Data Breaches Isaac Straley Chief Information Security Officer
Data Breaches Isaac Straley Chief Information Security Officer – Risk and Compliance UC Irvine Office of Information Technology 1
Top Risks Phishing / Stolen Credentials Out of date software (please patch!) Third party (“cloud”) service misconfiguration 2
Phishing scam compromises data on 25, 000 individuals at University of Alaska A phishing scam in December 2016 resulted in a data breach at the University of Alaska, affecting around 25, 000 students, staff and faculty members, according to a report on Wednesday by local Anchorage NBC affiliate KTUU. A university letter sent to affected individuals and subsequently published by KTUU stated that the breach exposed names and corresponding social security numbers, after a hacker stole an employee's user name and password and potentially gained access to several sensitive accounts. The letter was sent in April 2017, four months after the incident took place. Links https: //www. scmagazine. com/phishing-scam-compromises-data-on-25000 -individuals-at-university-ofalaska/article/665470/ http: //www. ktuu. com/content/news/University-of-Alaska-thousands-affected-by-data-breach-including-socialsecurity-information-425538543. html 3
Children’s Mercy Hospital notifies parents after physician error exposes health information of 5, 500 patients Children’s Mercy’s information security department recently discovered an unauthorized website that contained certain patient information. The information had been collected by one of the hospital’s physicians who was using the website in an effort to create an educational resource. Although the physician believed that all individual information contained in the website was password protected and inaccessible, unfortunately the website’s security controls did not meet the hospital’s standards and the information could have been accessed by unauthorized third parties. Promptly following discovery, Children’s Mercy took down the website… Link – https: //www. databreaches. net/childrens-mercy-hospital-notifies-parents-after-physician-error-exposes-health -information/ 4
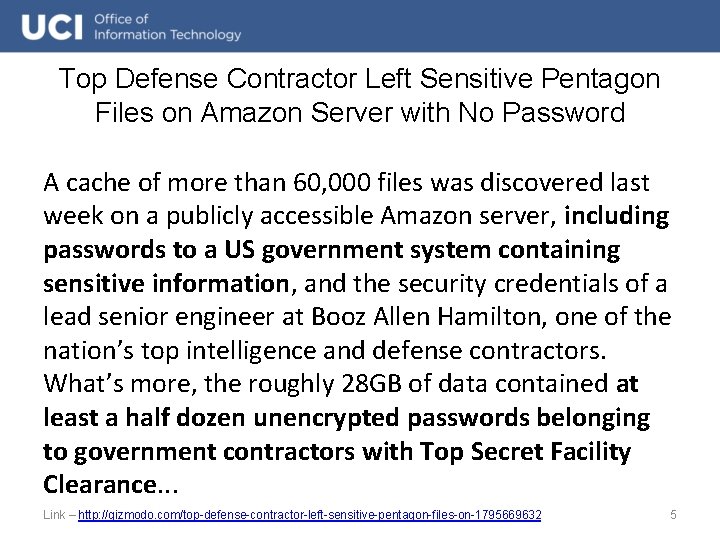
