Dealing with Privacy Obligations in Enterprises Marco Casassa
Dealing with Privacy Obligations in Enterprises Marco Casassa Mont marco. casassa-mont@hp. com Trusted Systems Lab Hewlett-Packard Labs, Bristol, UK 28 -30 September 2004 ISSE 2004 Berlin, Germany © 2004 Hewlett-Packard Development Company, L. P. The information contained herein is subject to change without notice
Presentation Outline • Setting the Context: Privacy and Privacy Obligations • Analysis of Privacy Obligations, Issues and Requirements • Privacy Obligations: Related Work • Privacy Obligations: Our Work • Discussion and Next Steps • Conclusions 11/26/2020 2
Our Approach • Focus on Privacy Obligations for Personal Data in Enterprises • Explore the problem from a technical angle: how to Model, Manage, Enforce and Monitor Privacy Obligations • Recognise it is not only a matter of technology but also involves laws, legislation, processes and human intervention. Nevertheless Automation can help. 11/26/2020 3
Setting the Context: Privacy and Privacy Obligations 11/26/2020 4
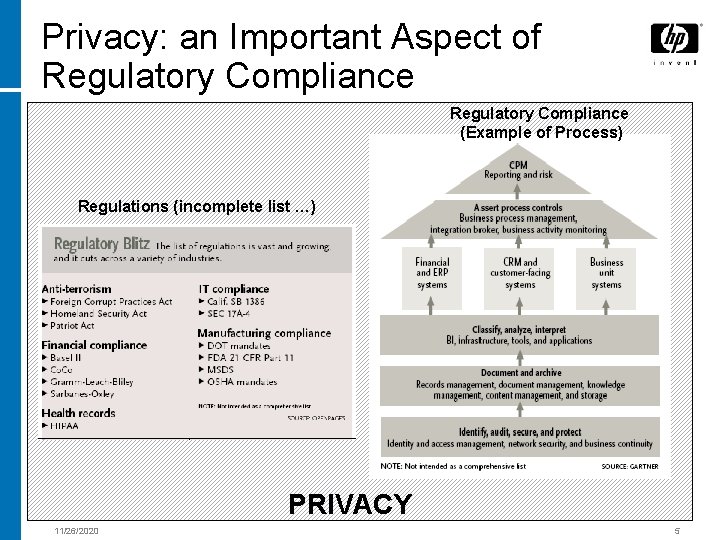
Privacy: an Important Aspect of Regulatory Compliance (Example of Process) Regulations (incomplete list …) PRIVACY 11/26/2020 5
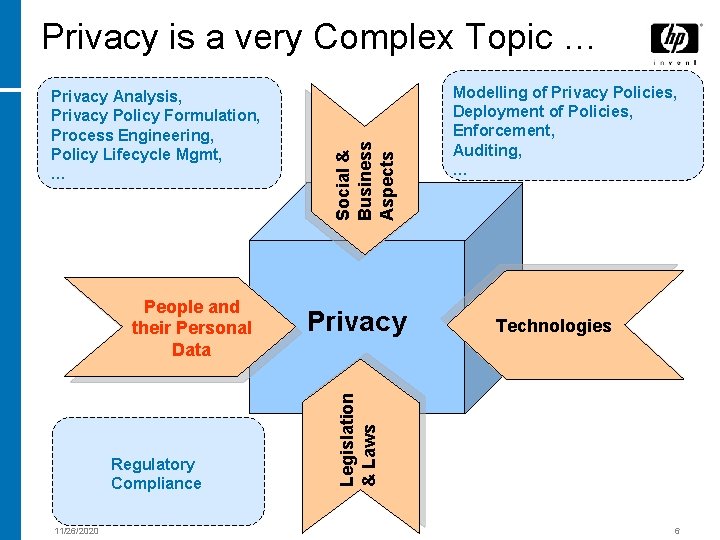
People and their Personal Data Regulatory Compliance 11/26/2020 Privacy Modelling of Privacy Policies, Deployment of Policies, Enforcement, Auditing, … Technologies Legislation & Laws Privacy Analysis, Privacy Policy Formulation, Process Engineering, Policy Lifecycle Mgmt, … Social & Business Aspects Privacy is a very Complex Topic … 6
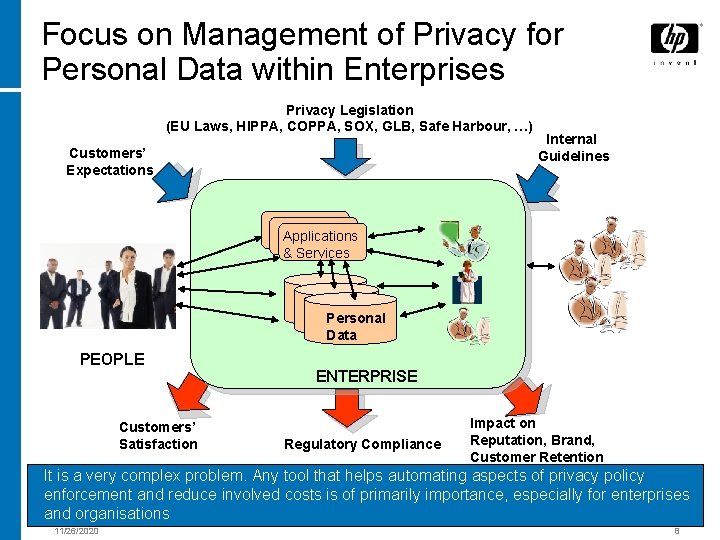
Focus on Management of Privacy for Personal Data within Enterprises Privacy Legislation (EU Laws, HIPPA, COPPA, SOX, GLB, Safe Harbour, …) Customers’ Expectations Internal Guidelines Applications & Services Personal Data PEOPLE Customers’ Satisfaction ENTERPRISE Regulatory Compliance Impact on Reputation, Brand, Customer Retention It is a very complex problem. Any tool that helps automating aspects of privacy policy enforcement and reduce involved costs is of primarily importance, especially for enterprises and organisations 11/26/2020 8
Privacy and Personal Data: Importance of Privacy Laws, Legislation and Guidelines • OECD Privacy Guidelines and Policies • EU Legislation • Various US Laws and Legislations: - HIPPA - COPPA - GLB, etc. • Safe Harbour Policies • Various Local and National Data Protection Initiatives: http: //www. privacyinternational. org/survey/phr 2003/ • Organisations and Enterprise Privacy Guidelines/Policies • … 11/26/2020 9
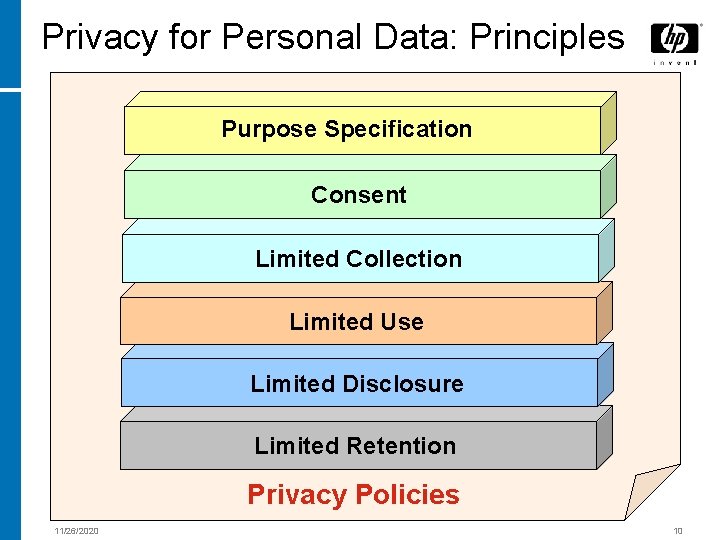
Privacy for Personal Data: Principles Purpose Specification Consent Limited Collection Limited Use Limited Disclosure Limited Retention Privacy Policies 11/26/2020 10
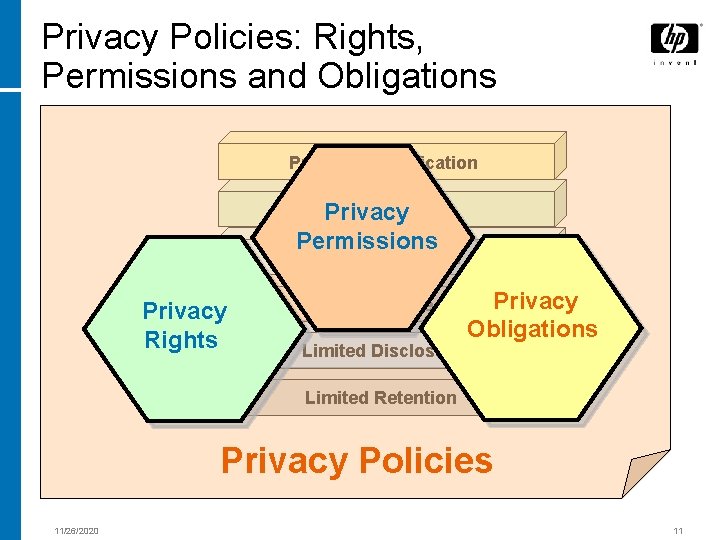
Privacy Policies: Rights, Permissions and Obligations Purpose Specification Consent Privacy Permissions Limited Collection Privacy Rights Limited Use Limited Disclosure Privacy Obligations Limited Retention Privacy Policies 11/26/2020 11
Focus on Privacy Obligations: Why? • Lot of technical work has already been done in the space of Privacy Rights and Permissions. More details will be presented in the Related Work Section … • The overall Management of Privacy Obligations from a technical perspective, as first-class citizens, is still a green field and open to research. • Privacy Obligations are a key aspect of regulatory compliance. 11/26/2020 12
Analysis of Privacy Obligations 11/26/2020 13
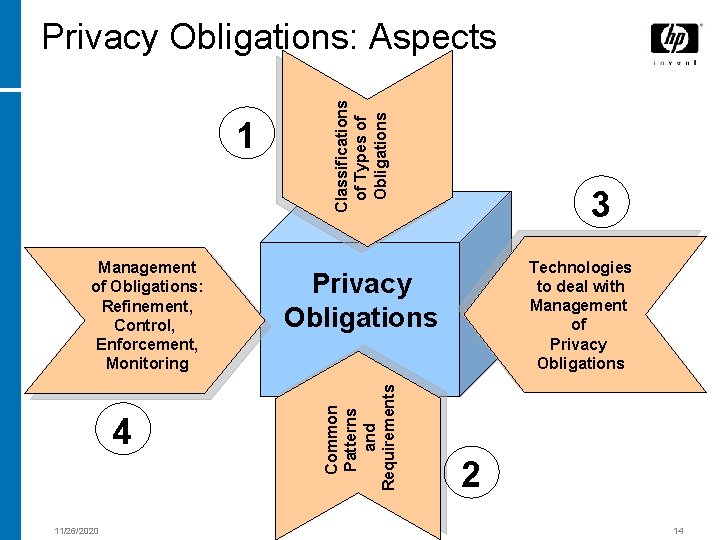
Management of Obligations: Refinement, Control, Enforcement, Monitoring 4 11/26/2020 3 Technologies to deal with Management of Privacy Obligations Common Patterns and Requirements 1 Classifications of Types of Obligations Privacy Obligations: Aspects 2 14
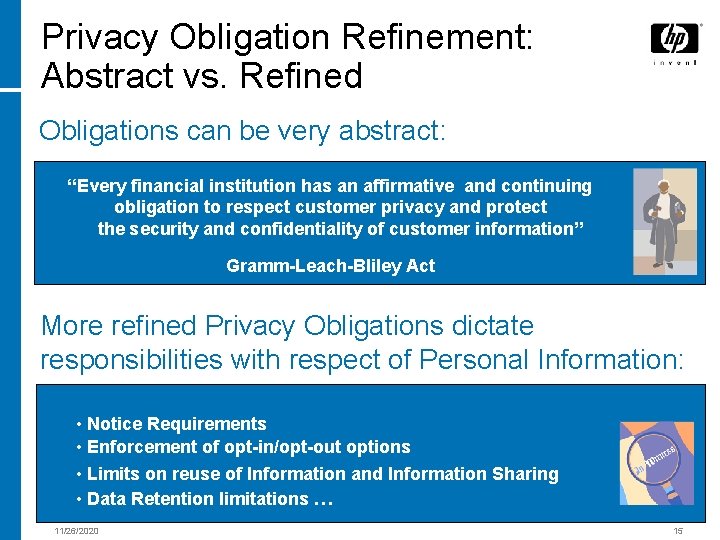
