Debunking the Myths and Establishing the Realities of
Debunking the Myths and Establishing the Realities of Security in Telemedicine Telehealth Alliance of Oregon 8 th Annual Meeting & Summit February 5, 2015 René Quashie Epstein Becker Green rquashie@ebglaw. com David Trepp Info@Risk davidt@infoatrisk. com .
Introduction 2
Today’s Presenters § Rene Quashie • Epstein Becker and Green: National law firm with a primary focus on health care and life sciences • Rene Quashie, Senior Counsel: HIPAA & telemedicine expertise § David Trepp • Info@Risk: National information security risk analysis firm • David Trepp, President & CEO: information security & privacy expertise 3
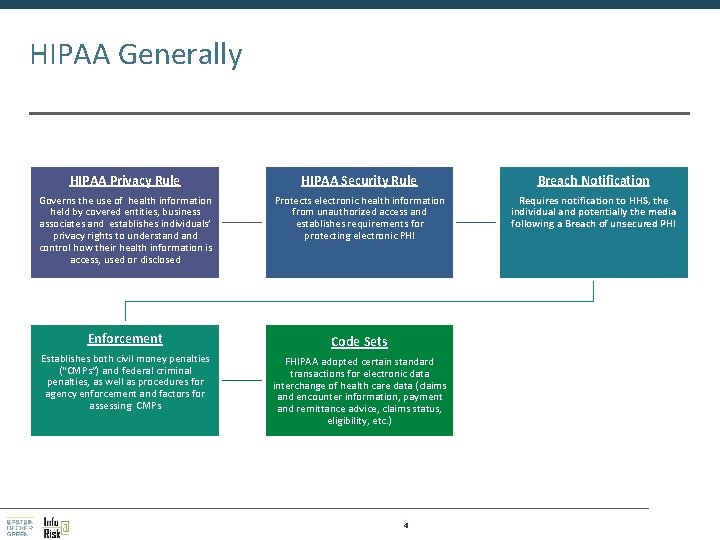
HIPAA Generally HIPAA Privacy Rule HIPAA Security Rule Breach Notification Governs the use of health information held by covered entities, business associates and establishes individuals’ privacy rights to understand control how their health information is access, used or disclosed Protects electronic health information from unauthorized access and establishes requirements for protecting electronic PHI Requires notification to HHS, the individual and potentially the media following a Breach of unsecured PHI Enforcement Code Sets Establishes both civil money penalties (“CMPs”) and federal criminal penalties, as well as procedures for agency enforcement and factors for assessing CMPs FHIPAA adopted certain standard transactions for electronic data interchange of health care data (claims and encounter information, payment and remittance advice, claims status, eligibility, etc. ) 4
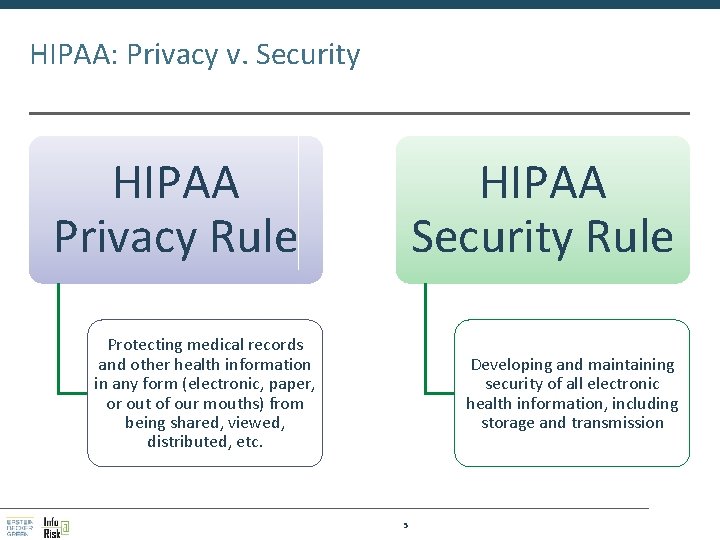
HIPAA: Privacy v. Security HIPAA Privacy Rule HIPAA Security Rule Protecting medical records and other health information in any form (electronic, paper, or out of our mouths) from being shared, viewed, distributed, etc. Developing and maintaining security of all electronic health information, including storage and transmission 5
