Data breaches Shocking numbers from the 2009 Data
Data breaches Shocking numbers from the 2009 Data Breach Report Matthijs van der Wel MBA CISSP® CISA® RON® QSA® QFI® Managing Principle Forensics EMEA © 2009 Verizon. All Rights Reserved. PTEXXXXX XX/09
7 types of intel • External Threat & Vulnerability Data - We continuously track new vulnerabilities and related attacks to assess how they impact information risk. • Underground Intelligence - Surveillance of numerous online groups help us know what the bad guys are discussing, sharing, planning and doing. • Net Intelligence - Over one million sensors are dispersed throughout our Internet backbone, enabling us to gather information on nefarious activity around the globe. • Managed Security Services - Verizon Business manages and monitors firewalls, IDS, IPS, and other network devices for many of the world’s largest companies. • Global Services - Internal data collection across Verizon’s extensive range of IT and security services. This is “real-world” data harvested as a byproduct of delivery. • Investigative Response – Forensics & computer crime Investigations. Extensive metrics are systematically recorded on hundreds of data breach cases per year. • ICSA Labs - ICSA Labs, an independent division of Verizon Business, performs vendorneutral testing of hundreds of security products.
WARNING: This is a true story. Based upon actual events. URL - http: //www. verizonbusiness. com/databreach/ Blog - http: //securityblog. verizonbusiness. com/ © 2009 Verizon. All Rights Reserved. PTEXXXXX XX/09
