Declarative Routing Extensible Routing with Declarative Queries Boon
Declarative Routing: Extensible Routing with Declarative Queries Boon Thau Loo 1 Joseph M. Hellerstein 1, 2, Ion Stoica 1, Raghu Ramakrishnan 3, 1 University of California at Berkeley, 2 Intel Research Berkeley, 3 University of Wisconsin-Madison 1
Motivation Lack of extensibility and flexibility in today’s Internet routing Hard to add/improve/update routing protocols 2
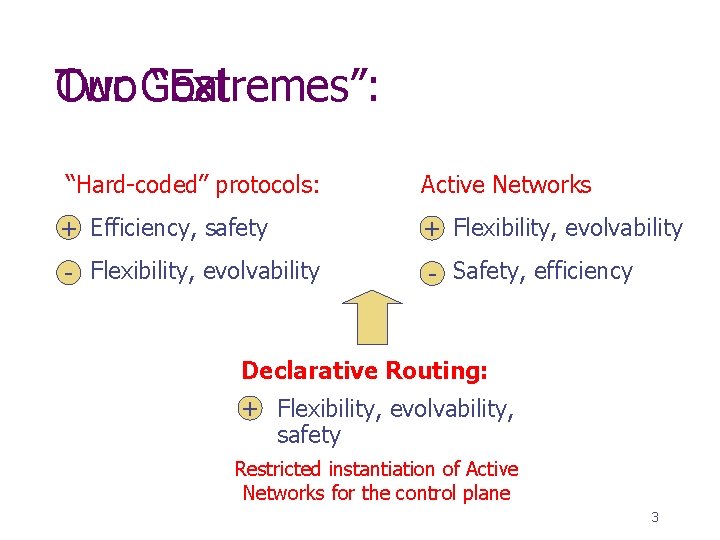
Two Our Goal “Extremes”: “Hard-coded” protocols: Active Networks +- Efficiency, safety -+ Flexibility, evolvability -- Safety, efficiency Declarative Routing: + Flexibility, evolvability, safety Restricted instantiation of Active Networks for the control plane 3
Key Idea Recursive query language for expressing routing protocols: n n n Datalog: a declarative recursive query language Well-researched in the database community Well-suited for querying properties of graphs 4
Advantages Expressiveness: Compact and clean representation of protocols Safety: Datalog has desirable safety properties on termination Efficiency: No fundamental overhead when executing standard protocols. 5
Usage Scenarios ISP administrators n n Run different protocols for different nodes Modify existing protocols in routers End-hosts n Set up customized routes for different quality-of-service and policy requirements of applications 6
Roadmap Execution Model Introduction to Datalog Path-Vector Protocol Example Advantages: n n n Expressiveness Safety Efficiency Evaluation 7
