Data Link Networks Hardware Building Blocks Nodes Links
Data Link Networks Hardware Building Blocks Nodes & Links CS 380 Int. to Comp. Networks Data Link Networks - Part I 1
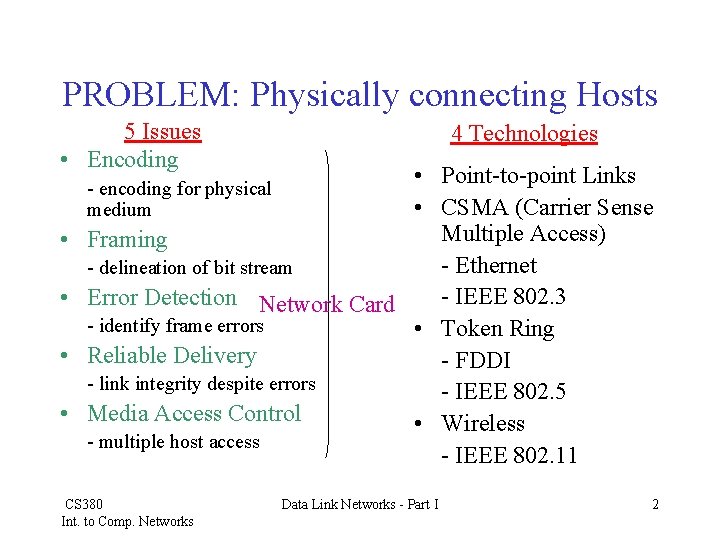
PROBLEM: Physically connecting Hosts 5 Issues • Encoding 4 Technologies • Point-to-point Links • CSMA (Carrier Sense Multiple Access) Framing - Ethernet - delineation of bit stream - IEEE 802. 3 Error Detection Network Card - identify frame errors • Token Ring Reliable Delivery - FDDI - link integrity despite errors - IEEE 802. 5 Media Access Control • Wireless - multiple host access - IEEE 802. 11 - encoding for physical medium • • CS 380 Int. to Comp. Networks Data Link Networks - Part I 2
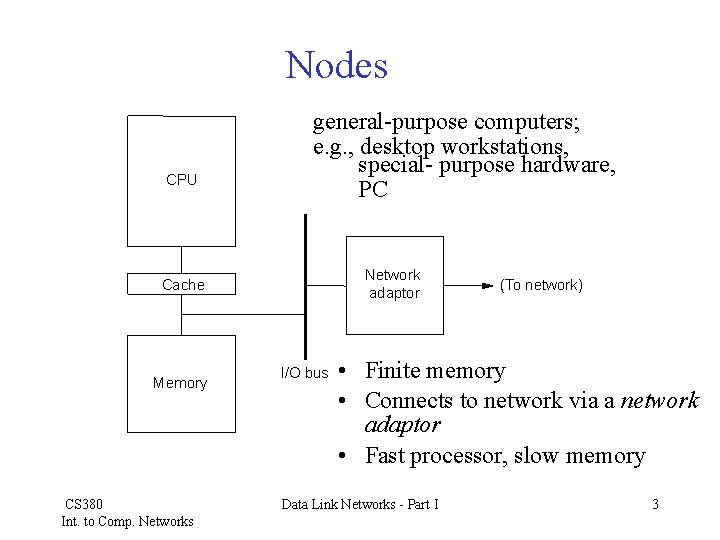
Nodes CPU general-purpose computers; e. g. , desktop workstations, special- purpose hardware, PC Network adaptor Cache Memory CS 380 Int. to Comp. Networks I/O bus (To network) • Finite memory • Connects to network via a network adaptor • Fast processor, slow memory Data Link Networks - Part I 3
Network Node Memory • Moore’s Law – Doubling processor speeds in 18 months • Memory Latency – Only 7% improvement each year • Network nodes run at memory speeds, not CPU speeds • Memory accesses needed to be considered carefully • Two scarce resources: bandwidth and memory CS 380 Int. to Comp. Networks Data Link Networks - Part I 4
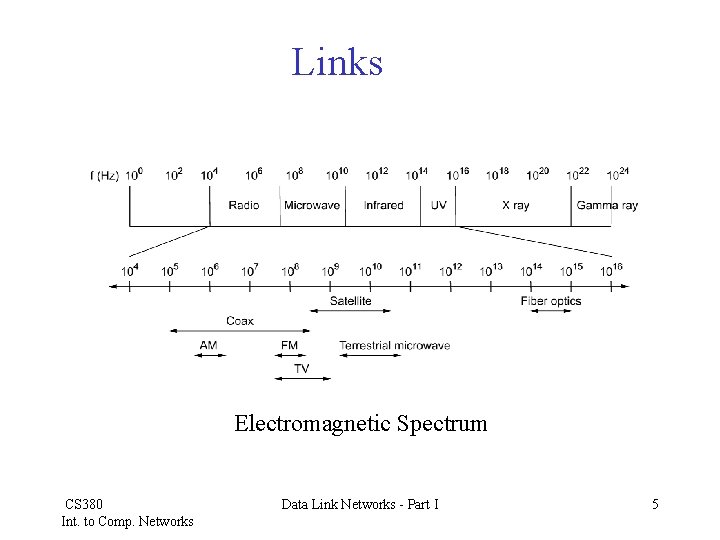
Links Electromagnetic Spectrum CS 380 Int. to Comp. Networks Data Link Networks - Part I 5
