Data Communications and Computer Networks A Business Users
Data Communications and Computer Networks: A Business User’s Approach Chapter 13 Network Security 1
What we will cover • Security measures • Firewalls • Business on the internet - Encryption 2
3
Introduction While computer systems today have some of the best security systems ever, they are more vulnerable than ever before. This vulnerability stems from the world-wide access to computer systems via the Internet. Computer and network security comes in many forms encryption algorithms access to facilities digital signatures fingerprints and face scans as passwords. Where do most security breaches come from? 4
What is network security? • Network security is preventing attackers from achieving objectives through unauthorized access or unauthorized use of computers and networks. www. cert. org 5
Basic Security Measures The basic security measures for computer systems fall into eight categories: External security Operational security Surveillance Passwords/authentication Auditing Access rights Standard system attacks Viruses/worms 6
External Security Protection from environmental damage such as floods, earthquakes, and heat. Physical security such as locking rooms, locking down computers, keyboards, and other devices. Electrical protection from power surges. Noise protection from placing computers away from devices that generate electromagnetic interference. 7
Personnel security • Most security violations have one common characteristic: – They are caused by people! • Training, Auditing, Least Privilege, . . . 8
Operational Security Deciding who has access to what. Limiting time of day access. Limiting day of week access. Limiting access from a location, such as not allowing a user to use a remote login during certain periods or any time. 9
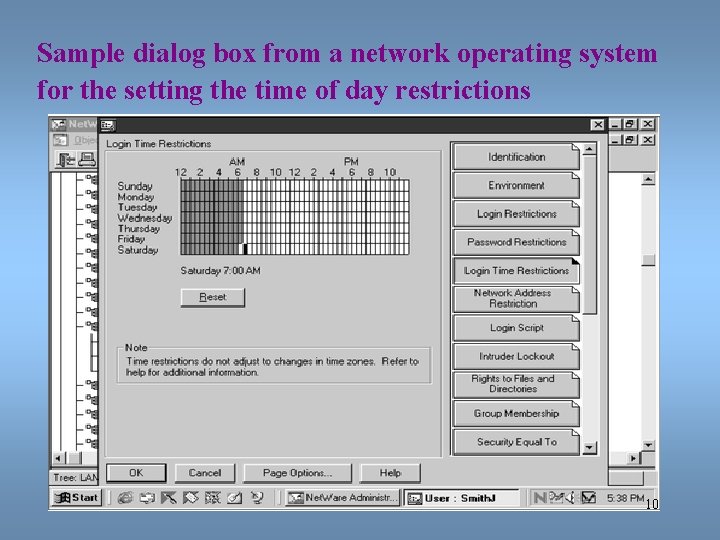
Sample dialog box from a network operating system for the setting the time of day restrictions 10
Surveillance Proper placement of security cameras can deter theft and vandalism. Cameras can also provide a record of activities. Intrusion detection is a field of study in which specialists try to prevent intrusion and try to determine if a computer system has been violated. 11
Passwords and ID Systems Passwords are the most common form of security and the most abused. Simple rules help support safe passwords, including: • Change your password often. • Pick a good, random password (minimum 8 characters, mixed symbols). • Don’t share passwords or write them down. • Don’t select names and familiar objects as passwords. • Most common password? 12
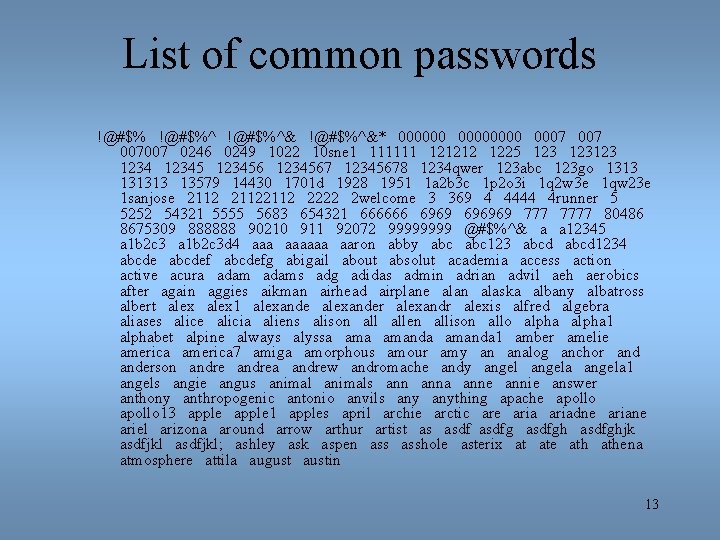
List of common passwords !@#$%^&* 00000000 0007 007007 0246 0249 1022 10 sne 1 111111 121212 1225 123123 1234567 12345678 1234 qwer 123 abc 123 go 131313 13579 14430 1701 d 1928 1951 1 a 2 b 3 c 1 p 2 o 3 i 1 q 2 w 3 e 1 qw 23 e 1 sanjose 21122112 2222 2 welcome 3 369 4 4444 4 runner 5 5252 54321 5555 5683 654321 666666 696969 7777 80486 8675309 888888 90210 911 92072 9999 @#$%^& a a 12345 a 1 b 2 c 3 d 4 aaaaaa aaron abby abc 123 abcd 1234 abcdefg abigail about absolut academia access action active acura adams adg adidas admin adrian advil aeh aerobics after again aggies aikman airhead airplane alan alaska albany albatross albert alex 1 alexander alexandr alexis alfred algebra aliases alice alicia aliens alison allen allison allo alpha 1 alphabet alpine always alyssa amanda 1 amber amelie america 7 amiga amorphous amour amy an analog anchor anderson andrea andrew andromache andy angela 1 angels angie angus animals anna anne annie answer anthony anthropogenic antonio anvils anything apache apollo 13 apple 1 apples april archie arctic are ariadne ariane ariel arizona around arrow arthur artist as asdfghjk asdfjkl; ashley ask aspen asshole asterix at ate athena atmosphere attila august austin 13
