Cybersecurity Summit Addressing Cyber Security Risk November 30

Cybersecurity Summit: Addressing Cyber Security Risk November 30, 2017 National Rural Electric Cooperative Association (NRECA) & Electric Power Research Institute (EPRI) Dr. Cynthia Hsu Cybersecurity Program Manager NRECA

2
CHALLENGES • • • Ransomware/Malware Hardware Trojans Software Development Life Cycle (SDLC) International Supply Chain Us
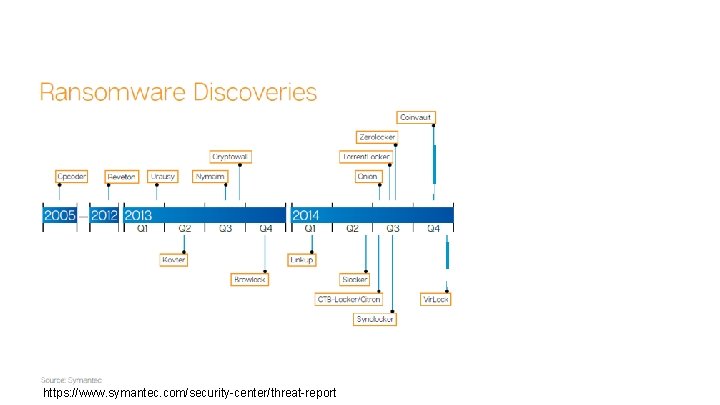
https: //www. symantec. com/security-center/threat-report
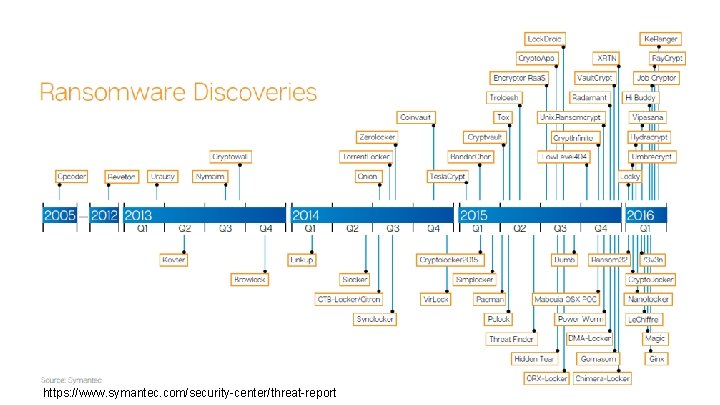
https: //www. symantec. com/security-center/threat-report
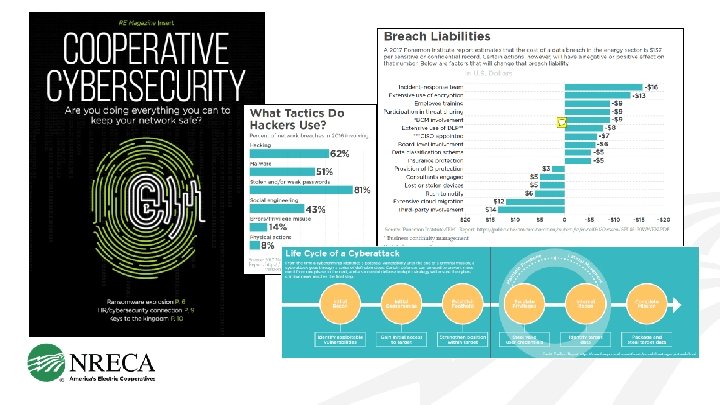
97. 25 % The percentage of phishing emails that contained ransomware in Q 3 2016 (Phish. Me 2016 Q 3 Malware Review) https: //phishme. com/ransomware-delivered-97 -phishing-emails-end-q 3 -2016 -supporting-booming -cybercrime-industry//
THE RANSOMWARE EXPLOSION “In 2016, threat actors evolved their tactics from targeting individual victims to companies that were more likely to view paying a ransom as their best option. This includes small businesses, schools, government agencies, critical infrastructure facilities, and medical facilities. ” (Phish. Me 2017 Phishing Trends & Intelligence Report) https: //www. owler. com/reports/phishlabs---releases-2017 -phishing-trends--intell/1486475521455#!//
