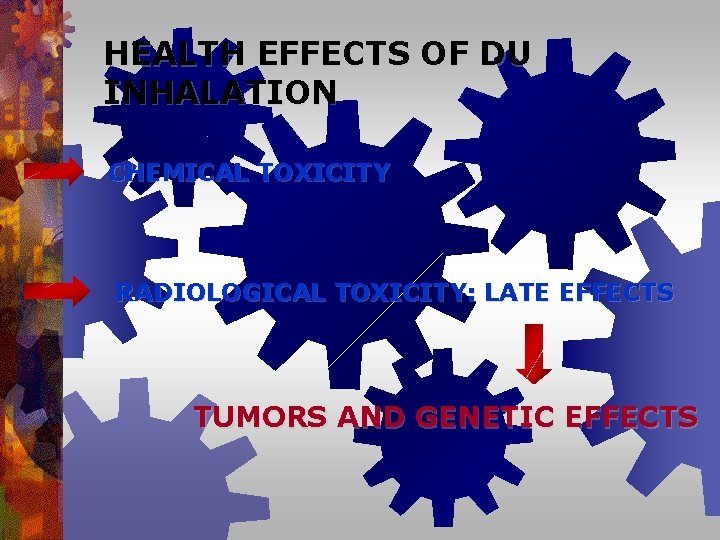
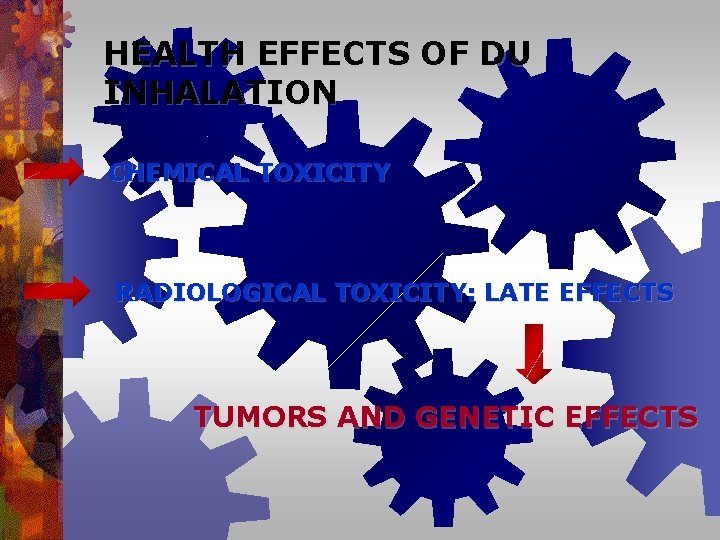
HEALTH EFFECTS OF DU INHALATION CHEMICAL TOXICITY RADIOLOGICAL TOXICITY: LATE EFFECTS TUMORS AND GENETIC EFFECTS
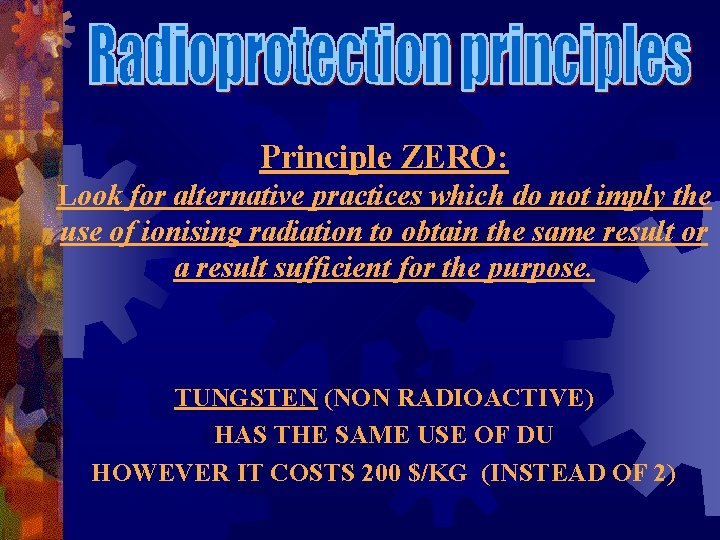
Principle ZERO: Look for alternative practices which do not imply the use of ionising radiation to obtain the same result or a result sufficient for the purpose. TUNGSTEN (NON