IR Case Data • All data collected during cases worked by the Verizon Business • Investigative Response team during 2008 • Objective, credible, first-hand information on actual breaches • 2008 Caseload: • 90 confirmed breaches (>150 total engagements) • 285 million compromised records (confirmed – not “data-at-risk”) • 1/3 of these cases have been publicly disclosed (so far) • About 50% of caseload comprised of sets of interrelated incidents – Same attacker(s), shared connections, identical circumstances, etc • 15 arrests (and counting) • 31% Retail, 30% Financial, 14% Food & Bev, remaining mixed • Over 1/3 of investigations conducted outside the US
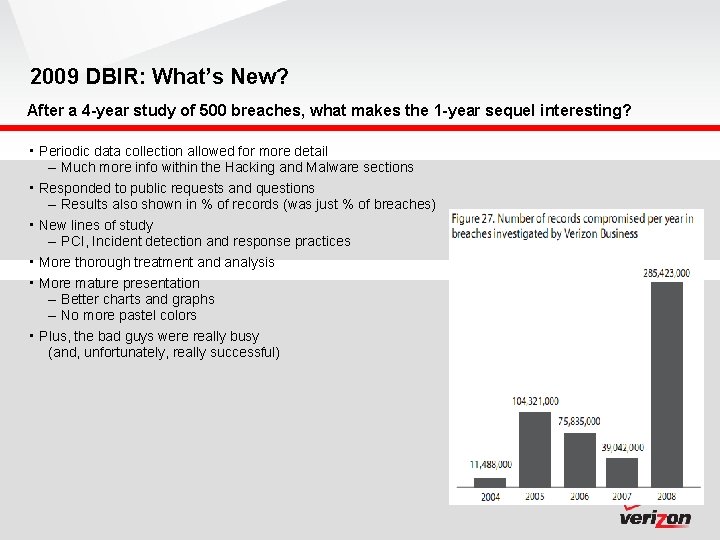
2009 DBIR: What’s New? After a 4 -year study of 500 breaches, what makes the 1 -year sequel interesting? • Periodic data collection allowed for more detail – Much more info within the Hacking and Malware sections • Responded to public requests and questions – Results also shown in % of records (was just % of breaches) • New lines of study – PCI, Incident detection and response practices • More thorough treatment and analysis • More mature presentation – Better charts and graphs – No more pastel colors • Plus, the bad guys were really busy (and, unfortunately, really successful)
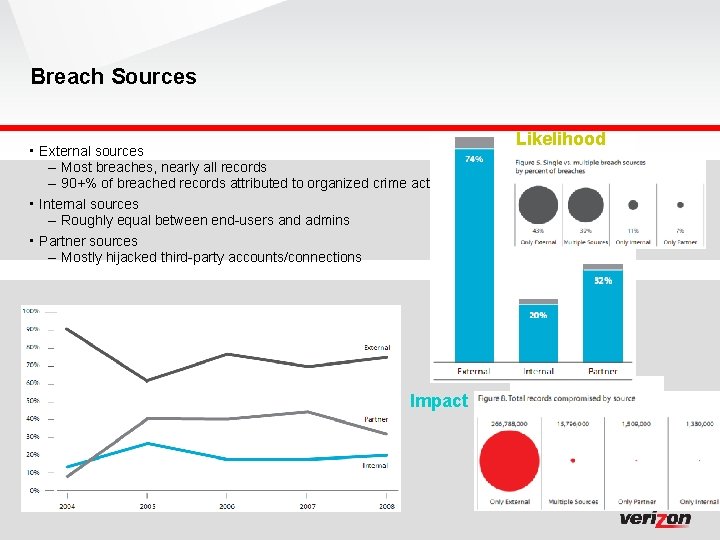
Breach Sources • External sources – Most breaches, nearly all records – 90+% of breached records attributed to organized crime activity • Internal sources – Roughly equal between end-users and admins • Partner sources – Mostly hijacked third-party accounts/connections Impact Likelihood
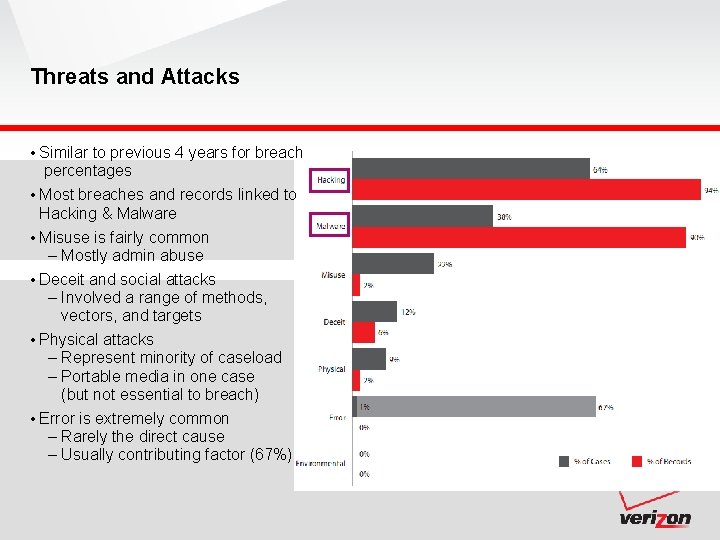
Threats and Attacks • Similar to previous 4 years for breach percentages • Most breaches and records linked to Hacking & Malware • Misuse is fairly common – Mostly admin abuse • Deceit and social attacks – Involved a range of methods, vectors, and targets • Physical attacks – Represent minority of caseload – Portable media in one case (but not essential to breach) • Error is extremely common – Rarely the direct cause – Usually contributing factor (67%)