Privacy Obligation Refinement: Abstract vs. Refined Obligations can be very abstract: “Every financial institution has an affirmative and continuing obligation to respect customer privacy and protect the security and confidentiality of customer information” Gramm-Leach-Bliley Act More refined Privacy Obligations dictate responsibilities with respect of Personal Information: • Notice Requirements • Enforcement of opt-in/opt-out options • Limits on reuse of Information and Information Sharing • Data Retention limitations … 11/26/2020 15
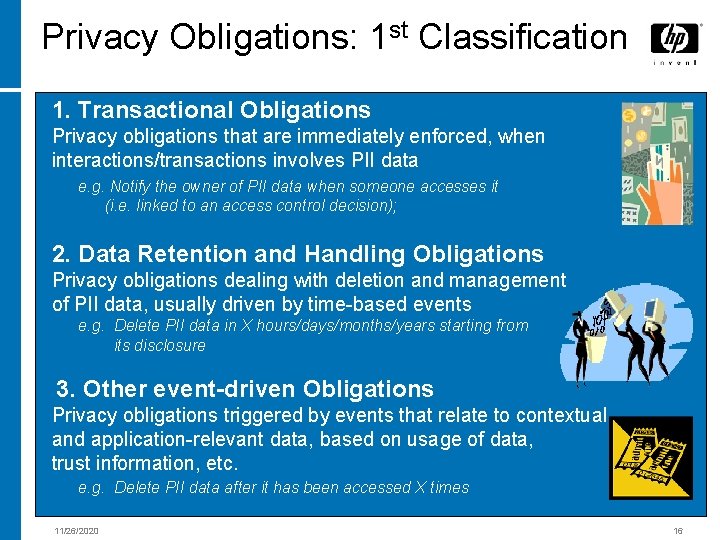
Privacy Obligations: 1 st Classification 1. Transactional Obligations Privacy obligations that are immediately enforced, when interactions/transactions involves PII data e. g. Notify the owner of PII data when someone accesses it (i. e. linked to an access control decision); 2. Data Retention and Handling Obligations Privacy obligations dealing with deletion and management of PII data, usually driven by time-based events e. g. Delete PII data in X hours/days/months/years starting from its disclosure 3. Other event-driven Obligations Privacy obligations triggered by events that relate to contextual and application-relevant data, based on usage of data, trust information, etc. e. g. Delete PII data after it has been accessed X times 11/26/2020 16
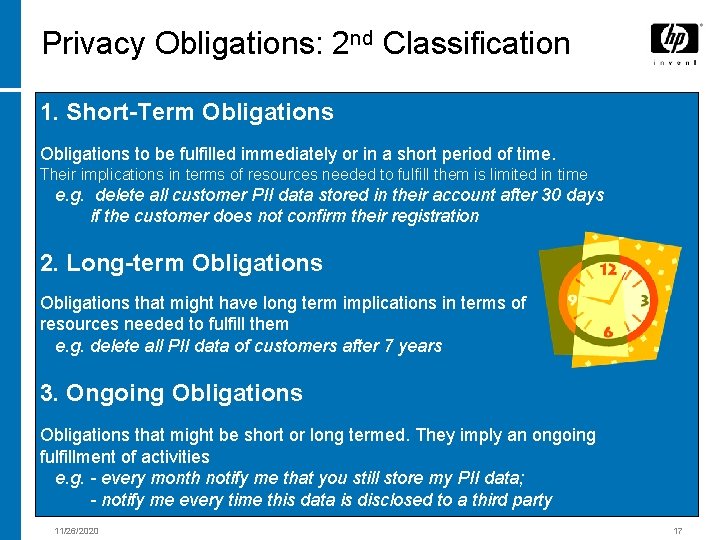
Privacy Obligations: 2 nd Classification 1. Short-Term Obligations to be fulfilled immediately or in a short period of time. Their implications in terms of resources needed to fulfill them is limited in time e. g. delete all customer PII data stored in their account after 30 days if the customer does not confirm their registration 2. Long-term Obligations that might have long term implications in terms of resources needed to fulfill them e. g. delete all PII data of customers after 7 years 3. Ongoing Obligations that might be short or long termed. They imply an ongoing fulfillment of activities e. g. - every month notify me that you still store my PII data; - notify me every time this data is disclosed to a third party 11/26/2020 17
Privacy Obligations and Access Control Obligations Contextual to Access Control These obligations include most of the transactional obligations and obligations that can be fulfilled after an authorization decision e. g. - notify me when you access my PII data; - delete my data after accessing it; - check for the trustworthiness of your platform when you access PII data; - log your access and intent in this third party audit server Obligations Unrelated to Access Control These obligations are unrelated to access control decisions. Part of data retention obligations, long-term obligations and ongoing obligations belong to this category e. g. - delete customers’ PII data after 7 years it has been stored – independently by the fact it is accessed - notify me every month if you still have PII data of mine 11/26/2020 18
Who is Setting Privacy Obligations? Obligations can be set by PII Data Subjects or Third Parties on their behalf People usually set privacy obligations that are related to the “visible” and operational aspects of their PII data. They usually dictate constraints on the usage of PII data, required interactions and actions (notifications, deletions, etc. ), opt-in/opt-out choices; Obligations can be set by Enterprises or imposed by Legislation Organisations need to support privacy obligations dictated by legislation, laws and internal guidelines. These privacy obligations can be seen as “default” obligations that users are entitled to. 11/26/2020 19
Privacy Obligations: Common Aspects and Requirements 11/26/2020 20
Privacy Obligations: Common Aspects • Timeframe (period of validity) of obligations • Events/Contexts that trigger the need to fulfil obligations • Target of an obligation (PII data) • Actions/Tasks to be Enforced • Entities responsible for enforcing obligations • Exceptions and special cases 11/26/2020 21
![Dealing with Privacy Obligations: Important Issues and Requirements [1/2] • Modelling/Representation of Privacy Obligations Dealing with Privacy Obligations: Important Issues and Requirements [1/2] • Modelling/Representation of Privacy Obligations](http://slidetodoc.com/presentation_image_h/a7200442183907603d8f693140f54aea/image-21.jpg)