Centralized Execution Model Store entire network state into a centralized database Issue Datalog queries on the centralized database for customized routes 8
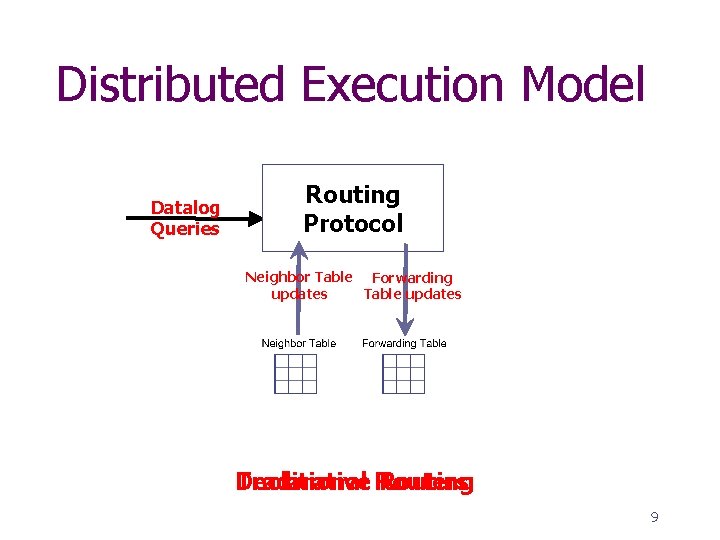
Distributed Execution Model Query Processor Datalog Queries Routing Input Output Tables Protocol Neighbor Table Forwarding updates Table updates Declarative Traditional Routers Routing 9
Introduction to Datalog rule syntax: <head> <precondition 1>, <precondition 2>, … , <precondition. N>. 10
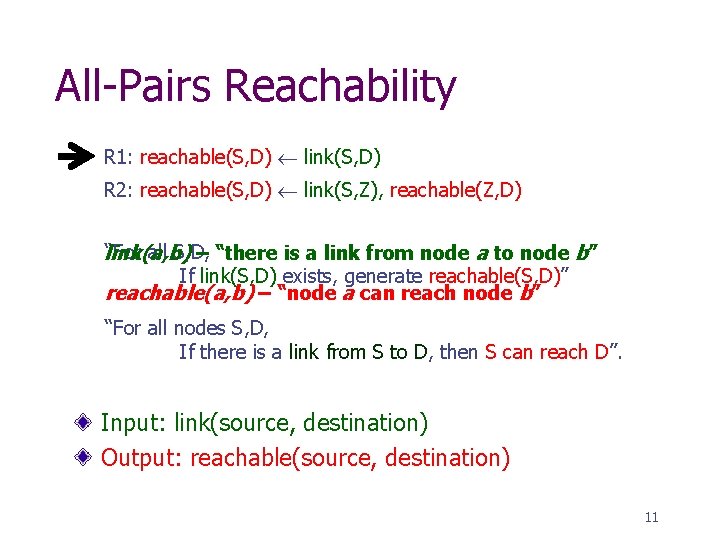
All-Pairs Reachability R 1: reachable(S, D) link(S, D) R 2: reachable(S, D) link(S, Z), reachable(Z, D) “For all S, D, link(a, b) – “there is a link from node a to node b” If link(S, D) exists, generate reachable(S, D)” reachable(a, b) – “node a can reach node b” “For all nodes S, D, If there is a link from S to D, then S can reach D”. Input: link(source, destination) Output: reachable(source, destination) 11
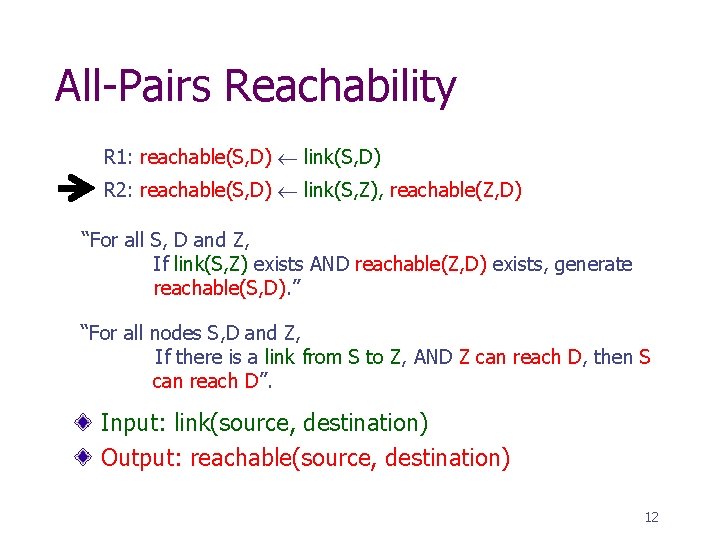
All-Pairs Reachability R 1: reachable(S, D) link(S, D) R 2: reachable(S, D) link(S, Z), reachable(Z, D) “For all S, D and Z, If link(S, Z) exists AND reachable(Z, D) exists, generate reachable(S, D). ” “For all nodes S, D and Z, If there is a link from S to Z, AND Z can reach D, then S can reach D”. Input: link(source, destination) Output: reachable(source, destination) 12
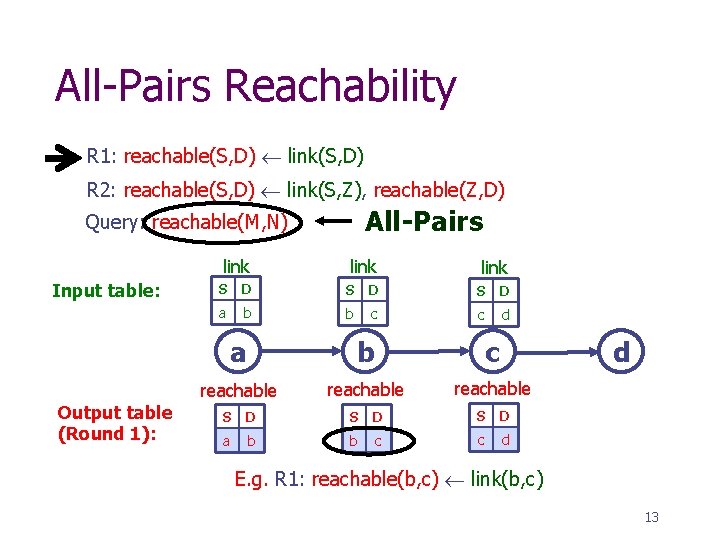
All-Pairs Reachability R 1: reachable(S, D) link(S, D) R 2: reachable(S, D) link(S, Z), reachable(Z, D) All-Pairs Query: reachable(M, N) Input table: Output table (Round 1): link S D S D a b b c c d a b c d reachable S D S D a b b c c d E. g. R 1: reachable(b, c) link(b, c) 13