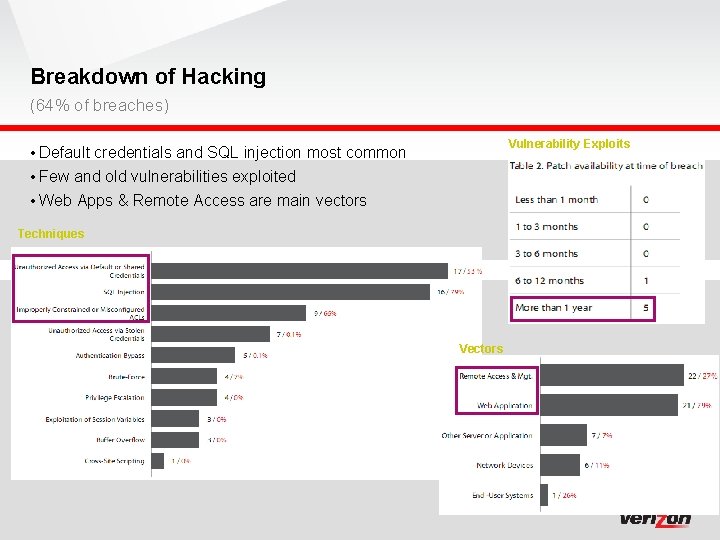
Breakdown of Hacking (64% of breaches) Vulnerability Exploits • Default credentials and SQL injection most common • Few and old vulnerabilities exploited • Web Apps & Remote Access are main vectors Techniques Vectors
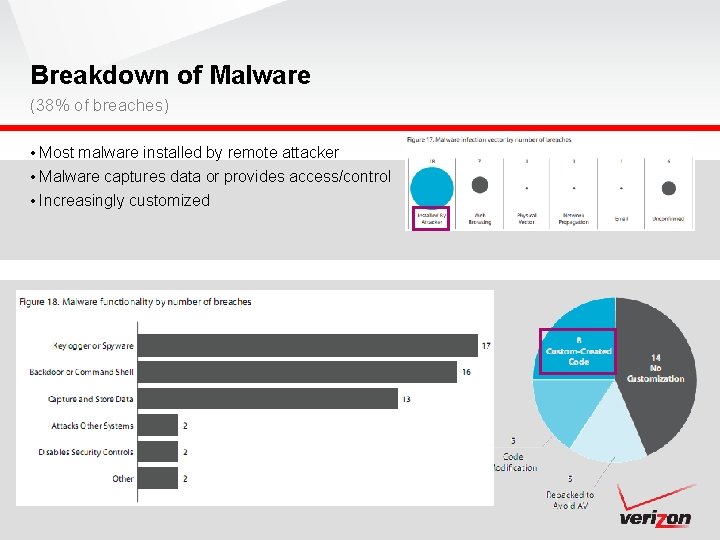
Breakdown of Malware (38% of breaches) • Most malware installed by remote attacker • Malware captures data or provides access/control • Increasingly customized
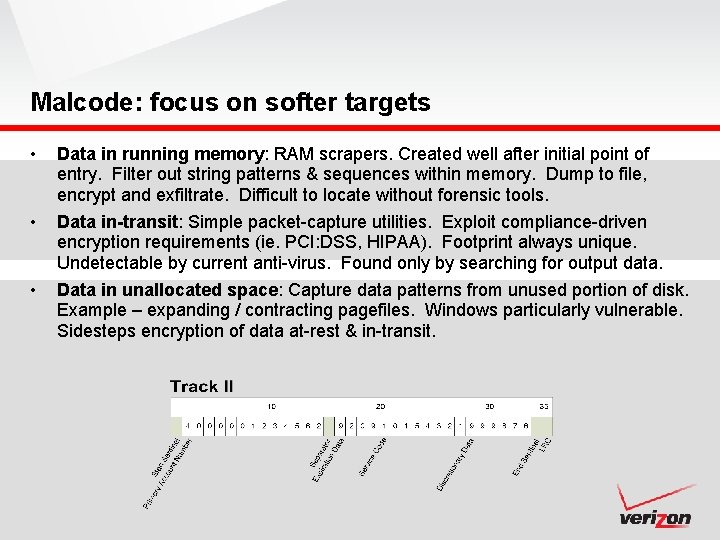
Malcode: focus on softer targets • Data in running memory: RAM scrapers. Created well after initial point of entry. Filter out string patterns & sequences within memory. Dump to file, encrypt and exfiltrate. Difficult to locate without forensic tools. • Data in-transit: Simple packet-capture utilities. Exploit compliance-driven encryption requirements (ie. PCI: DSS, HIPAA). Footprint always unique. Undetectable by current anti-virus. Found only by searching for output data. Data in unallocated space: Capture data patterns from unused portion of disk. Example – expanding / contracting pagefiles. Windows particularly vulnerable. Sidesteps encryption of data at-rest & in-transit. •
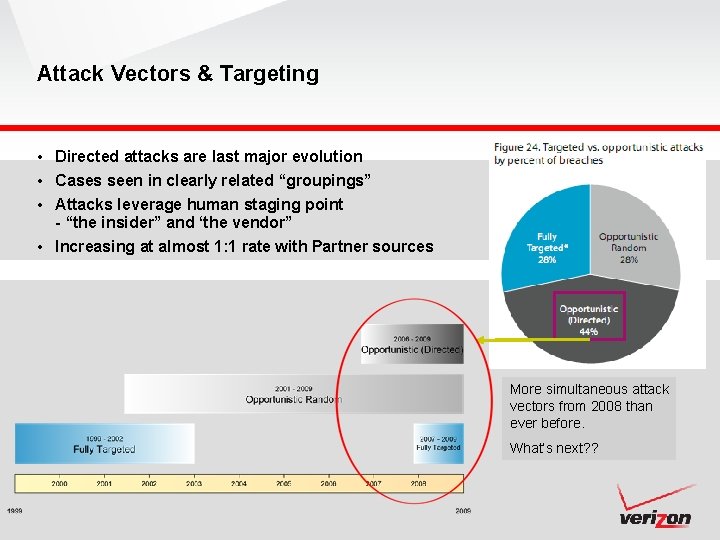
Attack Vectors & Targeting • Directed attacks are last major evolution • Cases seen in clearly related “groupings” • Attacks leverage human staging point - “the insider” and ‘the vendor” • Increasing at almost 1: 1 rate with Partner sources More simultaneous attack vectors from 2008 than ever before. What’s next? ?