HARDWARE TROJANS Modifications to circuitry by adversaries to exploit hardware or to use hardware mechanisms to gain access to data or software running on the chips A Survey of Hardware Trojan Taxonomy and Detection. 2010. M. Tehranipoor & F. Koushanfar. IEEE Design and Test of Computers
HARDWARE TROJANS Designed to disable or destroy a system at some future time, or leak confidential information and secret keys covertly to an adversary. A Survey of Hardware Trojan Taxonomy and Detection. 2010. M. Tehranipoor & F. Koushanfar. IEEE Design and Test of Computers
HARDWARE TROJANS GLOBALIZATION in the semiconductor design and fabrication process integrated circuits (ICs) are becoming increasingly vulnerable to malicious activities and alterations A Survey of Hardware Trojan Taxonomy and Detection. 2010. M. Tehranipoor & F. Koushanfar. IEEE Design and Test of Computers
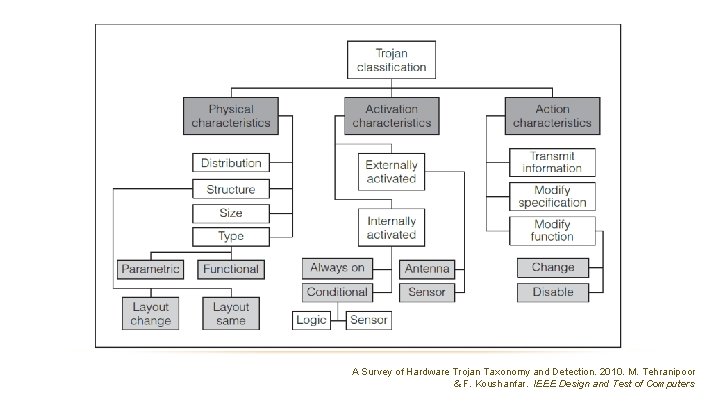
A Survey of Hardware Trojan Taxonomy and Detection. 2010. M. Tehranipoor & F. Koushanfar. IEEE Design and Test of Computers
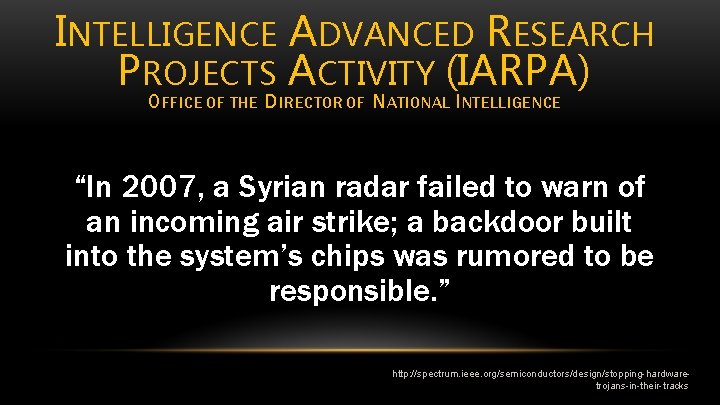
INTELLIGENCE ADVANCED RESEARCH PROJECTS ACTIVITY (IARPA) OFFICE OF THE DIRECTOR OF NATIONAL INTELLIGENCE “In 2007, a Syrian radar failed to warn of an incoming air strike; a backdoor built into the system’s chips was rumored to be responsible. ” http: //spectrum. ieee. org/semiconductors/design/stopping-hardwaretrojans-in-their-tracks
http: //www. dmea. osd. mil/TAPO/foundry. Services. htm