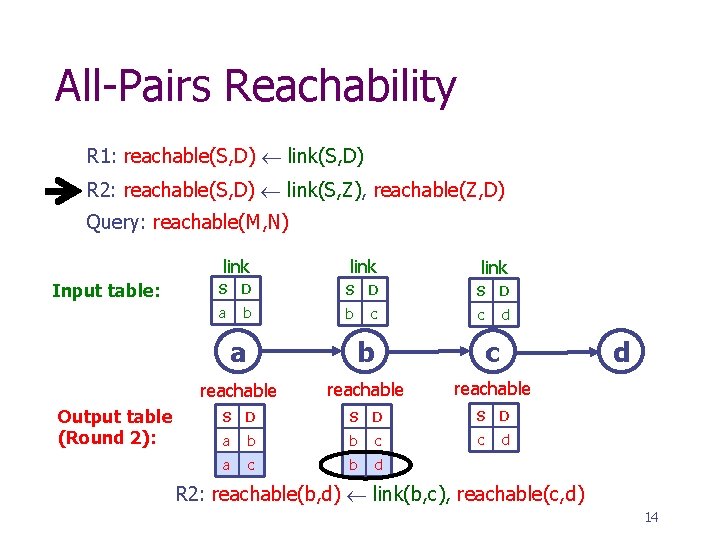
All-Pairs Reachability R 1: reachable(S, D) link(S, D) R 2: reachable(S, D) link(S, Z), reachable(Z, D) Query: reachable(M, N) Input table: Output table (Round 2): link S D S D a b b c c d a b c d reachable S D S D a b b c c d a c b d R 2: reachable(b, d) link(b, c), reachable(c, d) 14
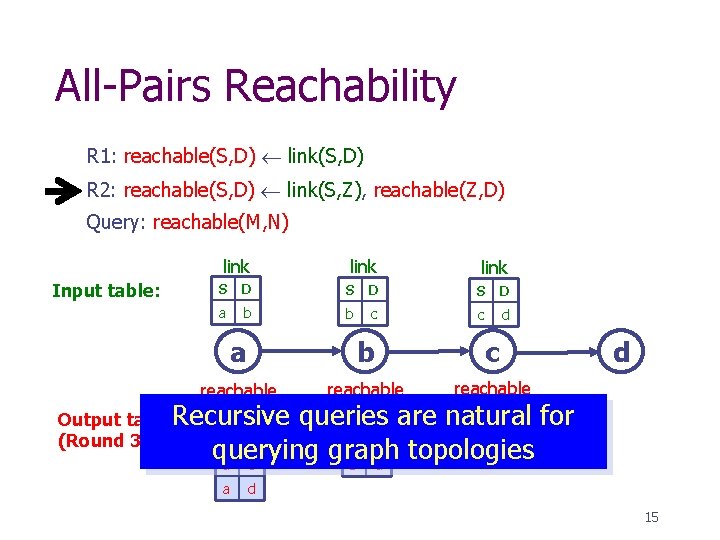
All-Pairs Reachability R 1: reachable(S, D) link(S, D) R 2: reachable(S, D) link(S, Z), reachable(Z, D) Query: reachable(M, N) Input table: link S D S D a b b c c d a b c reachable S D Output table. Recursive a b (Round 3): d S D are natural queries for c d b c querying graph topologies a c b d a d 15
Roadmap Execution Model Introduction to Datalog Path-Vector Protocol Example n Distributed Datalog Execution Plan Protocol Advantages: n n n Expressiveness Safety Efficiency Evaluation 16
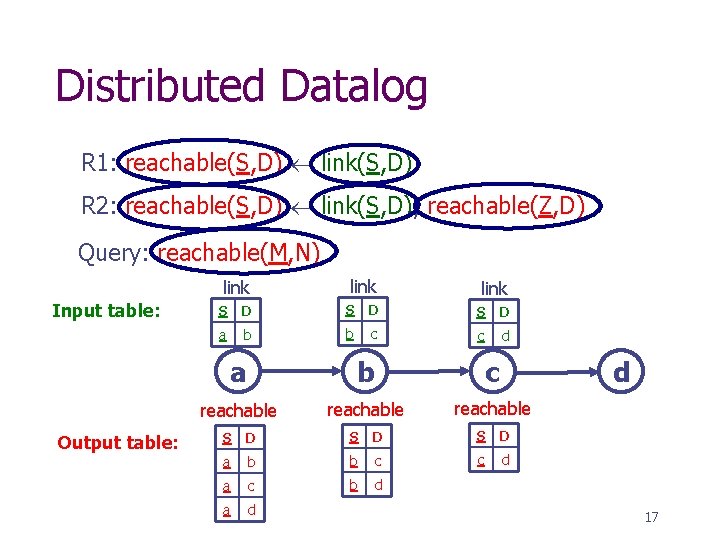
Distributed Datalog R 1: reachable(S, D) link(S, D) R 2: reachable(S, D) link(S, D), reachable(Z, D) Query: reachable(M, N) Input table: Output table: link S D S D a b b c c d a b c d reachable S D S D a b b c c d a c b d a d 17
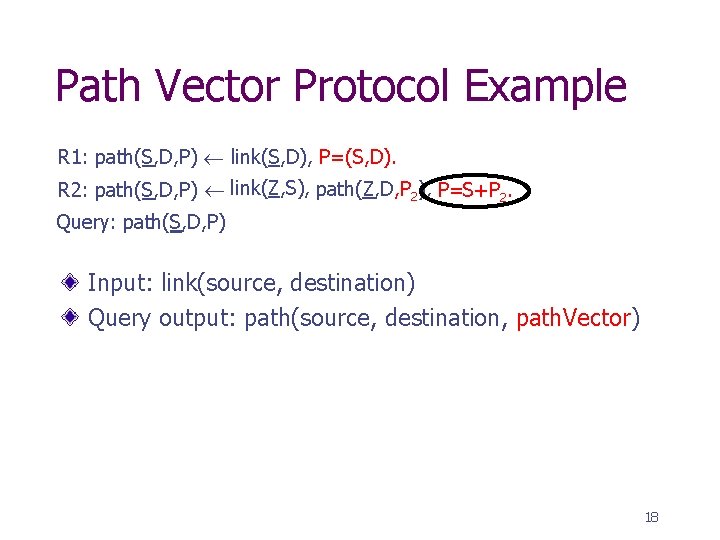
Path Vector Protocol Example R 1: path(S, D, P) link(S, D), P=(S, D). R 2: path(S, D, P) link(Z, S), path(Z, D, P 2), P=S+P 2. Query: path(S, D, P) Input: link(source, destination) Query output: path(source, destination, path. Vector) 18
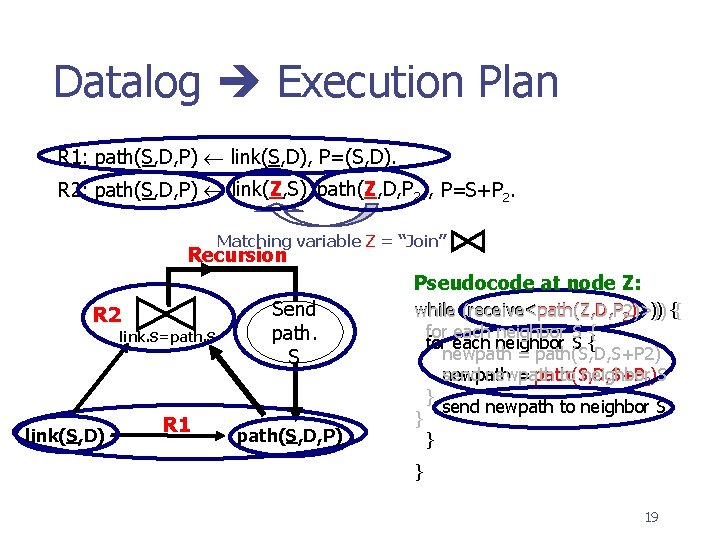