Top Defense Contractor Left Sensitive Pentagon Files on Amazon Server with No Password A cache of more than 60, 000 files was discovered last week on a publicly accessible Amazon server, including passwords to a US government system containing sensitive information, and the security credentials of a lead senior engineer at Booz Allen Hamilton, one of the nation’s top intelligence and defense contractors. What’s more, the roughly 28 GB of data contained at least a half dozen unencrypted passwords belonging to government contractors with Top Secret Facility Clearance. . . Link – http: //gizmodo. com/top-defense-contractor-left-sensitive-pentagon-files-on-1795669632 5
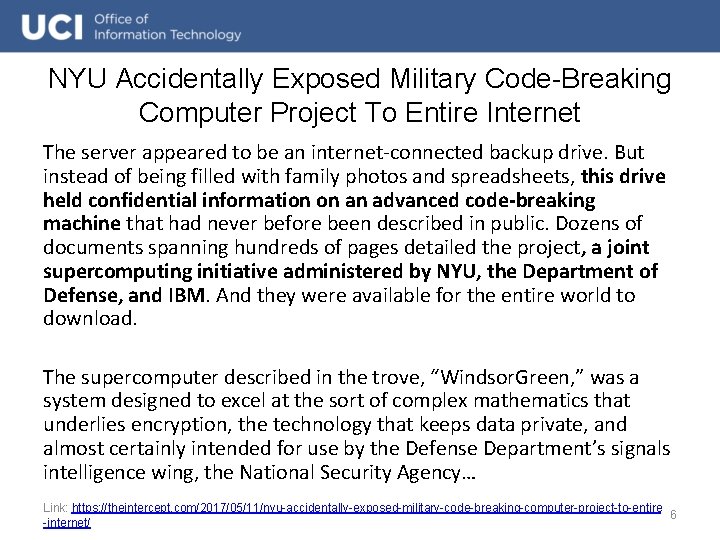
NYU Accidentally Exposed Military Code-Breaking Computer Project To Entire Internet The server appeared to be an internet-connected backup drive. But instead of being filled with family photos and spreadsheets, this drive held confidential information on an advanced code-breaking machine that had never before been described in public. Dozens of documents spanning hundreds of pages detailed the project, a joint supercomputing initiative administered by NYU, the Department of Defense, and IBM. And they were available for the entire world to download. The supercomputer described in the