RADIOACTIVE) HAS THE SAME USE OF DU HOWEVER IT COSTS 200 $/KG (INSTEAD OF 2)
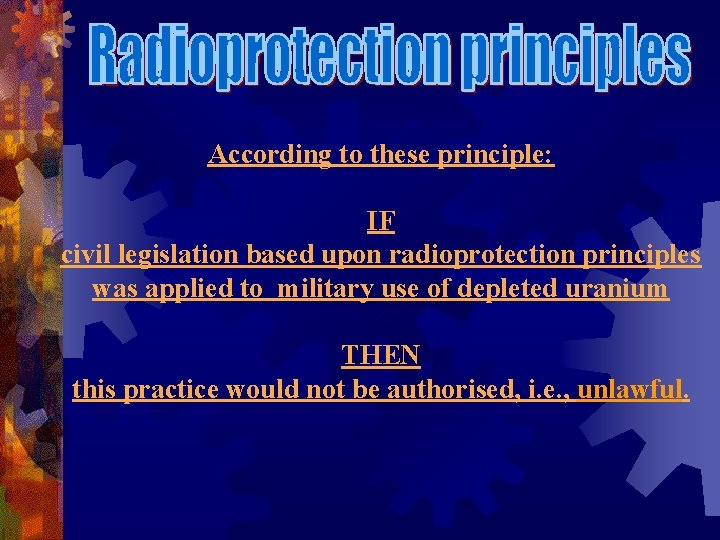
According to these principle: IF civil legislation based upon radioprotection principles was applied to military use of depleted uranium THEN this practice would not be authorised, i. e. , unlawful.
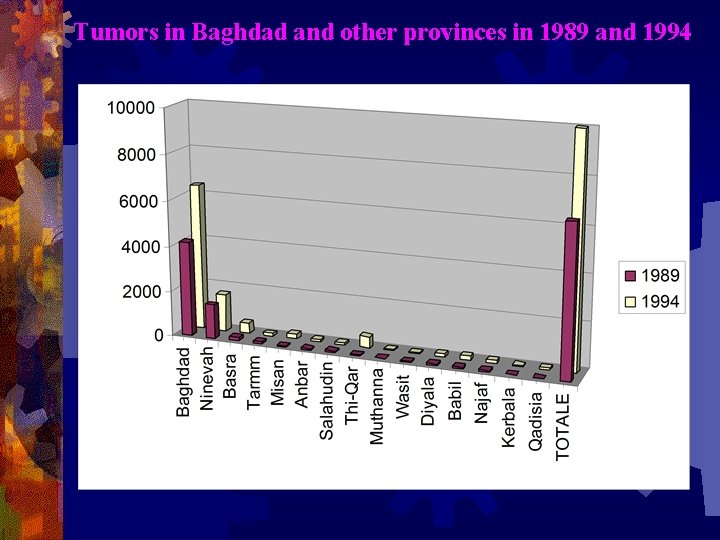
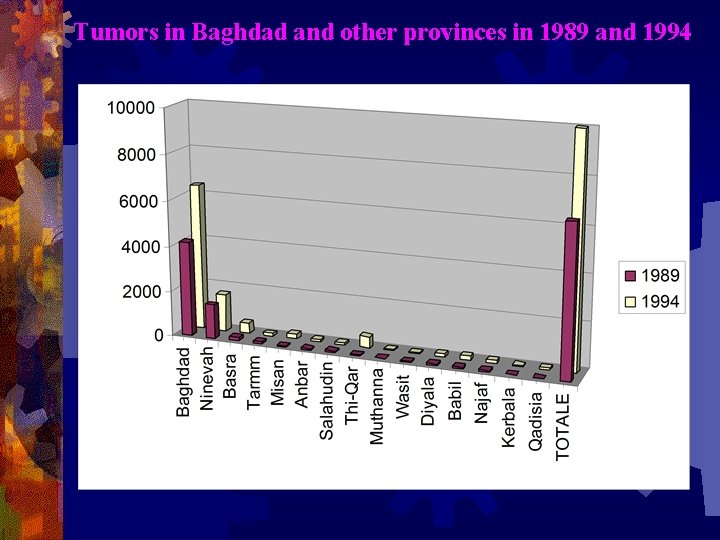