Datalog Execution Plan R 1: path(S, D, P) link(S, D), P=(S, D). R 2: path(S, D, P) link(Z, S), path(Z, D, P 2), P=S+P 2. Matching variable Z = “Join” Recursion Pseudocode at node Z: R 2 link. S=path. S link(S, D) R 1 Send path. S path(S, D, P) while (receive<path(Z, D, P 2)>)) {{ for each neighbor S { newpath = path(S, D, S+P 2) newpath = path(S, D, S+P send newpath to neighbor 2)S } send newpath to neighbor S } } } 19
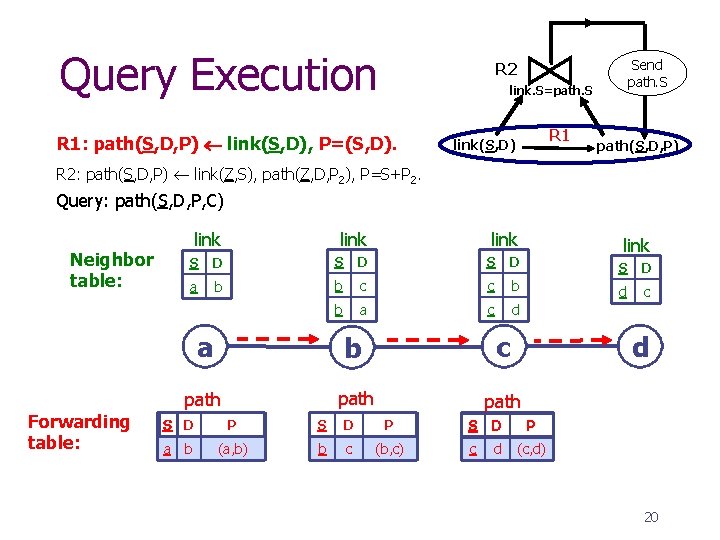
Query Execution Send path. S R 2 link. S=path. S R 1: path(S, D, P) link(S, D), P=(S, D). R 1 link(S, D) path(S, D, P) R 2: path(S, D, P) link(Z, S), path(Z, D, P 2), P=S+P 2. Query: path(S, D, P, C) link Neighbor table: Forwarding table: link S D S D a b b c c b d c b a c d a b c path S D a link b d P S D P (a, b) b c (b, c) c d (c, d) 20
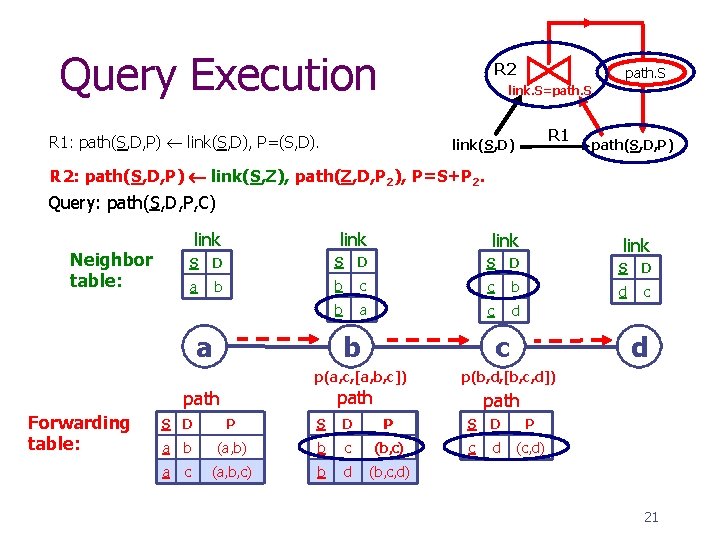
Query Execution R 2 path. S link. S=path. S R 1: path(S, D, P) link(S, D), P=(S, D). R 1 link(S, D) path(S, D, P) R 2: path(S, D, P) link(S, Z), path(Z, D, P 2), P=S+P 2. Query: path(S, D, P, C) link Neighbor table: link S D S D a b b c c b d c b a c d b a c p(a, c, [a, b, c]) S D d p(b, d, [b, c, d]) path Forwarding table: link path P S D P c d (c, d) a b (a, b) b c (b, c) a c (a, b, c) b d (b, c, d) 21
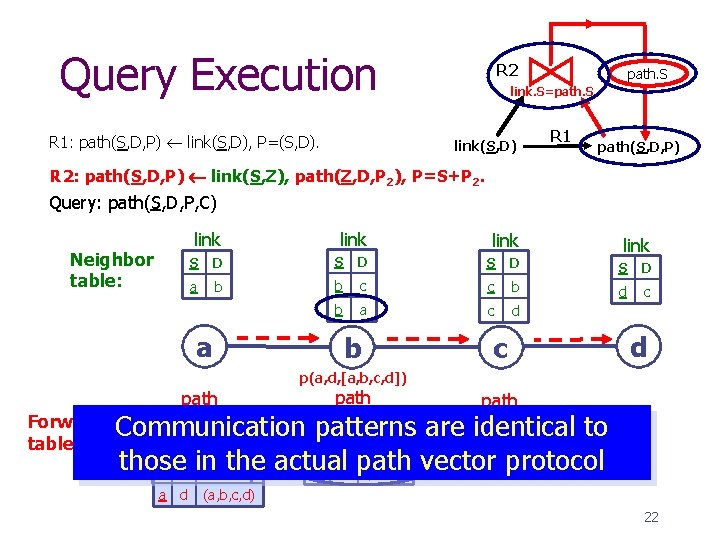
Query Execution R 1: path(S, D, P) link(S, D), P=(S, D). R 2 path. S link. S=path. S link(S, D) R 1 path(S, D, P) R 2: path(S, D, P) link(S, Z), path(Z, D, P 2), P=S+P 2. Query: path(S, D, P, C) link Neighbor table: link S D S D a b b c c b d c b a c d a b c d