Dealing with Privacy Obligations: Important Issues and Requirements [1/2] • Modelling/Representation of Privacy Obligations • Association of Obligations to Data • Mapping Obligations into Enforceable Actions • Compliance of Refined Policies to high-level Policies • Tracking the evolution of Obligation Policies 11/26/2020 22
![Privacy Obligations: Important Issues and Requirements [2/2] • Dealing with long-term Obligation Aspects • Privacy Obligations: Important Issues and Requirements [2/2] • Dealing with long-term Obligation Aspects •](http://slidetodoc.com/presentation_image_h/a7200442183907603d8f693140f54aea/image-22.jpg)
Privacy Obligations: Important Issues and Requirements [2/2] • Dealing with long-term Obligation Aspects • Accountability Management • User Involvement • Complexity and Cost of Instrumenting Applications and Services 11/26/2020 23
Privacy Obligations: Related Work 11/26/2020 24
![Technical Work in this Space [1/2] Technical advancements have been made to deal with Technical Work in this Space [1/2] Technical advancements have been made to deal with](http://slidetodoc.com/presentation_image_h/a7200442183907603d8f693140f54aea/image-24.jpg)
Technical Work in this Space [1/2] Technical advancements have been made to deal with Privacy Rights, Permissions and Obligations: - Extended access control and authorization mechanisms built to check and enforce privacy permissions against users’ rights, data purpose, intents … - Approaches to deal with privacy obligations available for data retention solutions and document management systems. They are very focused and limited in terms of obligation expressiveness and system functionalities. 11/26/2020 25
![Technical Work in this Space [2/2] Recent important work done in this space: - Technical Work in this Space [2/2] Recent important work done in this space: -](http://slidetodoc.com/presentation_image_h/a7200442183907603d8f693140f54aea/image-25.jpg)
Technical Work in this Space [2/2] Recent important work done in this space: - IBM Enterprise Privacy Architecture, including a policy management system, a privacy enforcement system and audit - Initial work on privacy obligations in the context of Enterprise Privacy Authorization Language (EPAL) lead by IBM 11/26/2020 26
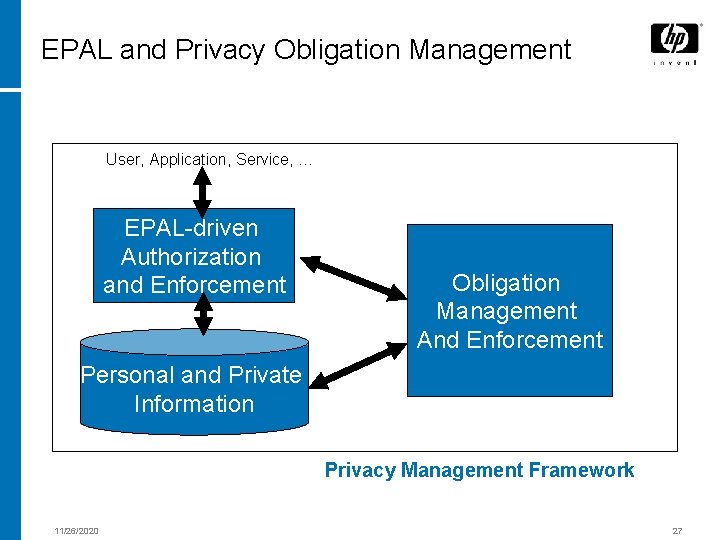
EPAL and Privacy Obligation Management User, Application, Service, … EPAL-driven Authorization and Enforcement Obligation Management And Enforcement Personal and Private Information Privacy Management Framework 11/26/2020 27
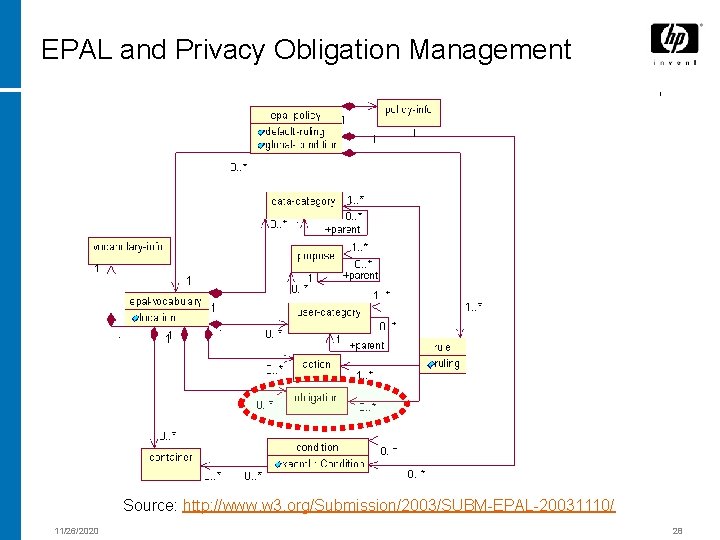
EPAL and Privacy Obligation Management Source: http: //www. w 3. org/Submission/2003/SUBM-EPAL-20031110/ 11/26/2020 28
EPAL and Privacy Obligation Management EPAL main limitations when dealing with privacy obligations: • EPAL (and related privacy architecture) is focuses on an authorization and access control perspective of privacy • EPAL does not model or describe obligations: it provides place-holders for them • Privacy obligations are considered as “second-class” citizens, as they are only considered in an authorization context … 11/26/2020 29
Privacy Obligations: Our Technical Work 11/26/2020 30
Privacy Obligations: Our Approach to Address the Problems • Deal with Privacy Obligations as “first-class citizens” in the context of Enterprises and Organisations – recognise its importance for Regulatory Compliance • Recognise the importance of separation of concerns: explore how to explicitly represent, manage and enforce privacy obligations without imposing any dominant view (for example, the authorization perspective) • Research and work on longer-term issues, such as accountability, stronger associations of obligations to data, obligation versioning and tracking 11/26/2020 31
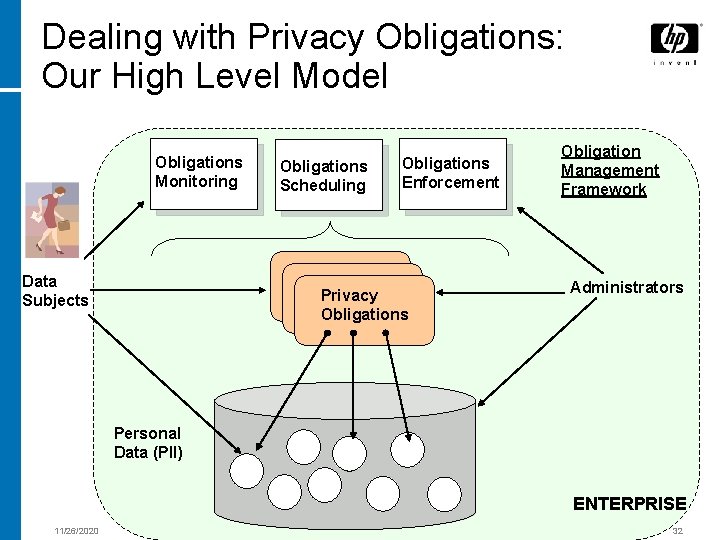