Authentication • Authentication is the process of reliably verifying the identity of someone (or something) by means of: – – A secret (password [one-time], . . . ) An object (smart card, . . . ) Physical characteristics (fingerprint, retina, . . . ) Trust • Do not mistake authentication for authorization! 14
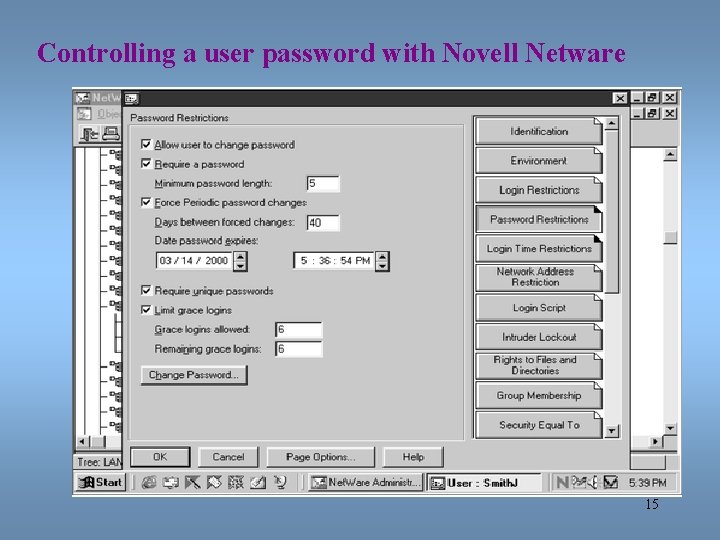
Controlling a user password with Novell Netware 15
Passwords and ID Systems Authentication? Many new forms of “passwords” are emerging: • Fingerprints • Face prints • Retina scans and iris scans • Voice prints • Ear prints 16
Auditing Creating a computer or paper audit can help detect wrongdoing. Auditing can also be used as a deterrent. Many network operating systems allow the administrator to audit most types of transactions. Many types of criminals have been caught because of computer -based audits. 17
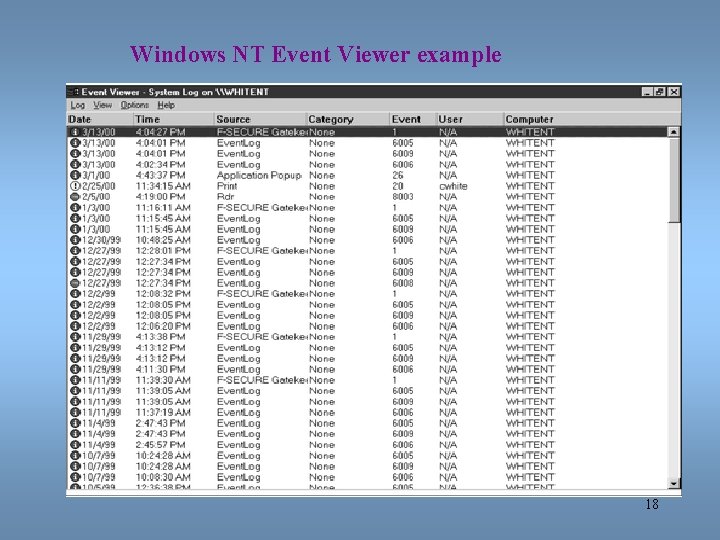
Windows NT Event Viewer example 18
Access Rights Two basic questions to access right: who and how? Who do you give access right to? No one, group of users, entire set of users? How does a user or group of users have access? Read, write, delete, print, copy, execute? Most network operating systems have a powerful system for assigning access rights. 19
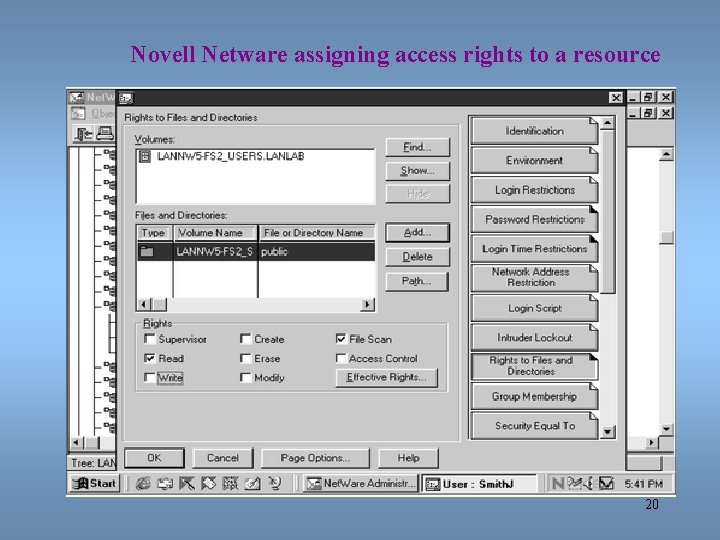
Novell Netware assigning access rights to a resource 20
Viruses Many different types of viruses, such as parasitic, boot sector, stealth, polymorphic, and macro. A Trojan Horse virus is a destructive piece of code that hides inside a harmless looking piece of code. Sending an e-mail with a destructive attachment is a form of a Trojan Horse virus. 21
Virus Detection and Scanning Signature-based scanners look for particular virus patterns or signatures and alert the user. Terminate-and-stay-resident programs run in the background constantly watching for viruses and their actions. Multi-level generic scanning is a combination of antivirus techniques including intelligent checksum analysis and expert system analysis. http: //www. symantec. com/avcenter/ 22
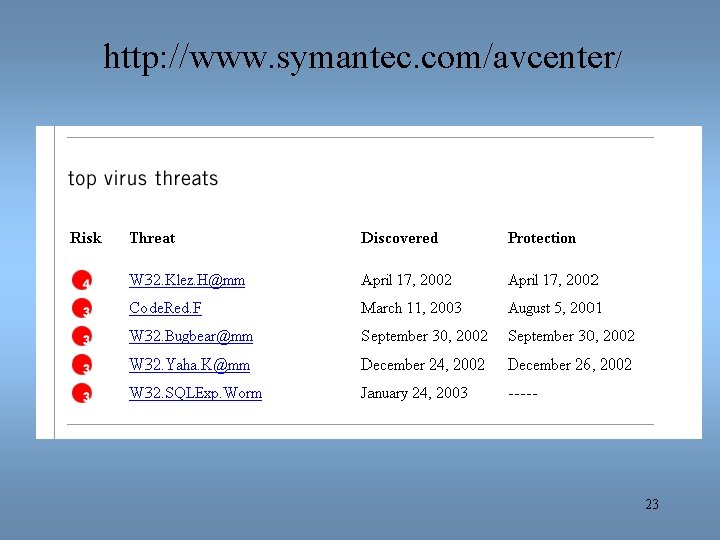
http: //www. symantec. com/avcenter/ 23
24
What is the difference between a computer virus and a computer worm? • Viruses are computer programs that are designed to spread themselves from one file to another on a single computer. A virus might rapidly infect every application file on an individual computer, or slowly infect the documents on that computer, but it does not intentionally try to spread itself from that computer to other computers. In most cases, that's where humans come in. We send e-mail document attachments, trade programs on diskettes, or copy files to file servers. When the next unsuspecting user receives the infected file or disk, they spread the virus to their computer, and so on. • Worms, on the other hand, are insidious because they rely less (or not at all) upon human behavior in order to spread themselves from one computer to others. • The computer worm is a program that is designed to copy itself from one computer to another over a network (e. g. by using e-mail). The worm spreads itself to many computers over a network, and doesn't wait for a human being to help. This means that computer worms spread much more rapidly than computer viruses. 25