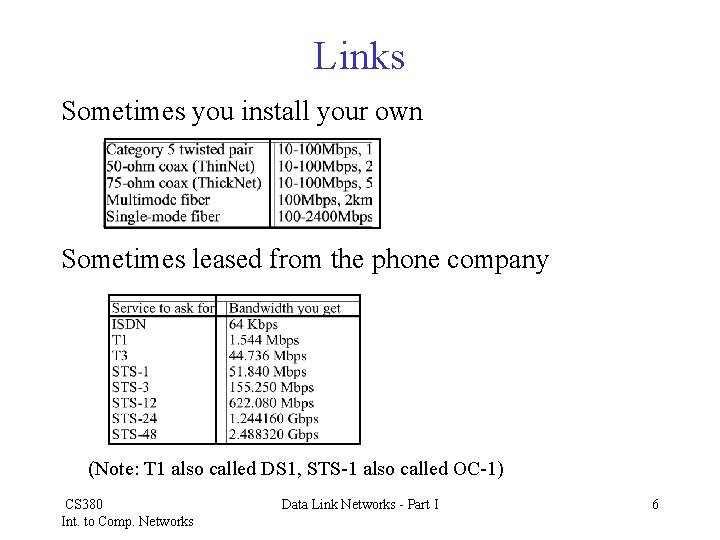
Links Sometimes you install your own Sometimes leased from the phone company (Note: T 1 also called DS 1, STS-1 also called OC-1) CS 380 Int. to Comp. Networks Data Link Networks - Part I 6
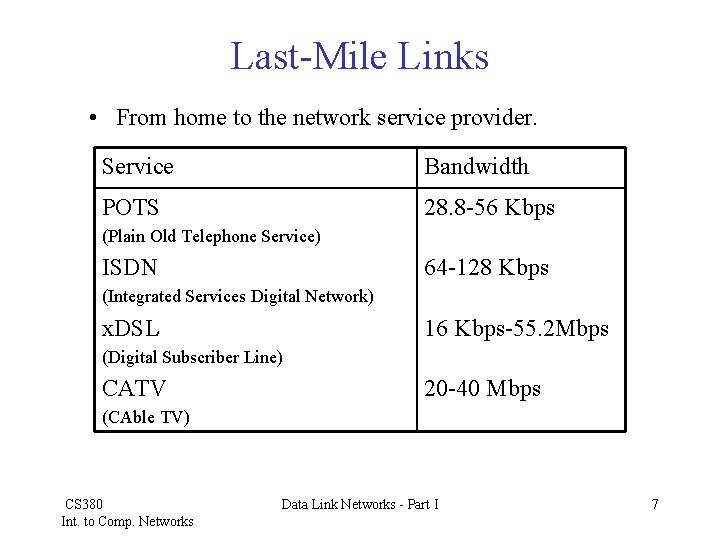
Last-Mile Links • From home to the network service provider. Service Bandwidth POTS 28. 8 -56 Kbps (Plain Old Telephone Service) ISDN 64 -128 Kbps (Integrated Services Digital Network) x. DSL 16 Kbps-55. 2 Mbps (Digital Subscriber Line) CATV 20 -40 Mbps (CAble TV) CS 380 Int. to Comp. Networks Data Link Networks - Part I 7
Point-to-Point Links • • Encoding Framing Error Detection Reliable Transmission CS 380 Int. to Comp. Networks Data Link Networks - Part I 8
Encoding • Signals propagate over a physical medium – modulate electromagnetic waves by varying the voltage • Network adaptor handles encoding – Encoded bits to signals (sending) – Decodes signals to bits (receiving) CS 380 Int. to Comp. Networks Data Link Networks - Part I 9
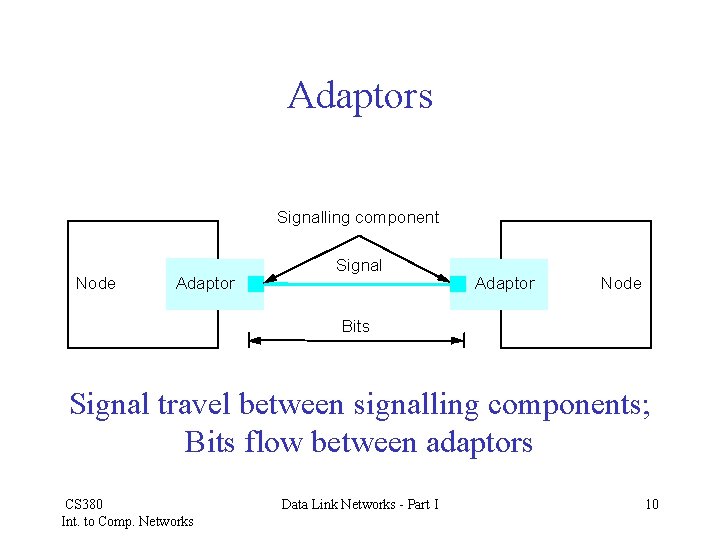
Adaptors Signalling component Node Adaptor Signal Adaptor Node Bits Signal travel between signalling components; Bits flow between adaptors CS 380 Int. to Comp. Networks Data Link Networks - Part I 10
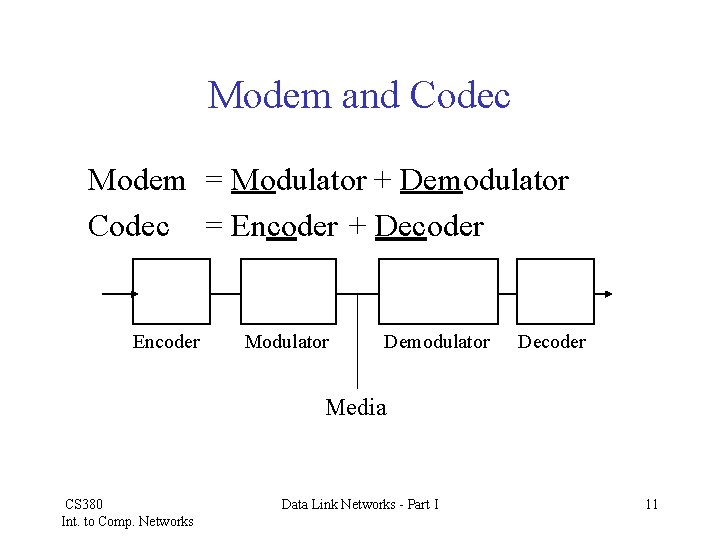
Modem and Codec Modem = Modulator + Demodulator Codec = Encoder + Decoder Encoder Modulator Demodulator Decoder Media CS 380 Int. to Comp. Networks Data Link Networks - Part I 11
