Deep Packet Inspection as a Service Anat BremlerBarr
Deep Packet Inspection as a Service Anat Bremler-Barr IDC Herzliya Joint work with Yotam Harchol, David Hay and Yaron Koral The Hebrew University Appeared at Co. NEXT 2014 www. deepness-lab. org This work was supported by European Research Council (ERC) Starting Grant no. 259085 and “Neptune” consortium
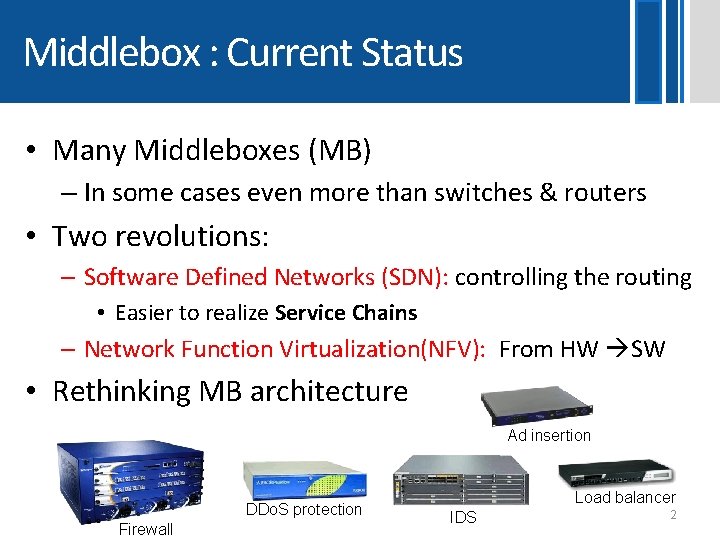
Middlebox : Current Status • Many Middleboxes (MB) – In some cases even more than switches & routers • Two revolutions: – Software Defined Networks (SDN): controlling the routing • Easier to realize Service Chains – Network Function Virtualization(NFV): From HW SW • Rethinking MB architecture Ad insertion DDo. S protection Firewall Load balancer IDS 2
NFV: Hardware MB Software MB • Hardware Middlebox – – – Not Flexible Expensive Hard to manage (many vendors) Not multi-tenants Difficult to add new features Constraining innovation: higher entry barrier • Software Middlebox – Performance penalty • Commodity Servers • VMs • No hardware accelerators We suggest a new MB architecture that improves performance and innovation using NFV and SDN 3
Our approach: MB common modules as a service • Break MB architecture to common modules - E. g. many MBs use Deep Packet Inspection (DPI) • Provide modules as a service - A single module provides a service to many different kinds of MBs - In service chain scenario: packets use the service only once and not repeatedly in each MB • DPI as an example