HOAXES 26
Standard System Attacks Denial of service attacks, or distributed denial of service attacks, bombard a computer site with so many messages that the site is incapable of answering valid request. In e-mail bombing, a user sends an excessive amount of unwanted e-mail to someone. Smurfing is a nasty technique in which a program attacks a network by exploiting IP broadcast addressing operations. Ping storm is a condition in which the Internet Ping program is used to send a flood of packets to a server. 27
Standard System Attacks Spoofing is when a user creates a packet that appears to be something else or from someone else. Trojan Horse is a malicious piece of code hidden inside a seemingly harmless piece of code. Stealing, guessing, and intercepting passwords is also a tried and true form of attack. 28
Web Spoofing • Web Spoofing is a security attack that allows an adversary to observe and modify all web pages sent to the victim's machine, and observe all information entered into forms by the victim. Web Spoofing works on both of the major browsers and is not prevented by "secure" connections. The attacker can observe and modify all web pages and form submissions, even when the browser's "secure connection" indicator is lit. The user sees no indication that anything is wrong. • The attack is initiated when the victim visits a malicious Web page, or receives a malicious email message (if the victim uses an HTML-enabled email reader). 29
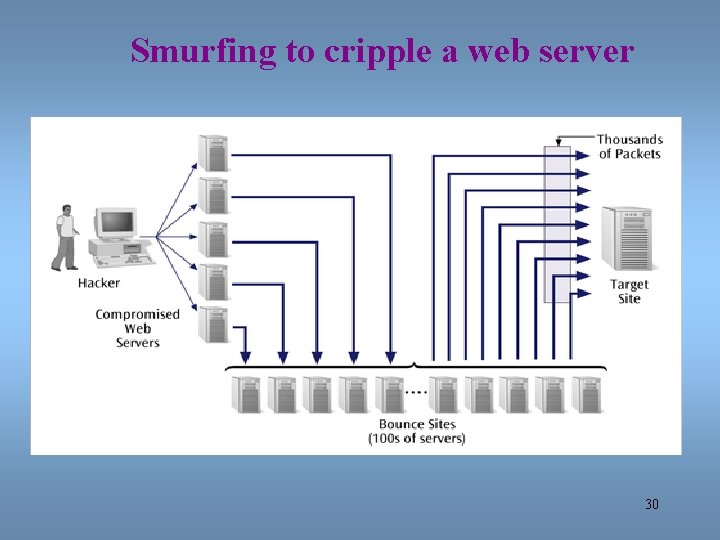
Smurfing to cripple a web server 30
Smurfing • Smurfing is the attacking of a network by exploiting Internet Protocol (IP) broadcast addressing and certain other aspects of Internet operation. Smurfing uses a program called Smurf and similar programs to cause the attacked part of a network to become inoperable. The exploit of smurfing, as it has come to be known, takes advantage of certain known characteristics of the Internet Protocol (IP) and the Internet Control Message Protocol (ICMP). The ICMP is used by network nodes and their administrators to exchange information about the state of the network. ICMP can be used to ping other nodes to see if they are operational. An operational node returns an echo message in response to a ping message. A smurf program builds a network packet that appears to originate from another address (this is known as spoofing an IP address). The packet contains an ICMP ping message that is addressed to an IP broadcast address, meaning all IP addresses in a given network. The echo responses to the ping message are sent back to the "victim" address. Enough pings and resultant echoes can flood the network making it unusable for real traffic. • One way to defeat smurfing is to disable IP broadcast addressing at each network router since it is seldom used. This is one of several suggestions provided by the CERT Coordination Center. 31
What is SSH? • SSH (Secure Shell) is a full replacement for rsh, rlogin, rcp, telnet, rexec, and ftp • Automatic authentication (? ) of users, no passwords are sent in clear text • Secure remote login, file copying, and tunneling X 11 and TCP connections (POP, IMAP, SMTP, HTTP) 32
www. cert. org 33
What is a firewall? • Used to control the flow of traffic (both inflows and outflows, but primarily inflows) between networks • The connected networks can be internal or a combination of internal and external networks 34