Dealing with Privacy Obligations: Our High Level Model Obligations Monitoring Data Subjects Obligations Scheduling Obligations Enforcement Privacy Obligations Obligation Management Framework Administrators Personal Data (PII) ENTERPRISE 11/26/2020 32
![Privacy Obligations: Our Technical Work and Research on Privacy Obligations: [1] Modelling and Representation Privacy Obligations: Our Technical Work and Research on Privacy Obligations: [1] Modelling and Representation](http://slidetodoc.com/presentation_image_h/a7200442183907603d8f693140f54aea/image-32.jpg)
Privacy Obligations: Our Technical Work and Research on Privacy Obligations: [1] Modelling and Representation of Obligations [2] An Obligation Management System (OMS) for Management, Enforcement and Monitoring of Obligations [3] Accountability and Strong Association of Obligations to Personal Data [4] Prototype 11/26/2020 33
![[1] Privacy Obligations: Modelling and Representation Privacy Obligation Identifier References to stored PII data [1] Privacy Obligations: Modelling and Representation Privacy Obligation Identifier References to stored PII data](http://slidetodoc.com/presentation_image_h/a7200442183907603d8f693140f54aea/image-33.jpg)
[1] Privacy Obligations: Modelling and Representation Privacy Obligation Identifier References to stored PII data Targeted Personal Data e. g. Database query, LDAP reference, etc. Triggering Events Actions Additional Metadata (Future Extensions) 11/26/2020 One or more Events that trigger different Actions potentially involving changes to PII data e. g. Event: Time-based events Actions: Delete PII, Notify 34
![[1] Privacy Obligations: Format Example <obligation id=“gfrbg 7645 gt 45"> 11/26/2020 <target> <database> <dbname>Customers</dbname> [1] Privacy Obligations: Format Example <obligation id=“gfrbg 7645 gt 45"> 11/26/2020 <target> <database> <dbname>Customers</dbname>](http://slidetodoc.com/presentation_image_h/a7200442183907603d8f693140f54aea/image-34.jpg)
[1] Privacy Obligations: Format Example <obligation id=“gfrbg 7645 gt 45"> 11/26/2020 <target> <database> <dbname>Customers</dbname> <tname>Customers</tname> <locator> <key name=“User. ID">oid_a 83 b 8 a: fdfc 44 df 3 b: -7 f 9 c</key> </locator> <data attr="part"> <item>creditcard</item> <item>firstname</item> </database> </target> <obligationitem sid="1"> <metadata> <type>LONGTERM</type> <description>Delete [firstname, surname] at Sat Aug 15 17: 26: 21 BST 2004. ]</description> </metadata> <events> <event> <type>TIMEOUT</type> <date now="no"> <year>2004</year> <month>08</month> <day>14</day> <hour>17</hour><minute>26</minute> </events> <action> <type>DELETE</type> <data attr="part"> <item>creditcard</item> <item>firstname</item> </data> </actions> </obligationitem> </obligation> 35
![[2] Our Privacy Obligations Management System (OMS) • Explicit Management of Privacy Obligations within [2] Our Privacy Obligations Management System (OMS) • Explicit Management of Privacy Obligations within](http://slidetodoc.com/presentation_image_h/a7200442183907603d8f693140f54aea/image-35.jpg)
[2] Our Privacy Obligations Management System (OMS) • Explicit Management of Privacy Obligations within Enterprises • Core Functionalities: q Processing q Scheduling q Enforcing q Monitoring of Privacy Obligations 11/26/2020 36
![[2] OMS as part of an Identity Management System Obligation Management System 11/26/2020 Model [2] OMS as part of an Identity Management System Obligation Management System 11/26/2020 Model](http://slidetodoc.com/presentation_image_h/a7200442183907603d8f693140f54aea/image-36.jpg)
[2] OMS as part of an Identity Management System Obligation Management System 11/26/2020 Model of Identity Management Systems 37
![[2] OMS: High Level System Architecture Applications and Services Admins Privacy-enabled Portal Obligation Monitoring [2] OMS: High Level System Architecture Applications and Services Admins Privacy-enabled Portal Obligation Monitoring](http://slidetodoc.com/presentation_image_h/a7200442183907603d8f693140f54aea/image-37.jpg)