Privacy Rule 6
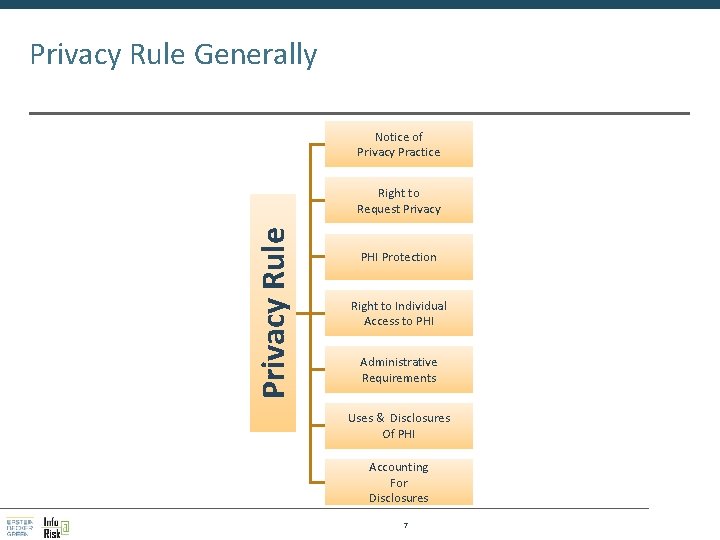
Privacy Rule Generally Notice of Privacy Practice Privacy Rule Right to Request Privacy PHI Protection Right to Individual Access to PHI Administrative Requirements Uses & Disclosures Of PHI Accounting For Disclosures 7
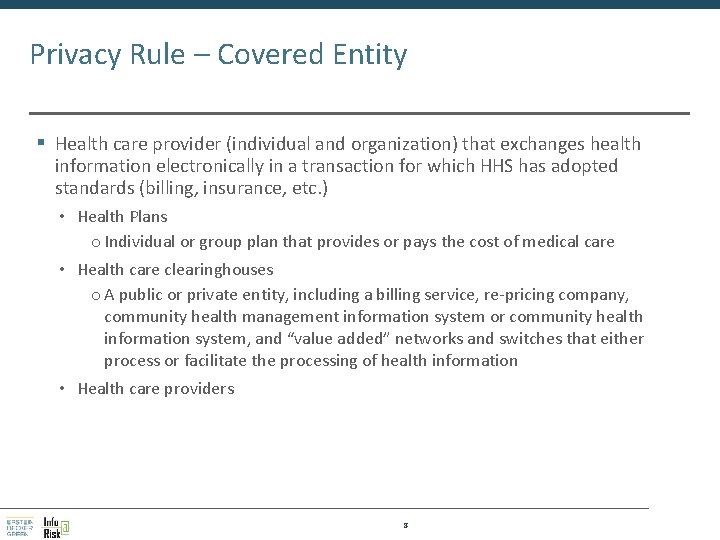
Privacy Rule – Covered Entity § Health care provider (individual and organization) that exchanges health information electronically in a transaction for which HHS has adopted standards (billing, insurance, etc. ) • Health Plans o Individual or group plan that provides or pays the cost of medical care • Health care clearinghouses o A public or private entity, including a billing service, re-pricing company, community health management information system or community health information system, and “value added” networks and switches that either process or facilitate the processing of health information • Health care providers 8
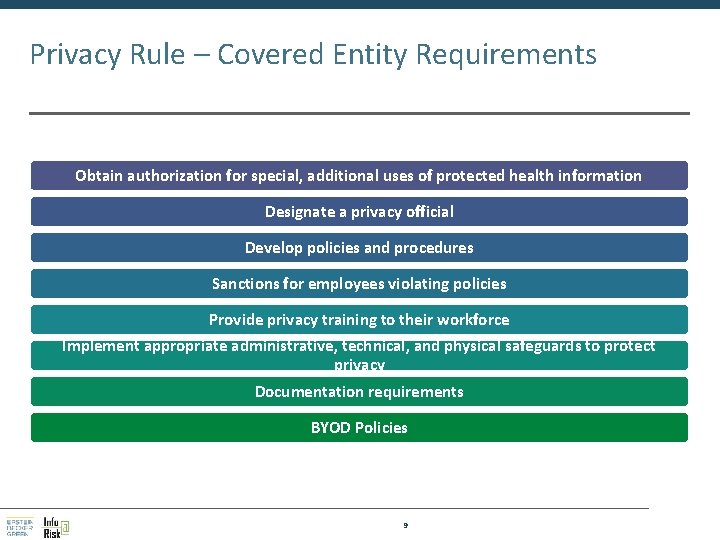
Privacy Rule – Covered Entity Requirements Obtain authorization for special, additional uses of protected health information Designate a privacy official Develop policies and procedures Sanctions for employees violating policies Provide privacy training to their workforce Implement appropriate administrative, technical, and physical safeguards to protect privacy Documentation requirements BYOD Policies 9
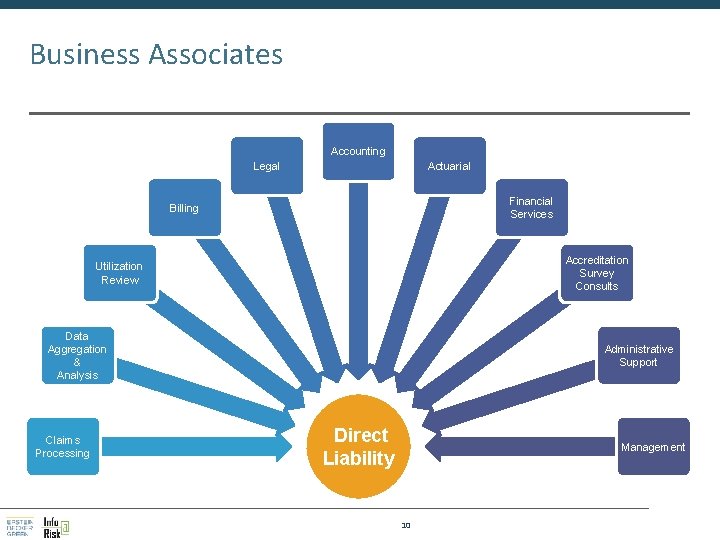
Business Associates Accounting Legal Actuarial Financial Services Billing Accreditation Survey Consults Utilization Review Data Aggregation & Analysis Claims Processing Administrative Support Direct Liability Management 10
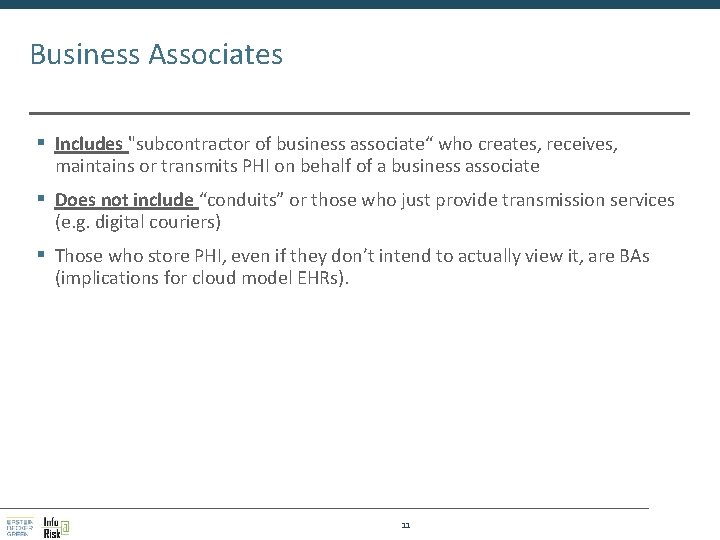