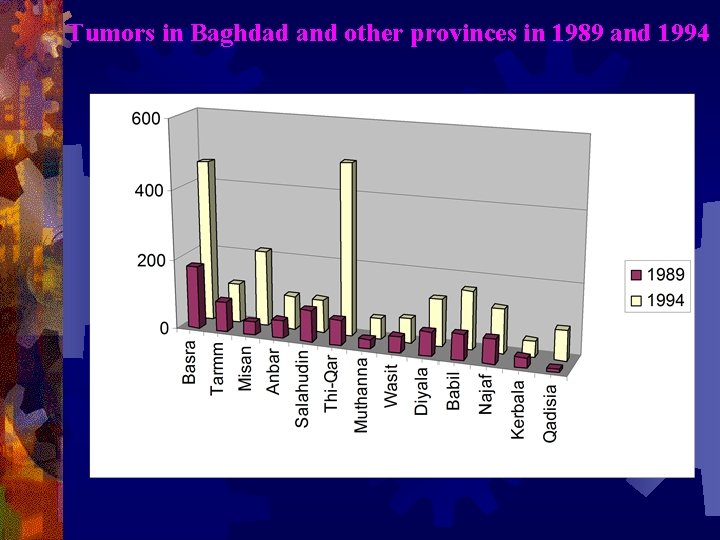
Tumors in Baghdad and other provinces in 1989 and 1994
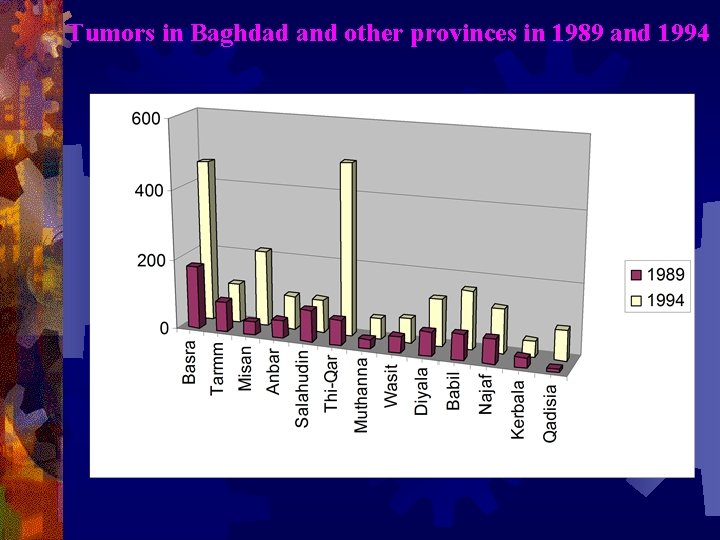
Tumors in Baghdad and other provinces in 1989 and 1994
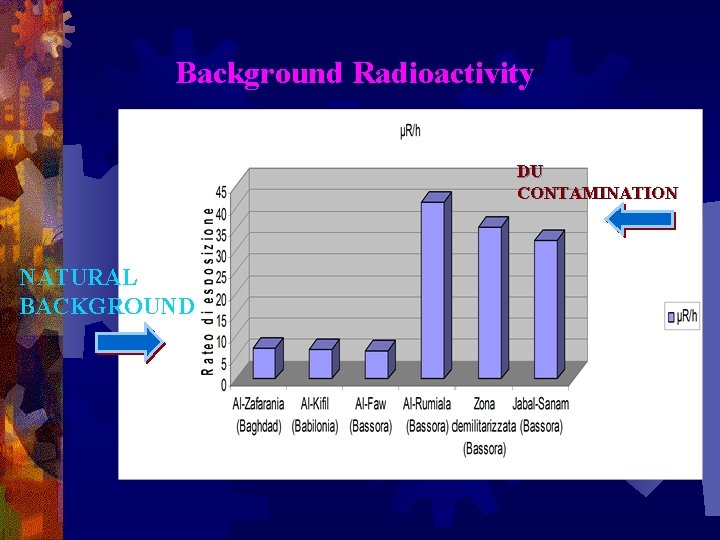
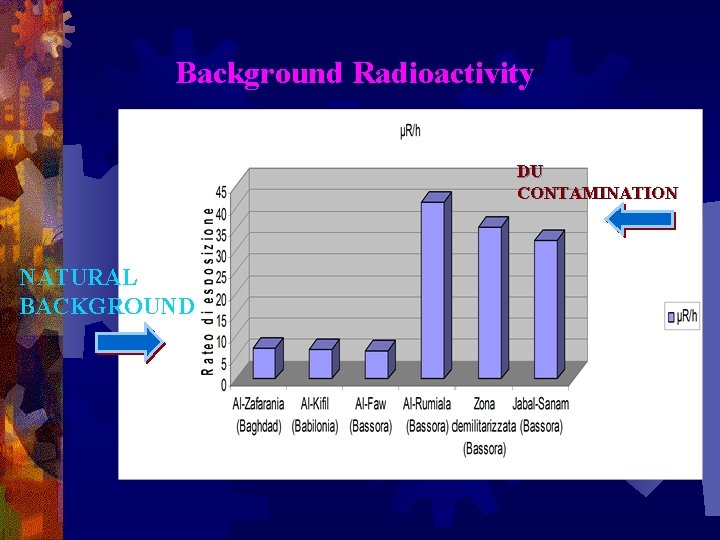
Background Radioactivity DU CONTAMINATION NATURAL BACKGROUND
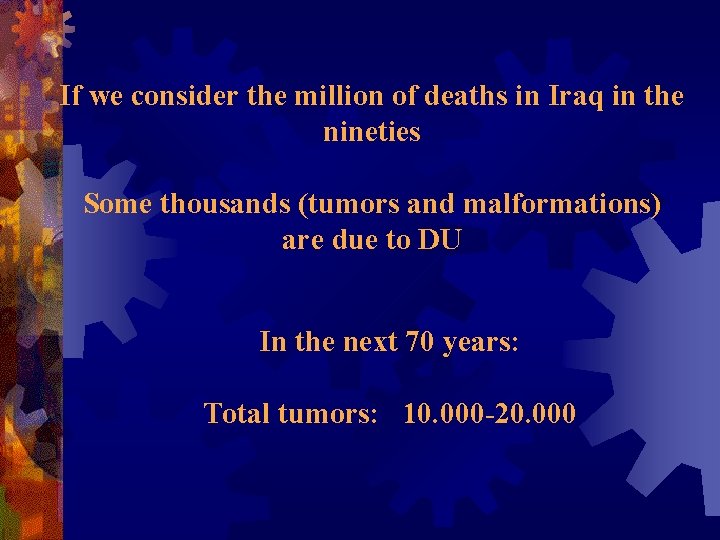
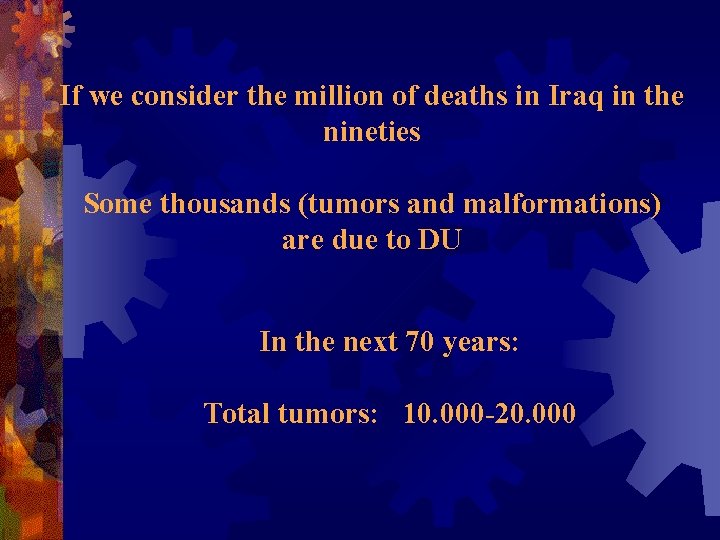
If we consider the million of deaths in Iraq in the nineties Some thousands (tumors and malformations) are due to DU In the next 70 years: Total tumors: 10. 000 -20. 000
® What happened to epidemiological data after the destructions of the 2003 war? ® During the 2003 war, Iraqi cities have suffered wide destructions, and so hospitals, research institutions, etc. . ® Invaders wanted everything to be destroyed and forgotten….