Firewalls A system or combination of systems that supports an access control policy between two networks. A firewall can limit the types of transactions that enter a system, as well as the types of transactions that leave a system. Firewalls can be programmed to stop certain types or ranges of IP addresses, as well as certain types of TCP port numbers (applications such as ftp, telnet, etc. ) 35
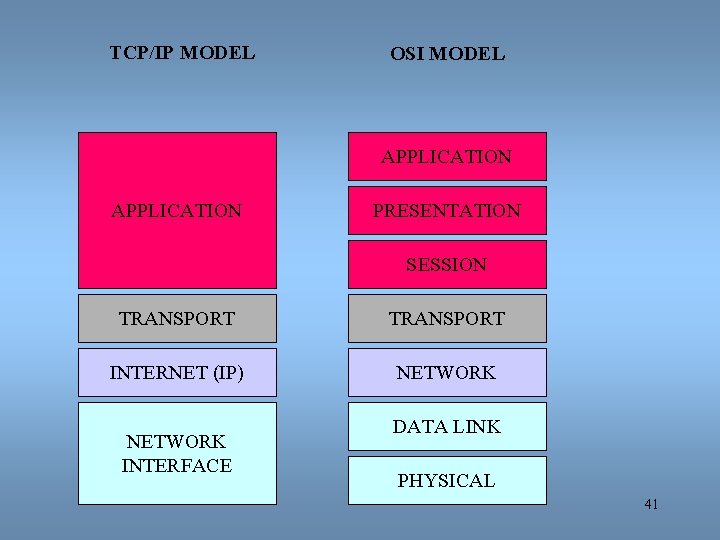
Transmission Control Protocol/ Internet Protocol - TCP/IP • A conglomeration of underlying protocols designed to enable communications between computers across networks 36
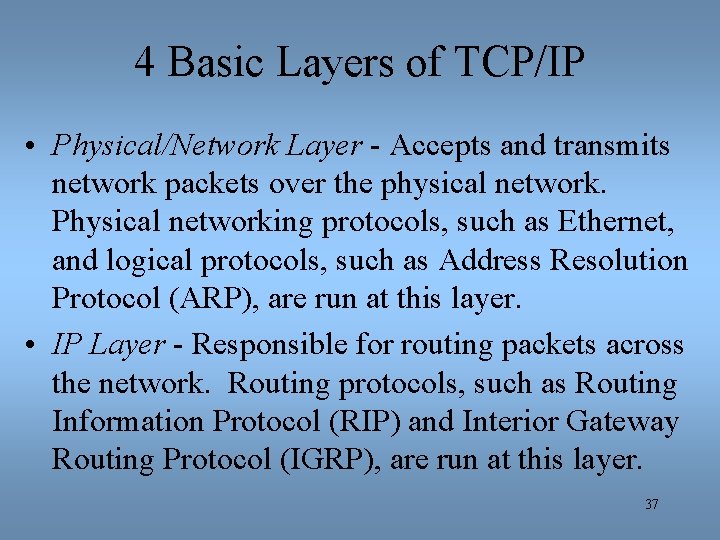
4 Basic Layers of TCP/IP • Physical/Network Layer - Accepts and transmits network packets over the physical network. Physical networking protocols, such as Ethernet, and logical protocols, such as Address Resolution Protocol (ARP), are run at this layer. • IP Layer - Responsible for routing packets across the network. Routing protocols, such as Routing Information Protocol (RIP) and Interior Gateway Routing Protocol (IGRP), are run at this layer. 37
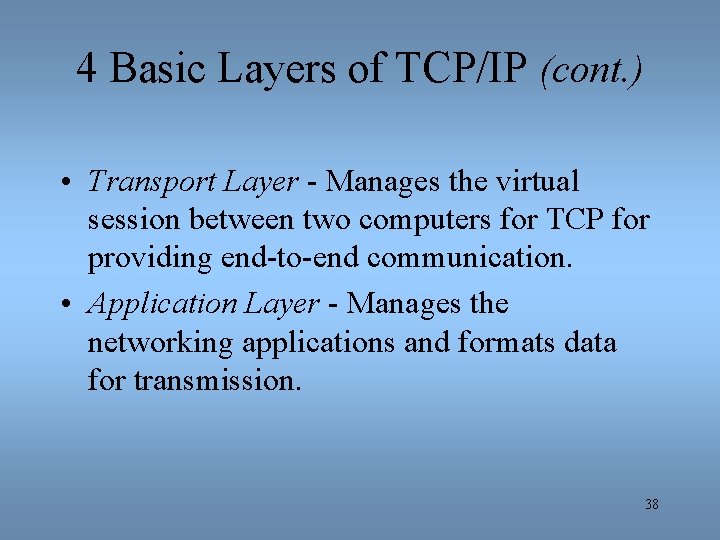
4 Basic Layers of TCP/IP (cont. ) • Transport Layer - Manages the virtual session between two computers for TCP for providing end-to-end communication. • Application Layer - Manages the networking applications and formats data for transmission. 38
Open Systems Interconnect (OSI) • Developed by the International Organization for Standardization • A seven layer model that further divides the layers from the TCP/IP model 39
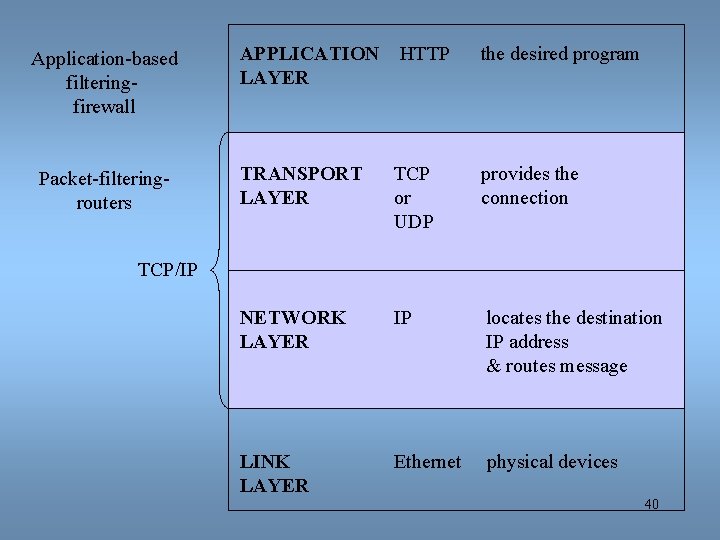
Application-based filteringfirewall Packet-filteringrouters APPLICATION LAYER HTTP the desired program TRANSPORT LAYER TCP or UDP provides the connection NETWORK LAYER IP locates the destination IP address & routes message LINK LAYER Ethernet physical devices TCP/IP 40
TCP/IP MODEL OSI MODEL APPLICATION PRESENTATION SESSION TRANSPORT INTERNET (IP) NETWORK INTERFACE DATA LINK PHYSICAL 41
Characteristics of Good Firewalls • All traffic from inside the corporate network to outside the network, and vice-versa, must pass through it; • Only authorized traffic, as defined by the security policy, is allowed to pass through it; and the system itself is immune to penetration. 42
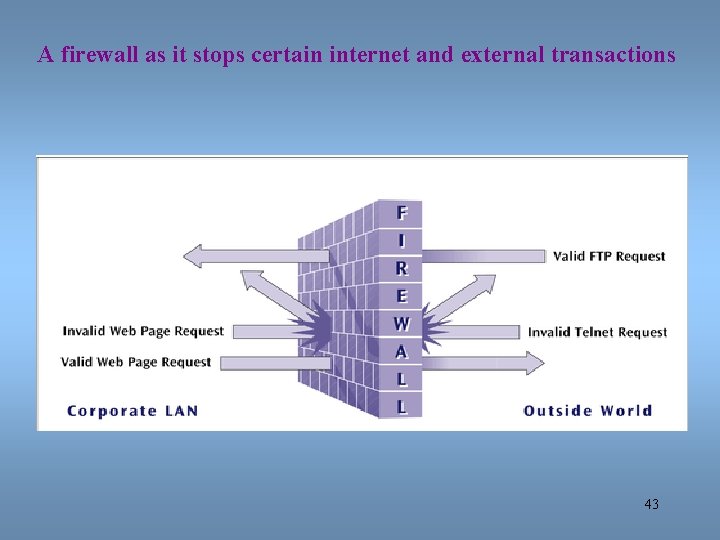
A firewall as it stops certain internet and external transactions 43
Firewalls – 2 types A packet filter firewall is essentially a router that has been programmed to filter out or allow to pass certain IP addresses or TCP port numbers. A proxy server is a more advanced firewall that acts as a doorman into a corporate network. Any external transaction that request something from the corporate network must enter through the proxy server. Proxy servers are more advanced but make external accesses slower. 44
Firewall Filtering • Firewall features that are standard on routers. – Separate input and output filters on: • Source and destination address • Protocol (TCP/IP, IPX, UDP, ICMP, RIP, OSPF, BGP) • Protocol service (Web, e-mail, FTP) • Established sessions – Packet logging – Extended Frame Relay filtering (variable-length packet switching data transmission) 45 www. lucent. com
Static Firewalls • Pre-configured rulebases are used for traffic passing decisions • Default permit - the firewall allows all traffic except that which is explicitly blocked by the firewall rulebase • Default deny - the firewall denies all traffic except that which is explicitly allowed by the firewall rulebase 46