Business Associates § Includes "subcontractor of business associate“ who creates, receives, maintains or transmits PHI on behalf of a business associate § Does not include “conduits” or those who just provide transmission services (e. g. digital couriers) § Those who store PHI, even if they don’t intend to actually view it, are BAs (implications for cloud model EHRs). 11
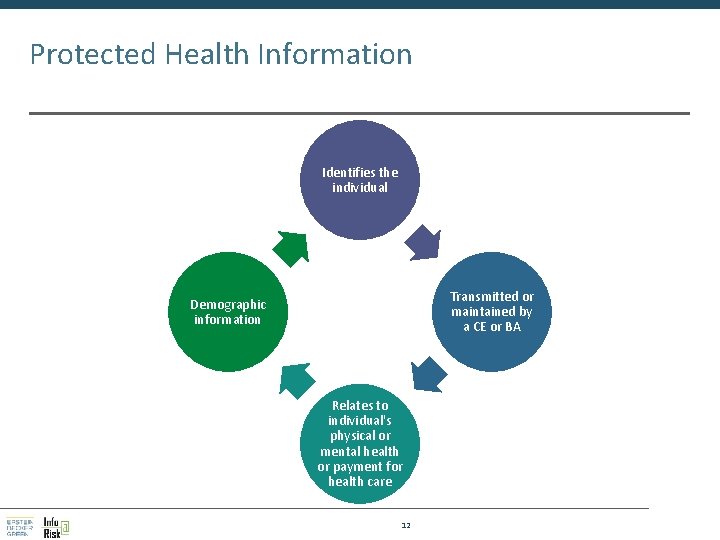
Protected Health Information Identifies the individual Transmitted or maintained by a CE or BA Demographic information Relates to individual's physical or mental health or payment for health care 12
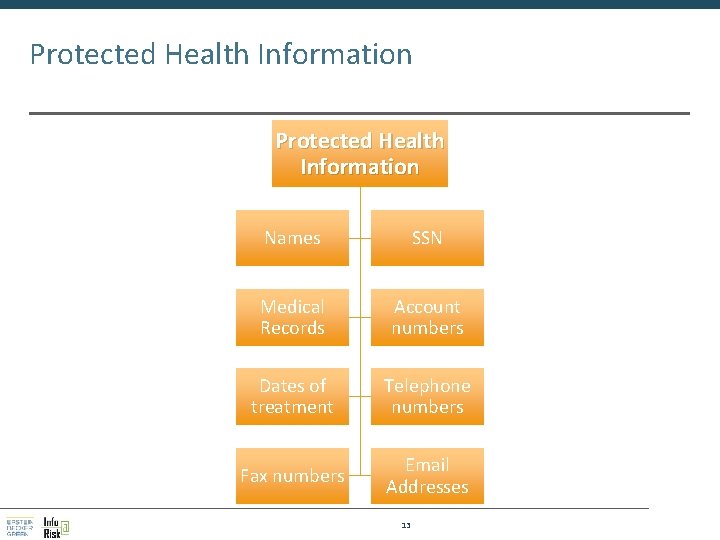
Protected Health Information Names SSN Medical Records Account numbers Dates of treatment Telephone numbers Fax numbers Email Addresses 13
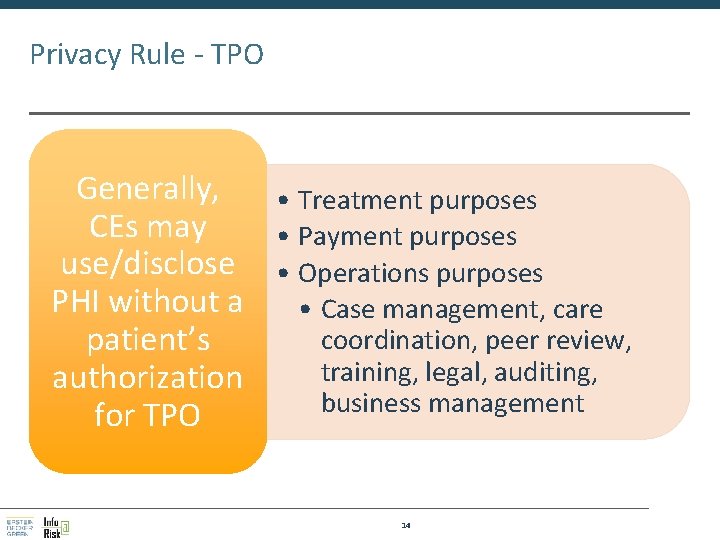
Privacy Rule - TPO Generally, • Treatment purposes CEs may • Payment purposes use/disclose • Operations purposes PHI without a • Case management, care coordination, peer review, patient’s training, legal, auditing, authorization business management for TPO 14
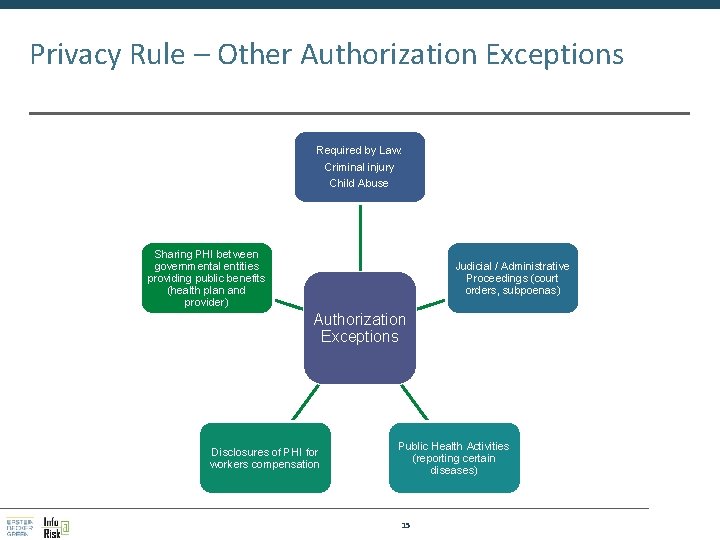
Privacy Rule – Other Authorization Exceptions Required by Law: Criminal injury Child Abuse Sharing PHI between governmental entities providing public benefits (health plan and provider) Judicial / Administrative Proceedings (court orders, subpoenas) Authorization Exceptions Disclosures of PHI for workers compensation Public Health Activities (reporting certain diseases) 15
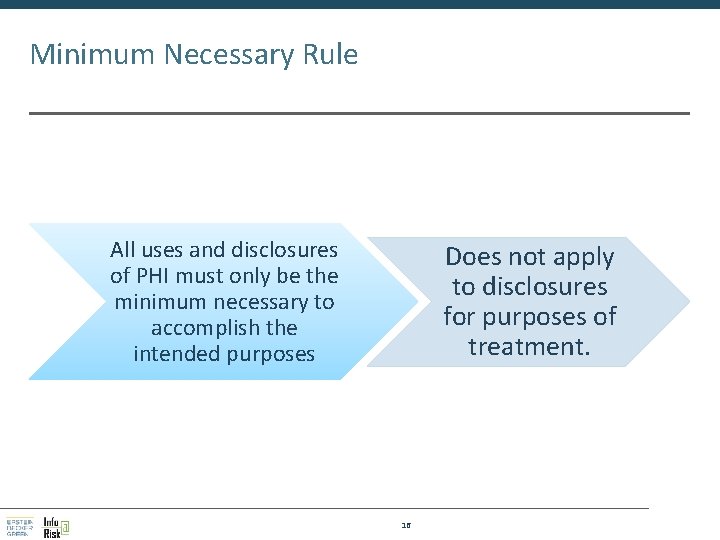
Minimum Necessary Rule All uses and disclosures of PHI must only be the minimum necessary to accomplish the intended purposes Does not apply to disclosures for purposes of treatment. 16
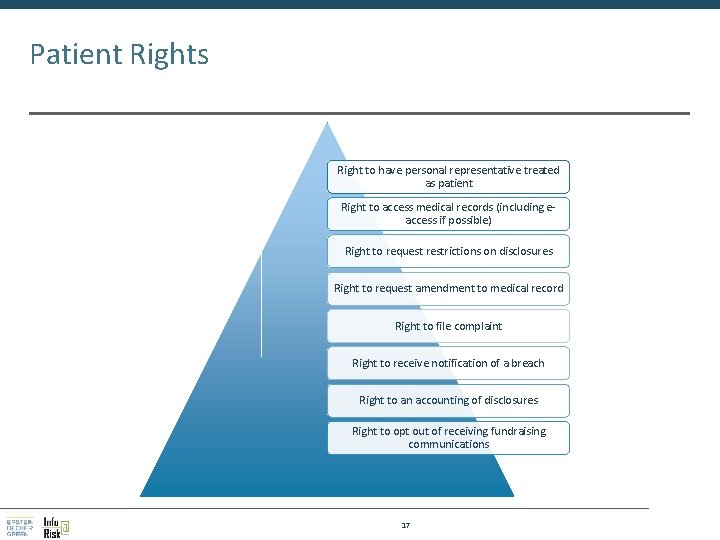
Patient Rights Right to have personal representative treated as patient Right to access medical records (including eaccess if possible) Right to request restrictions on disclosures Right to request amendment to medical record Right to file complaint Right to receive notification of a breach Right to an accounting of disclosures Right to opt out of receiving fundraising communications 17