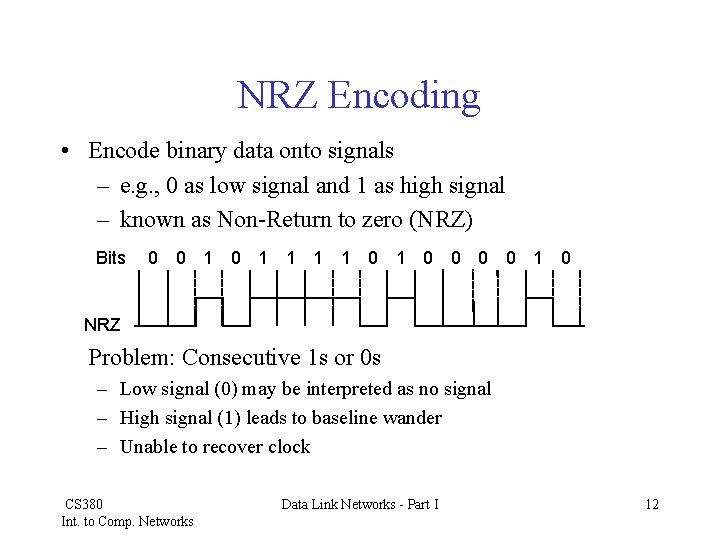
NRZ Encoding • Encode binary data onto signals – e. g. , 0 as low signal and 1 as high signal – known as Non-Return to zero (NRZ) Bits 0 0 1 1 1 1 0 0 0 0 1 0 NRZ Problem: Consecutive 1 s or 0 s – Low signal (0) may be interpreted as no signal – High signal (1) leads to baseline wander – Unable to recover clock CS 380 Int. to Comp. Networks Data Link Networks - Part I 12
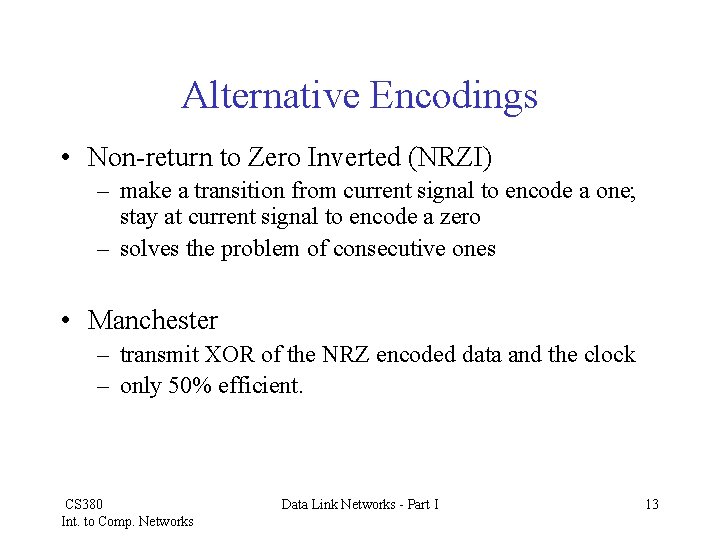
Alternative Encodings • Non-return to Zero Inverted (NRZI) – make a transition from current signal to encode a one; stay at current signal to encode a zero – solves the problem of consecutive ones • Manchester – transmit XOR of the NRZ encoded data and the clock – only 50% efficient. CS 380 Int. to Comp. Networks Data Link Networks - Part I 13
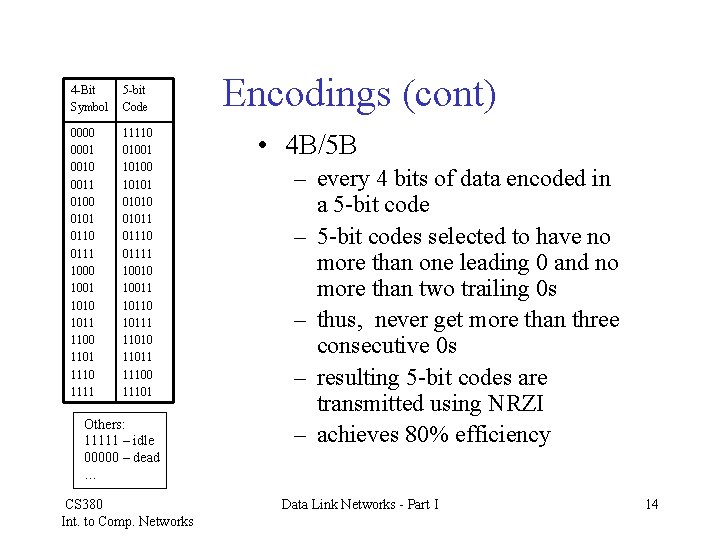
4 -Bit Symbol 5 -bit Code 0000 0001 0010 0011 0100 0101 0110 0111 1000 1001 1010 1011 1100 1101 1110 11110 01001 10100 101010 01011 01110 01111 10010 10011 10110 10111 11010 11011 11100 11101 Others: 11111 – idle 00000 – dead … CS 380 Int. to Comp. Networks Encodings (cont) • 4 B/5 B – every 4 bits of data encoded in a 5 -bit code – 5 -bit codes selected to have no more than one leading 0 and no more than two trailing 0 s – thus, never get more than three consecutive 0 s – resulting 5 -bit codes are transmitted using NRZI – achieves 80% efficiency Data Link Networks - Part I 14