Dynamic Firewalls • Also uses rulebases, but the denial and permission of any service can be established for a given time period • Stateful inspection is also a dynamic configuration – A stateful inspection firewall also monitors the state of the connection and compiles the information in a state table. Because of this, filtering decisions are based not only on administrator-defined rules (as in static packet filtering) but also on context that has been established by prior packets that have passed through the firewall. 47
Components of Firewalls • Chokes - limit the flow of packets between networks. Read packets and determine, based on the rules, if the traffic should pass • Gates - act as a control point for external connections. They control the external connections. 48
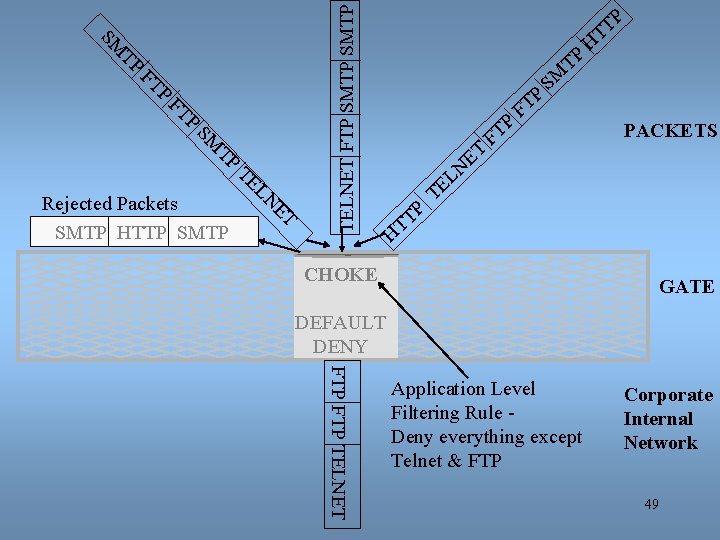
P FT FT P TP SM ET LN TE TELNET FTP SMTP TP SM Rejected Packets SMTP HTTP SMTP ET LN P T T P T F SM TP P T T H PACKETS TE H CHOKE GATE DEFAULT DENY FTP TELNET Application Level Filtering Rule Deny everything except Telnet & FTP Corporate Internal Network 49
Firewall Functions • • • Packet Filtering Network Address Translation Application-level Proxies Stateful Inspection Virtual Private Networks Real-time Monitoring 50
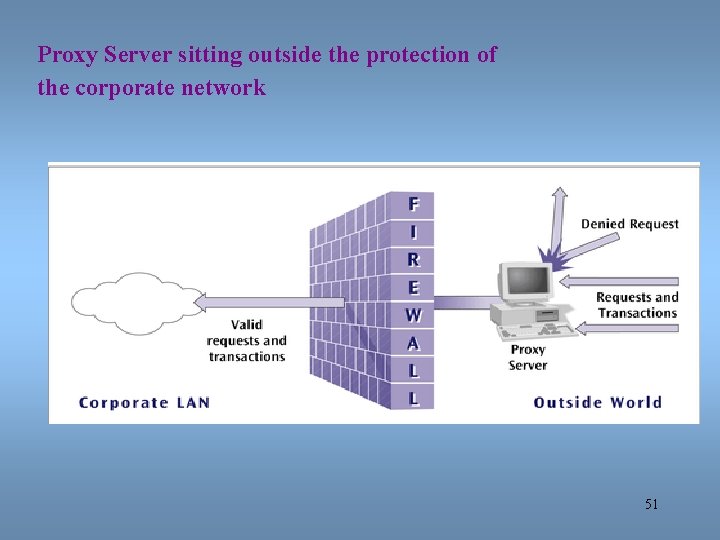
Proxy Server sitting outside the protection of the corporate network 51
Last time • Security issues • Firewalls This time • Business over the internet • Cryptography 52
So you want to do business over the internet • What do you have to worry about? 53
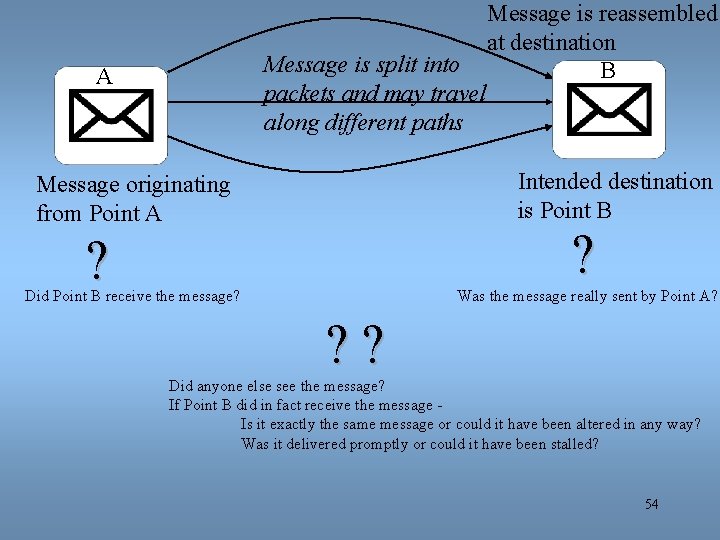
Message is split into packets and may travel along different paths A Message is reassembled at destination B Intended destination is Point B Message originating from Point A ? ? Did Point B receive the message? Was the message really sent by Point A? ? ? Did anyone else see the message? If Point B did in fact receive the message Is it exactly the same message or could it have been altered in any way? Was it delivered promptly or could it have been stalled? 54
Important Techniques used to prevent/detect data interception • Message Origin Authentication • Proof of Delivery (non-repudiation) • Message Integrity – Same message – Not seen by others • Timely Delivery of Messages 55
Encryption…. • Is the best device for ensuring message (and data) confidentiality • involves transforming plaintext into ciphertext using a KEY • the level of secrecy is a function of – strength of the algorithm – key length – key management policies 56
What is cryptography? • “hidden writing” – versus steganography (hiding the message) • Until recently: military tool • Like any military technology: methods change over time • Two sides: designing codes breaking codes (cryptanalysis) • Computers have changed both
Basic Encryption and Decryption Terms Cryptography is the study of creating and using encryption and decryption techniques. Encryption vs decryption Plaintext (sometimes called cleartext) is the data that exists before any encryption has been performed. Ciphertext is the data after encryption has been performed. The key(s) is(are) the unique piece of information that is used to create ciphertext and decrypt the ciphertext back into plaintext. Key is also called the cryptovariable. The cipher is the algorithm for encrypting and decrypting; also called the protocol or scheme. 58