p(a, d, [a, b, c, d]) path Forwarding S D PP Communication table: (a, b) a b (a, b) path D P patterns are. Sidentical to c d (c, d) b c (b, c) those the actual path vector protocol (a, b, c) a c in (a, b, c) b d (b, c, d) a d S (a, b, c, d) 22
Roadmap Execution Model Introduction to Datalog Path-Vector Protocol Example n Distributed Datalog Execution Plan Protocol Advantages: n n n Expressiveness Safety Efficiency Evaluation 23
Expressiveness Best-Path Routing Minor variants give Distance Vector many options! Dynamic Source Routing Policy Decisions Qo. S-based Routing Link-state Multicast Overlays (Single-Source & CBT) 24
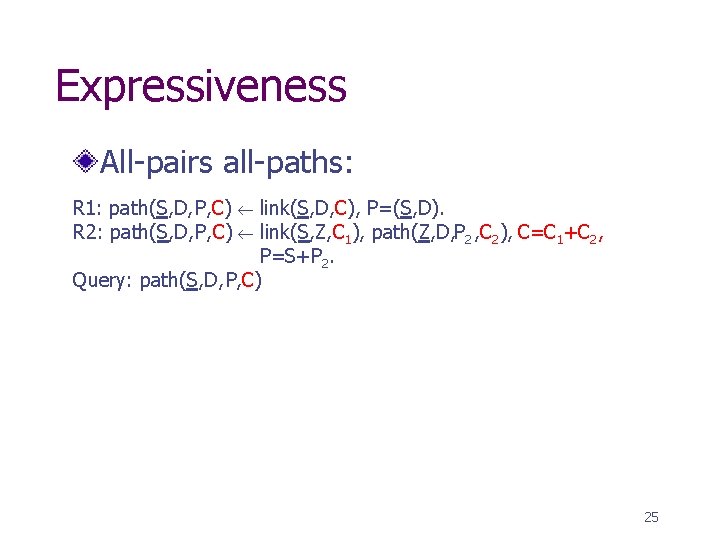
Expressiveness All-pairs all-paths: R 1: path(S, D, P, C) link(S, D, C) , P=(S, D). R 2: path(S, D, P, C) link(S, Z, C 1), path(Z, D, P 2 , C 2), C=C 1+C 2, P=S+P 2. Query: path(S, D, P, C) 25
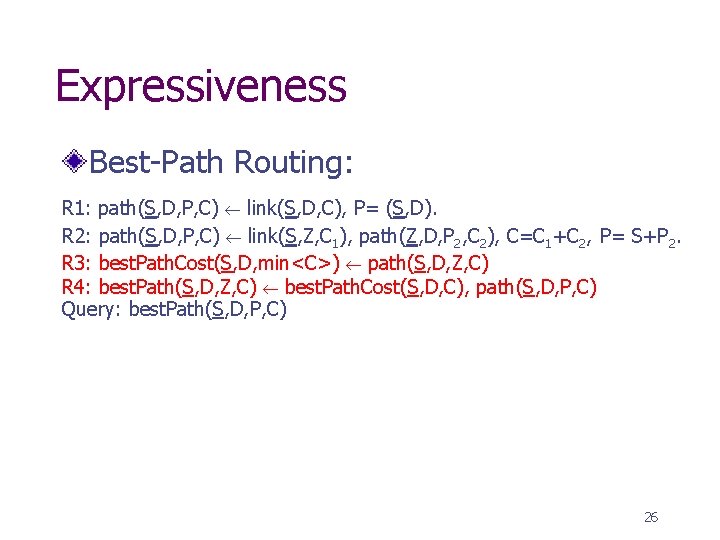
Expressiveness Best-Path Routing: R 1: path(S, D, P, C) link(S, D, C), P= (S, D). R 2: path(S, D, P, C) link(S, Z, C 1), path(Z, D, P 2, C 2), C=C 1+C 2, P= S+P 2. R 3: best. Path. Cost(S, D, min<C>) path(S, D, Z, C) R 4: best. Path(S, D, Z, C) best. Path. Cost(S, D, C), path(S, D, P, C) Query: best. Path(S, D, P, C) 26
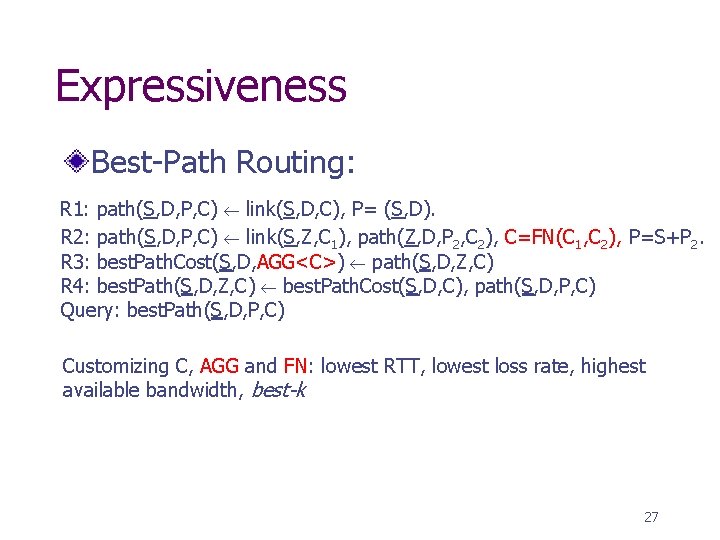
Expressiveness Best-Path Routing: R 1: path(S, D, P, C) link(S, D, C), P= (S, D). R 2: path(S, D, P, C) link(S, Z, C 1), path(Z, D, P 2, C 2), C=FN(C 1, C 2), P=S+P 2. R 3: best. Path. Cost(S, D, AGG<C>) path(S, D, Z, C) R 4: best. Path(S, D, Z, C) best. Path. Cost(S, D, C), path(S, D, P, C) Query: best. Path(S, D, P, C) Customizing C, AGG and FN: lowest RTT, lowest loss rate, highest available bandwidth, best-k 27