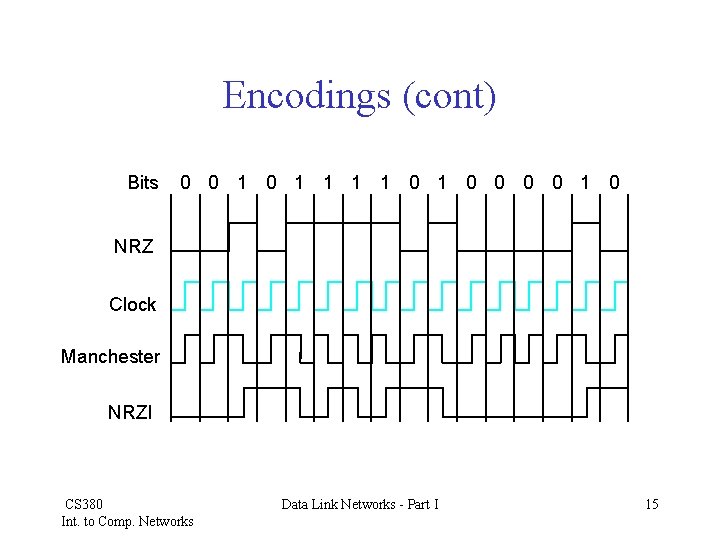
Encodings (cont) Bits 0 0 1 1 1 1 0 0 0 0 1 0 NRZ Clock Manchester NRZI CS 380 Int. to Comp. Networks Data Link Networks - Part I 15
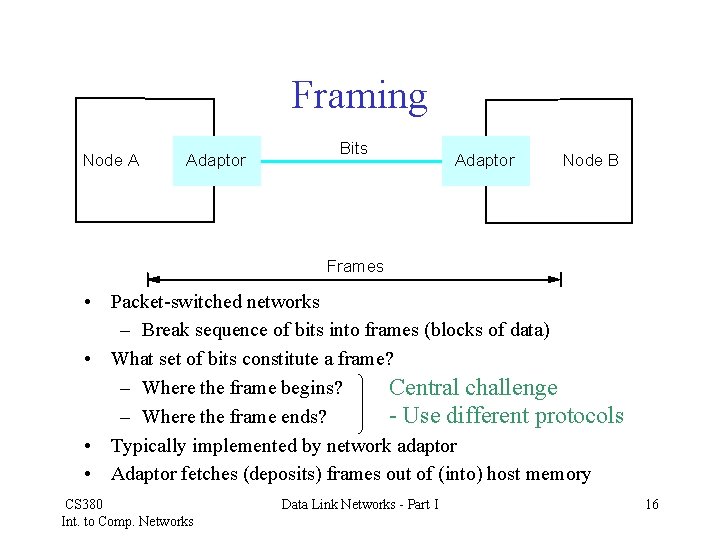
Framing Node A Adaptor Bits Adaptor Node B Frames • Packet-switched networks – Break sequence of bits into frames (blocks of data) • What set of bits constitute a frame? – Where the frame begins? Central challenge – Where the frame ends? - Use different protocols • Typically implemented by network adaptor • Adaptor fetches (deposits) frames out of (into) host memory CS 380 Int. to Comp. Networks Data Link Networks - Part I 16
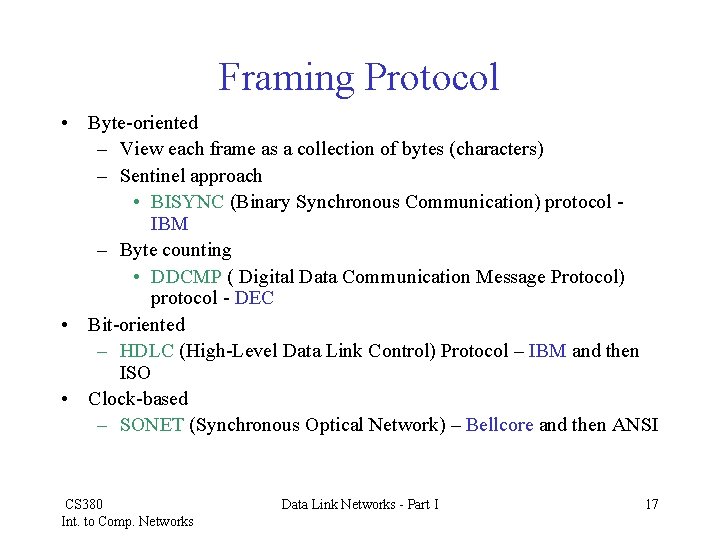
Framing Protocol • Byte-oriented – View each frame as a collection of bytes (characters) – Sentinel approach • BISYNC (Binary Synchronous Communication) protocol IBM – Byte counting • DDCMP ( Digital Data Communication Message Protocol) protocol - DEC • Bit-oriented – HDLC (High-Level Data Link Control) Protocol – IBM and then ISO • Clock-based – SONET (Synchronous Optical Network) – Bellcore and then ANSI CS 380 Int. to Comp. Networks Data Link Networks - Part I 17
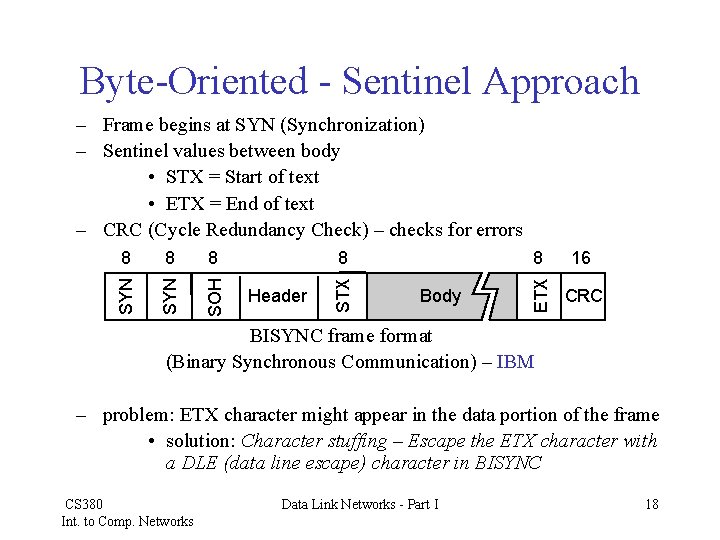
Byte-Oriented - Sentinel Approach 8 SYN SOH 8 Header Body 8 16 ETX 8 SYN – Frame begins at SYN (Synchronization) – Sentinel values between body • STX = Start of text • ETX = End of text – CRC (Cycle Redundancy Check) – checks for errors CRC BISYNC frame format (Binary Synchronous