Epidemiologists worked heroically to maintain this database through the darkest days of 2003. Dr Ahmed, an epidemiologist working with the cancer board, remembers, “We moved into the hospital in the first days after the war, when no-one else was working, and managed to save all our data. Everything was kept safe…and not destroyed by fire and looting. ”
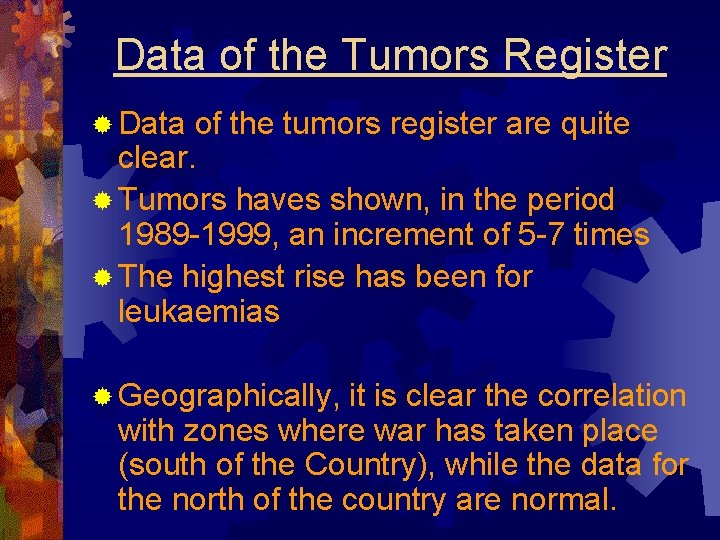
Data of the Tumors Register ® Data of the tumors register are quite clear. ® Tumors haves shown, in the period 1989 -1999, an increment of 5 -7 times ® The highest rise has been for leukaemias ® Geographically, it is clear the correlation with zones where war has taken place (south of the Country), while the data for the north of the country are normal.
Tumor forecasts ® On the base of these data, the forecasts of tumor cases in Iraq in the next years are tremendous ® Iraq is full of chemical and radioactive pollutants ® DU is just one of the causes of this phenomenon