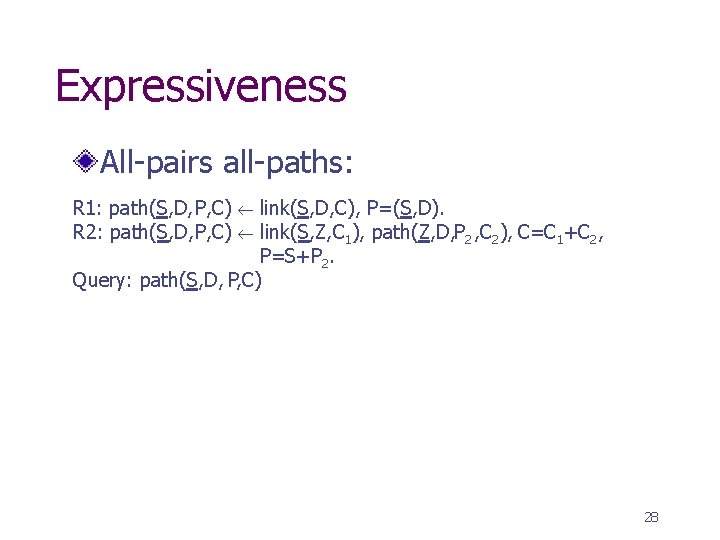
Expressiveness All-pairs all-paths: R 1: path(S, D, P, C) link(S, D, C) , P=(S, D). R 2: path(S, D, P, C) link(S, Z, C 1), path(Z, D, P 2 , C 2), C=C 1+C 2, P=S+P 2. Query: path(S, D, P, C) 28
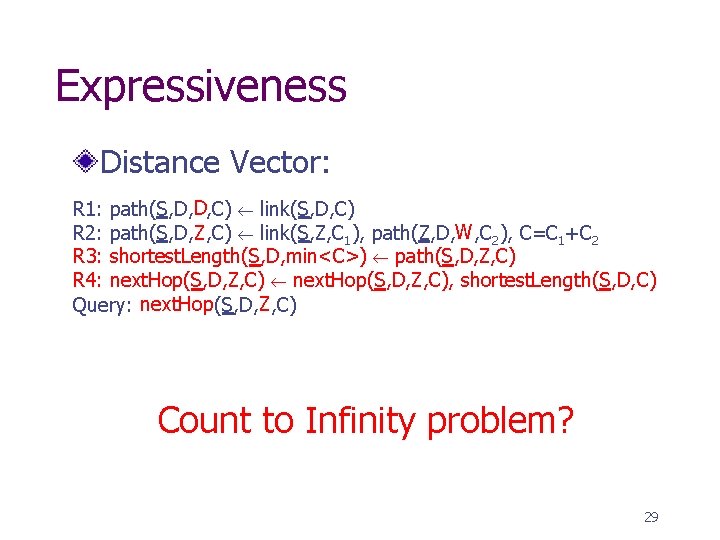
Expressiveness Distance Vector: R 1: path(S, D, D, C) link(S, D, C) R 2: path(S, D, Z , C) link(S, Z, C 1), path(Z, D, W , C 2), C=C 1+C 2 R 3: shortest. Length(S, D, min<C>) path(S, D, Z, C) R 4: next. Hop(S, D, Z, C), shortest. Length(S, D, C) Query: next. Hop(S, D, Z , C) Count to Infinity problem? 29
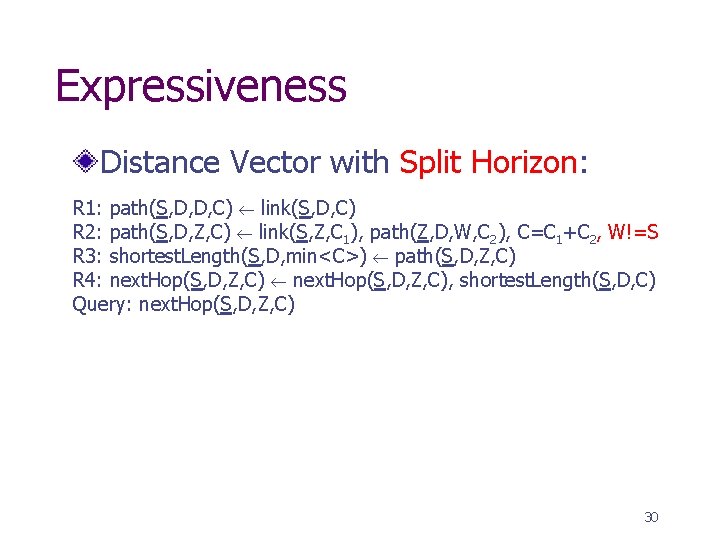
Expressiveness Distance Vector with Split Horizon: R 1: path(S, D, D, C) link(S, D, C) R 2: path(S, D, Z, C) link(S, Z, C 1), path(Z, D, W, C 2), C=C 1+C 2, W!=S R 3: shortest. Length(S, D, min<C>) path(S, D, Z, C) R 4: next. Hop(S, D, Z, C), shortest. Length(S, D, C) Query: next. Hop(S, D, Z, C) 30
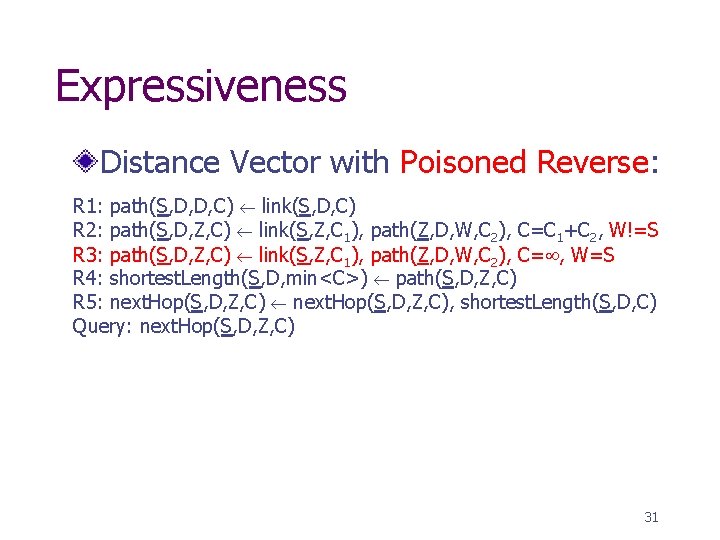
Expressiveness Distance Vector with Poisoned Reverse: R 1: path(S, D, D, C) link(S, D, C) R 2: path(S, D, Z, C) link(S, Z, C 1), path(Z, D, W, C 2), C=C 1+C 2, W!=S R 3: path(S, D, Z, C) link(S, Z, C 1), path(Z, D, W, C 2), C= , W=S R 4: shortest. Length(S, D, min<C>) path(S, D, Z, C) R 5: next. Hop(S, D, Z, C), shortest. Length(S, D, C) Query: next. Hop(S, D, Z, C) 31
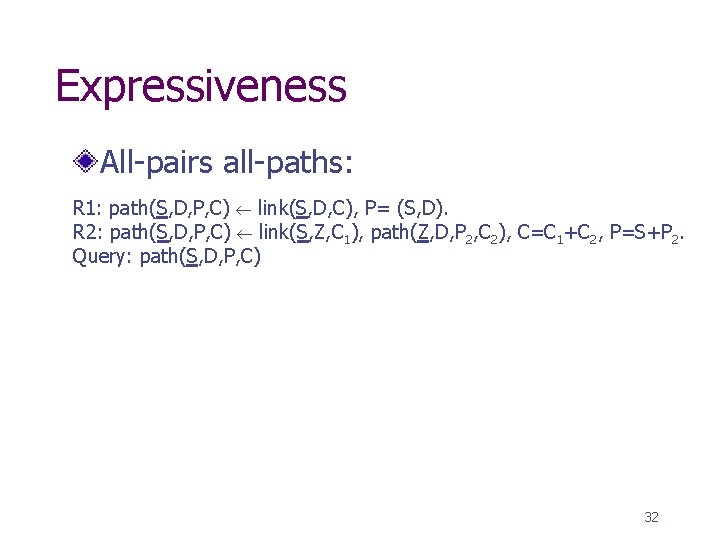