Communication) – IBM – problem: ETX character might appear in the data portion of the frame • solution: Character stuffing – Escape the ETX character with a DLE (data line escape) character in BISYNC CS 380 Int. to Comp. Networks Data Link Networks - Part I 18
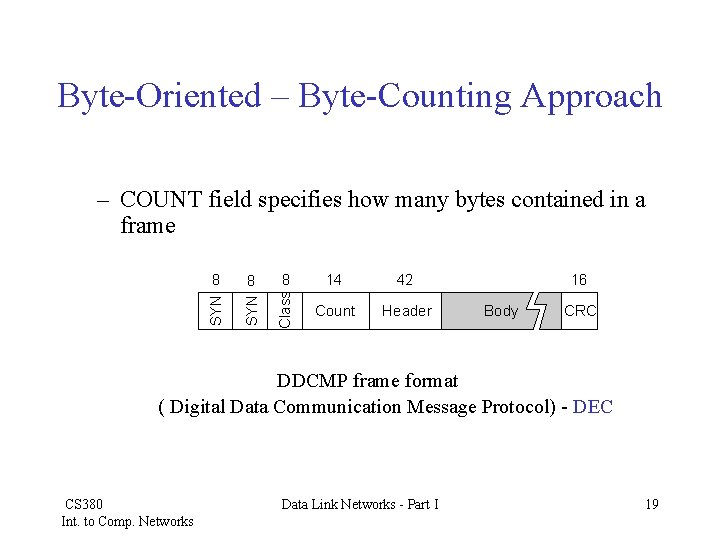
Byte-Oriented – Byte-Counting Approach 8 8 8 14 42 SYN Class – COUNT field specifies how many bytes contained in a frame Count Header 16 Body CRC DDCMP frame format ( Digital Data Communication Message Protocol) - DEC CS 380 Int. to Comp. Networks Data Link Networks - Part I 19
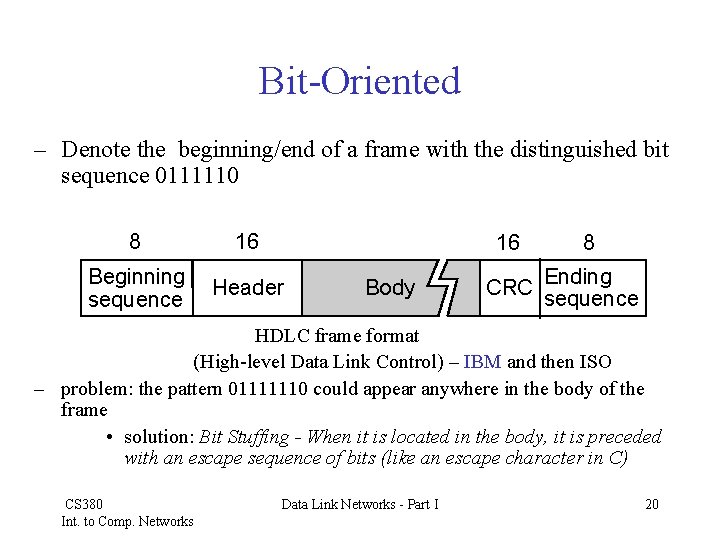
Bit-Oriented – Denote the beginning/end of a frame with the distinguished bit sequence 0111110 8 16 Beginning sequence Header 16 Body 8 Ending CRC sequence HDLC frame format (High-level Data Link Control) – IBM and then ISO – problem: the pattern 01111110 could appear anywhere in the body of the frame • solution: Bit Stuffing - When it is located in the body, it is preceded with an escape sequence of bits (like an escape character in C) CS 380 Int. to Comp. Networks Data Link Networks - Part I 20
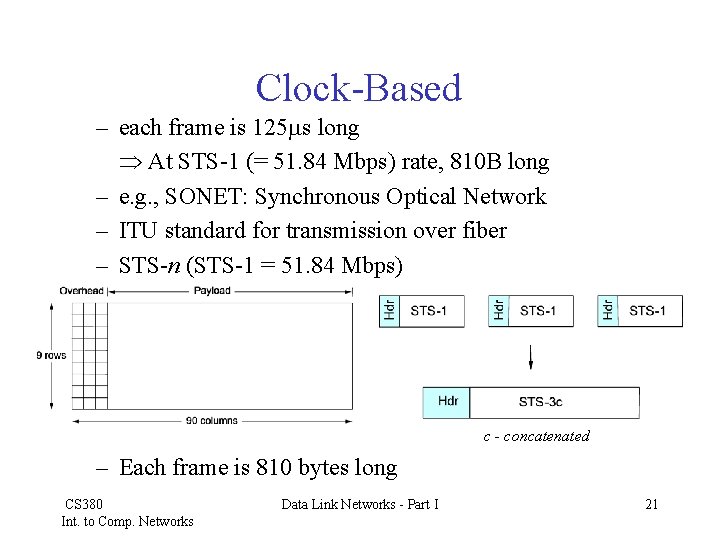
Clock-Based – each frame is 125 s long At STS-1 (= 51. 84 Mbps) rate, 810 B long – e. g. , SONET: Synchronous Optical Network – ITU standard for transmission over fiber – STS-n (STS-1 = 51. 84 Mbps) c - concatenated – Each frame is 810 bytes long CS 380 Int. to Comp. Networks Data Link Networks - Part I 21