INSECURE SOFTWARE DEVELOPMENT 1) Poor software design 2) Reliance on open source software as a base, vulnerabilities multiply into hundreds or thousands of software products built on that base and persist over time 3) Commercial Off The Shelf (COTS) products that rely on foreign and non-vetted domestic suppliers
INSECURE SOFTWARE DEVELOPMENT 1) Poor software design 2) Reliance on open source software as a base, vulnerabilities multiply into hundreds or thousands of software products built on that base and persist over time 3) Commercial Off The Shelf (COTS) products that rely on foreign and non-vetted domestic suppliers
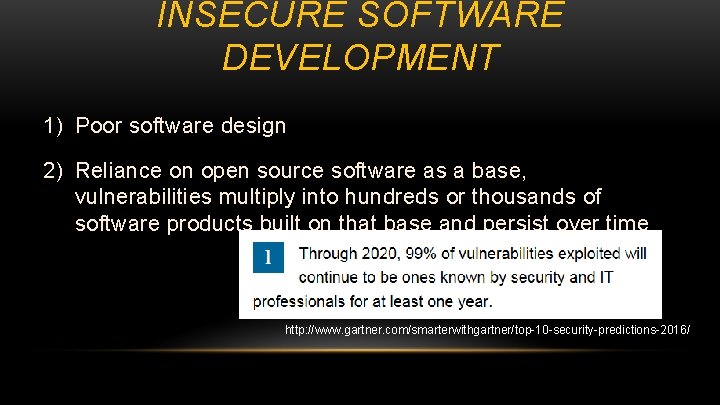
INSECURE SOFTWARE DEVELOPMENT 1) Poor software design 2) Reliance on open source software as a base, vulnerabilities multiply into hundreds or thousands of software products built on that base and persist over time 3) Commercial Off The Shelf (COTS) products that rely on foreign and non-vetted domestic suppliers http: //www. gartner. com/smarterwithgartner/top-10 -security-predictions-2016/
SOFTWARE DEVELOPMENT LIFE CYCLE (SDLC) Vendors sometimes neglect security and validation of software during rapid development. • 2013 5, 186 vulnerabilities National Institute of Standards and Technology
SOFTWARE DEVELOPMENT LIFE CYCLE (SDLC) Vendors sometimes neglect security and validation of software during rapid development. • 2013 5, 186 vulnerabilities • 2017 13, 525 reported as of November 28 National Institute of Standards and Technology
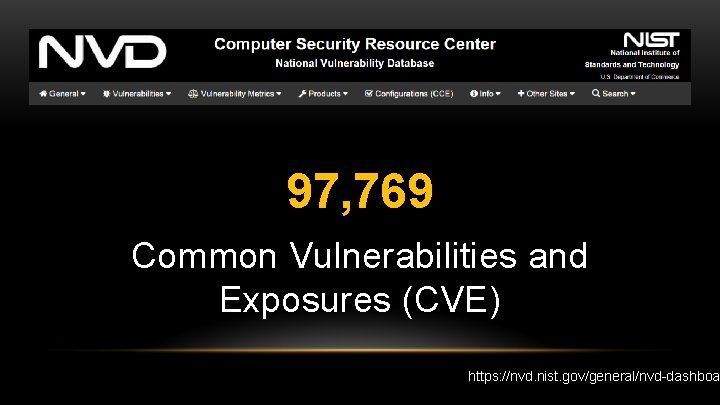