trove, “Windsor. Green, ” was a system designed to excel at the sort of complex mathematics that underlies encryption, the technology that keeps data private, and almost certainly intended for use by the Defense Department’s signals intelligence wing, the National Security Agency… Link: https: //theintercept. com/2017/05/11/nyu-accidentally-exposed-military-code-breaking-computer-project-to-entire 6 -internet/
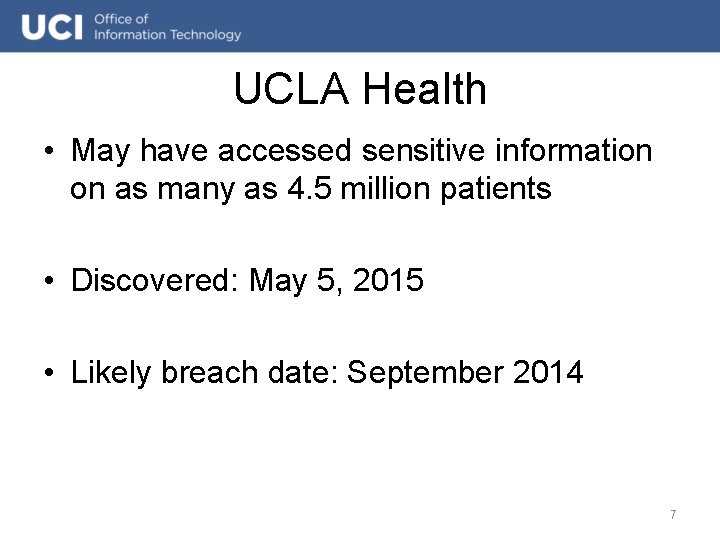
UCLA Health • May have accessed sensitive information on as many as 4. 5 million patients • Discovered: May 5, 2015 • Likely breach date: September 2014 7
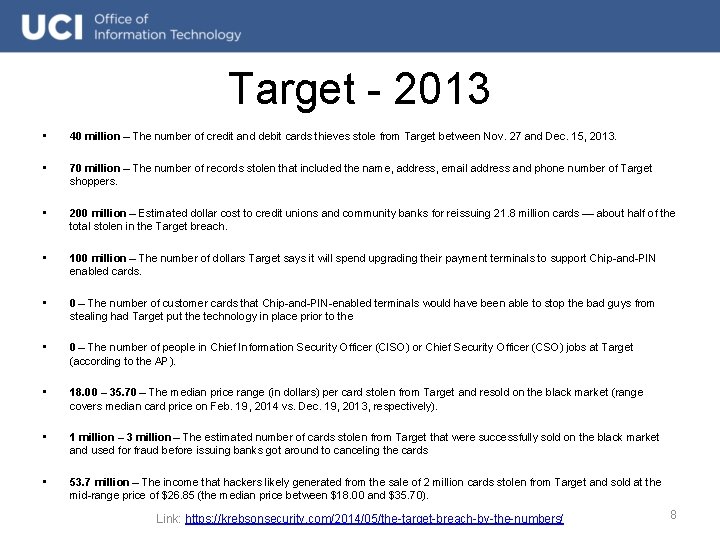
Target - 2013 • 40 million – The number of credit and debit cards thieves stole from Target between Nov. 27 and Dec. 15, 2013. • 70 million – The number of records stolen that included the name, address, email address and phone number of Target shoppers. • 200 million – Estimated dollar cost to credit unions and community banks for reissuing 21. 8 million cards — about half of the total stolen in the Target breach. • 100 million – The number of dollars Target says it will spend upgrading their payment terminals to