[2] OMS: High Level System Architecture Applications and Services Admins Privacy-enabled Portal Obligation Monitoring Service ENTERPRISE Admins 11/26/2020 Monitoring Task Handler Obligation Server Obligation Scheduler Workflows Obligation Enforcer Action Adaptors Audit Server Data Ref. Obligation Store & Versioning Events Handler Information Tracker Data Subjects Confidential Data 38
![[2] OMS: High Level System Architecture Data Subjects ENTERPRISE Admins 11/26/2020 Applications and Services [2] OMS: High Level System Architecture Data Subjects ENTERPRISE Admins 11/26/2020 Applications and Services](http://slidetodoc.com/presentation_image_h/a7200442183907603d8f693140f54aea/image-38.jpg)
[2] OMS: High Level System Architecture Data Subjects ENTERPRISE Admins 11/26/2020 Applications and Services Privacy-enabled Portal Setting Privacy Obligations On Personal Data Obligation Server Obligation Scheduler Audit Server Data Ref. Obligation Store & Versioning Confidential Data 39
![[2] OMS: High Level System Architecture Data Subjects Enforcing Privacy Obligations Applications and Services [2] OMS: High Level System Architecture Data Subjects Enforcing Privacy Obligations Applications and Services](http://slidetodoc.com/presentation_image_h/a7200442183907603d8f693140f54aea/image-39.jpg)
[2] OMS: High Level System Architecture Data Subjects Enforcing Privacy Obligations Applications and Services Admins Events Handler 11/26/2020 Obligation Scheduler Obligation Workflows Obligation Enforcer Action Adaptors Audit Server Data Ref. Obligation Store & Versioning Information Tracker ENTERPRISE Admins Confidential Data 40
![[2] OMS: High Level System Architecture Applications and Services Data Subjects Admins 11/26/2020 Obligation [2] OMS: High Level System Architecture Applications and Services Data Subjects Admins 11/26/2020 Obligation](http://slidetodoc.com/presentation_image_h/a7200442183907603d8f693140f54aea/image-40.jpg)
[2] OMS: High Level System Architecture Applications and Services Data Subjects Admins 11/26/2020 Obligation Monitoring Service Monitoring Task Handler Workflows Obligation Enforcer Action Adaptors Obligation Audit Server Data Ref. Obligation Store & Versioning Events Handler Information Tracker ENTERPRISE Monitoring Privacy Obligations Confidential Data 41
![[3] OMS: Towards Strong Association of Obligations to Data and Accountability Applications and Services [3] OMS: Towards Strong Association of Obligations to Data and Accountability Applications and Services](http://slidetodoc.com/presentation_image_h/a7200442183907603d8f693140f54aea/image-41.jpg)
[3] OMS: Towards Strong Association of Obligations to Data and Accountability Applications and Services Subjects Admins Privacy-enabled Portal ENTERPRISE Admins Obligation Server Key Mgmt Service Obligation Data Ref. Obligation Store & Versioning Monitoring Task Handler Obligation Scheduler Workflows Obligation Enforcer Action Adaptors Events Handler Information Tracker Obligation Monitoring Service Audit Server encrypted data+ sticky obligation Confidential Data Encryption + Sticky Policies: based on IBE crypto or traditional RSA crypto 11/26/2020 42
![[4] OMS Prototype: Core System Components 11/26/2020 43 [4] OMS Prototype: Core System Components 11/26/2020 43](http://slidetodoc.com/presentation_image_h/a7200442183907603d8f693140f54aea/image-42.jpg)
[4] OMS Prototype: Core System Components 11/26/2020 43
![Discussion [1/2] • Our system is an initial step towards the explicit management, enforcement Discussion [1/2] • Our system is an initial step towards the explicit management, enforcement](http://slidetodoc.com/presentation_image_h/a7200442183907603d8f693140f54aea/image-43.jpg)
Discussion [1/2] • Our system is an initial step towards the explicit management, enforcement and monitoring of privacy obligations: plenty of space for refinements and improvements • We assume that the enterprise is willing to be compliant to privacy obligations. Additional assurance and accountability can be added by hardening the audit server and involving trusted third parties 11/26/2020 44