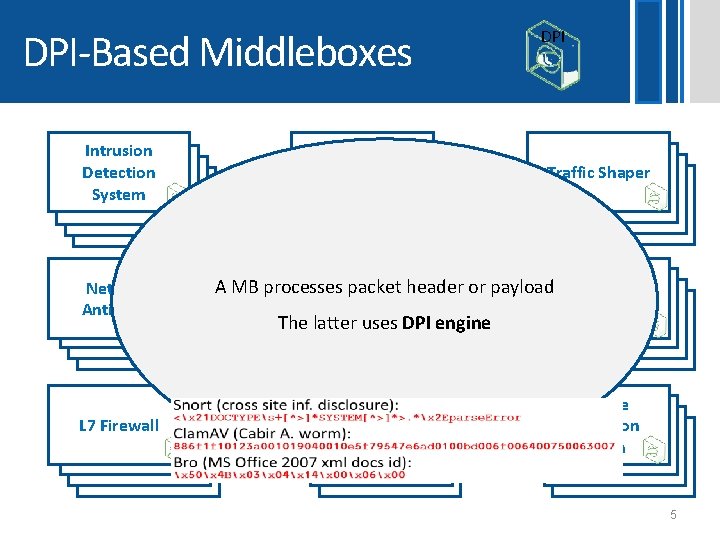
DPI-Based Middleboxes Intrusion Detection System Network Anti-Virus L 7 Firewall Network Analytic DPI Traffic Shaper A MB processes packet header or payload Lawful Copyright Enforcement Interception L 7 Load Balancer Leakage Prevention System The latter uses DPI engine 5
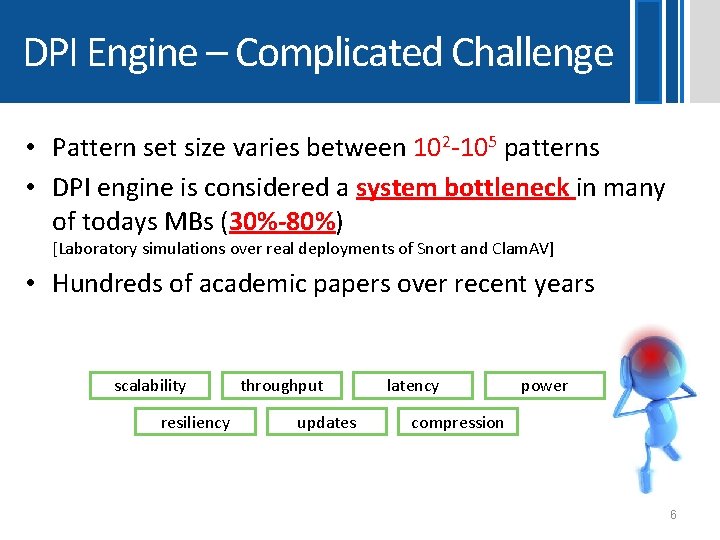
DPI Engine – Complicated Challenge • Pattern set size varies between 102 -105 patterns • DPI engine is considered a system bottleneck in many of todays MBs (30%-80%) [Laboratory simulations over real deployments of Snort and Clam. AV] • Hundreds of academic papers over recent years scalability resiliency throughput updates latency power compression 6
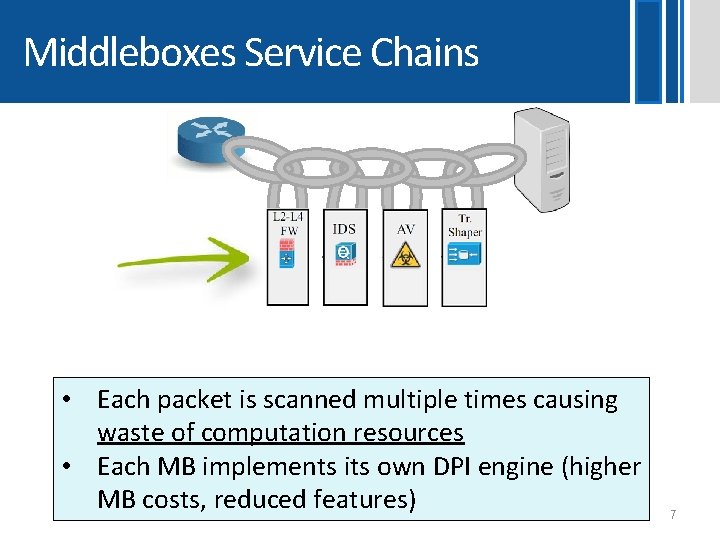
Middleboxes Service Chains • Each packet is scanned multiple times causing waste of computation resources • Each MB implements its own DPI engine (higher MB costs, reduced features) 7
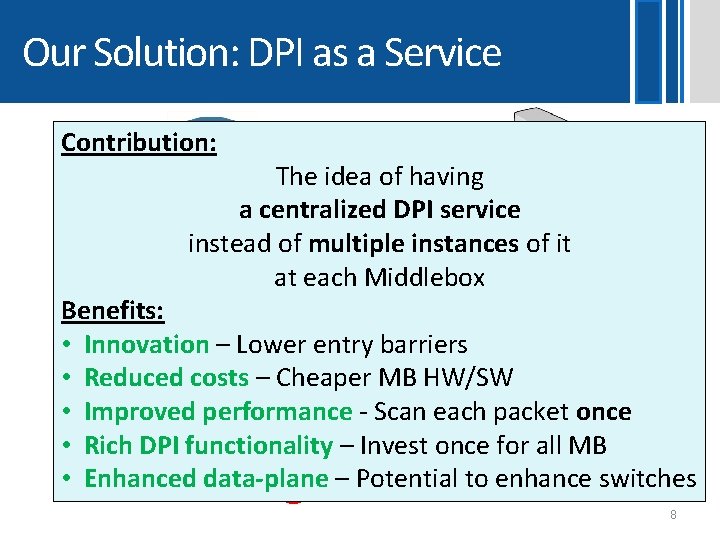
Our Solution: DPI as a Service Contribution: The idea of having a centralized DPI service instead of multiple instances of it at each Middlebox Benefits: • Innovation – Lower entry barriers • Reduced costs – Cheaper MB HW/SW • Improved performance - Scan each packet once • Rich DPI functionality – Invest once for all MB • Enhanced data-plane – Potential to enhance switches 8
