Data Explosion Excellence in Application Data Governance 2

- Slides: 30

Data Explosion Excellence in Application & Data Governance 2
빅데이터 시대의 보안이 슈 Excellence in Application & Data Governance 3
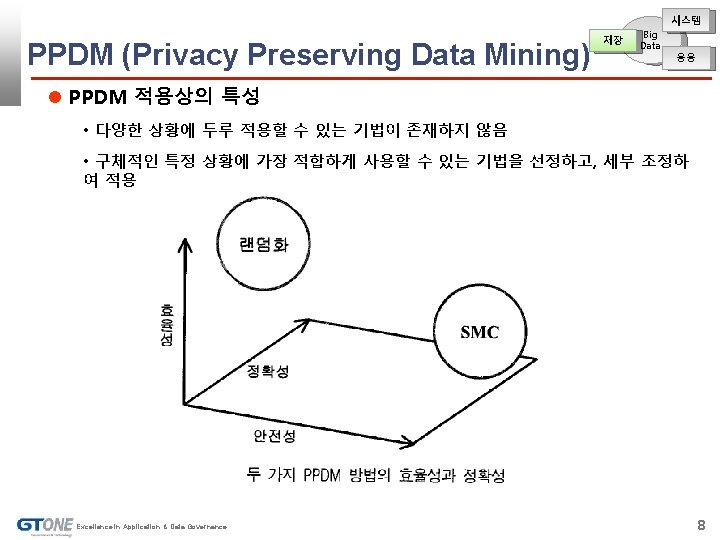
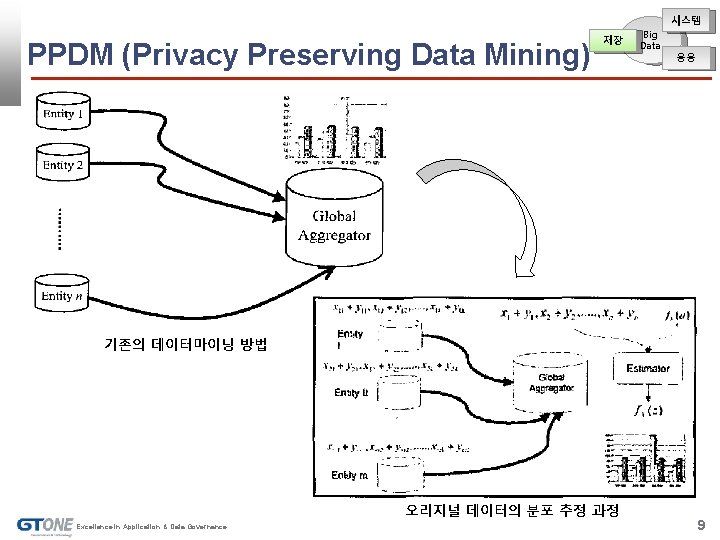
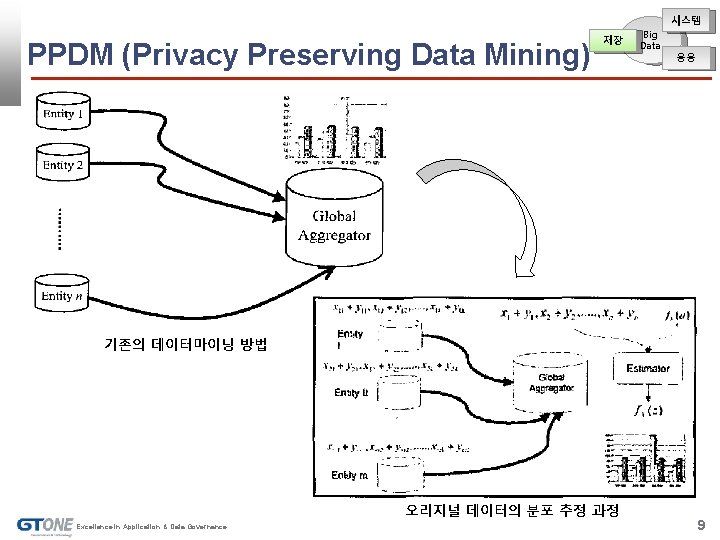
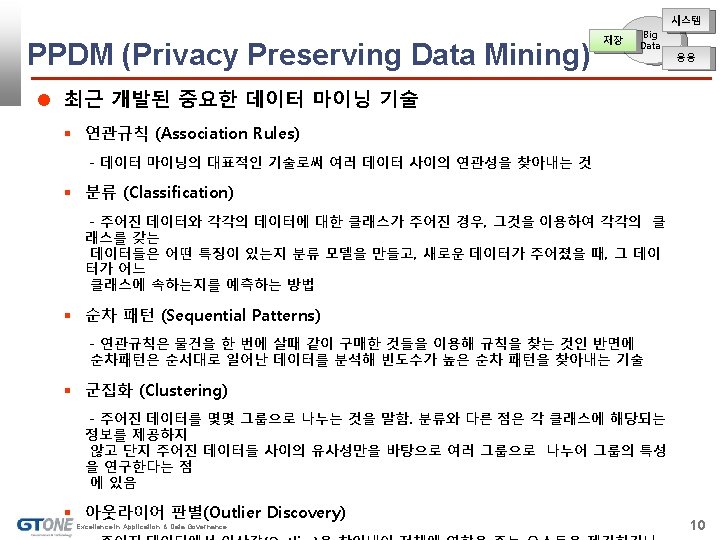
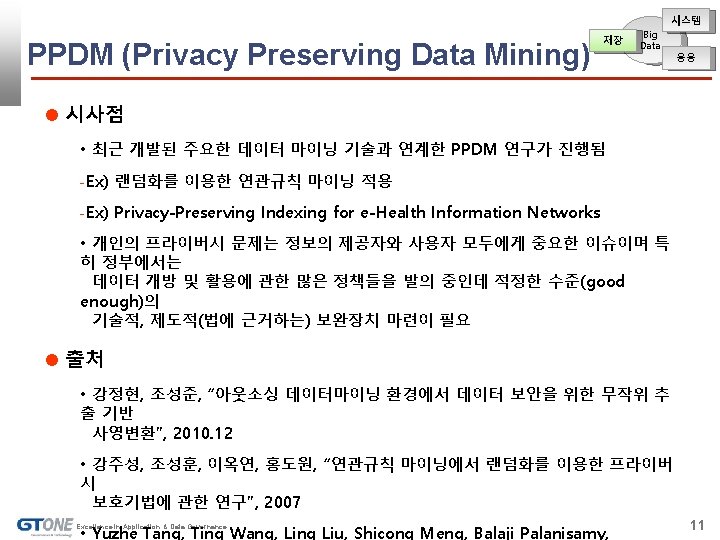
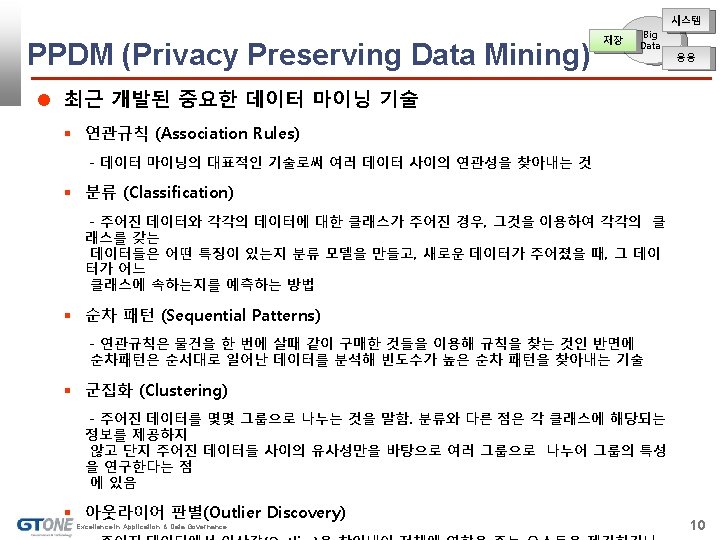
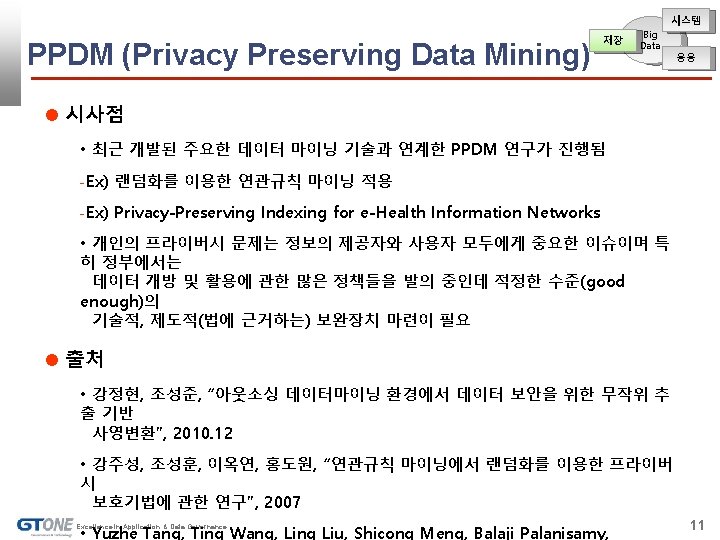
시스템 PPDM (Privacy Preserving Data Mining) 저장 Big Data 응용 기존의 데이터마이닝 방법 오리지널 데이터의 분포 추정 과정 Excellence in Application & Data Governance 9