![Discussion [2/2] • We introduced and discussed a centralised OMS system: potential for bottlenecks. Discussion [2/2] • We introduced and discussed a centralised OMS system: potential for bottlenecks.](http://slidetodoc.com/presentation_image_h/a7200442183907603d8f693140f54aea/image-44.jpg)
Discussion [2/2] • We introduced and discussed a centralised OMS system: potential for bottlenecks. Exploring how to distribute it … • Security is required to control the access to obligations and PII data by Administrators and Users • We did not discuss the implications of long-terms obligation management in terms of requirements for reliability, survivability and longevity of the platforms running our system. Related work can be leveraged in this space 11/26/2020 45
Next Steps • Refinement of our concepts, OMS architecture and further research • Addressing open issues such as obligation life-cycle management, overall efficiency, stickiness of privacy obligations to PII data • Further research to be done in the context of the EU PRIME project 11/26/2020 46
Conclusions • Privacy obligations are a key aspect of privacy. They are “first-class” citizens: need to be explicitly managed • The management of privacy obligations is important for enterprises and organisations as part of the overall Regulatory Compliance • We introduced our research and technical work in the privacy obligation management space. Described an Obligation Management System (OMS) to schedule, enforce and monitor privacy obligations • Open issues: OMS efficiency, scalability, strong association of privacy obligations to data • Our research and work are in progress. Part of this work will be done in the context of the EU PRIME project 11/26/2020 47
BACK-UP SLIDES 11/26/2020 48
Some Privacy Definitions … • “The quality of being secluded from the presence or view of others” • “The right of an individual to be secure from unauthorized disclosure of information about oneself that is contained in documents and digital data” • “Ensuring that individuals maintain the right to control what information is collected about them and how it is used as well” • “For citizens and consumers, freedom from unauthorized intrusion. For organizations, privacy involves the policies that determine what information is gathered, how it is used, and how customers are informed and involved in this process. Privacy is a legal issue, but it is also an information security issue” • … 11/26/2020 49
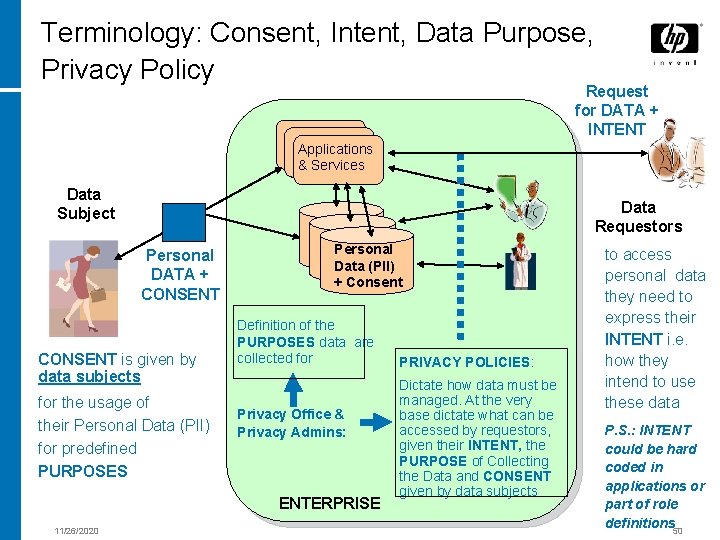
Terminology: Consent, Intent, Data Purpose, Privacy Policy Request for DATA + INTENT Applications & Services Data Subject Data Requestors Personal DATA + CONSENT is given by data subjects for the usage of their Personal Data (PII) for predefined PURPOSES Personal Data (PII) + Consent Definition of the PURPOSES data are collected for Privacy Office & Privacy Admins: ENTERPRISE 11/26/2020 PRIVACY POLICIES: Dictate how data must be managed. At the very base dictate what can be accessed by requestors, given their INTENT, the PURPOSE of Collecting the Data and CONSENT given by data subjects to access personal data they need to express their INTENT i. e. how they intend to use these data P. S. : INTENT could be hard coded in applications or part of role definitions 50
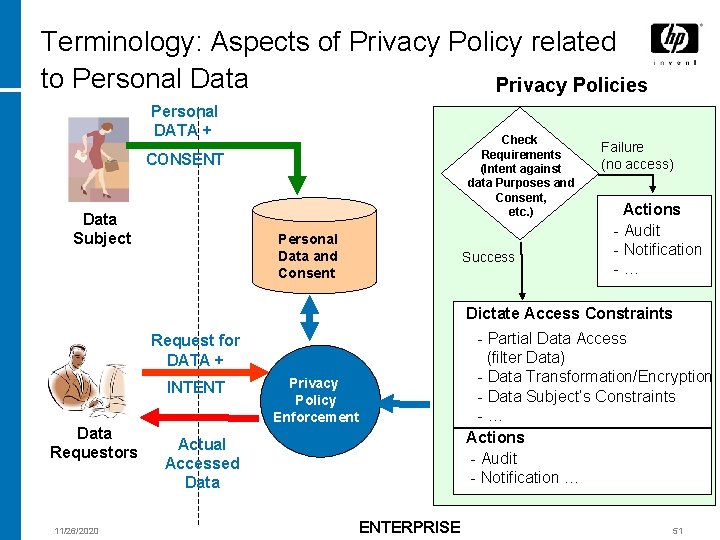
Terminology: Aspects of Privacy Policy related to Personal Data Privacy Policies Personal DATA + Check Requirements (Intent against data Purposes and Consent, etc. ) CONSENT Data Subject Personal Data and Consent Success Failure (no access) Actions - Audit - Notification -… Dictate Access Constraints - Partial Data Access (filter Data) - Data Transformation/Encryption - Data Subject’s Constraints -… Actions - Audit - Notification … Request for DATA + INTENT Data Requestors 11/26/2020 Privacy Policy Enforcement Actual Accessed Data ENTERPRISE 51
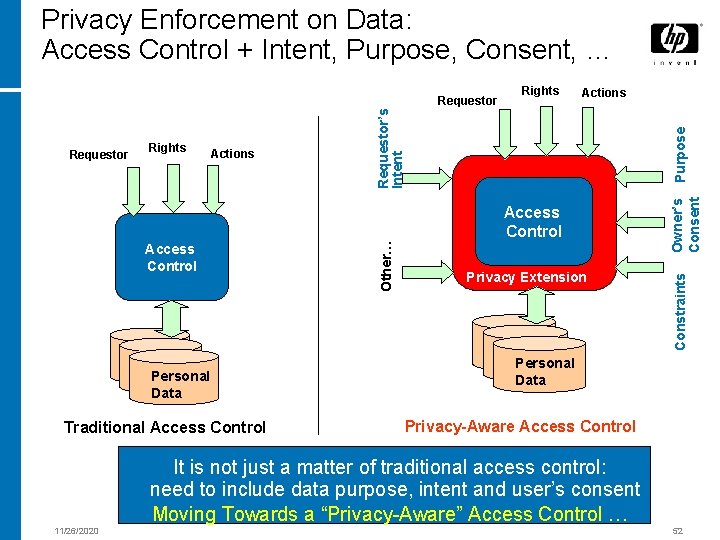