Security Rule 18
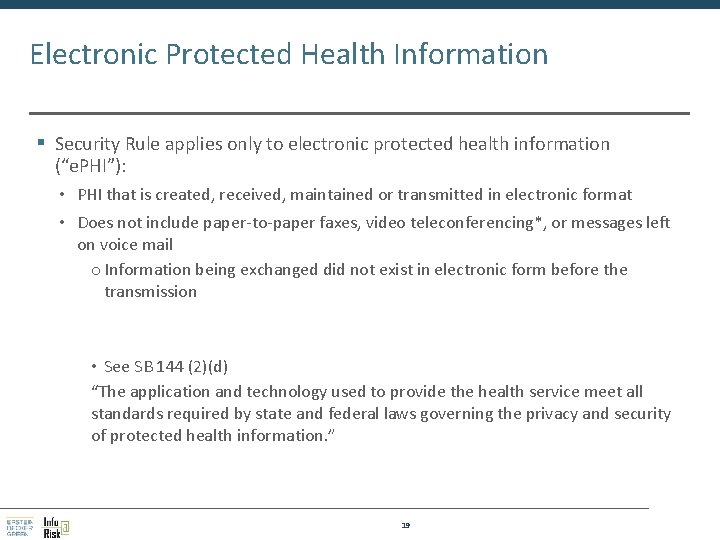
Electronic Protected Health Information § Security Rule applies only to electronic protected health information (“e. PHI”): • PHI that is created, received, maintained or transmitted in electronic format • Does not include paper-to-paper faxes, video teleconferencing*, or messages left on voice mail o Information being exchanged did not exist in electronic form before the transmission • See SB 144 (2)(d) “The application and technology used to provide the health service meet all standards required by state and federal laws governing the privacy and security of protected health information. ” 19

HIPAA Security Safeguard Domains Four major information security domains must be addressed to protect an organization's sensitive information and information systems. Administrative § 164. 308, 314, 316 Physical § 164. 310 Technological § 164. 312 20 Human § 164. 308(a)(1, 3 & 5)

Major Security Rule Controls SECURITY RULE Administrative Safeguards Physical Safeguards Technical Safeguards Privacy & Security Officers Physical Access Controls Logical Access Controls Policies & Procedures Output & Media Controls Encryption Access Authorization e. PHI Destruction Password Protection Business Associates Emergency Controls Written Record of Network Configuration Disaster Recovery/ Contingency Plans Human Safeguards Risk Analysis Documentation Routine Audits Screening, Training & Sanctions Risk Management Documentation 21
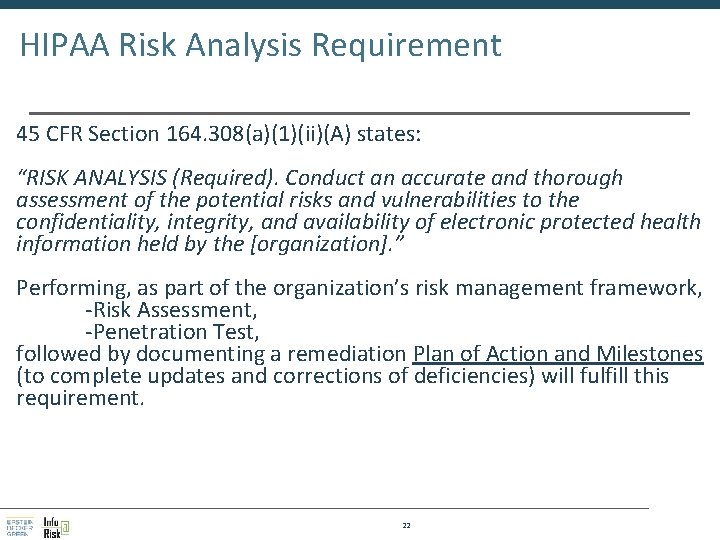
HIPAA Risk Analysis Requirement 45 CFR Section 164. 308(a)(1)(ii)(A) states: “RISK ANALYSIS (Required). Conduct an accurate and thorough assessment of the potential risks and vulnerabilities to the confidentiality, integrity, and availability of electronic protected health information held by the [organization]. ” Performing, as part of the organization’s risk management framework, -Risk Assessment, -Penetration Test, followed by documenting a remediation Plan of Action and Milestones (to complete updates and corrections of deficiencies) will fulfill this requirement. 22