Uses of Cryptography • Besides confidentiality, cryptography provides – Authentication: knowing who sent the message actually sent it. – Integrity: message has not been tampered with and/or the message is legit – Nonrepudiation: a user should not be able to deny that he sent the message 59
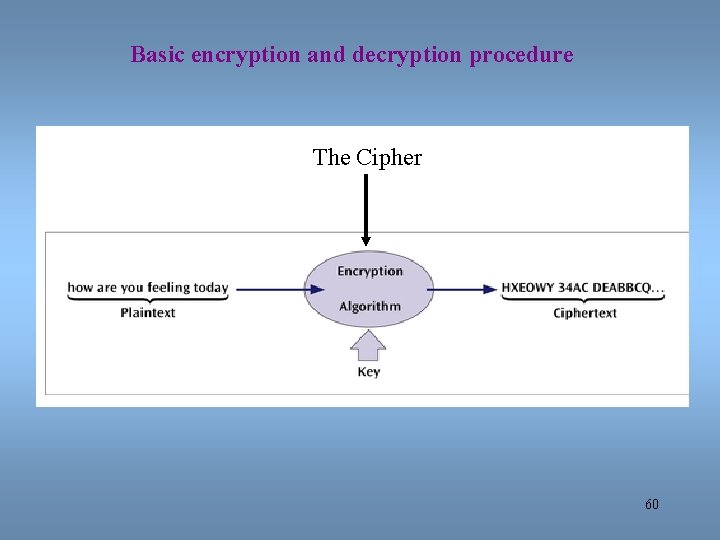
Basic encryption and decryption procedure The Cipher 60
Simple encryption methods • Pig Latin • Decoder rings 61
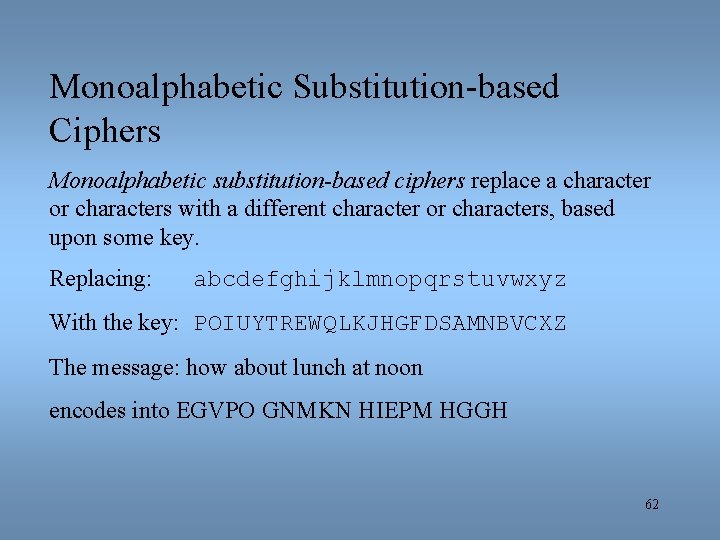
Monoalphabetic Substitution-based Ciphers Monoalphabetic substitution-based ciphers replace a character or characters with a different character or characters, based upon some key. Replacing: abcdefghijklmnopqrstuvwxyz With the key: POIUYTREWQLKJHGFDSAMNBVCXZ The message: how about lunch at noon encodes into EGVPO GNMKN HIEPM HGGH 62
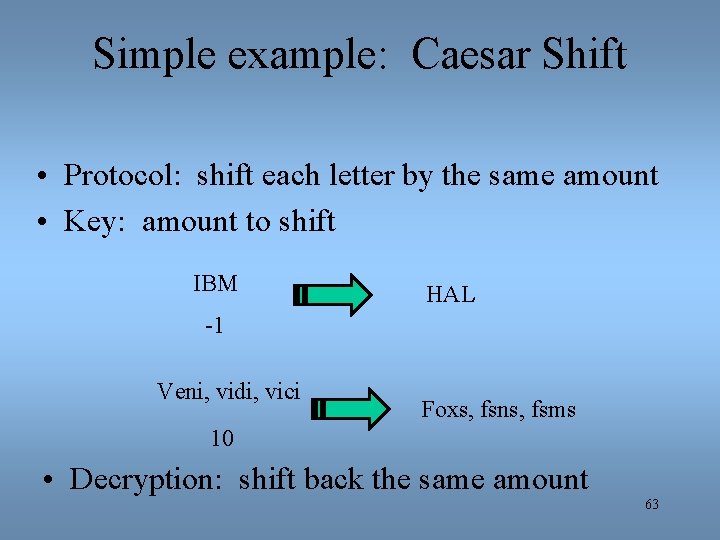
Simple example: Caesar Shift • Protocol: shift each letter by the same amount • Key: amount to shift IBM HAL -1 Veni, vidi, vici Foxs, fsns, fsms 10 • Decryption: shift back the same amount 63
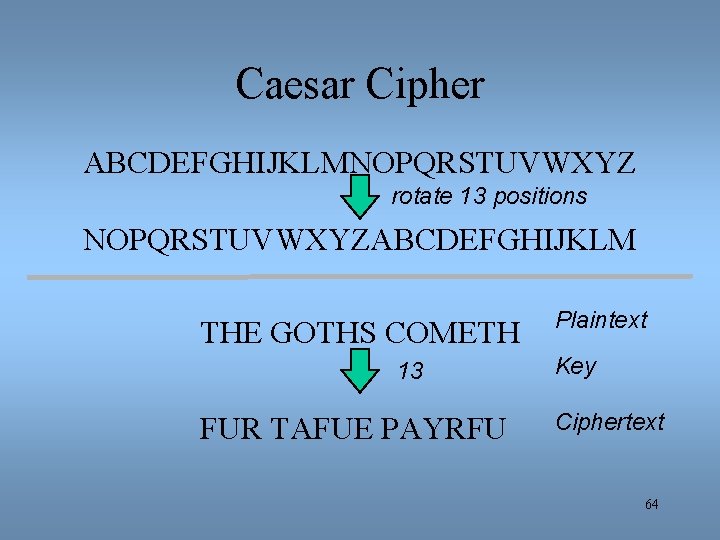
Caesar Cipher ABCDEFGHIJKLMNOPQRSTUVWXYZ rotate 13 positions NOPQRSTUVWXYZABCDEFGHIJKLM THE GOTHS COMETH 13 FUR TAFUE PAYRFU Plaintext Key Ciphertext 64
Example: Caesar Shift • What is: – ozqsx shld 65
Types of Keys • Symmetric (one key) • Asymmetric (two keys) 70
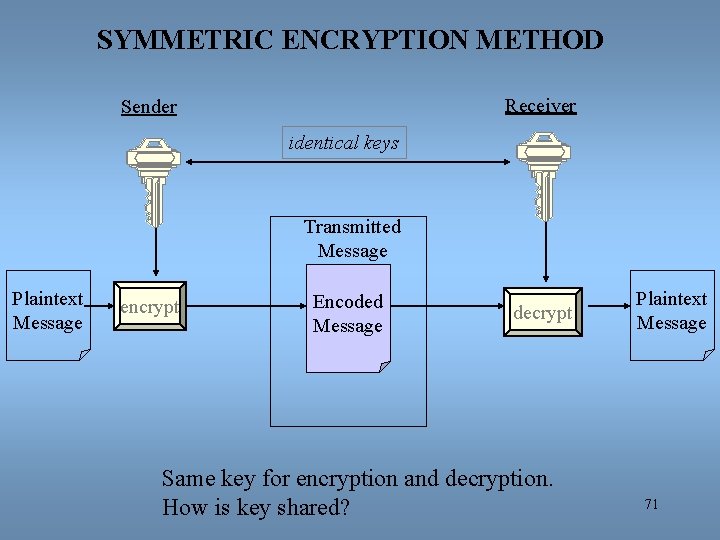
SYMMETRIC ENCRYPTION METHOD Receiver Sender identical keys Transmitted Message Plaintext Message encrypt Encoded Message decrypt Same key for encryption and decryption. How is key shared? Plaintext Message 71
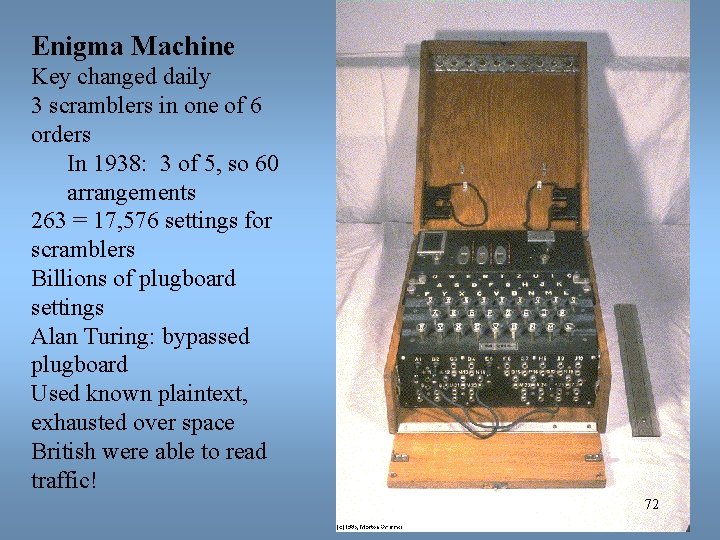
Enigma Machine Key changed daily 3 scramblers in one of 6 orders In 1938: 3 of 5, so 60 arrangements 263 = 17, 576 settings for scramblers Billions of plugboard settings Alan Turing: bypassed plugboard Used known plaintext, exhausted over space British were able to read traffic! 72
Paradigm Shift! • • Alice wants to mail Bob a letter securely If they share a “key”, Alice locks, Bob unlocks If not: Alice puts on padlock, sends box to Bob adds his padlock, sends box back to Alice removes her padlock, sends box to Bob unlocks box, reads letter Problem: how to translate this to a protocol? 73
Public Key Cryptography Very powerful encryption technique in which two keys are used: • first key (the public key) encrypts the message • second key (the private key) decrypts the message Not possible to deduce one key from the other. Not possible to break the code given the public key. If you want someone to send you secure data, give them your public key, you keep the private key. Secure sockets layer (SSL) on the Internet is a common example of public key cryptography Connection between application layer and transport layer (TCP) S-HTTP another method 74
75
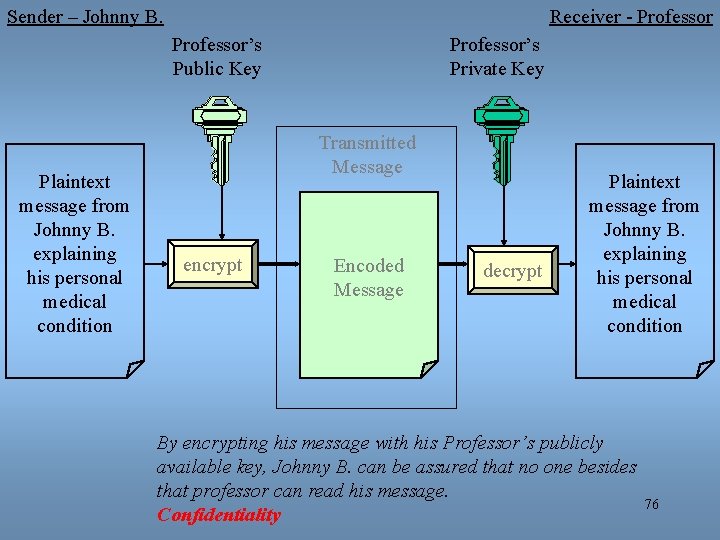
Sender – Johnny B. Receiver - Professor’s Public Key Plaintext message from Johnny B. explaining his personal medical condition Professor’s Private Key Transmitted Message encrypt Encoded Message decrypt Plaintext message from Johnny B. explaining his personal medical condition By encrypting his message with his Professor’s publicly available key, Johnny B. can be assured that no one besides that professor can read his message. Confidentiality 76
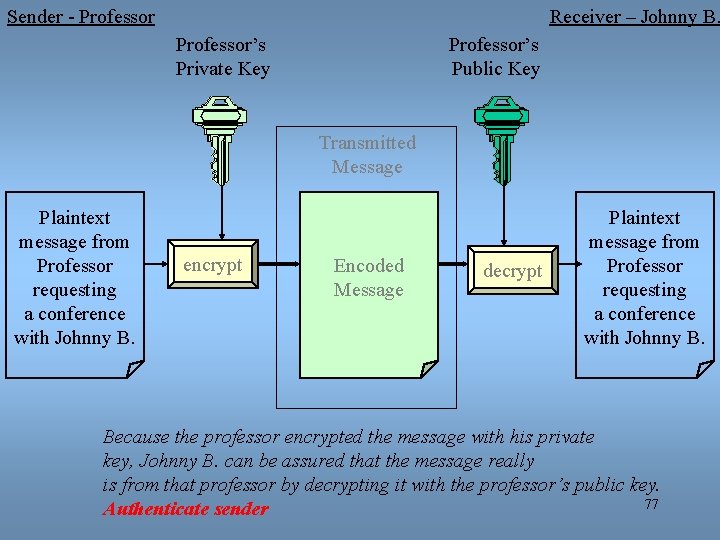