Agenda • Architecture aspects of DPI as a service – DPI controller – Passing results from the DPI to the MBs • Scalable algorithm that combines DPI patterns from different MBs • Experimental Results • Vision & Future Work
ARCHITECTURE 10
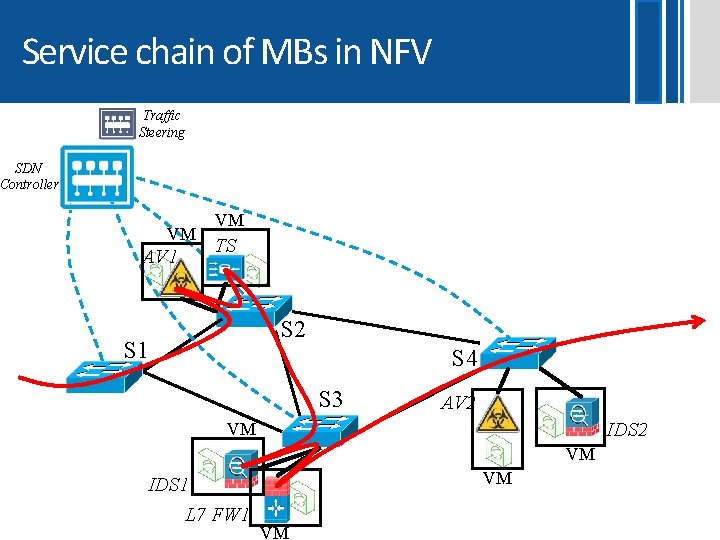
Service chain of MBs in NFV Traffic Steering SDN Controller VM AV 1 VM TS S 2 S 1 S 4 S 3 AV 2 IDS 2 VM VM VM IDS 1 L 7 FW 1 VM
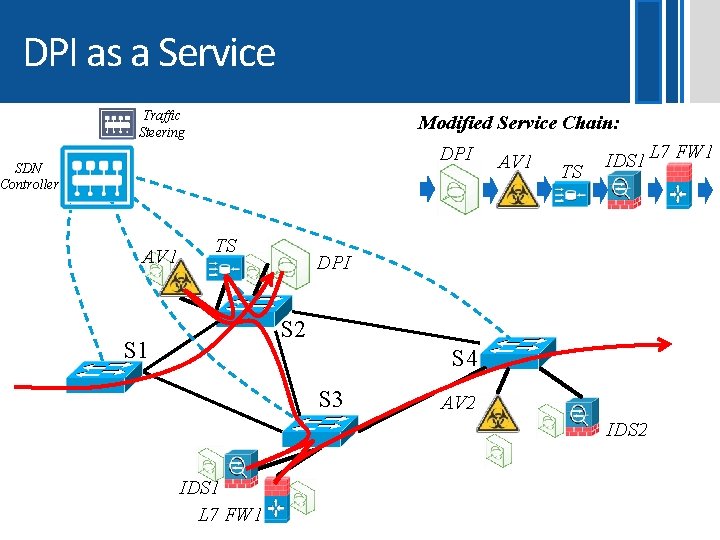
DPI as a Service Traffic Steering Modified Service Chain: DPI SDN Controller AV 1 TS IDS 1 L 7 FW 1 DPI S 2 S 1 S 4 S 3 AV 2 IDS 1 L 7 FW 1
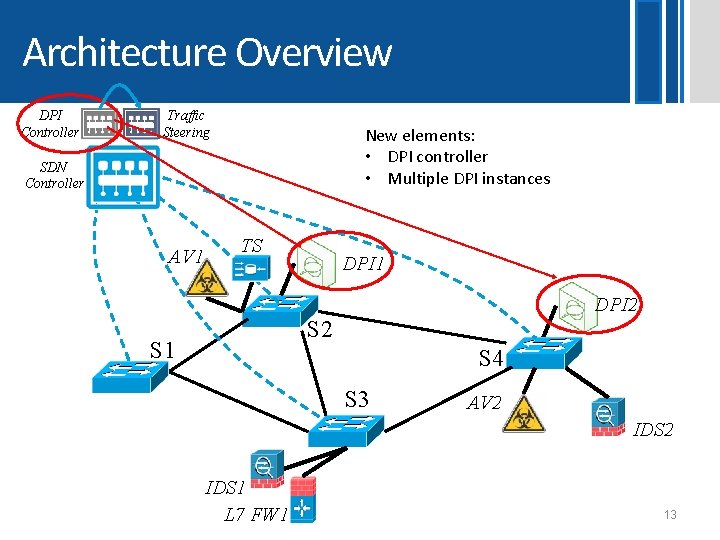
Architecture Overview DPI Controller Traffic Steering New elements: • DPI controller • Multiple DPI instances SDN Controller AV 1 TS DPI 1 DPI 2 S 1 S 4 S 3 AV 2 IDS 1 L 7 FW 1 13
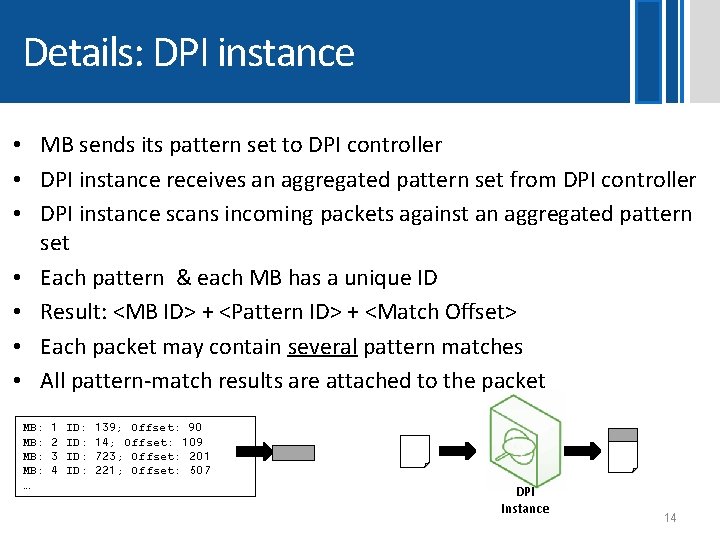
Details: DPI instance • MB sends its pattern set to DPI controller • DPI instance receives an aggregated pattern set from DPI controller • DPI instance scans incoming packets against an aggregated pattern set • Each pattern & each MB has a unique ID • Result: <MB ID> + <Pattern ID> + <Match Offset> • Each packet may contain several pattern matches • All pattern-match results are attached to the packet MB: MB: … 1 2 3 4 ID: ID: 139; Offset: 90 14; Offset: 109 723; Offset: 201 221; Offset: 507 DPI Instance 14
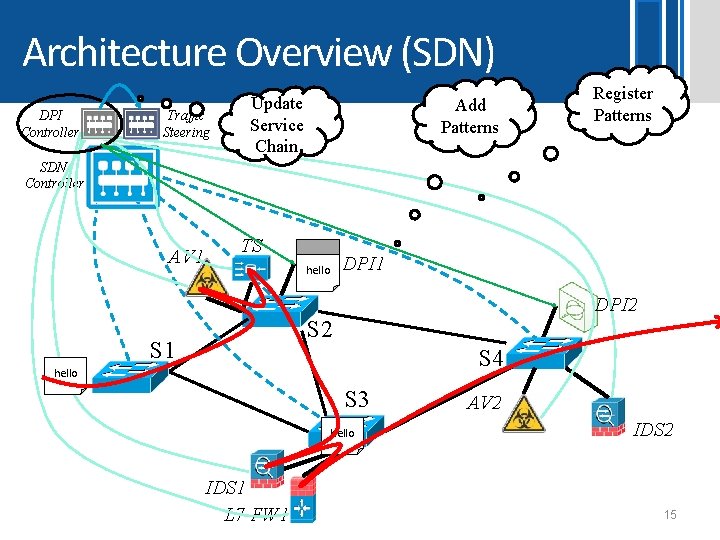