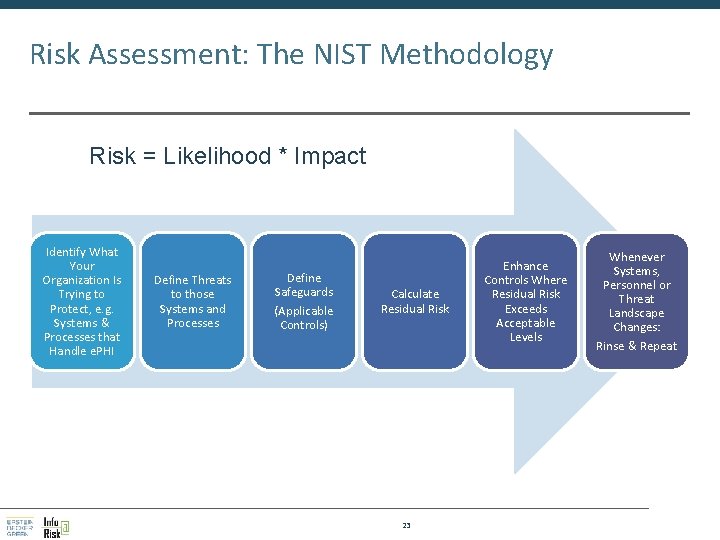
Risk Assessment: The NIST Methodology Risk = Likelihood * Impact Identify What Your Organization Is Trying to Protect, e. g. Systems & Processes that Handle e. PHI Define Threats to those Systems and Processes Define Safeguards (Applicable Controls) Calculate Residual Risk 23 Enhance Controls Where Residual Risk Exceeds Acceptable Levels Whenever Systems, Personnel or Threat Landscape Changes: Rinse & Repeat
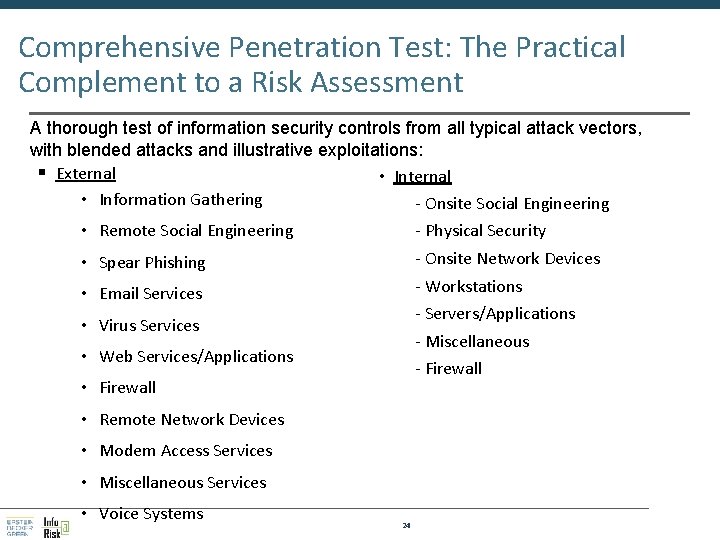
Comprehensive Penetration Test: The Practical Complement to a Risk Assessment A thorough test of information security controls from all typical attack vectors, with blended attacks and illustrative exploitations: § External • Information Gathering - Onsite Social Engineering • Remote Social Engineering - Physical Security • Spear Phishing - Onsite Network Devices • Email Services - Workstations - Servers/Applications • Virus Services - Miscellaneous • Web Services/Applications - Firewall • Firewall • Remote Network Devices • Modem Access Services • Miscellaneous Services • Voice Systems 24

Some Handy Security Safeguards Access controls to restrict access to PHI to authorized personnel only Audit controls to monitor activity on systems containing e-PHI (e. g. , electronic health record system) Integrity controls to prevent improper e-PHI alteration or destruction 25 Transmission security measures to protect e-PHI when transmitted over an electronic network
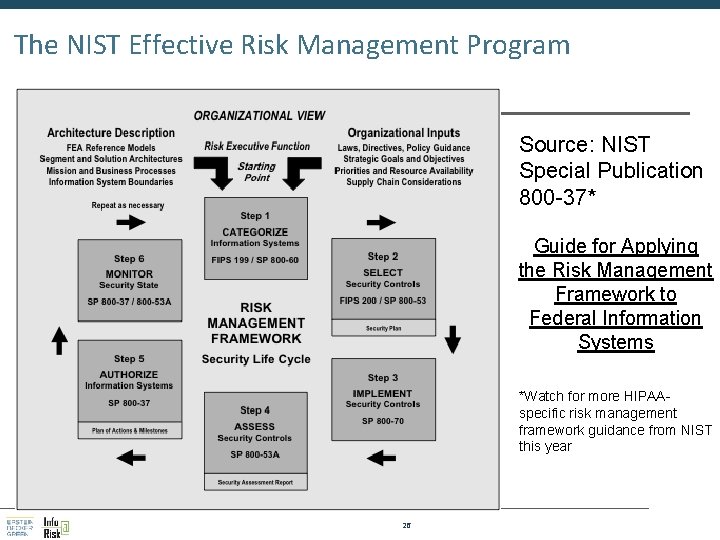
The NIST Effective Risk Management Program Source: NIST Special Publication 800 -37* Guide for Applying the Risk Management Framework to Federal Information Systems *Watch for more HIPAAspecific risk management framework guidance from NIST this year 26