support Chip-and-PIN enabled cards. • 0 – The number of customer cards that Chip-and-PIN-enabled terminals would have been able to stop the bad guys from stealing had Target put the technology in place prior to the • 0 – The number of people in Chief Information Security Officer (CISO) or Chief Security Officer (CSO) jobs at Target (according to the AP). • 18. 00 – 35. 70 – The median price range (in dollars) per card stolen from Target and resold on the black market (range covers median card price on Feb. 19, 2014 vs. Dec. 19, 2013, respectively). • 1 million – 3 million – The estimated number of cards stolen from Target that were successfully sold on the black market and used for fraud before issuing banks got around to canceling the cards • 53. 7 million – The income that hackers likely generated from the sale of 2 million cards stolen from Target and sold at the mid-range price of $26. 85 (the median price between $18. 00 and $35. 70). Link: https: //krebsonsecurity. com/2014/05/the-target-breach-by-the-numbers/ 8
Verizon • 6 million users leaked online • data was exposed by NICE Systems, an Israelbased company Verizon was working with to facilitate customer service calls • Phone numbers and some PIN codes were hidden but others were visible next to phone numbers • misconfigured Amazon S 3 storage Link: 9
Equifax • 145. 5 Million people: – – Social Security Numbers birth dates addresses “some” driver’s license numbers • 209, 000 U. S. : credit card numbers for roughly 209, 000 U. S. consumers • 182, 000 U. S. ” “certain dispute documents with personal identifying information” 10
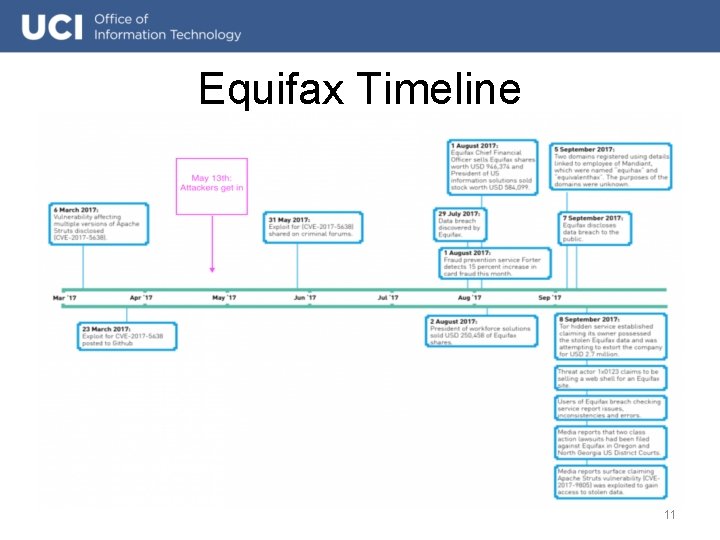
Equifax Timeline 11
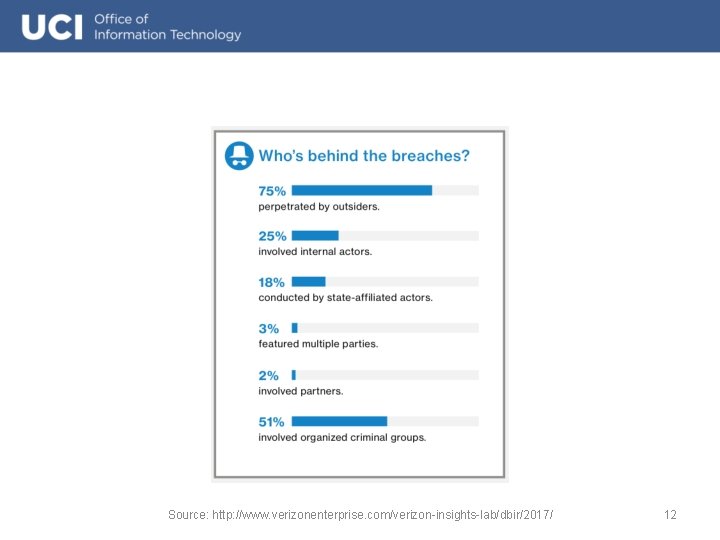
Source: http: //www. verizonenterprise. com/verizon-insights-lab/dbir/2017/ 12
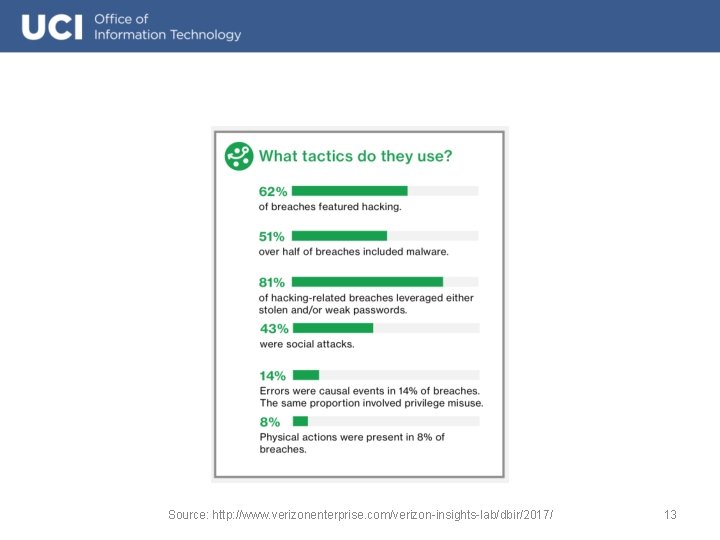
Source: http: //www. verizonenterprise. com/verizon-insights-lab/dbir/2017/ 13
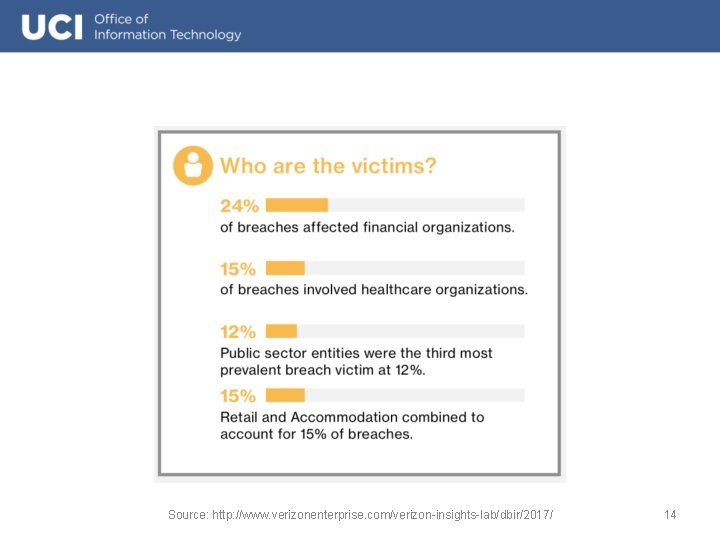
Source: http: //www. verizonenterprise. com/verizon-insights-lab/dbir/2017/ 14
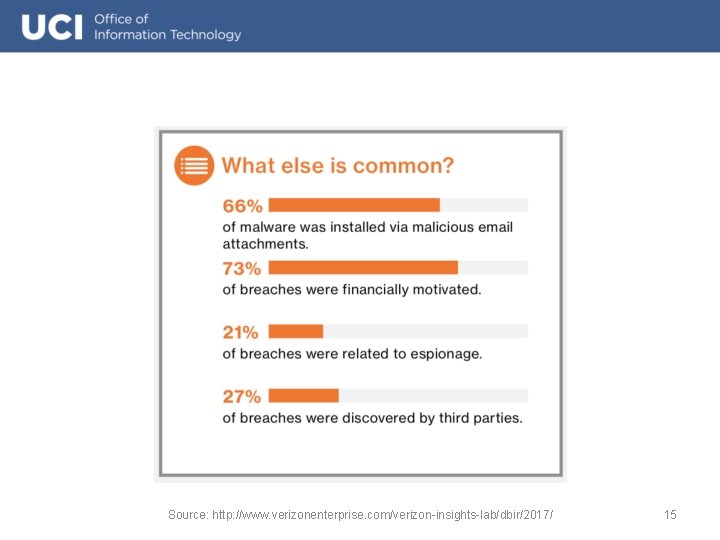
Source: http: //www. verizonenterprise. com/verizon-insights-lab/dbir/2017/ 15
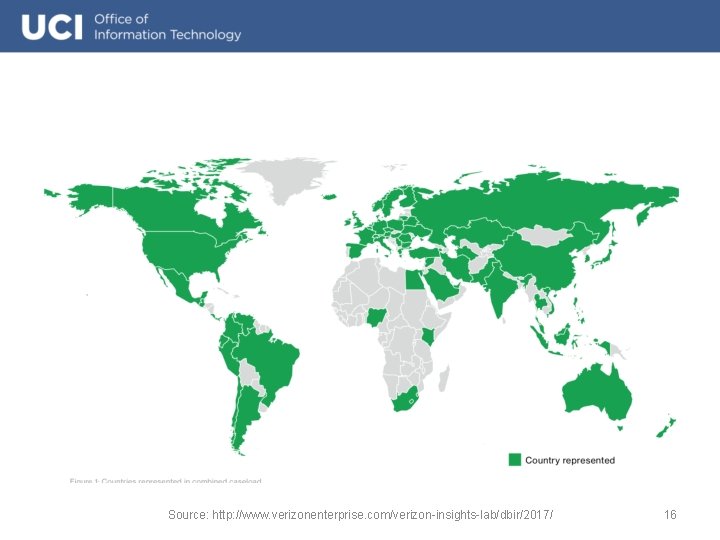
Source: http: //www. verizonenterprise. com/verizon-insights-lab/dbir/2017/ 16
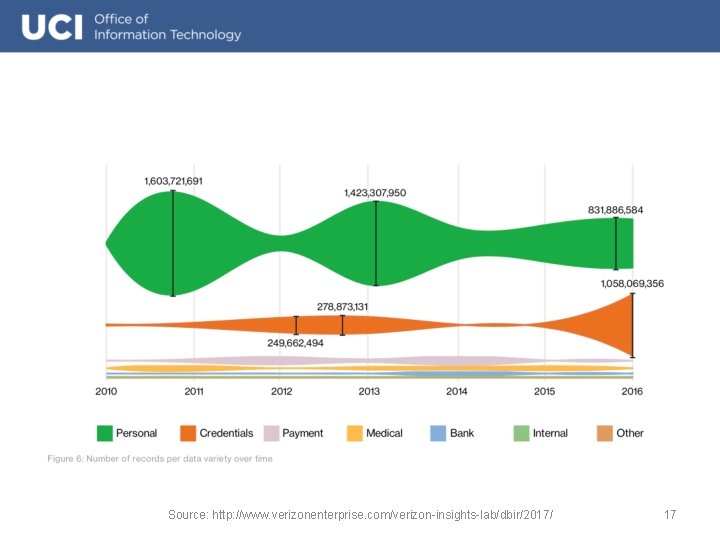