Expressiveness All-pairs all-paths: R 1: path(S, D, P, C) link(S, D, C), P= (S, D). R 2: path(S, D, P, C) link(S, Z, C 1), path(Z, D, P 2, C 2), C=C 1+C 2, P=S+P 2. Query: path(S, D, P, C) 32
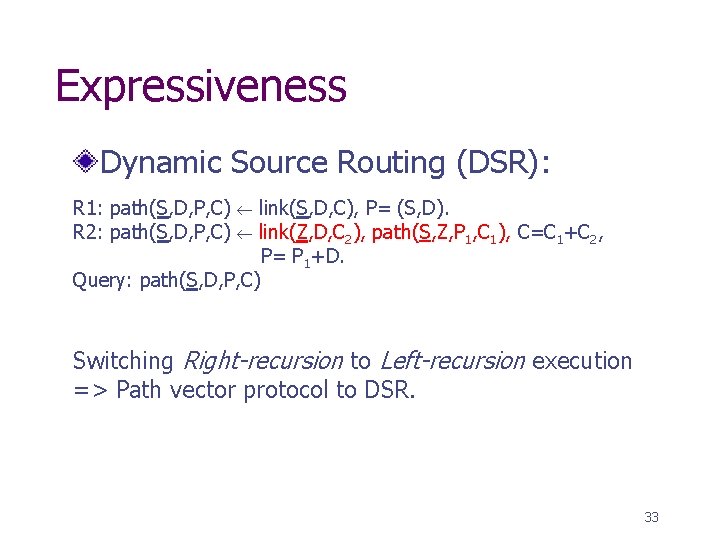
Expressiveness Dynamic Source Routing (DSR): R 1: path(S, D, P, C) R 2: path(S, D, P, C) link(S, D, C), P= (S, D). link(Z, D, C 2), path(S, Z, P 1, C 1), C=C 1+C 2, P= P 1+D. Query: path(S, D, P, C) Switching Right-recursion to Left-recursion execution => Path vector protocol to DSR. 33
Expressiveness Best-Path routing Distance Vector Dynamic Source Routing Policy-based routing Qo. S-based routing Link-state Multicast Overlays (Single-Source & CBT) 34
Safety Queries are sand-boxed within query engine n n Queries use input tables to produce output tables No side-effects on existing input tables Pure Datalog guarantees termination: n Natural bound on resource consumption of queries Static termination checks for our extended Datalog: n n Identify recursive definitions and check for termination E. g. , monotonically increasing/decreasing cost fields whose values are upper/lower bounded Orthogonal security issues: n Denial-of-service attacks, compromised routers 35
Efficiency Explore well-known database techniques n n Aggregate selections: avoid sending unnecessary paths to neighbors Limit computation to portion of network w Few sources and destinations w Magic sets + left-right recursion rewrite n Multi-query sharing: w Identify “similar” queries, share their computations w Reuse previously computed paths 36