Breach Reporting 27
Breach Notification Generally Covered entities and business associates must provide notification of breaches of unsecured protected health information PHI is unsecured if it is NOT • Encrypted • Destroyed 28
Breach Reporting Exceptions for inadvertent, harmless mistakes • Unintentional access by workforce member and no further impermissible use or disclosure • Inadvertent disclosure at same CE/BA/OHCA and no further impermissible use or disclosure • Recipient could not reasonably have retained the PHI 29
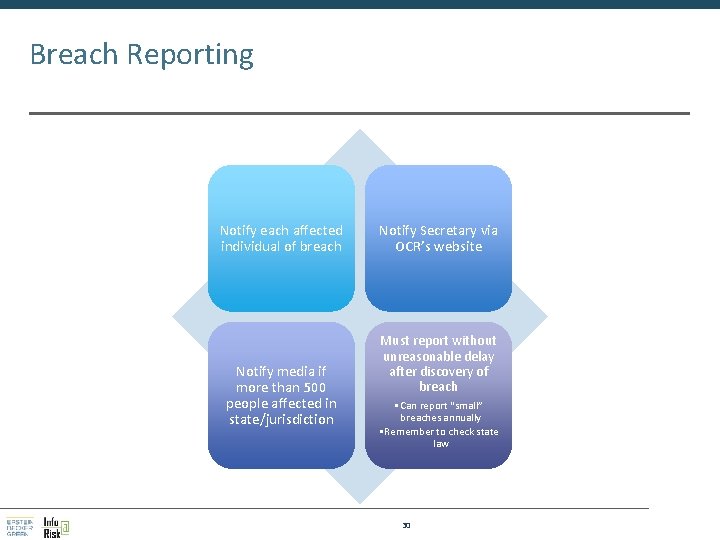
Breach Reporting Notify each affected individual of breach Notify media if more than 500 people affected in state/jurisdiction Notify Secretary via OCR’s website Must report without unreasonable delay after discovery of breach • Can report “small” breaches annually • Remember to check state law 30
Penalties & Enforcement 31
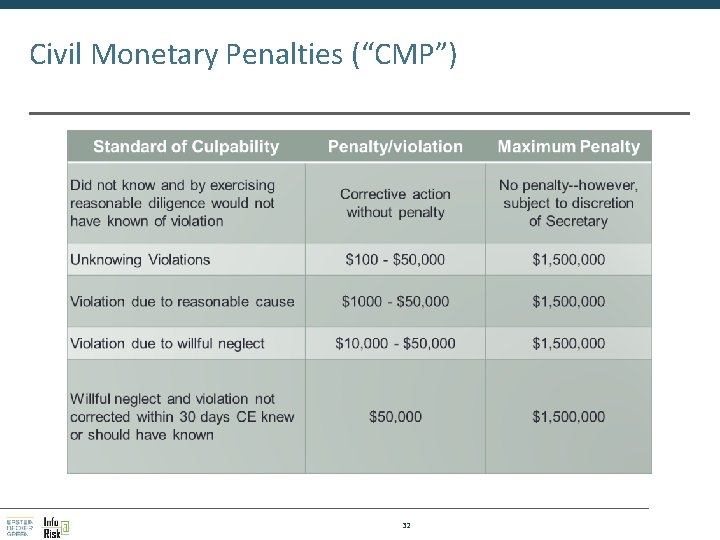
Civil Monetary Penalties (“CMP”) 32
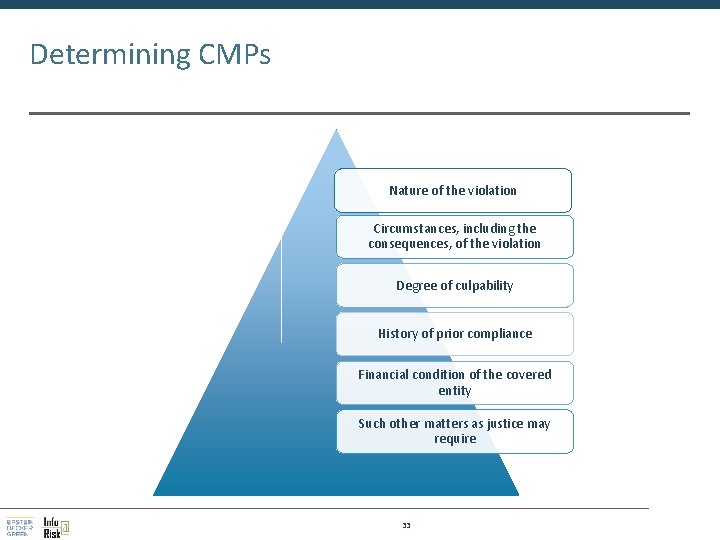
Determining CMPs Nature of the violation Circumstances, including the consequences, of the violation Degree of culpability History of prior compliance Financial condition of the covered entity Such other matters as justice may require 33
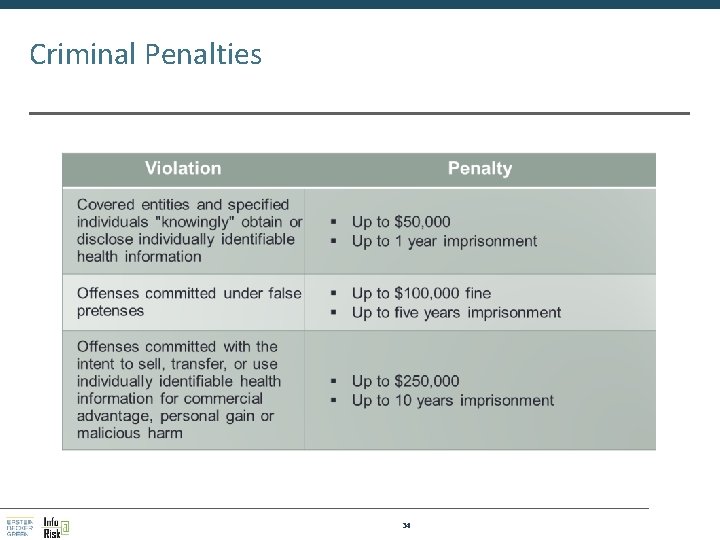
Criminal Penalties 34
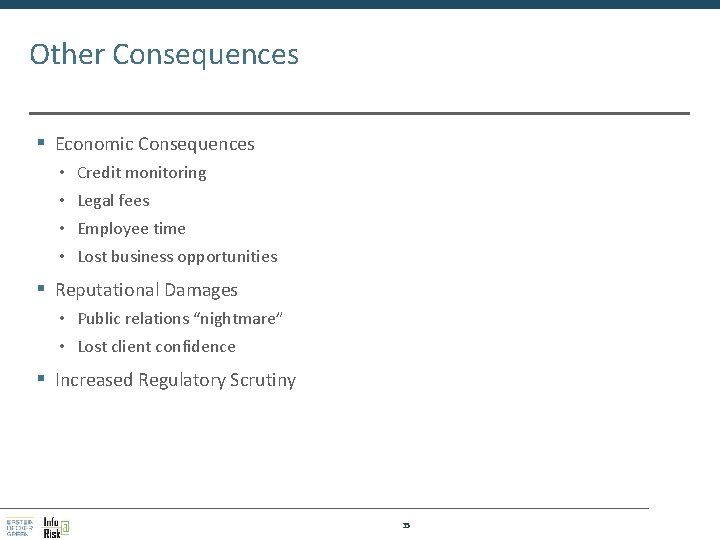
Other Consequences § Economic Consequences • Credit monitoring • Legal fees • Employee time • Lost business opportunities § Reputational Damages • Public relations “nightmare” • Lost client confidence § Increased Regulatory Scrutiny 35
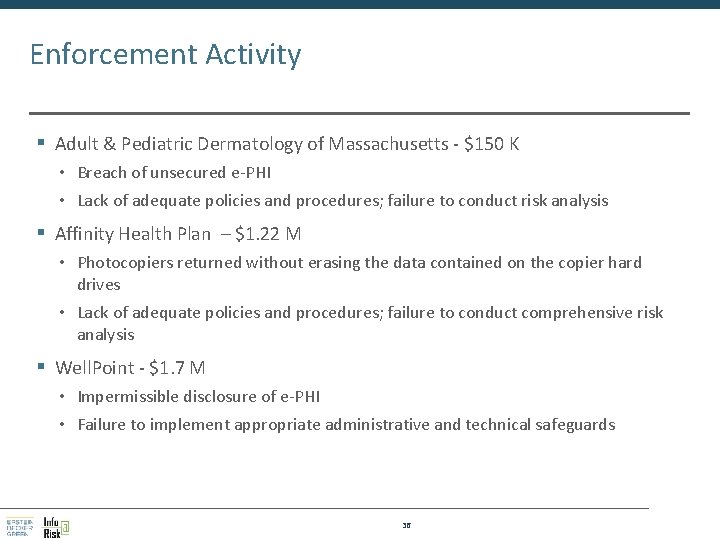