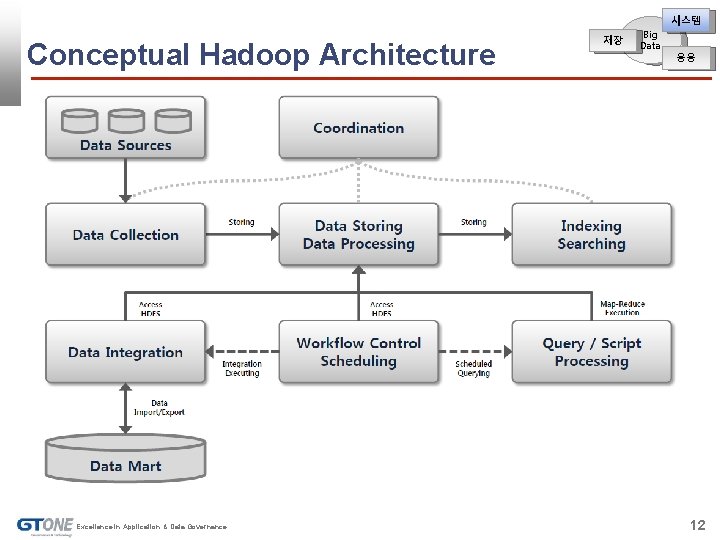
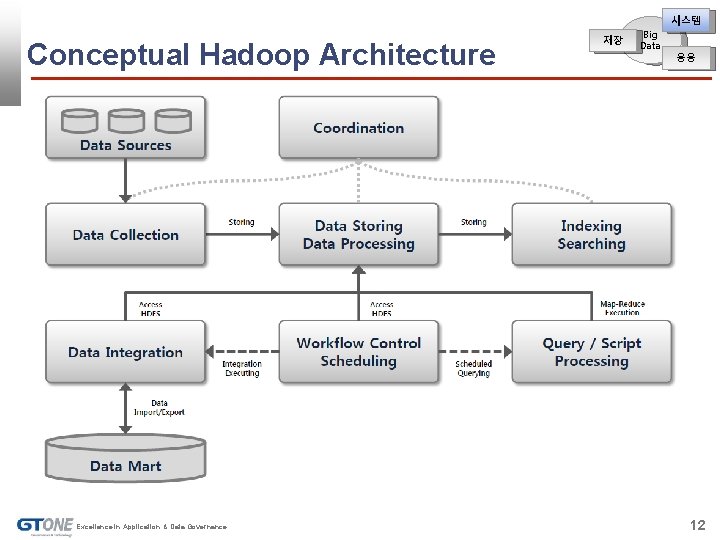
시스템 Conceptual Hadoop Architecture Excellence in Application & Data Governance 저장 Big Data 응용 12
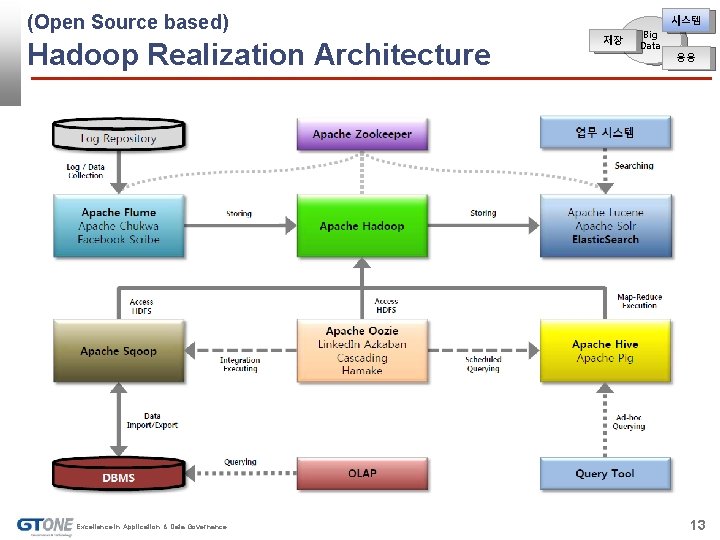
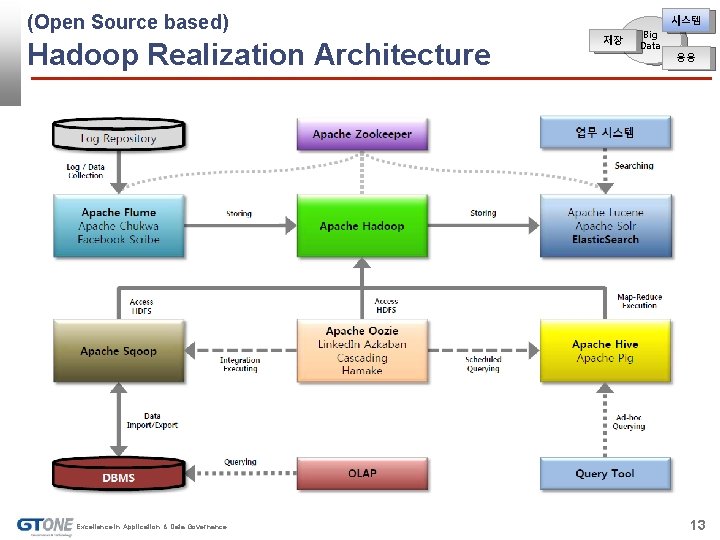
(Open Source based) Hadoop Realization Architecture Excellence in Application & Data Governance 시스템 저장 Big Data 응용 13
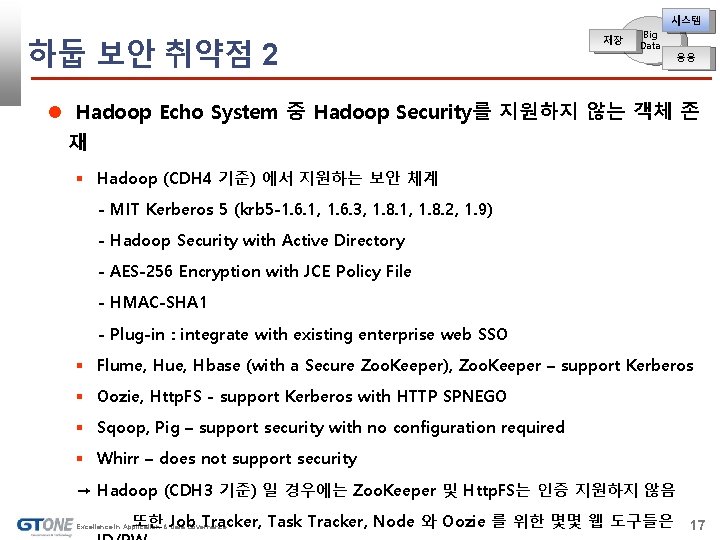
