Cybersecurity Threat Matrix Janica Edmonds Cybersecurity First Principles
Cybersecurity: Threat Matrix Janica Edmonds

Cybersecurity First Principles Domain separation Process Isolation Resource encapsulation Layering Modularization Least Privilege Information hiding Abstraction Simplicity Minimization 2
Cyber Realm Card game • Created by Gen. Cyber Duo at California State University, San Bernardino • Played in pairs 3
Security Needs Confidentiality Integrity Availability 4
Security Threats A potential occurrence, malicious or otherwise, that might damage or compromise assets. • Interception – asset is diverted. • Interruption – asset is delayed • Modification – asset is altered. • Fabrication – asset is manufactured. 5
Security Assets Components of the system or network. • Hardware • Software • People • Data 6
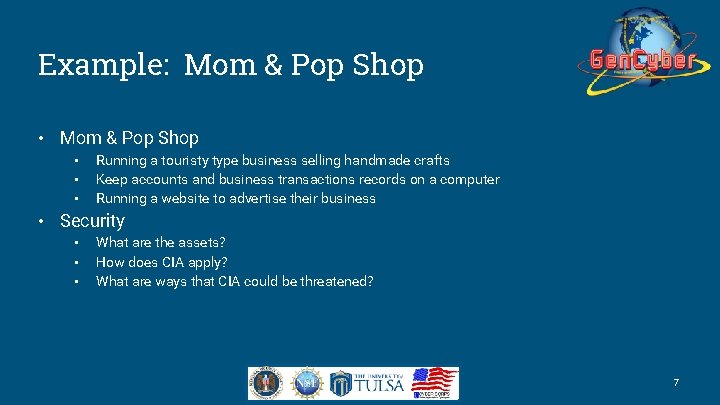
Example: Mom & Pop Shop • • • Running a touristy type business selling handmade crafts Keep accounts and business transactions records on a computer Running a website to advertise their business • Security • • • What are the assets? How does CIA apply? What are ways that CIA could be threatened? 7
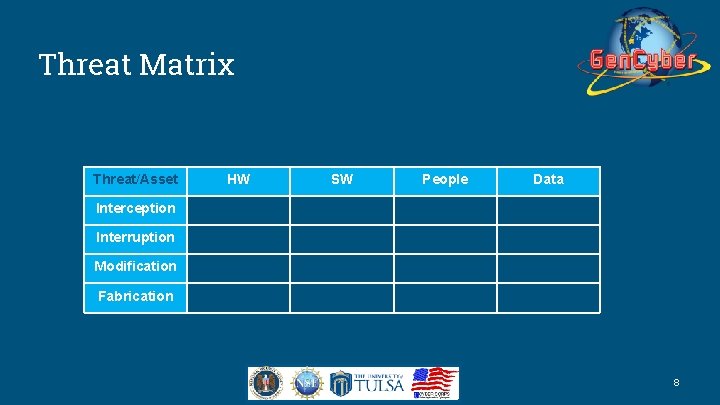
Threat Matrix Threat/Asset HW SW People Data Interception Interruption Modification Fabrication 8
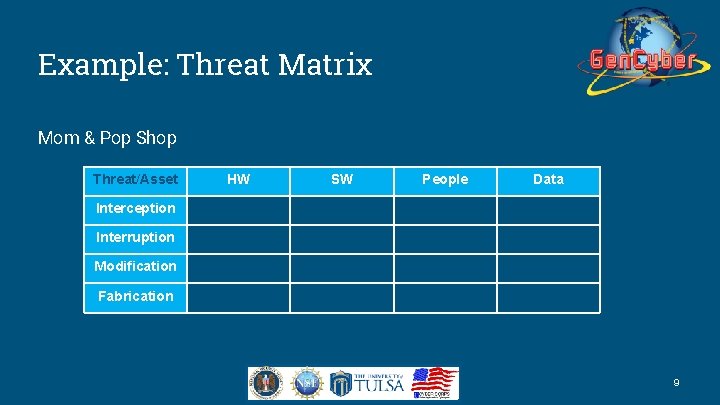
Example: Threat Matrix Mom & Pop Shop Threat/Asset HW SW People Data Interception Interruption Modification Fabrication 9
Example: Principles Applied • Domain separation • Layering • Least privilege • Information hiding • Simplicity • Minimization • Modularization 10
- Slides: 10