Source: http: //www. verizonenterprise. com/verizon-insights-lab/dbir/2017/ 17
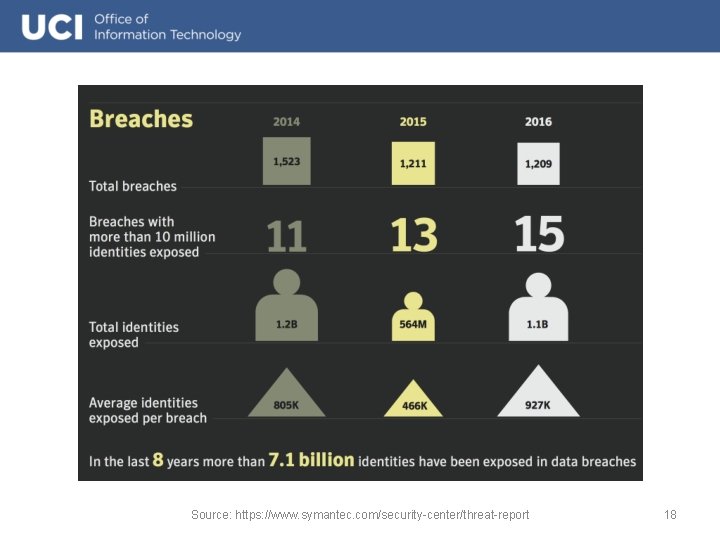
Source: https: //www. symantec. com/security-center/threat-report 18
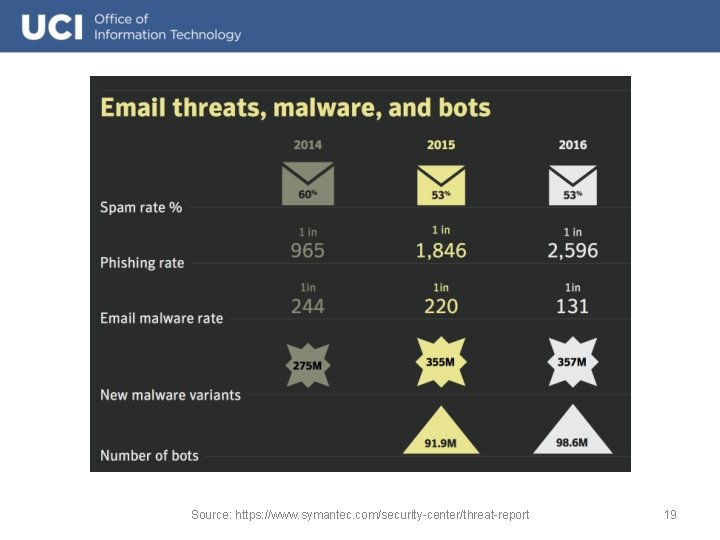
Source: https: //www. symantec. com/security-center/threat-report 19
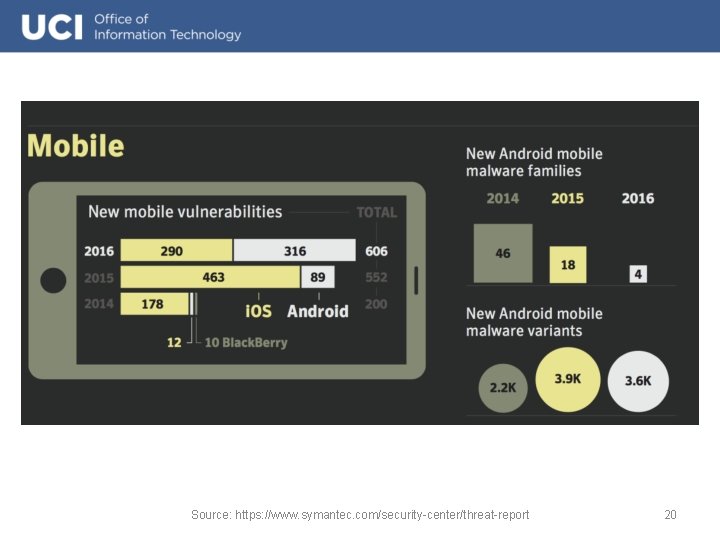
Source: https: //www. symantec. com/security-center/threat-report 20
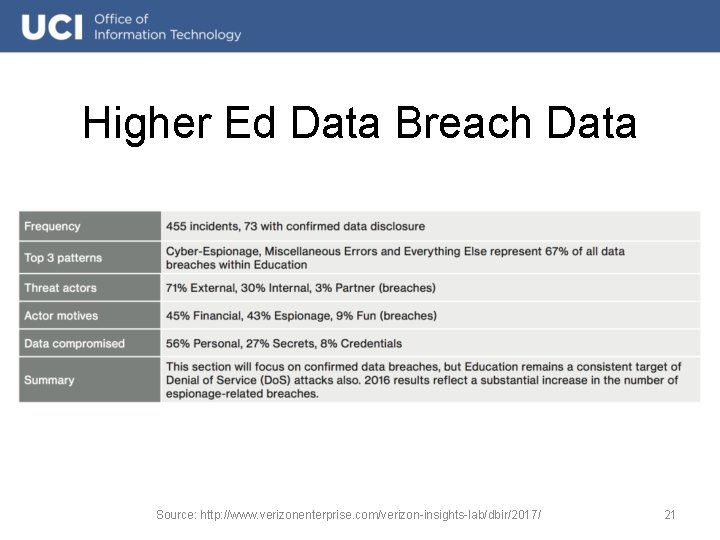
Higher Ed Data Breach Data Source: http: //www. verizonenterprise. com/verizon-insights-lab/dbir/2017/ 21
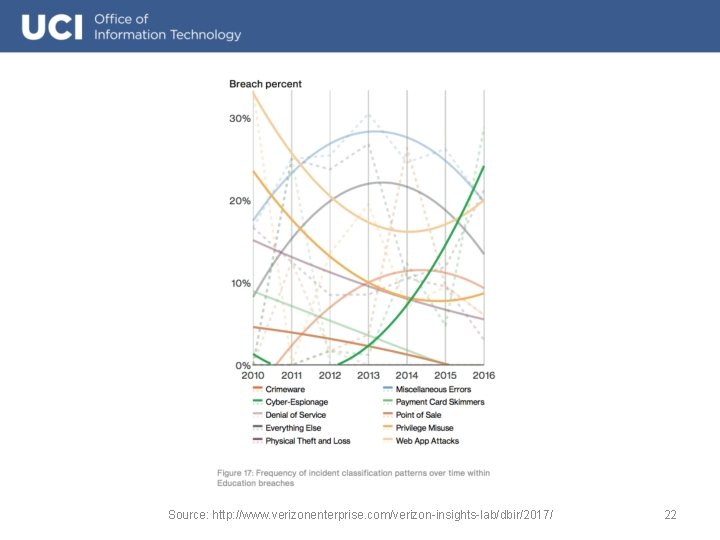
Source: http: //www. verizonenterprise. com/verizon-insights-lab/dbir/2017/ 22
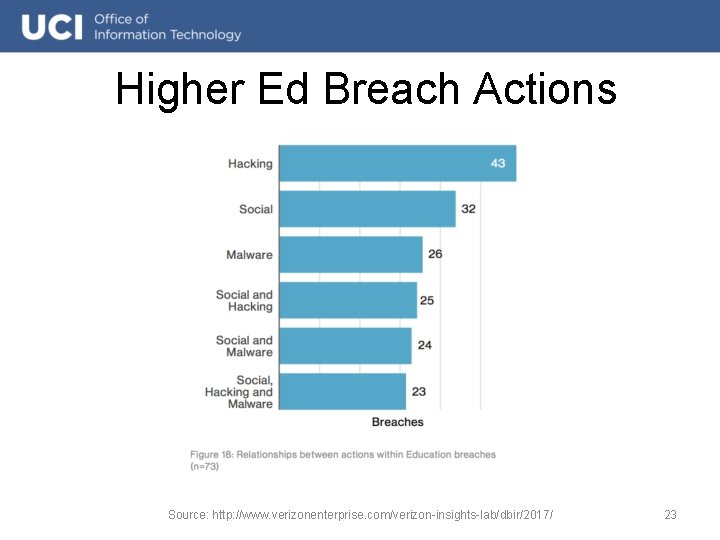
Higher Ed Breach Actions Source: http: //www. verizonenterprise. com/verizon-insights-lab/dbir/2017/ 23
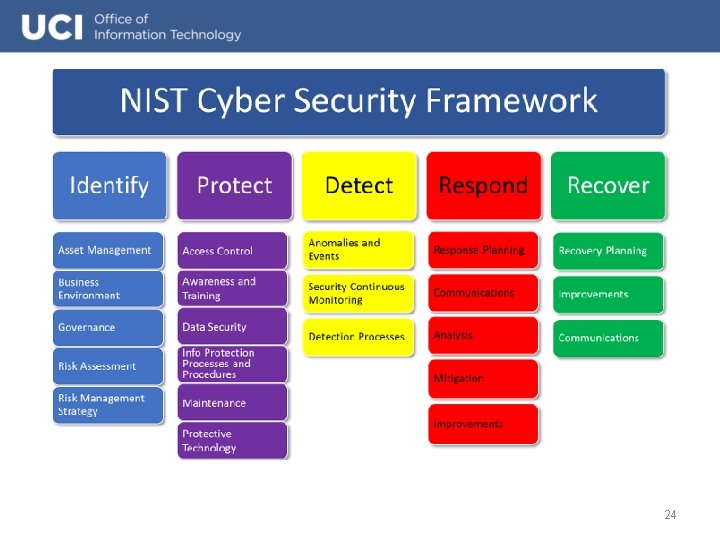
24
Be aware UC Learning Center – “UC Cyber Security Awareness Training” Brian Krebs – Krebs On Security – http: //krebsonsecurity. com/ Threat. Post – https: //threatpost. com/ Bruce Schneier - Schneier on Security – https: //www. schneier. com/ Naked Security – https: //nakedsecurity. sophos. com/ 25
Questions! 26
- Slides: 26