Privacy Enforcement on Data: Access Control + Intent, Purpose, Consent, … Purpose Actions Access Control Personal Data Traditional Access Control 11/26/2020 Other… Access Control Privacy Extension Owner’s Consent Rights Actions Constraints Requestor Rights Requestor’s Intent Requestor Personal Data Privacy-Aware Access Control It is not just a matter of traditional access control: need to include data purpose, intent and user’s consent Moving Towards a “Privacy-Aware” Access Control … 52
Enterprises: Regulatory Compliance and Enforcement of Privacy Policies • It is a very complex problem • The full enforcement of privacy rights, permissions and obligations cannot usually be achieved only via technical solutions • Processes, best practices and good behaviours are important However, being able to automate aspects of privacy policy enforcement and reduce involved costs is of primarily importance, especially for enterprises and organisations 11/26/2020 53
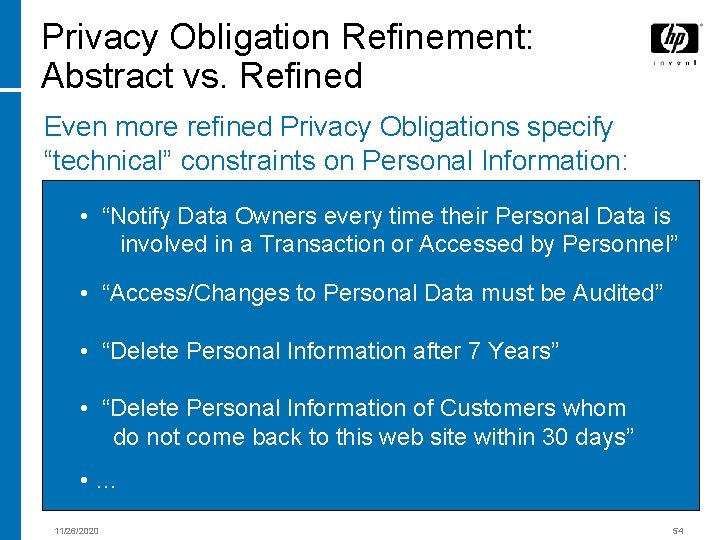
Privacy Obligation Refinement: Abstract vs. Refined Even more refined Privacy Obligations specify “technical” constraints on Personal Information: • “Notify Data Owners every time their Personal Data is involved in a Transaction or Accessed by Personnel” • “Access/Changes to Personal Data must be Audited” • “Delete Personal Information after 7 Years” • “Delete Personal Information of Customers whom do not come back to this web site within 30 days” • … 11/26/2020 54
Privacy Policies: Rights, Permissions and Obligations Example Privacy Policies in e-commerce web sites: • describe rights of users about their personal information • describe permissions given to the involved parties • describe obligations the involved parties are subject to Privacy Practices can be checked by consumers to: • decide if these practices are acceptable • decide what to opt-in and opt-out • who to do business with 11/26/2020 55
![Privacy Obligations: Explored Types, Events and Actions [1/2] Long-term Privacy Obligations Events Triggering Obligations Privacy Obligations: Explored Types, Events and Actions [1/2] Long-term Privacy Obligations Events Triggering Obligations](http://slidetodoc.com/presentation_image_h/a7200442183907603d8f693140f54aea/image-55.jpg)
Privacy Obligations: Explored Types, Events and Actions [1/2] Long-term Privacy Obligations Events Triggering Obligations Time-driven Driven by Usage and Counters 1. at a specific date and time (e. g. 1: 00 am 01 -Jan-2005) 2. after a certain period of time (e. g. 1 hour, 3 days, 5 minutes) 3. after the data has being used for a certain number of times (e. g. after being used twice) in a specific timeframe Actions Dictated by Obligations Delete/ Update 1. delete all confidential data of a given data subject 2. partially delete data (e. g. delete only the credit card number) 3. replace data with an updated set of data (e. g. update subject’s address) Hide/ Unhide • • 11/26/2020 hide (encrypt) all data of a subject from any access hide a part of this data from any access unhide all data unhide a part of the data 57
![Privacy Obligations: Explored Types, Events and Actions [2/2] Ongoing Privacy Obligations Events Triggering Obligations Privacy Obligations: Explored Types, Events and Actions [2/2] Ongoing Privacy Obligations Events Triggering Obligations](http://slidetodoc.com/presentation_image_h/a7200442183907603d8f693140f54aea/image-56.jpg)
Privacy Obligations: Explored Types, Events and Actions [2/2] Ongoing Privacy Obligations Events Triggering Obligations Time-driven 1. periodically (e. g. every month) Driven by Contextual Events 1. when the data being used 2. when the data being transferred 3. when the data being deleted 4. a particular party/parties try to access 5. data is being used for certain purpose (e. g. send advertisement) 6. a set of data is going to be retrieved together 7. any action predefined by the data subject Others 1. when the privacy policies changed Actions Dictated by Obligations 1. send a report to a subject containing the status of their data and their opt-in/opt-out options (e. g. number of times being used, who has tried to access) 2. tell the subject