97, 769 Common Vulnerabilities and Exposures (CVE) https: //nvd. nist. gov/general/nvd-dashboa
EQUIFAX • Sept 7 th – sensitive personal information of 143 million American consumers exposed • Oct 2 nd – approximately 2. 5 million additional U. S. consumers were potentially impacted
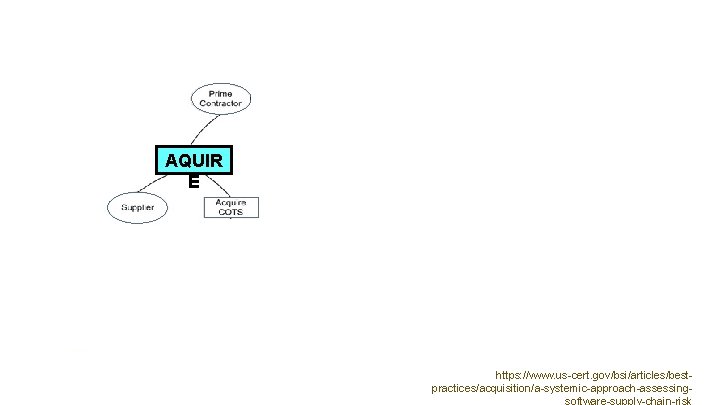
AQUIR E https: //www. us-cert. gov/bsi/articles/bestpractices/acquisition/a-systemic-approach-assessing-
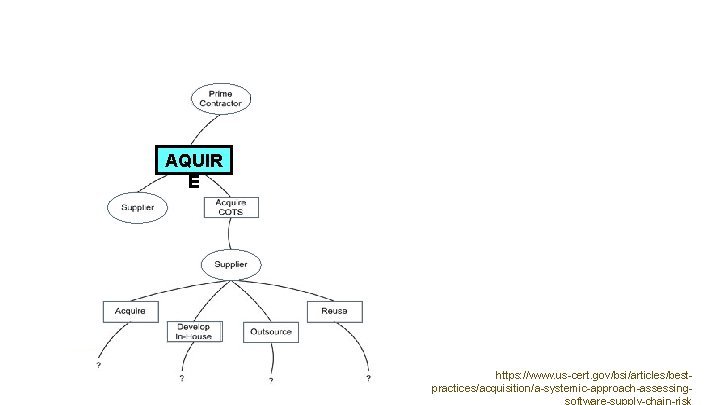
AQUIR E https: //www. us-cert. gov/bsi/articles/bestpractices/acquisition/a-systemic-approach-assessing-
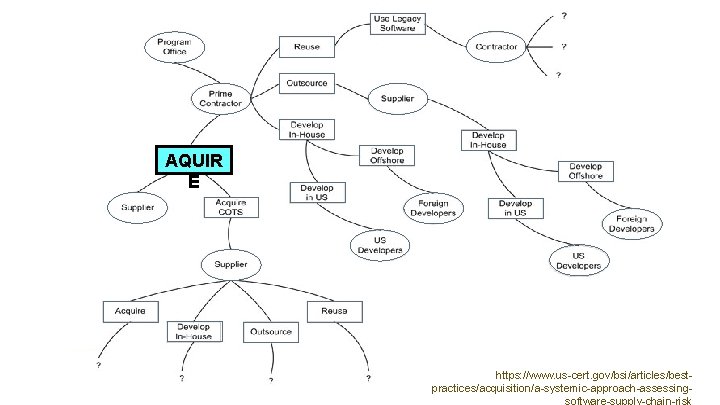
AQUIR E https: //www. us-cert. gov/bsi/articles/bestpractices/acquisition/a-systemic-approach-assessing-


IMPROVING THE CYBER AND PHYSICAL SECURITY POSTURE OF THE ELECTRIC SECTOR
Up to $7. 5 million over three years $2. 5 million per year
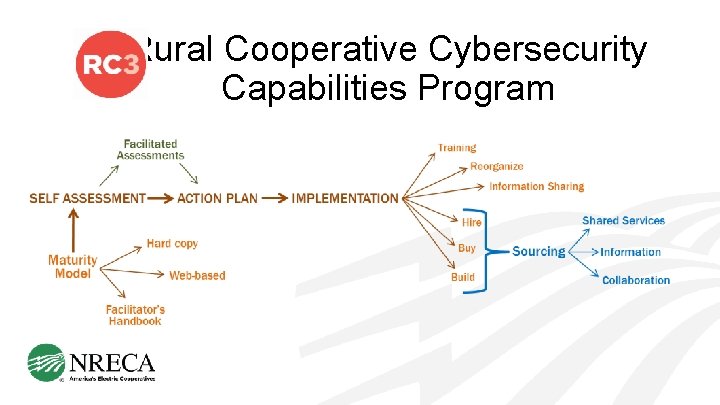
Rural Cooperative Cybersecurity Capabilities Program

PEOPLE, PROCESS, &TECHNOLOGY
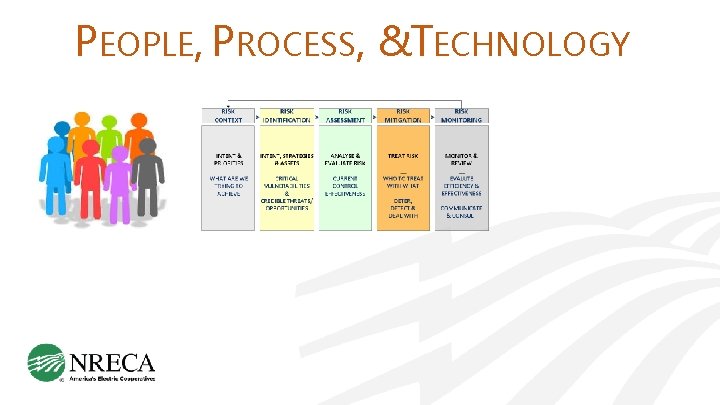
PEOPLE, PROCESS, &TECHNOLOGY
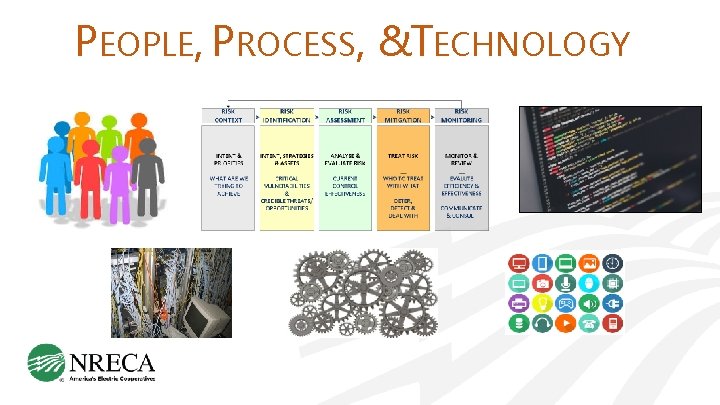
PEOPLE, PROCESS, &TECHNOLOGY
https: //www. nrel. gov/docs/fy 17 osti/67669. p
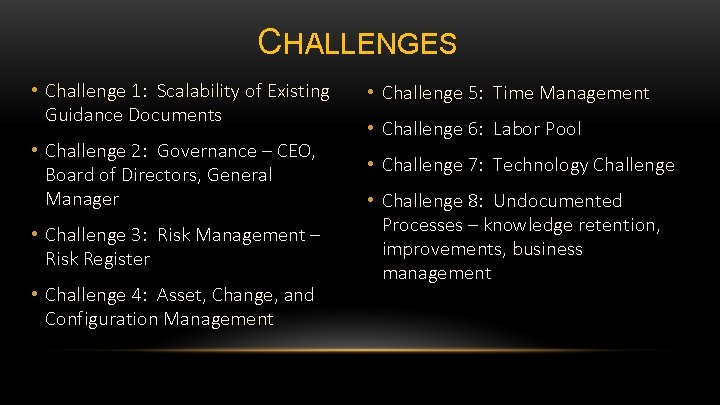
CHALLENGES • Challenge 1: Scalability of Existing Guidance Documents • Challenge 5: Time Management • Challenge 2: Governance – CEO, Board of Directors, General Manager • Challenge 7: Technology Challenge • Challenge 3: Risk Management – Risk Register • Challenge 4: Asset, Change, and Configuration Management • Challenge 6: Labor Pool • Challenge 8: Undocumented Processes – knowledge retention, improvements, business management