시스템 하둡 보안 취약점 2 저장 Big Data 응용 Hadoop Echo System 중 Hadoop Security를 지원하지 않는 객체 존 재 Hadoop (CDH 4 기준) 에서 지원하는 보안 체계 - MIT Kerberos 5 (krb 5 -1. 6. 1, 1. 6. 3, 1. 8. 1, 1. 8. 2, 1. 9) - Hadoop Security with Active Directory - AES-256 Encryption with JCE Policy File - HMAC-SHA 1 - Plug-in : integrate with existing enterprise web SSO Flume, Hue, Hbase (with a Secure Zoo. Keeper), Zoo. Keeper – support Kerberos Oozie, Http. FS - support Kerberos with HTTP SPNEGO Sqoop, Pig – support security with no configuration required Whirr – does not support security → Hadoop (CDH 3 기준) 일 경우에는 Zoo. Keeper 및 Http. FS는 인증 지원하지 않음 또한 Job Tracker, Task Tracker, Node 와 Oozie 를 위한 몇몇 웹 도구들은 Excellence in Application & Data Governance 17
시스템 하둡 보안 취약점 2 저장 Big Data 응용 하둡 보안 도입시 검토 대상 Job Control – Dose nothing to prevent malicious users from causing harm (weak authentication) Is not support encryption on the wire and encryption on disk Is not protect DOS attacks Is not support edge authentication (eg, PKI, SAML) Is not easy to setting up Hadoop Security System 새로운 하둡 컴포넌트 도입시 하둡 보안을 지원하는 컴포넌트로 구성해야 함 Excellence in Application & Data Governance 18