Enforcement Activity § Adult & Pediatric Dermatology of Massachusetts - $150 K • Breach of unsecured e-PHI • Lack of adequate policies and procedures; failure to conduct risk analysis § Affinity Health Plan – $1. 22 M • Photocopiers returned without erasing the data contained on the copier hard drives • Lack of adequate policies and procedures; failure to conduct comprehensive risk analysis § Well. Point - $1. 7 M • Impermissible disclosure of e-PHI • Failure to implement appropriate administrative and technical safeguards 36
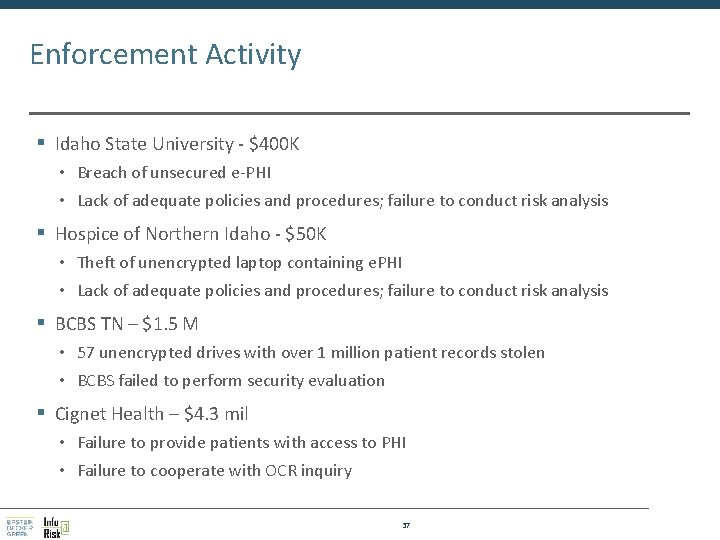
Enforcement Activity § Idaho State University - $400 K • Breach of unsecured e-PHI • Lack of adequate policies and procedures; failure to conduct risk analysis § Hospice of Northern Idaho - $50 K • Theft of unencrypted laptop containing e. PHI • Lack of adequate policies and procedures; failure to conduct risk analysis § BCBS TN – $1. 5 M • 57 unencrypted drives with over 1 million patient records stolen • BCBS failed to perform security evaluation § Cignet Health – $4. 3 mil • Failure to provide patients with access to PHI • Failure to cooperate with OCR inquiry 37
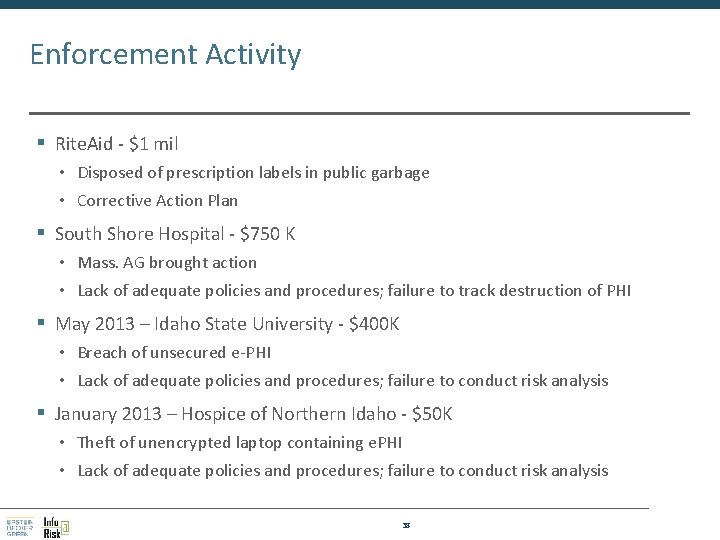
Enforcement Activity § Rite. Aid - $1 mil • Disposed of prescription labels in public garbage • Corrective Action Plan § South Shore Hospital - $750 K • Mass. AG brought action • Lack of adequate policies and procedures; failure to track destruction of PHI § May 2013 – Idaho State University - $400 K • Breach of unsecured e-PHI • Lack of adequate policies and procedures; failure to conduct risk analysis § January 2013 – Hospice of Northern Idaho - $50 K • Theft of unencrypted laptop containing e. PHI • Lack of adequate policies and procedures; failure to conduct risk analysis 38

Myths 39 39
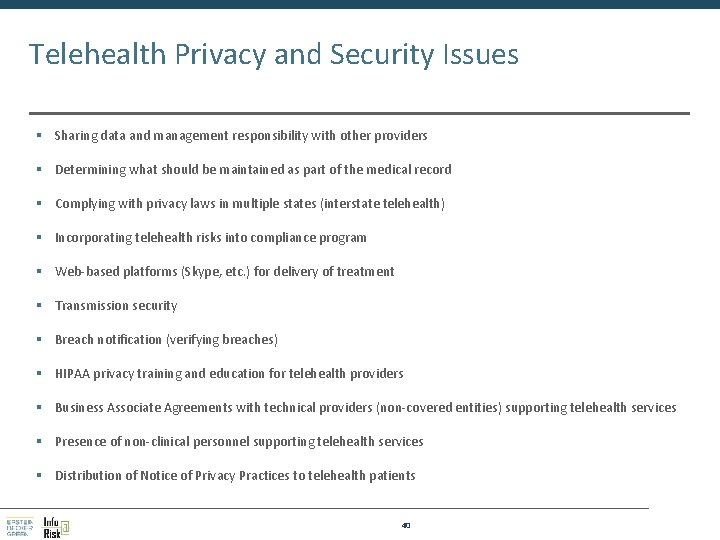
Telehealth Privacy and Security Issues § Sharing data and management responsibility with other providers § Determining what should be maintained as part of the medical record § Complying with privacy laws in multiple states (interstate telehealth) § Incorporating telehealth risks into compliance program § Web-based