Error • Long history of dealing with bit errors – Hamming – Reed/Solomon • Detecting Error is only one part of the problem, the other part is correcting errors • Two methods of error correction – Have the message retransmitted – Error-correcting codes (algorithms that all the recipient to reconstruct the correct message) CS 380 Int. to Comp. Networks Data Link Networks - Part I 22
Error Detection • Basic idea – add extra (redundant) bits to a frame that can be used to determine if errors have been introduced. • Ethernet: 1500 B data requires only 32 -bits (CRC-32) • Sender applies algorithm to the message to come up with the extra bits • Receiver uses the same algorithm to check if the calculation comes up with the same result • Common error-detecting codes – Two-dimensional parity (ASCII) (link-level) – Checksum (internet) (not link-level) – CRC, Cyclic Redundancy Check, (link-level) CS 380 Int. to Comp. Networks Data Link Networks - Part I 23
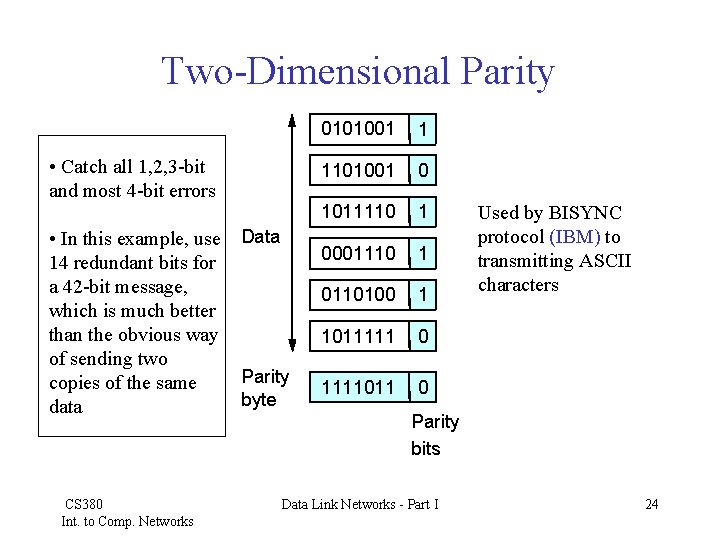
Two-Dimensional Parity • Catch all 1, 2, 3 -bit and most 4 -bit errors • In this example, use Data 14 redundant bits for a 42 -bit message, which is much better than the obvious way of sending two Parity copies of the same byte data CS 380 Int. to Comp. Networks 0101001 1 1101001 0 1011110 1 0001110 1 0110100 1 1011111 0 1111011 0 Used by BISYNC protocol (IBM) to transmitting ASCII characters Parity bits Data Link Networks - Part I 24
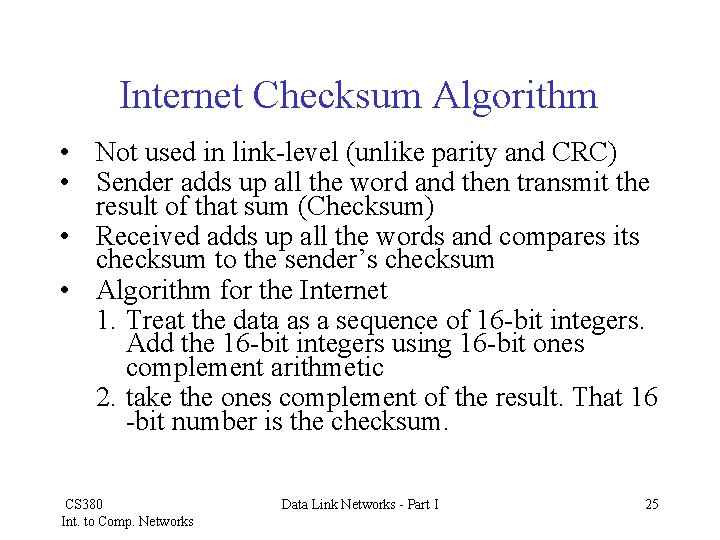