Architecture Overview (SDN) DPI Controller Traffic Steering Update Service Chain Add Patterns Register Patterns SDN Controller AV 1 TS DPI 1 hello DPI 2 S 1 S 4 hello S 3 hello IDS 1 L 7 FW 1 AV 2 IDS 2 15
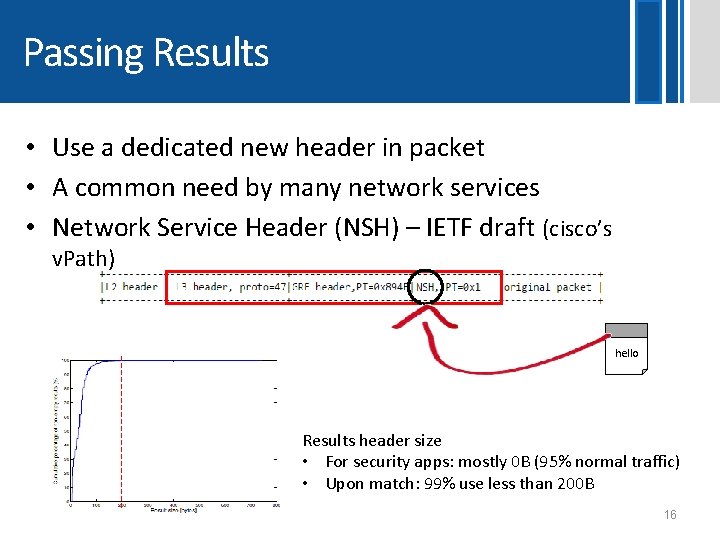
Passing Results • Use a dedicated new header in packet • A common need by many network services • Network Service Header (NSH) – IETF draft (cisco’s v. Path) hello Results header size • For security apps: mostly 0 B (95% normal traffic) • Upon match: 99% use less than 200 B 16
Question: Are The DPI algorithms scalable? 17
Are DPI Algorithms Scalable? • Yes, Yes each input byte requires a single lookup regardless the number of patterns!! • But: Lookup can be 1 memory access or 1 cache access • Increasing the number of patterns may result in a moderate performance reduction • DPI service has a small penalty as compared to its advantages. 18
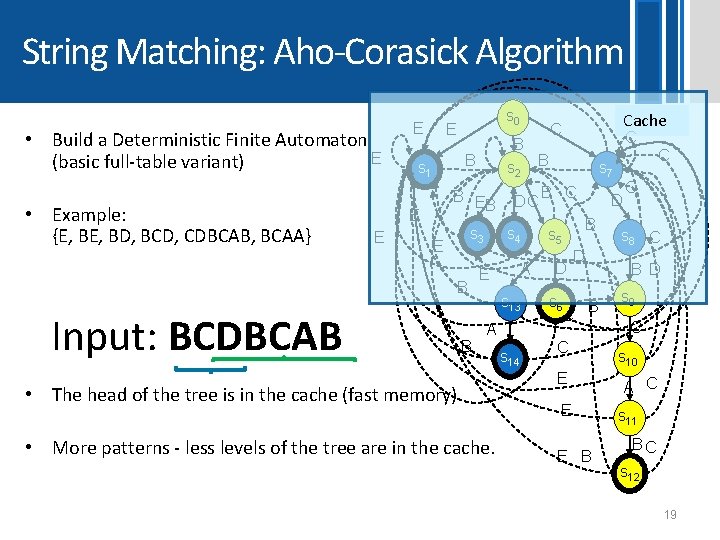
String Matching: Aho-Corasick Algorithm • Build a Deterministic Finite Automaton E (basic full-table variant) • Example: {E, BD, BCD, CDBCAB, BCAA} E B B s 2 B B E B DC s 1 E E s 0 E s 3 E B Input: BCDBCAB B s 4 E A s 13 A • The head of the tree is in the cache (fast memory). • More patterns - less levels of the tree are in the cache. s 14 Cache C C C s 7 B C B s 5 D D D s 6 B C C E E E B C s 8 C B D s 9 C s 10 A C s 11 BC s 12 19