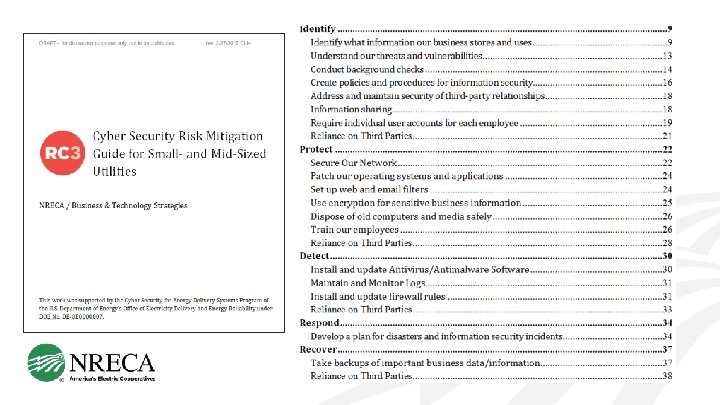
CHALLENGE 1: SCALABILITY OF EXISTING GUIDANCE DOCUMENTS
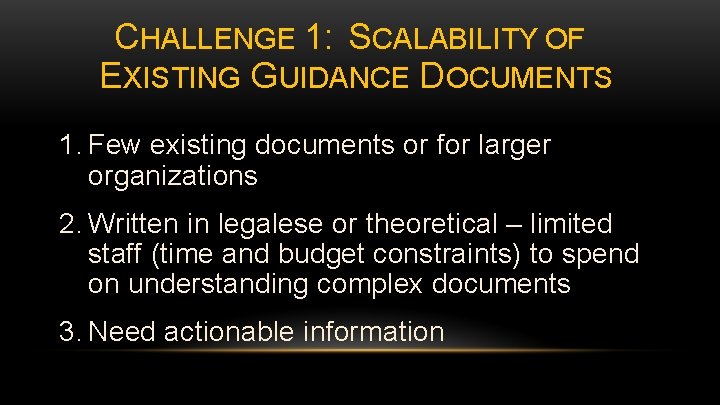
CHALLENGE 1: SCALABILITY OF EXISTING GUIDANCE DOCUMENTS 1. Few existing documents or for larger organizations 2. Written in legalese or theoretical – limited staff (time and budget constraints) to spend on understanding complex documents 3. Need actionable information
CHALLENGE 2: GOVERNANCE – CEO, BOARD OF DIRECTORS, GENERAL MANAGER
CHALLENGE 2: GOVERNANCE – CEO, BOARD OF DIRECTORS, GENERAL MANAGER 1. Materials/messaging for CEO and Board audiences to convey importance, risks, and exposure 2. Importance of CEO and Board leadership on this topic 3. Boards want guaranteed results for investment, and IT is trying to secure necessary resources and funding for preventative measures

CHALLENGE 3: RISK MANAGEMENT
CHALLENGE 3: RISK MANAGEMENT 1. Need ways to identify, understand, and prioritize cyber security risks – tools for risk assessment, tracking, and monitoring 2. Assistance in how to communicate risks to management and Board to gain understanding and support for resources 3. Best practices training, general education, and actual co-op examples (not theory) 4. Risk register – who decides on risk level that is acceptable?