시스템 하둡 보안 취약점 – 해결 솔루션 예제 저장 Big Data 응용 Solution Ex) Gazzang z. Ncrypt for Big Data Transparent, unified data encryption to protect data at rest and in motion with minimal performance impact Advanced key management that stores keys separately from the encrypted data to ensure ongoing data privacy compliance and minimize the risk of a potential data breach Process-based access control lists to restrict access based on specific processes rather than job function, and ensure encrypted data is accessible only to those who absolutely need it Platform independence to protect your investment – and your big data – no matter which cloud provider you choose or which cloud model you deploy 출처 • 박승제, 김희열, “해쉬 체인을 이용한 하둡 보안의 향상”, 2012. 06 • Owen O’Malley, Kan Zhang, Sanjay Radia, Ram Marti, and Christopher Harrell, “Hadoop Security Design”, 2009. 10 • Andrew Beeherer, “Hadoop Security Design Just Add Kerberos? Really? ”, 2010 • Cloudera, “CDH 4 Security Guide 4. 0”, 2012. 06 • Cloudera, “CDH 3 Security Guide 3. 0”, 2012. 02 • Gazzng, “Gazzang z. Ncrypt for Big Data - data sheet”, 2012 Excellence in Application & Data Governance 19
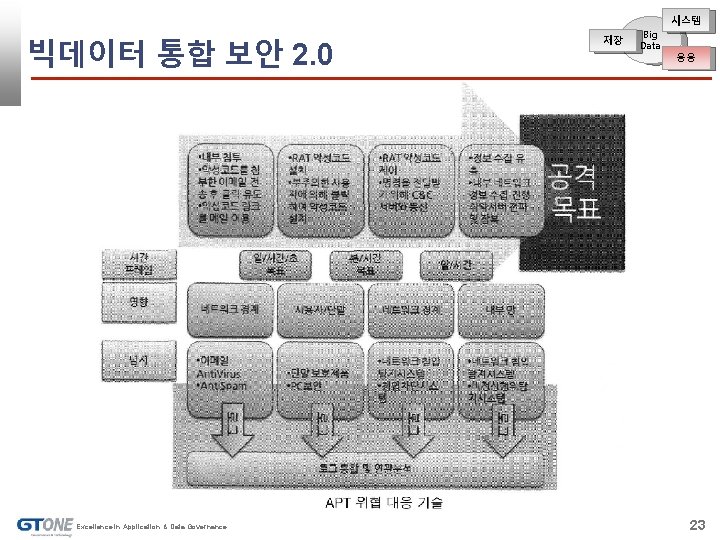
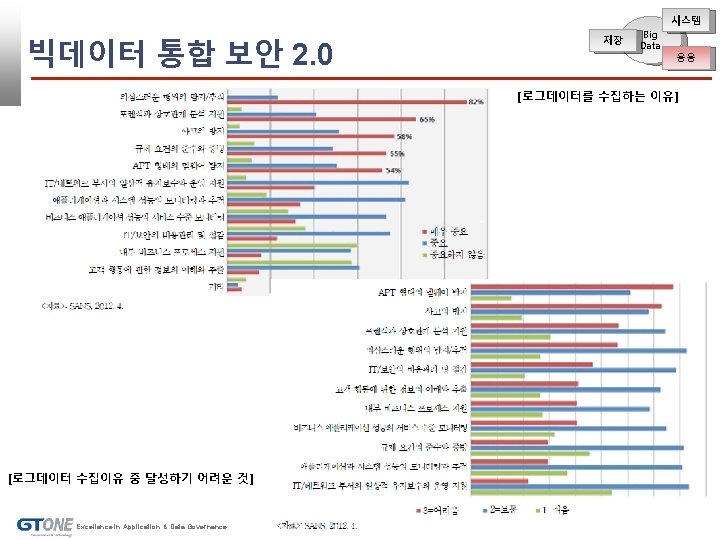
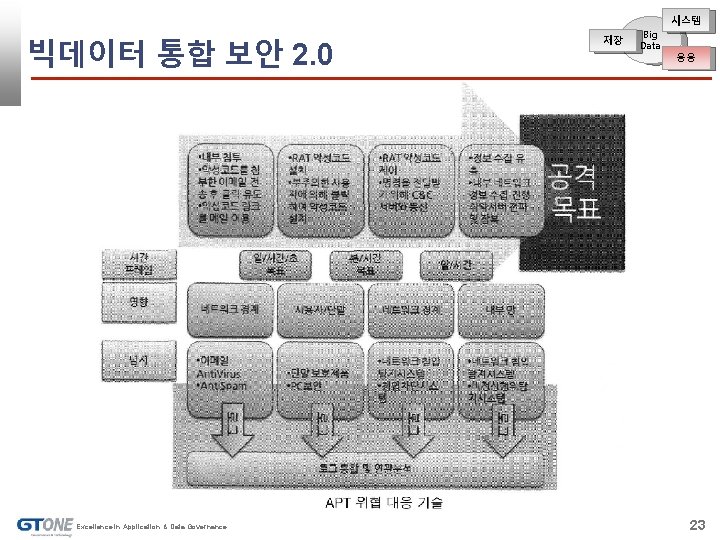
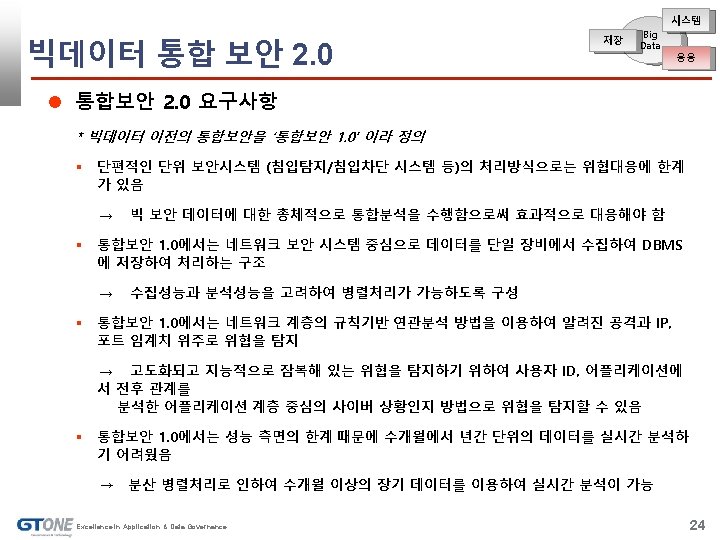
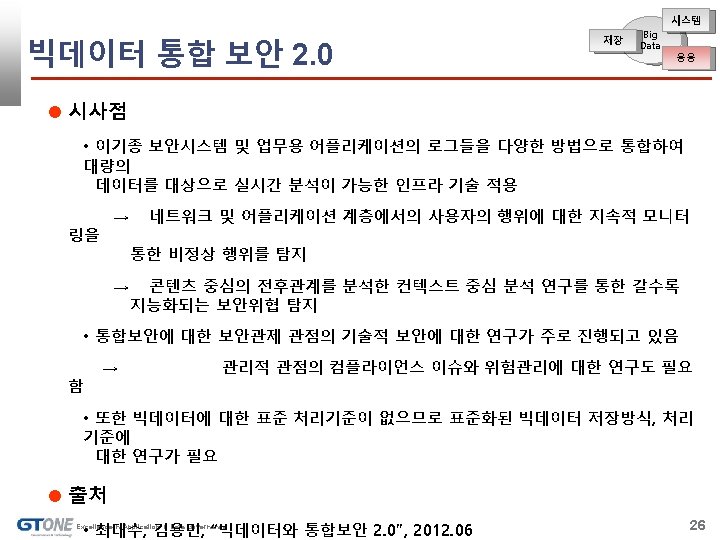
시스템 빅데이터 통합 보안 2. 0 Excellence in Application & Data Governance 저장 Big Data 응용 23
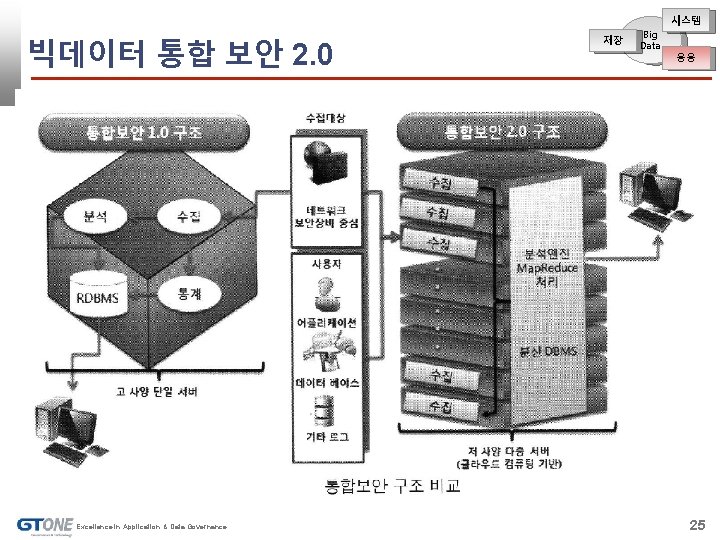
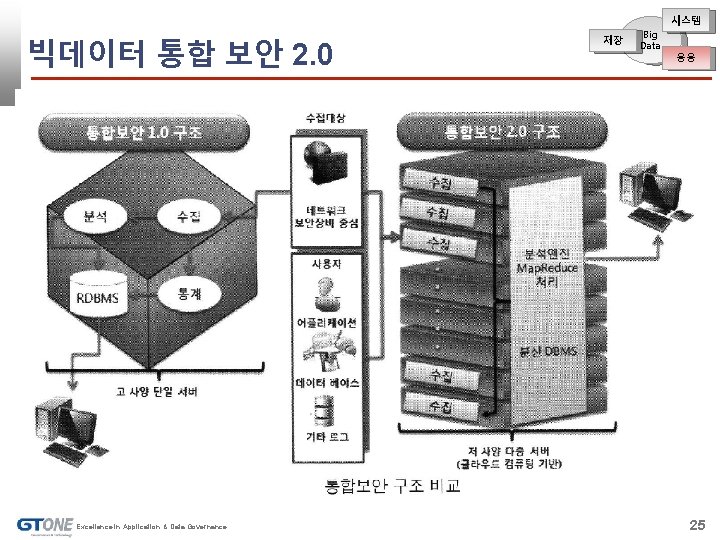
시스템 빅데이터 통합 보안 2. 0 Excellence in Application & Data Governance 저장 Big Data 응용 25
감사합니다. 이동우 지티원 데이터거버넌스 사업부 Tel : 010 -4801 -6609 email : leewow 9@naver. com Excellence in Application & Data Governance 30