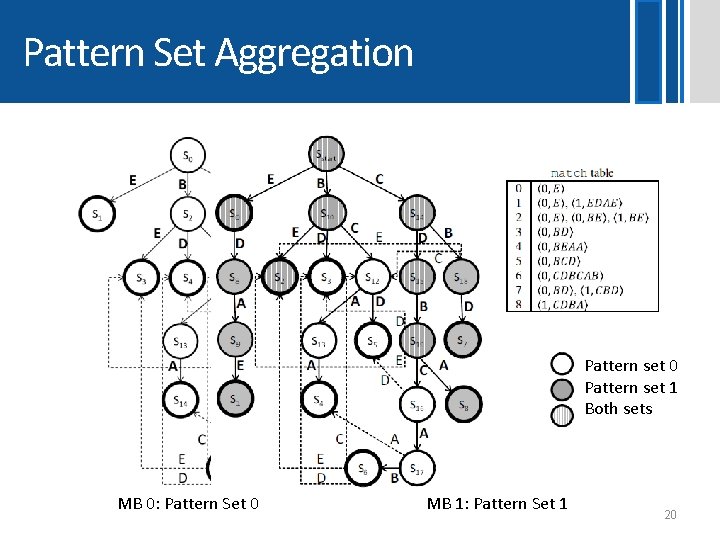
Pattern Set Aggregation Pattern set 0 Pattern set 1 Both sets Pattern set 1 Pattern set 2 MB 0: Pattern Set 0 MB 1: Pattern Set 1 Both sets 20
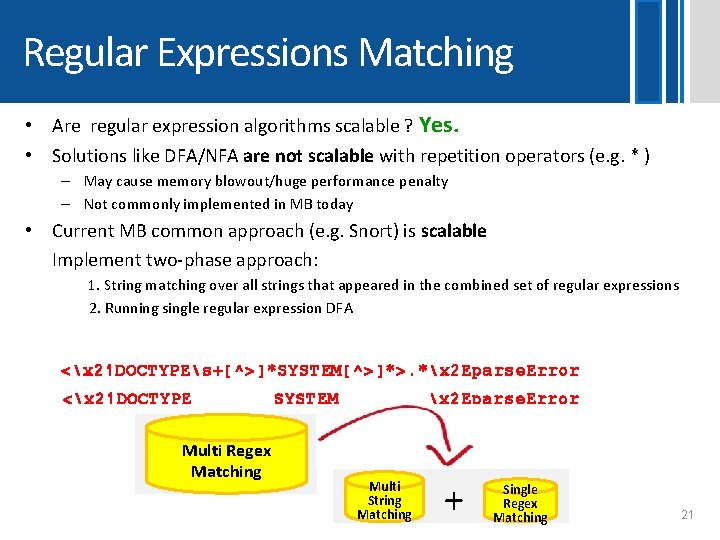
Regular Expressions Matching • Are regular expression algorithms scalable ? Yes. • Solutions like DFA/NFA are not scalable with repetition operators (e. g. * ) – May cause memory blowout/huge performance penalty – Not commonly implemented in MB today • Current MB common approach (e. g. Snort) is scalable Implement two-phase approach: 1. String matching over all strings that appeared in the combined set of regular expressions 2. Running single regular expression DFA <x 21 DOCTYPEs+[^>]*SYSTEM[^>]*>. *x 2 Eparse. Error <x 21 DOCTYPE Multi Regex Matching SYSTEM x 2 Eparse. Error Multi String Matching + Single Regex Matching 21
![Other Middlebox architecture DP AV 1 I • MB Consolidation – [Comb, NSDI 2012], Other Middlebox architecture DP AV 1 I • MB Consolidation – [Comb, NSDI 2012],](http://slidetodoc.com/presentation_image/ffc5170ed795399efafd4c9e00b38969/image-22.jpg)
Other Middlebox architecture DP AV 1 I • MB Consolidation – [Comb, NSDI 2012], [x. OMB, ANCS 2012], [Crossbeam, 2012], [Kekely et al. , Infocom 2014] DP IDS 1 L 7 FW 1 DP I I DP TS I DP I Hypervisor – One box to rule them all (MBs) – Unified management & resource sharing – Our DPI as a service can be also combined internal