Sender - Professor Receiver – Johnny B. Professor’s Private Key Professor’s Public Key Transmitted Message Plaintext message from Professor requesting a conference with Johnny B. encrypt Encoded Message decrypt Plaintext message from Professor requesting a conference with Johnny B. Because the professor encrypted the message with his private key, Johnny B. can be assured that the message really is from that professor by decrypting it with the professor’s public key. 77 Authenticate sender
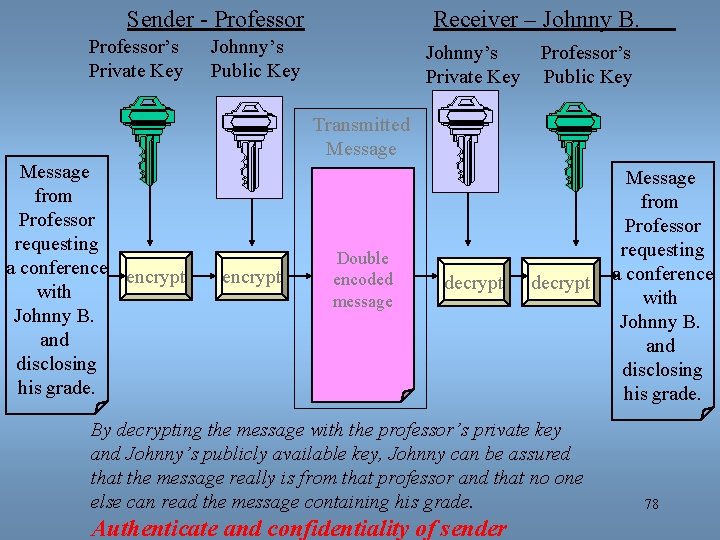
Sender - Professor’s Private Key Receiver – Johnny B. Johnny’s Public Key Johnny’s Private Key Professor’s Public Key Transmitted Message from Professor requesting a conference encrypt with Johnny B. and disclosing his grade. encrypt Double encoded message decrypt By decrypting the message with the professor’s private key and Johnny’s publicly available key, Johnny can be assured that the message really is from that professor and that no one else can read the message containing his grade. Authenticate and confidentiality of sender Message from Professor requesting a conference with Johnny B. and disclosing his grade. 78
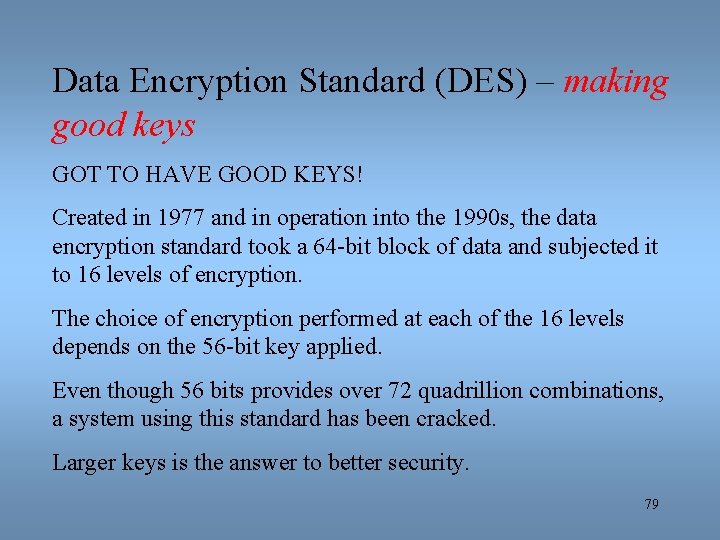
Data Encryption Standard (DES) – making good keys GOT TO HAVE GOOD KEYS! Created in 1977 and in operation into the 1990 s, the data encryption standard took a 64 -bit block of data and subjected it to 16 levels of encryption. The choice of encryption performed at each of the 16 levels depends on the 56 -bit key applied. Even though 56 bits provides over 72 quadrillion combinations, a system using this standard has been cracked. Larger keys is the answer to better security. 79
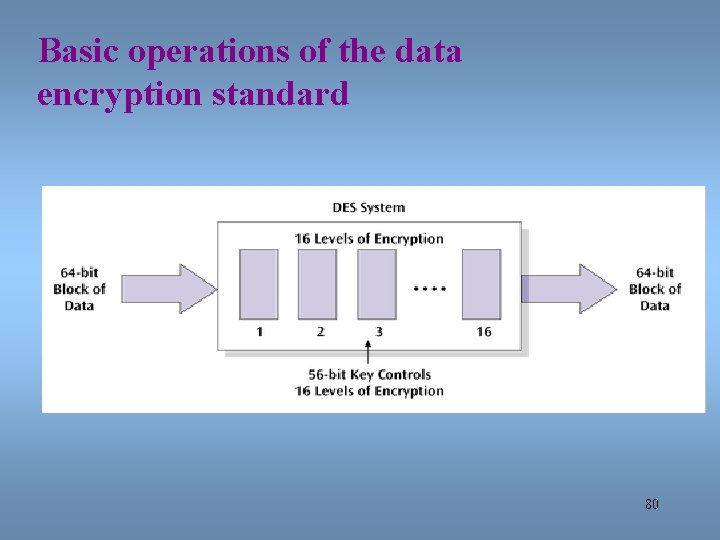
Basic operations of the data encryption standard 80
Triple-DES A more powerful data encryption standard. Data is encrypted using DES three times: the first time by the first key, the second time by a second key, and the third time by the first key again. While virtually unbreakable, triple-DES is CPU intensive. With more smart cards, cell phones, and PDAs, a faster (and smaller) piece of code is highly desirable. 81
Advanced Encryption Standard (AES) Selected by the U. S. government to replace DES. National Institute of Standards and Technology selected the algorithm Rijndael (pronounced rain-doll) in October 2000 as the basis for AES has more elegant mathematical formulas, requires only one pass, and was designed to be fast, unbreakable, and able to support even the smallest computing device. Key size of AES: 128, 192, or 256 bits Estimated time to crack (assuming one machine could try 255 keys per second (NIST)) : 149 trillion years Very fast execution with very good use of resources AES should be widely implemented by 2004 82
83
• PGP is a digital data encryption program created by Phil Zimmerman. • Provides confidentiality, authentication, and compression for email and data storage. • Its building blocks are made of the best available cryptographic algorithms: RSA, DSS, Diffie. Hellman. • It is independent of operating system and processor. • It has a small set of easy-to-use commands 84
PGP • Because PGP is freely available via the Internet, and has a fully compatible low-cost commercial version it is now widely used. • It has a wide range of applicability from corporations to individuals who wish to communicate worldwide securely over the Internet and other networks. • It is not controlled by any government which makes it attractive to many. 85
