DDOS Defense by Offense OFFENSE Presented by Anup
DDOS Defense by Offense OFFENSE Presented by: Anup Goyal Aojan Su
Objections Ø Several objections identified By Authors itself ü ü ü Ø Bandwidth Envy Flash Crowds Variable bandwidth cost Is It Practical in real Internet ? ?
Clients’ upload capacity Ø Ø Clients with limited upload capacity (dialup users) can not “speak-up” They can’t increase their chance to obtain service. In worse case, they can suffer when everyone else speaks up.

Can’t detect malicious client Ø Ø Even good clients need to flood the server to get service. It could be much more difficult to detect attackers.
Access Link Congestion Ø Ø If the access link of thinner is congested, legitimate clients would back off due to congestion control. Attackers could ignore congestion control and send at higher capacity.
Edge Network Flooding Ø Good client’s flooding traffic effect edge networks by increased traffic volumes. ü potentially harming other flows.
Problem for good guys Ø Ø No good way to accommodate clientèle (good and bad) coming from the same location. Good Client always loose while sharing a Bottleneck link.
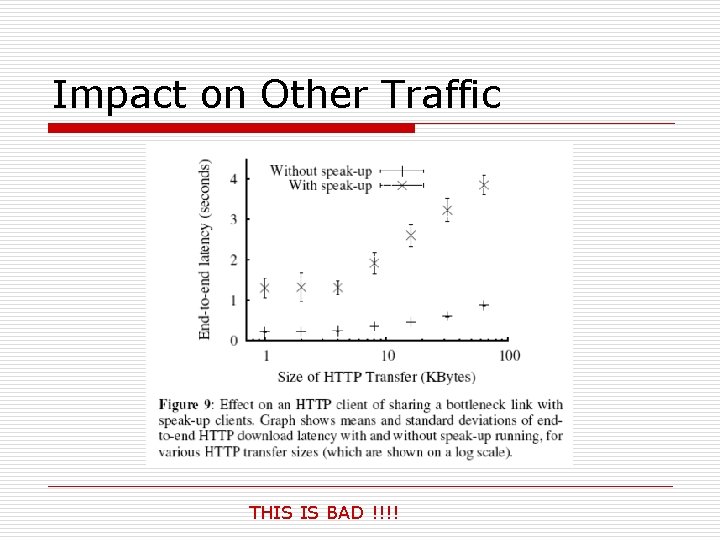
Impact on Other Traffic THIS IS BAD !!!!
Problems Unaddressed/overlooked Ø Effect of low-rate attack not addressed ü Ø Bad client also has spare bandwidth. Assumptions hold because of nature of current network characteristics ü ü ü How to detect when these assumptions break? Switch off speak-up (automatically? ) under these conditions. Effect of various traffic patterns? (i. e. heavy-tail distribution)
My Question Ø Are speak-up’s assumptions reasonable? ü Ø “The thinner is never congested”? Impact on network ü ü good traffic amplifier? How much bandwidth will be wasted for dummy bytes?
Primary Focus on HTTP Ø Ø Focus primarily on Web traffic and its properties (e. g. HTTP). Does not mention its usefulness for any other situation or protocol.
Market Survey Missing Ø Ø The researchers have not done a market survey, thus all their findings are theoretical. Economic issue consideration is missing.
Extra hardware Ø There is extra hardware (the Thinner) that has to sit in front of any server we want to protect by Speak-Up. Ø Expensive Ø Single Point of Failure
- Slides: 13