in MB consolidation solution • Outsource MB (out-of-network) – – [Gibb et al. , Hot. SDN 2012], [Sherry et al. , SIGCOMM 2012] Latency is no more an issue DDo. S mitigation - Prolexic (now part of Akamai) Our DPI as a service can be also combined in outsource MB 22

Experiments 23
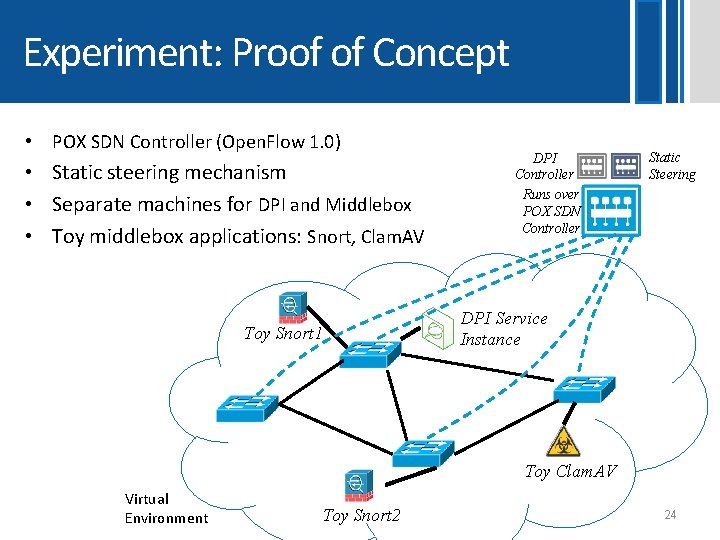
Experiment: Proof of Concept • POX SDN Controller (Open. Flow 1. 0) • Static steering mechanism • Separate machines for DPI and Middlebox • Toy middlebox applications: Snort, Clam. AV Toy Snort 1 DPI Controller Runs over POX SDN Controller Static Steering DPI Service Instance Toy Clam. AV Virtual Environment Toy Snort 2 24
![Throughput [Mbps] Virtual DPI Performance Number of Patterns • Running DPI as a virtual Throughput [Mbps] Virtual DPI Performance Number of Patterns • Running DPI as a virtual](http://slidetodoc.com/presentation_image/ffc5170ed795399efafd4c9e00b38969/image-25.jpg)
Throughput [Mbps] Virtual DPI Performance Number of Patterns • Running DPI as a virtual service has minor implications on performance
![Throughput [Mbps] DPI on Combined Pattern Set Total Number of Patterns • The throughput Throughput [Mbps] DPI on Combined Pattern Set Total Number of Patterns • The throughput](http://slidetodoc.com/presentation_image/ffc5170ed795399efafd4c9e00b38969/image-26.jpg)