what data he/she has provided 3. get updated data from subject 4. audit the logs, report any improper use of the data Notify • notify the subject Log 1. take logs Access 1. default allow/disallow all access 2. allow 3. disallow Consult 1. get authorization from data subject 2. get authorization from third party 3. check according to certain condition made by the user 1. Stop access to the data 2. update obligation Short-term and Transactional Privacy Obligations might need to be dictated by a transaction or an interaction. The actions specified by these obligations might need to be immediately fulfilled. These actions can be the same as the ones specified by long-term and on-going obligations. 11/26/2020 58
Privacy Obligations: 1 st Classification – Examples 1. Transactional Obligations • Notify the owner of PII data when someone accesses it (i. e. linked to an access control decision); • Notify the owner of PII data when their data is disclosed to a third party; • Delete/Encrypt PII data of a user at the end of a transaction (or after data has been accessed); • Ask for authorization to the owner of PII data when someone accesses it; • Ask for authorization to the owner of PII data when their data is disclosed to a third party; • Create an audit log when PII data is accessed; • … 11/26/2020 59
Privacy Obligations: 1 st Classification – Examples 2. Data Retention and Handling Obligations • Delete PII data in X hours/days/months/years starting from now (e. g. delete ABC data on 01/01/2010) ; • Send PII data (in clear or encrypted) to entity Y at time Z (optional: delete the local data after this actions is performed); • Notify the owner of PII data every X days/months/years that their data is stored in an enterprise database; • Encrypt data under some key at a certain time (alternative to delete) • … 11/26/2020 60
Privacy Obligations: 1 st Classification – Examples 3. Other event-driven Obligations • Delete PII data after it has been accessed X times e. g. delete my PII data once it has been used one time); • Notify the owner of PII data after it has been accessed X times; • … 11/26/2020 61
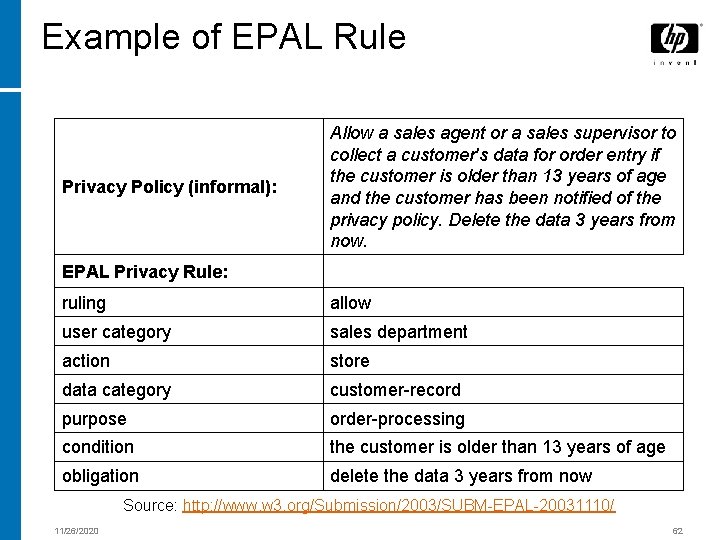
Example of EPAL Rule Privacy Policy (informal): Allow a sales agent or a sales supervisor to collect a customer's data for order entry if the customer is older than 13 years of age and the customer has been notified of the privacy policy. Delete the data 3 years from now. EPAL Privacy Rule: ruling allow user category sales department action store data category customer-record purpose order-processing condition the customer is older than 13 years of age obligation delete the data 3 years from now Source: http: //www. w 3. org/Submission/2003/SUBM-EPAL-20031110/ 11/26/2020 62
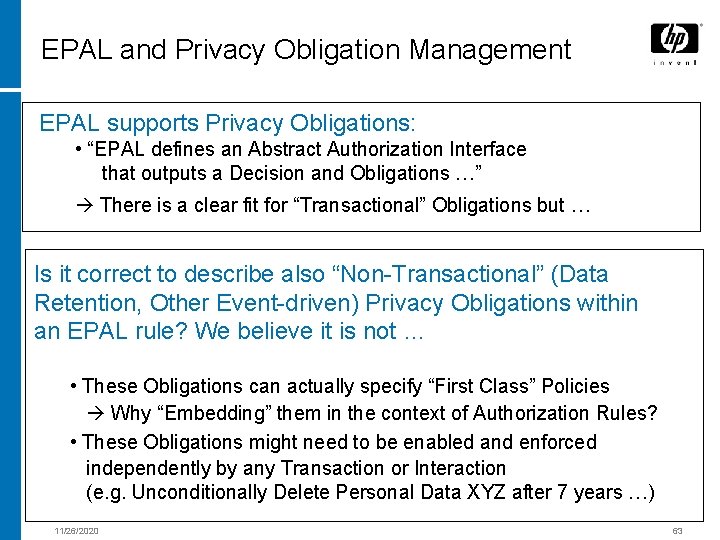
EPAL and Privacy Obligation Management EPAL supports Privacy Obligations: • “EPAL defines an Abstract Authorization Interface that outputs a Decision and Obligations …” There is a clear fit for “Transactional” Obligations but … Is it correct to describe also “Non-Transactional” (Data Retention, Other Event-driven) Privacy Obligations within an EPAL rule? We believe it is not … • These Obligations can actually specify “First Class” Policies Why “Embedding” them in the context of Authorization Rules? • These Obligations might need to be enabled and enforced independently by any Transaction or Interaction (e. g. Unconditionally Delete Personal Data XYZ after 7 years …) 11/26/2020 63
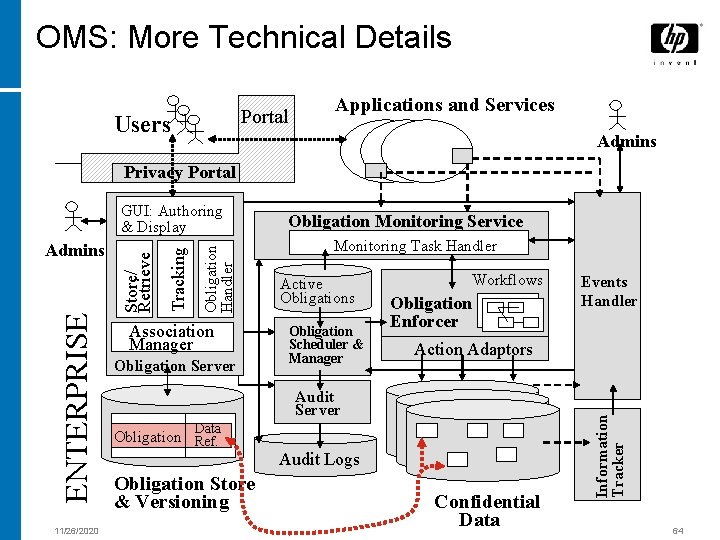
OMS: More Technical Details Portal Users Applications and Services Admins Privacy Portal 11/26/2020 Association Manager Obligation Server Obligation Monitoring Service Monitoring Task Handler Active Obligations Obligation Scheduler & Manager Workflows Obligation Enforcer Action Adaptors Audit Server Data Obligation Ref. Audit Logs Obligation Store & Versioning Events Handler Confidential Data Information Tracker Tracking Obligation Handler ENTERPRISE Admins Store/ Retrieve GUI: Authoring & Display 64

- Slides: 63