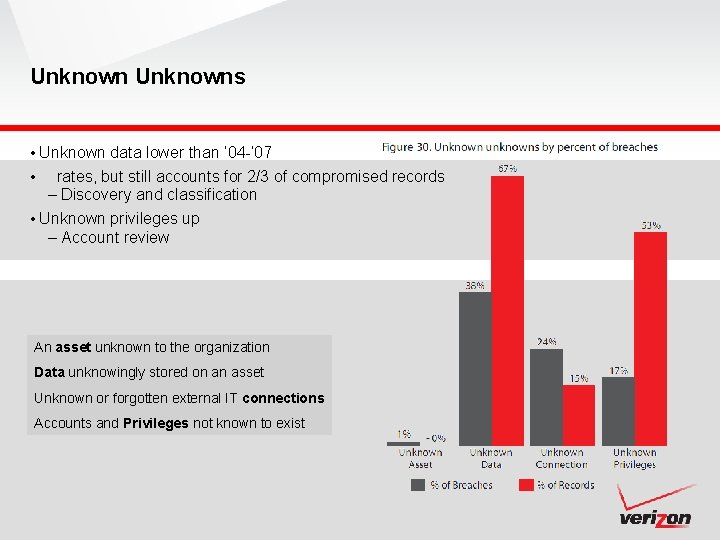
Unknowns • Unknown data lower than ’ 04 -’ 07 • rates, but still accounts for 2/3 of compromised records – Discovery and classification • Unknown privileges up – Account review An asset unknown to the organization Data unknowingly stored on an asset Unknown or forgotten external IT connections Accounts and Privileges not known to exist
Recommendations • Recap from previous report • (They still apply) • Align process with policy • Achieve “Essential” then worry about “Excellent” • Secure Business Partner Connections • Create a Data Retention Plan • Control data with transaction zones • Monitor event logs • Create an Incident Response Plan • Increase awareness • Engage in mock incident testing
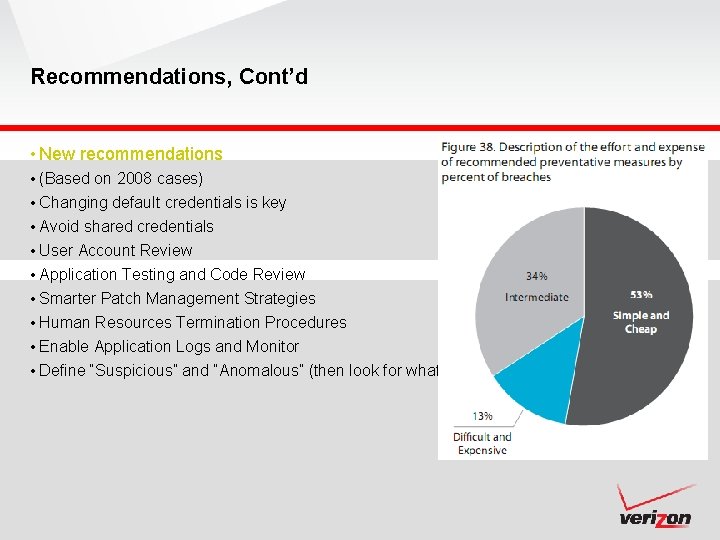
Recommendations, Cont’d • New recommendations • (Based on 2008 cases) • Changing default credentials is key • Avoid shared credentials • User Account Review • Application Testing and Code Review • Smarter Patch Management Strategies • Human Resources Termination Procedures • Enable Application Logs and Monitor • Define “Suspicious” and “Anomalous” (then look for whatever “It” is)
Summary • 2008 saw much of the same, but new twists and trends were observed • Sources: Similar distribution; organized crime behind most large breaches – Organized criminal groups driving evolution of cybercrime • Attacks: Criminals exploit errors, hack into systems, install malware – 2008 saw more targeted attacks, especially against orgs processing or storing large volumes of desirable data – Highly difficult attacks not common but very damaging – Large increase in customized, intelligent malware • Assets and Data: Focus is online cashable data – Nearly all breached from servers & apps – New data types (PIN data) sought which requires new techniques and targets • Discovery: Takes months and is accomplished by 3 rd parties • Prevention: The basics–if done consistently–are effective in most cases – Increasing divergence between Targets of Opportunity and Targets of Choice » To. O: Remove blatant opportunities through basic controls » To. C: Same as above but prepare for very determined, very skilled attacks – Initial hack appears the easiest point of control

Questions?
In case of an incident, please call our worldwide 24/7 Incident Response Hotline: +1. 866. 912. 6565 18 18
- Slides: 17