Throughput [Mbps] DPI on Combined Pattern Set Total Number of Patterns • The throughput of the combined AC DFA is comparable to the original AC DFA • The number of patterns has moderate effect on the throughput
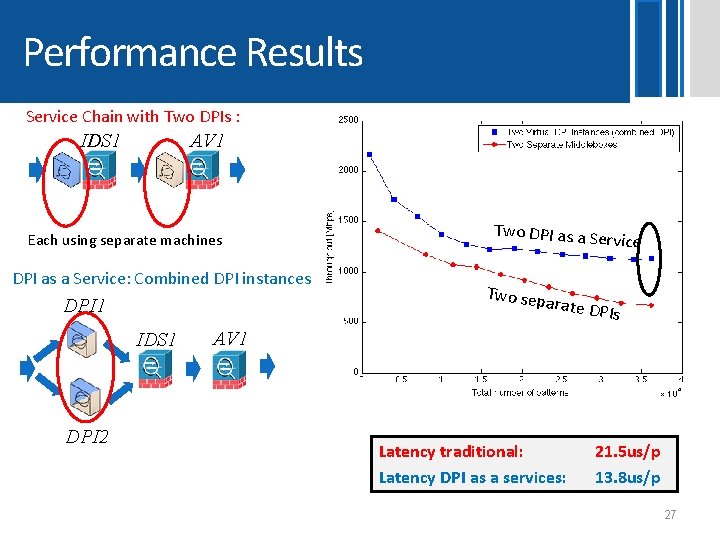
Performance Results Service Chain with Two DPIs : IDS 1 AV 1 Each using separate machines DPI as a Service: Combined DPI instances Two sep a rvice rate DPI 1 IDS 1 DPI 2 Two DPI as a Se s AV 1 Latency traditional: Latency DPI as a services: 21. 5 us/p 13. 8 us/p 27
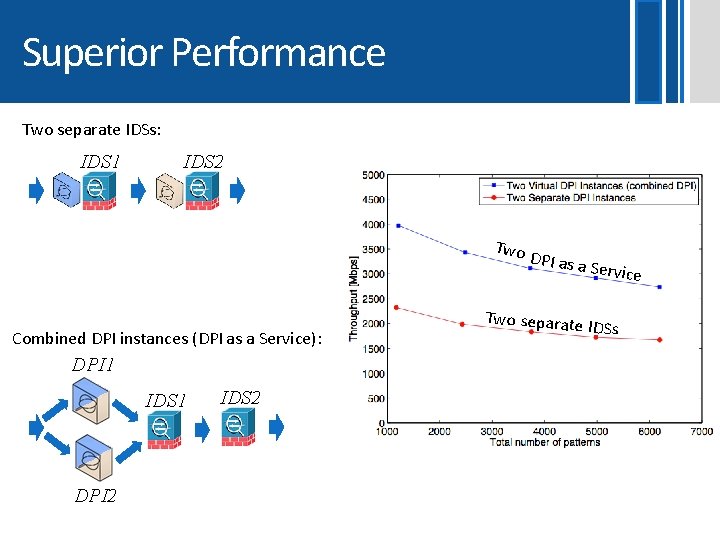
Superior Performance Two separate IDSs: IDS 1 IDS 2 Two Combined DPI instances (DPI as a Service): DPI 1 IDS 1 DPI 2 IDS 2 DPI as a Two separate Service IDSs
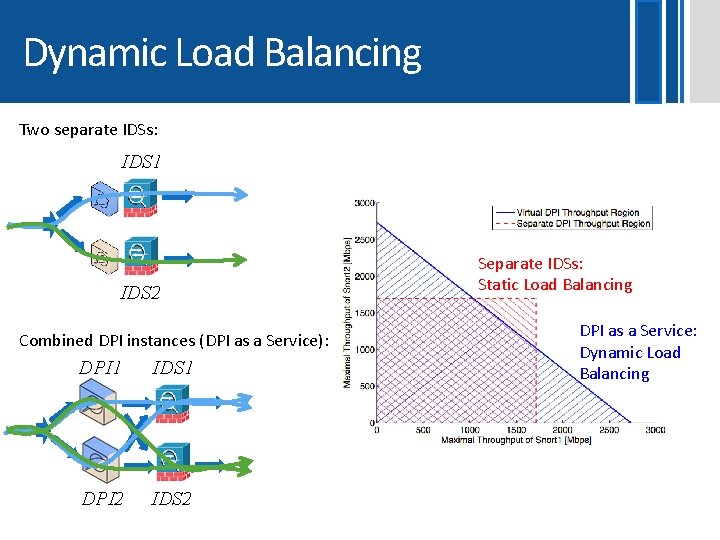
Dynamic Load Balancing Two separate IDSs: IDS 1 IDS 2 Combined DPI instances (DPI as a Service): DPI 1 IDS 1 DPI 2 IDS 2 Separate IDSs: Static Load Balancing DPI as a Service: Dynamic Load Balancing
Vision & Future work 30
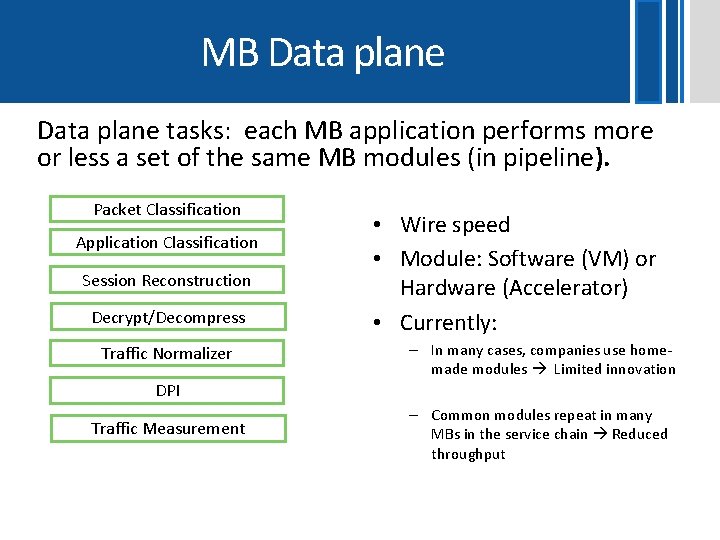
MB Data plane tasks: each MB application performs more or less a set of the same MB modules (in pipeline). Packet Classification Application Classification Session Reconstruction Decrypt/Decompress Traffic Normalizer • Wire speed • Module: Software (VM) or Hardware (Accelerator) • Currently: – In many cases, companies use homemade modules Limited innovation DPI Traffic Measurement – Common modules repeat in many MBs in the service chain Reduced throughput
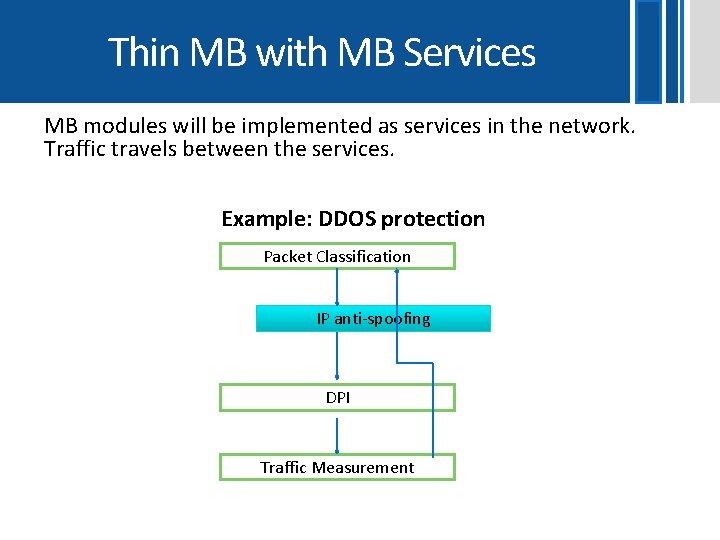