Internet Checksum Algorithm • Not used in link-level (unlike parity and CRC) • Sender adds up all the word and then transmit the result of that sum (Checksum) • Received adds up all the words and compares its checksum to the sender’s checksum • Algorithm for the Internet 1. Treat the data as a sequence of 16 -bit integers. Add the 16 -bit integers using 16 -bit ones complement arithmetic 2. take the ones complement of the result. That 16 -bit number is the checksum. CS 380 Int. to Comp. Networks Data Link Networks - Part I 25
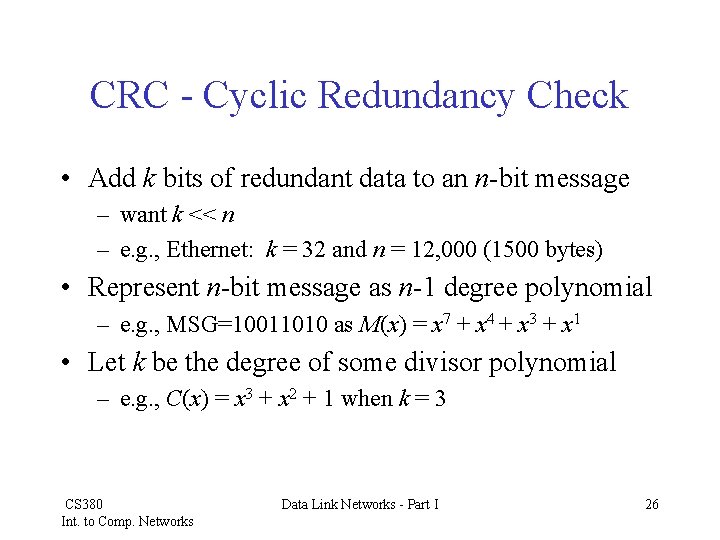
CRC - Cyclic Redundancy Check • Add k bits of redundant data to an n-bit message – want k << n – e. g. , Ethernet: k = 32 and n = 12, 000 (1500 bytes) • Represent n-bit message as n-1 degree polynomial – e. g. , MSG=10011010 as M(x) = x 7 + x 4 + x 3 + x 1 • Let k be the degree of some divisor polynomial – e. g. , C(x) = x 3 + x 2 + 1 when k = 3 CS 380 Int. to Comp. Networks Data Link Networks - Part I 26
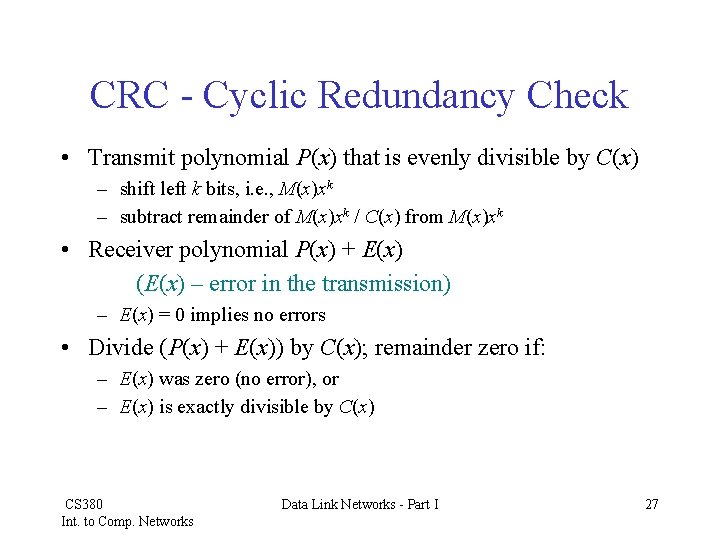
CRC - Cyclic Redundancy Check • Transmit polynomial P(x) that is evenly divisible by C(x) – shift left k bits, i. e. , M(x)xk – subtract remainder of M(x)xk / C(x) from M(x)xk • Receiver polynomial P(x) + E(x) (E(x) – error in the transmission) – E(x) = 0 implies no errors • Divide (P(x) + E(x)) by C(x); remainder zero if: – E(x) was zero (no error), or – E(x) is exactly divisible by C(x) CS 380 Int. to Comp. Networks Data Link Networks - Part I 27