CHALLENGE 4: ASSET, CHANGE, AND CONFIGURATION MANAGEMENT
CHALLENGE 4: ASSET, CHANGE, AND CONFIGURATION MANAGEMENT 1. Decentralized business systems and disconnected systems that don’t communicate with tracking tools make tracking difficult 2. Guidance on what to track using policies and education 3. Easy-to-use tools/checklists to help track 4. Automated tracking tools
CHALLENGE 5: TIME MANAGEMENT
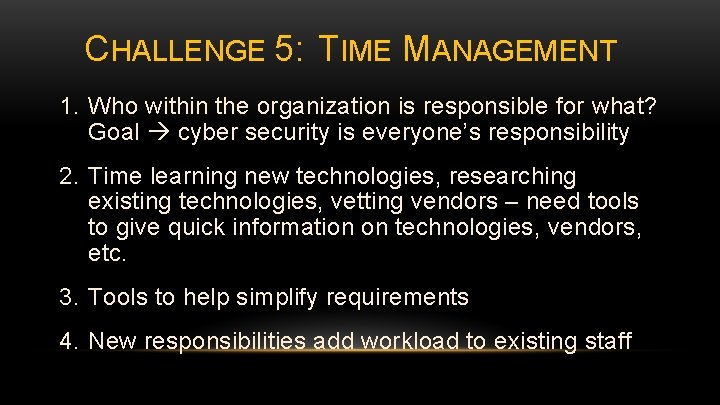
CHALLENGE 5: TIME MANAGEMENT 1. Who within the organization is responsible for what? Goal cyber security is everyone’s responsibility 2. Time learning new technologies, researching existing technologies, vetting vendors – need tools to give quick information on technologies, vendors, etc. 3. Tools to help simplify requirements 4. New responsibilities add workload to existing staff

CHALLENGE 6: LABOR POOL
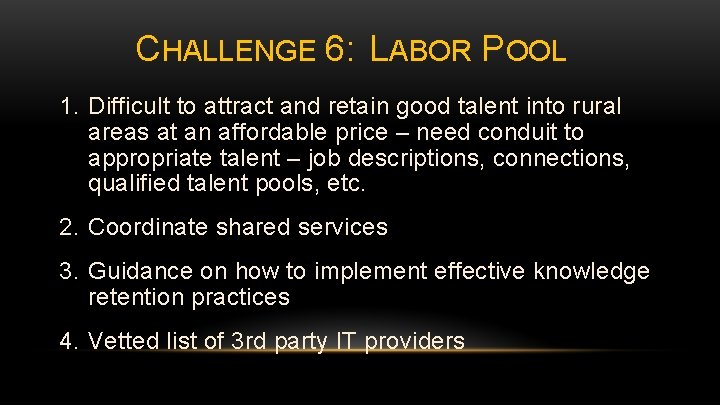
CHALLENGE 6: LABOR POOL 1. Difficult to attract and retain good talent into rural areas at an affordable price – need conduit to appropriate talent – job descriptions, connections, qualified talent pools, etc. 2. Coordinate shared services 3. Guidance on how to implement effective knowledge retention practices 4. Vetted list of 3 rd party IT providers

CHALLENGE 7: TECHNOLOGY
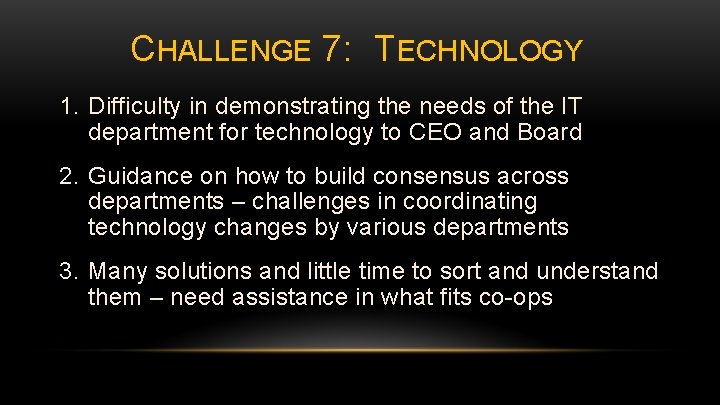
CHALLENGE 7: TECHNOLOGY 1. Difficulty in demonstrating the needs of the IT department for technology to CEO and Board 2. Guidance on how to build consensus across departments – challenges in coordinating technology changes by various departments 3. Many solutions and little time to sort and understand them – need assistance in what fits co-ops
CHALLENGE 8: UNDOCUMENTED PROCESSES KNOWLEDGE RETENTION , IMPROVEMENTS, BUSINESS MANAGEMENT
CHALLENGE 8: UNDOCUMENTED PROCESSES KNOWLEDGE RETENTION , IMPROVEMENTS, BUSINESS MANAGEMENT 1. People who know the processes are too busy implementing to document 2. Guidance on what and how to document 3. No technology standard – documenting not useful for everyone 4. Cross-training needed to ensure information sharing, knowledge retention, succession planning

YOU DESIGN THE RESEARCH • Challenge 1: Scalability of Existing Guidance Documents • Challenge 5: Time Management • Challenge 2: Governance – CEO, Board of Directors, General Manager • Challenge 7: Technology Challenge • Challenge 3: Risk Management – Risk Register • Challenge 4: Asset, Change, and Configuration Management • Challenge 6: Labor Pool • Challenge 8: Undocumented Processes – knowledge retention, improvements, business management
WHAT WILL HAPPEN TO THE INFORMATION COLLECTED TODAY? • Raw data not shared • Aggregated, anonymized summaries will be used to inform: • Other co-ops • Future RC 3 Program directions • DOE
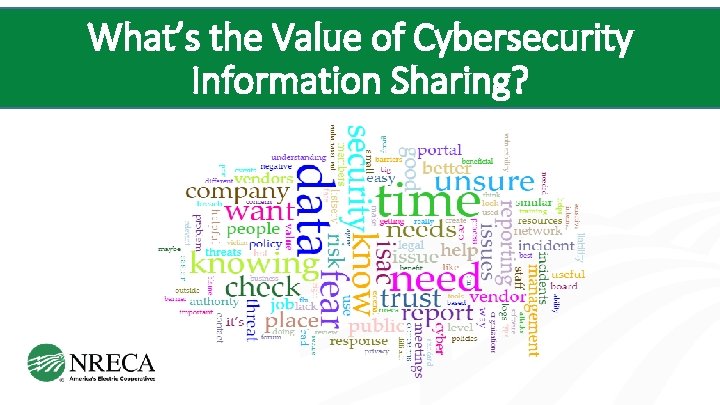
What’s the Value of Cybersecurity Information Sharing?