Thin MB with MB Services MB modules will be implemented as services in the network. Traffic travels between the services. Example: DDOS protection Packet Classification IP anti-spoofing DPI Traffic Measurement
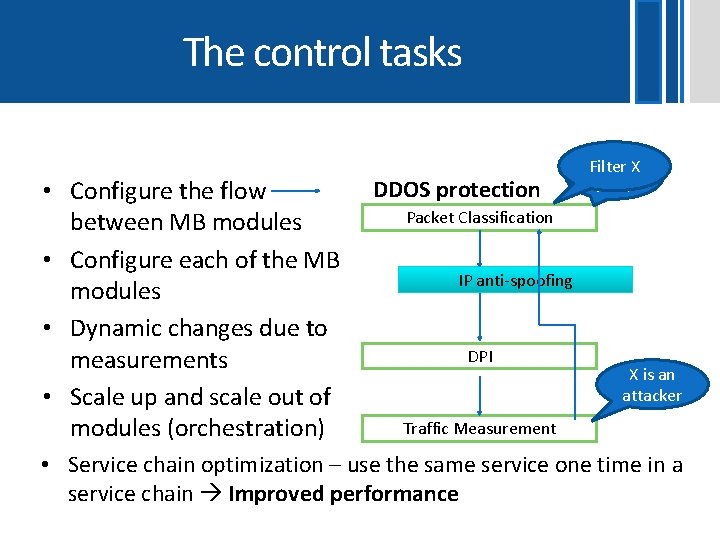
The control tasks • Configure the flow between MB modules • Configure each of the MB modules • Dynamic changes due to measurements • Scale up and scale out of modules (orchestration) DDOS protection FIlter. X Filter ICMP Packet Classification IP anti-spoofing DPI X is an attacker Traffic Measurement • Service chain optimization – use the same service one time in a service chain Improved performance
Innovation Enabler • Lower entry barriers – If the modules are services one can tailor a MB by using off-the shelf modules – Cheaper MB HW/SW • Richer functionality – Companies will specialize in specific MB modules • Simple MB would be implemented by off-the-shelf services and switches – Enhance Switch: use DPI service to tag packets to drive policies in switches – Enhance MB: SDN switches can perform the packet classification module 34
Related Industry solution: Qosmos • Application aware classification Application Classification – The company (Qosmos) suggests a NFV service that classifies the traffic • Skype/IM/Vo. IP/FTP/Video/Social Networks… 35
Anat Bremler-Barr David Hay Yotam Harchol Yaron Koral
Thank You!!
- Slides: 37