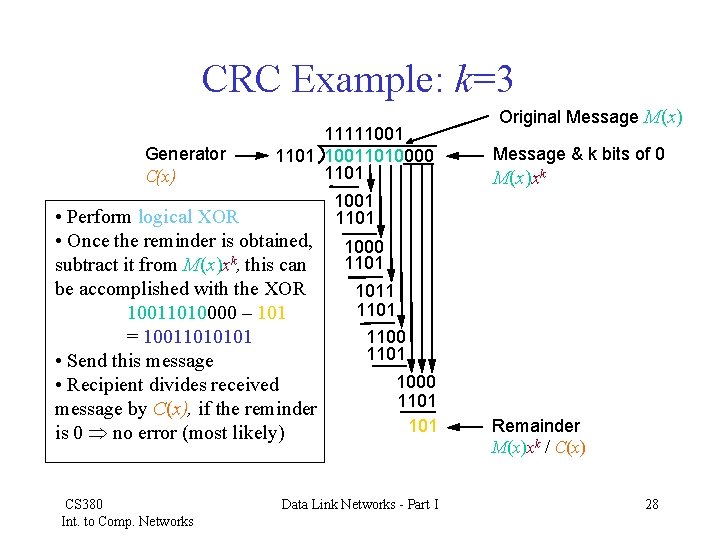
CRC Example: k=3 Generator C(x) 11111001 1101 10011010000 1101 • Perform logical XOR • Once the reminder is obtained, subtract it from M(x)xk, this can be accomplished with the XOR 10011010000 – 101 = 10011010101 • Send this message • Recipient divides received message by C(x), if the reminder is 0 no error (most likely) CS 380 Int. to Comp. Networks Original Message M(x) Message & k bits of 0 M(x)xk 1001 1101 1000 1101 1011 1100 1101 1000 1101 Data Link Networks - Part I Remainder M(x)xk / C(x) 28
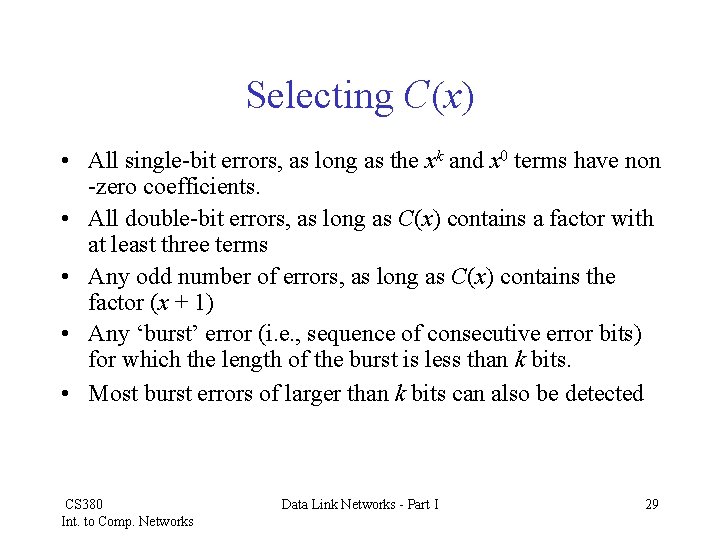
Selecting C(x) • All single-bit errors, as long as the xk and x 0 terms have non -zero coefficients. • All double-bit errors, as long as C(x) contains a factor with at least three terms • Any odd number of errors, as long as C(x) contains the factor (x + 1) • Any ‘burst’ error (i. e. , sequence of consecutive error bits) for which the length of the burst is less than k bits. • Most burst errors of larger than k bits can also be detected CS 380 Int. to Comp. Networks Data Link Networks - Part I 29
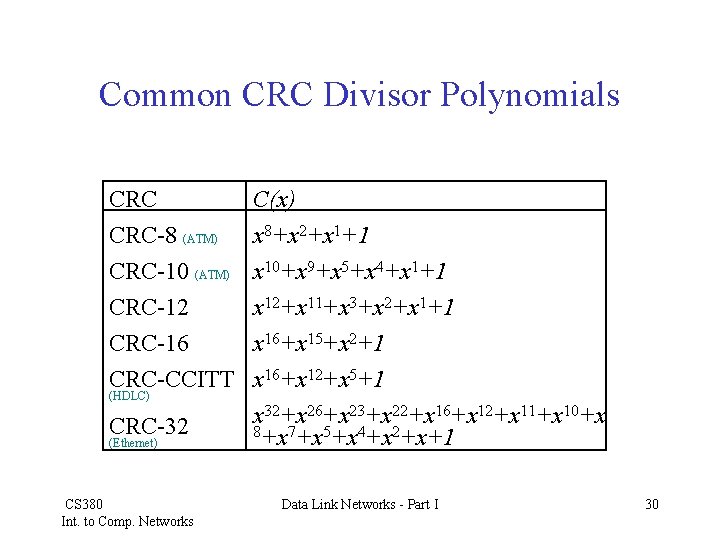
Common CRC Divisor Polynomials CRC C(x) CRC-8 (ATM) x 8+x 2+x 1+1 CRC-10 (ATM) CRC-12 CRC-16 CRC-CCITT x 10+x 9+x 5+x 4+x 1+1 x 12+x 11+x 3+x 2+x 1+1 x 16+x 15+x 2+1 x 16+x 12+x 5+1 x 32+x 26+x 23+x 22+x 16+x 12+x 11+x 10+x 8+x 7+x 5+x 4+x 2+x+1 (HDLC) CRC-32 (Ethernet) CS 380 Int. to Comp. Networks Data Link Networks - Part I 30
- Slides: 30