CONCLUSION ® It is important to gather data and researches in the field of DU and of the effects of the US “new wars” on man and environment ® It is necessary to show that modern new weapons, instead of being “surgical”, produce unacceptable damages. ® Effects of the US and NATO “new wars” on man and environment must be shown without reticence

THANKS FOR ATTENTION! ® massimo. zucchetti@polito. it ® http: //staff. polito. it/massimo. zucchetti/

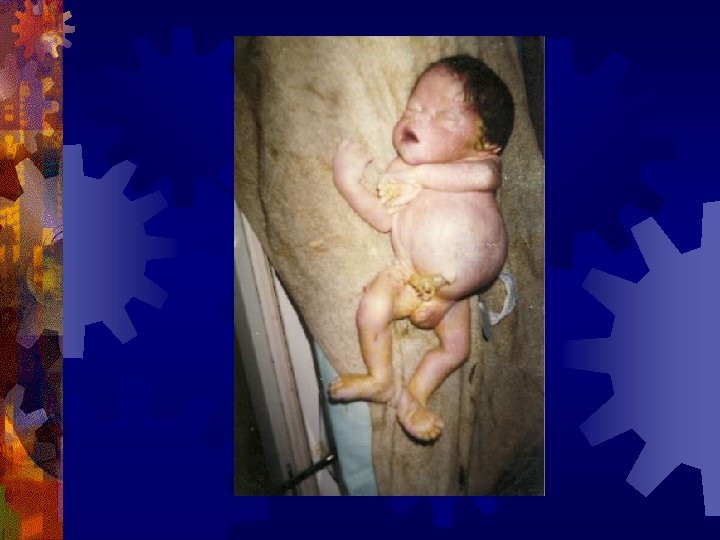
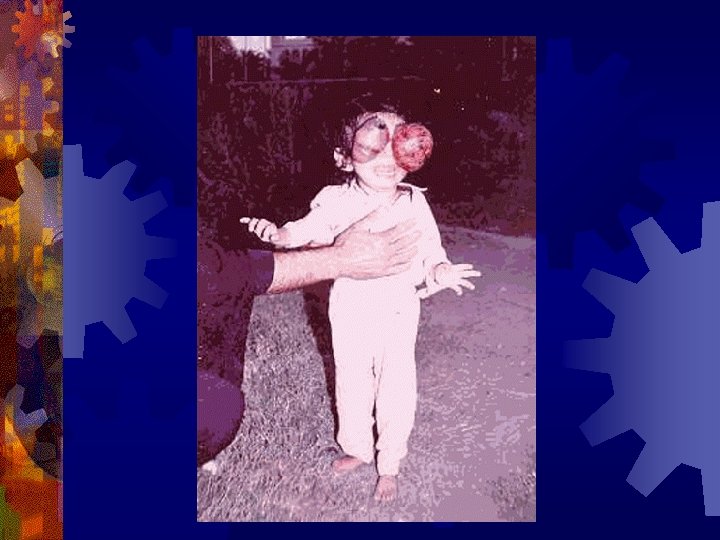
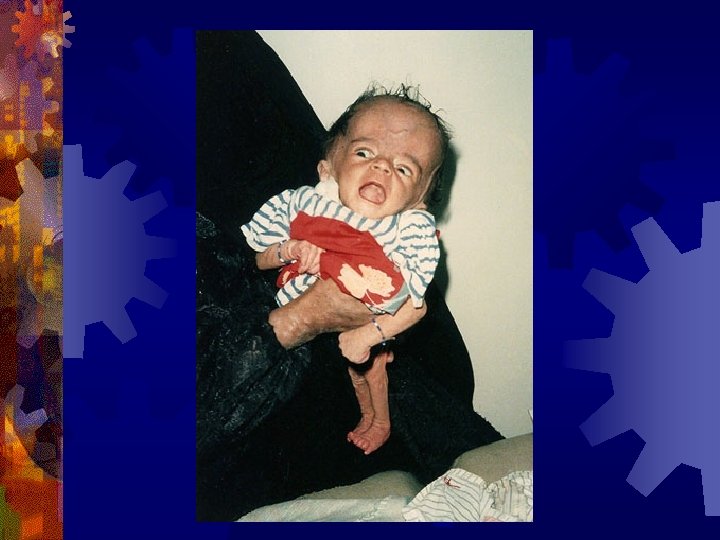
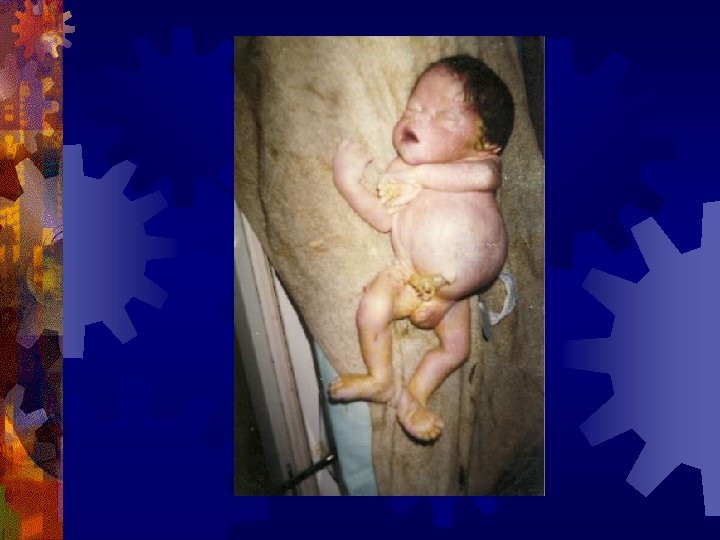
MALFORMATIONS IN CHILDREN OF IRAQ, AFGHANISTAN AND US ARMY VETERANS











































Thanks for your attention, Massimo