platforms (Skype, etc. ) for delivery of treatment § Transmission security § Breach notification (verifying breaches) § HIPAA privacy training and education for telehealth providers § Business Associate Agreements with technical providers (non-covered entities) supporting telehealth services § Presence of non-clinical personnel supporting telehealth services § Distribution of Notice of Privacy Practices to telehealth patients 40
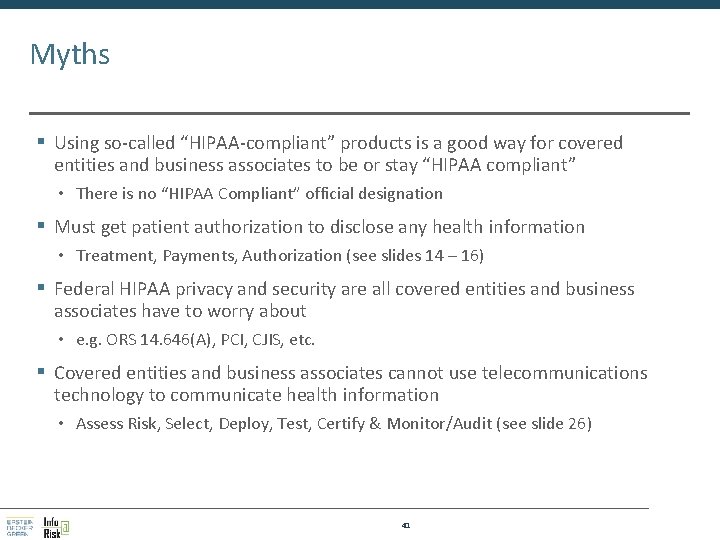
Myths § Using so-called “HIPAA-compliant” products is a good way for covered entities and business associates to be or stay “HIPAA compliant” • There is no “HIPAA Compliant” official designation § Must get patient authorization to disclose any health information • Treatment, Payments, Authorization (see slides 14 – 16) § Federal HIPAA privacy and security are all covered entities and business associates have to worry about • e. g. ORS 14. 646(A), PCI, CJIS, etc. § Covered entities and business associates cannot use telecommunications technology to communicate health information • Assess Risk, Select, Deploy, Test, Certify & Monitor/Audit (see slide 26) 41
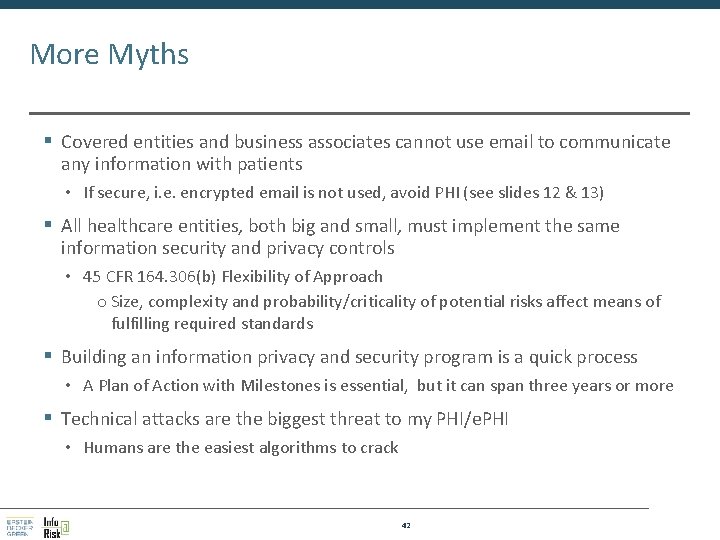
More Myths § Covered entities and business associates cannot use email to communicate any information with patients • If secure, i. e. encrypted email is not used, avoid PHI (see slides 12 & 13) § All healthcare entities, both big and small, must implement the same information security and privacy controls • 45 CFR 164. 306(b) Flexibility of Approach o Size, complexity and probability/criticality of potential risks affect means of fulfilling required standards § Building an information privacy and security program is a quick process • A Plan of Action with Milestones is essential, but it can span three years or more § Technical attacks are the biggest threat to my PHI/e. PHI • Humans are the easiest algorithms to crack 42
- Slides: 42