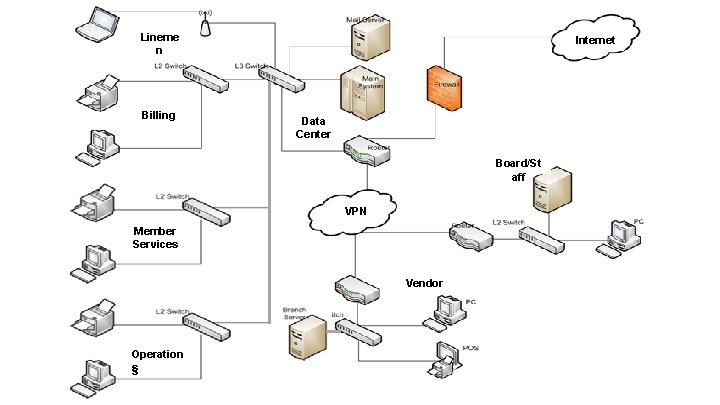
Lineme n Billing Internet Data Center Board/St aff VPN Member Services Vendor Operation s s
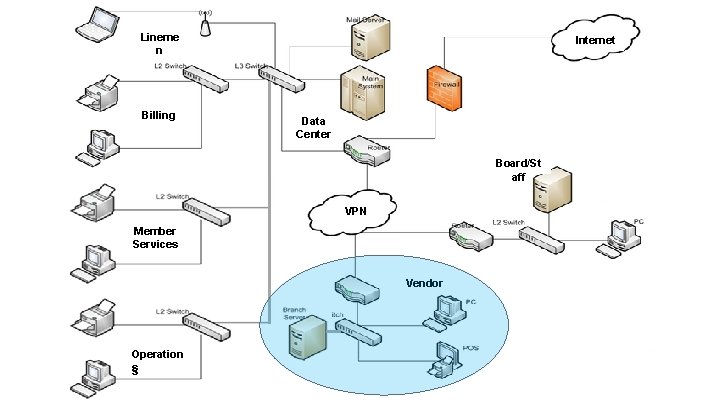
Lineme n Billing Internet Data Center Board/St aff VPN Member Services Vendor Operation s s


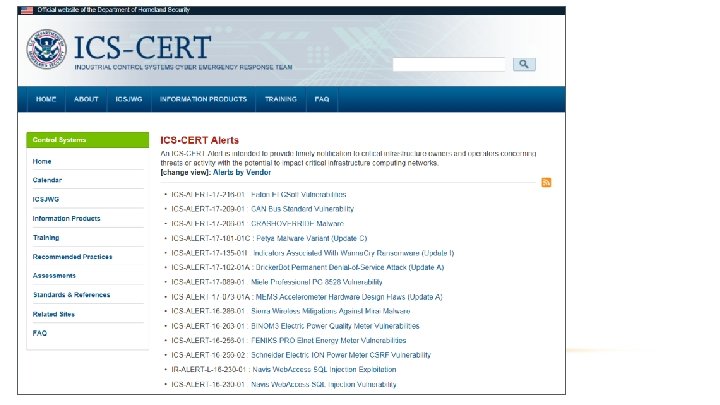
advanced persistent threat (APT) actions targeting government entities and organizations in the energy, nuclear, water, aviation, and critical manufacturing sector
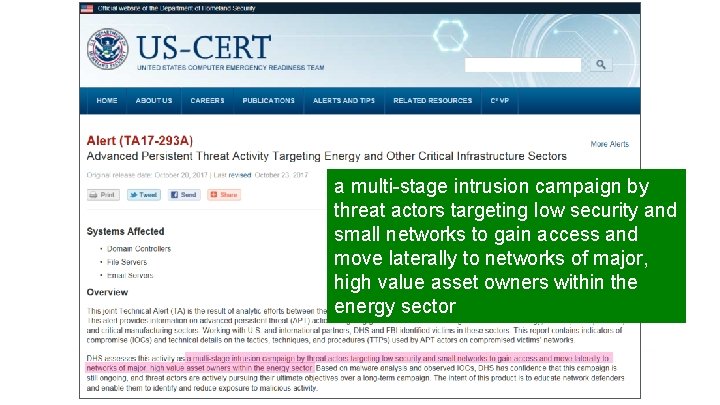
a multi-stage intrusion campaign by threat actors targeting low security and small networks to gain access and move laterally to networks of major, high value asset owners within the energy sector
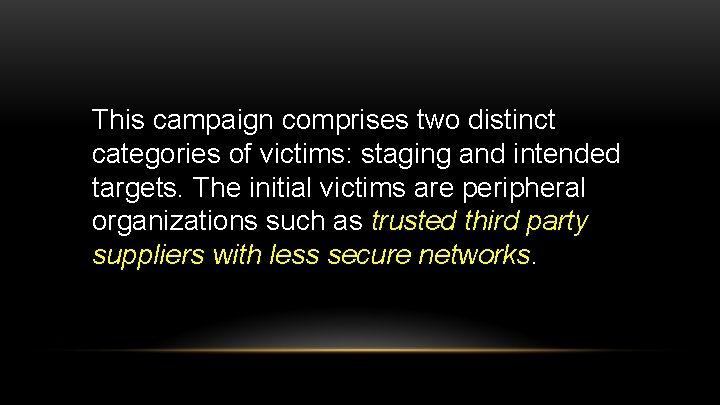
This campaign comprises two distinct categories of victims: staging and intended targets. The initial victims are peripheral organizations such as trusted third party suppliers with less secure networks.
Forensic analysis identified that threat actors are conducting open-source reconnaissance of their targets, gathering information posted on company-controlled websites.
Forensic analysis identified that threat actors are conducting open-source reconnaissance of their targets, gathering information posted on company-controlled websites. … As an example, the threat actors downloaded a small photo from a publically accessible human resources page. The image, when expanded, was a high-resolution photo that displayed control systems equipment models and status information in the background.
DHS and FBI: themes used in spear-phishing emails Email messages include references to common industrial control equipment and protocols. The emails leveraged malicious Microsoft Word attachments that appear to be legitimate résumés or curricula vitae (CVs) for industrial control systems personnel, as well as invitations and policy documents that entice the user to open the attachment.