Queries under Churn Long-running continuous queries Maintain all intermediate derived tuples for query duration Incremental updates: n n Link failures are treated as link updates with cost=infinity. Paths invalidated (cost=infinity), and new paths are incrementally recomputed. 37
Evaluation Setup PIER: Distributed relational query processor n n Each node runs the query engine of PIER Initialized neighbor table directly accessible by PIER. Simulation: n n Bandwidth and latency bottlenecks Transit-stub topologies Planet. Lab n n n 72 PIER nodes Random, location-aware topologies Long-running queries 38
Summary of Results Simulations: n When all nodes issue the same query, w Scalability properties show similar trends as traditional DV/PV protocols n When few nodes issue the same query, w Overhead is reduced using standard query optimizations Planet. Lab experiments: n n n Long-running all-pairs shortest RTT paths query Ability to handle link RTT changes Induced failures (up to 20% of nodes) w Recovery time: <1 s (median), <3. 6 s (average) 39
Conclusion Declarative routing: n n Express routing protocols using a recursive query language Better balance between routing extensibility and safety Future work: n n Expressing policies as declarative rules Run-time query optimizations: w Cost-based decisions on query rewrites w Multi-query sharing n n Static checker for routing protocols Run-time monitoring of routing protocols Declarative Networks n n Research agenda: Specify and construct networks declaratively P 2: “Implementing Declarative Overlays” (SOSP 2005) 40
Thank You 41
- Slides: 41