Digital Signatures • A digital signature is much like a hand signature in that it provides proof that you are the originator of the message (Authentication); assigns a code to a document. • Used to bound the message originator with the exact contents of the message through the use of key pairs. This allows for the feature of non-repudiation to be achieved this is crucial for electronic commerce. • Non-repudiation is a property achieved through cryptographic methods which prevents an individual or entity from denying having performed a particular action related to data. • The private key of the sender is used to compute a message digest. 86
Digital Signatures Reason for digital signatures? integrity of transactions How they work: Document to be signed is sent through a complex mathematical computation that generates a hash, called the message digest. (reduces the size of the message) Hash is encoded with the owner’s private key. To prove future ownership, the hash is decoded using the owner’s public key and the hash is compared with a current hash of the document. If the two hashes agree, the document belongs to the owner. The U. S. A. approved legislation to accept digitally signed documents as legal proof. 87
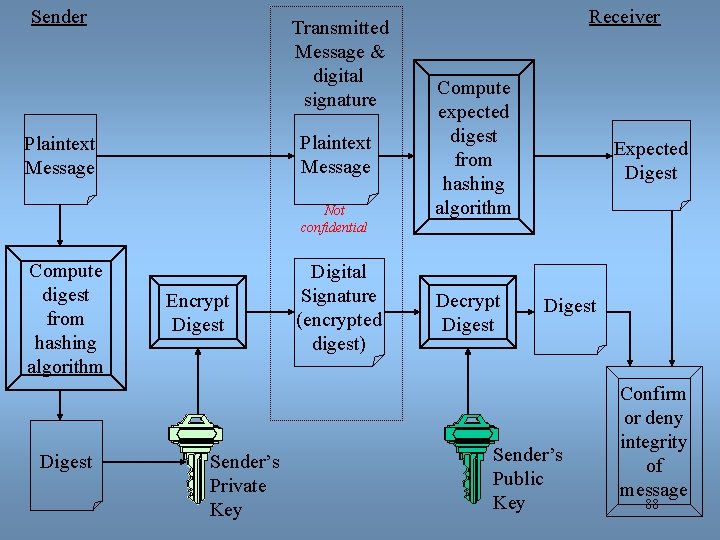
Sender Transmitted Message & digital signature Plaintext Message Not confidential Compute digest from hashing algorithm Digest Encrypt Digest Sender’s Private Key Digital Signature (encrypted digest) Receiver Compute expected digest from hashing algorithm Decrypt Digest Expected Digest Sender’s Public Key Confirm or deny integrity of message 88
Public Key Infrastructure Putting it all together!! The combination of encryption techniques, software, and services that involves all the necessary pieces to support digital certificates, certificate authorities, and public key generation, storage, and management. A certificate, or digital certificate, is an electronic document, similar to a passport, that establishes your credentials when you are performing transactions. 89
Public Key Infrastructure (PKI) Applications that benefit from PKI: • World Wide Web transactions • Virtual private networks • Electronic mail • Client-server applications • Banking transactions 90
Security Policy Design Issues What is the company’s desired level of security? How much money is the company willing to invest in security? If the company is serious about restricting access through an Internet link, what about restricting access through all other entry ways? The company must have a well-designed security policy. 91
Network Security In Action: Banking and PKI If you want to perform online banking transactions, how does the system know you are a legitimate user? Scotia. Bank uses a PKI system designed by Entrust. Each customer is assigned a digital certificate. Whenever a customer wants to perform an online transaction, they “present” their certificate. 92
What did we cover? • Security for internet communications – Message Origin Authentication – Proof of Delivery (non-repudiation) – Message Integrity • Same message • Not seen by others • Cryptography – Keys – PKI 93
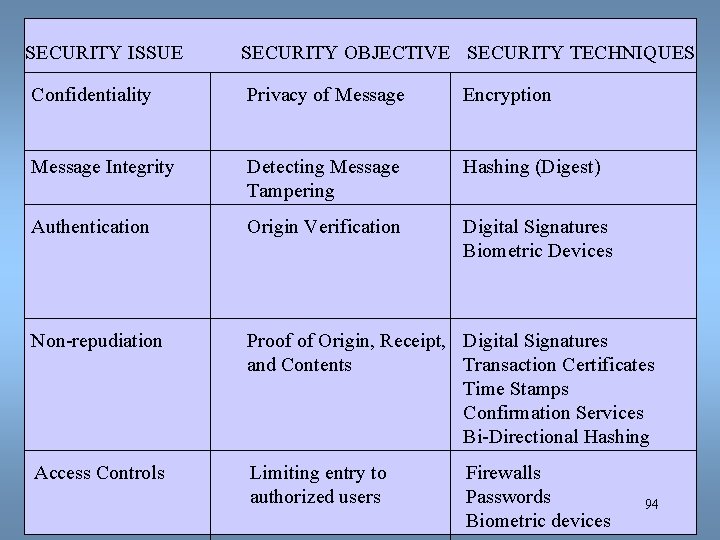
SECURITY ISSUE SECURITY OBJECTIVE SECURITY TECHNIQUES Confidentiality Privacy of Message Encryption Message Integrity Detecting Message Tampering Hashing (Digest) Authentication Origin Verification Digital Signatures Biometric Devices Non-repudiation Proof of Origin, Receipt, Digital Signatures and Contents Transaction Certificates Time Stamps Confirmation Services Bi-Directional Hashing Access Controls Limiting entry to authorized users Firewalls Passwords Biometric devices 94
- Slides: 90