TARGETING OF ICS AND SCADA INFRASTRUCTURE In one instance, the threat actors accessed workstations and servers on a corporate network that contained data output from control systems within energy generation facilities.

FREE!
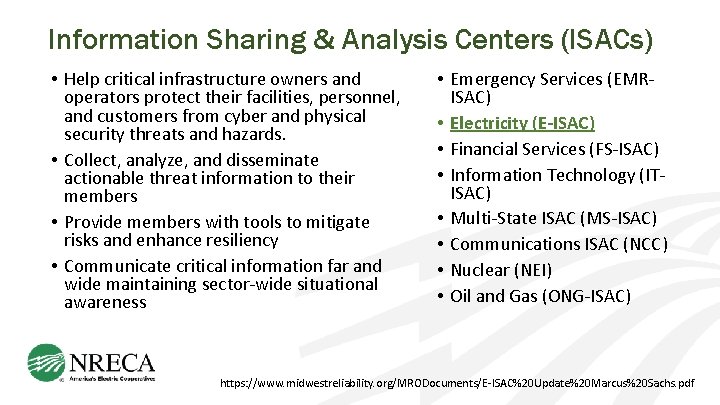
Information Sharing & Analysis Centers (ISACs) • Help critical infrastructure owners and operators protect their facilities, personnel, and customers from cyber and physical security threats and hazards. • Collect, analyze, and disseminate actionable threat information to their members • Provide members with tools to mitigate risks and enhance resiliency • Communicate critical information far and wide maintaining sector-wide situational awareness • Emergency Services (EMRISAC) • Electricity (E-ISAC) • Financial Services (FS-ISAC) • Information Technology (ITISAC) • Multi-State ISAC (MS-ISAC) • Communications ISAC (NCC) • Nuclear (NEI) • Oil and Gas (ONG-ISAC) https: //www. midwestreliability. org/MRODocuments/E-ISAC%20 Update%20 Marcus%20 Sachs. pdf
Electricity – ISAC • The E-ISAC has access to the National Cybersecurity and Communications Integration Center (NCCIC), a Department of Homeland Security-operated 24/7 watch floor near Washington, DC • Top Secret, real-time operations center • Hub for classified threat and vulnerability work • E-ISAC cleared personnel analyze threat and vulnerability components seen by the intelligence community and can make an initial determination of potential impacts on the Bulk Power System. https: //www. midwestreliability. org/MRODocuments/E-ISAC%20 Update%20 Marcus%20 Sachs. pdf https: //www. dhs. gov/national-cybersecurity-and-communications-integration-center
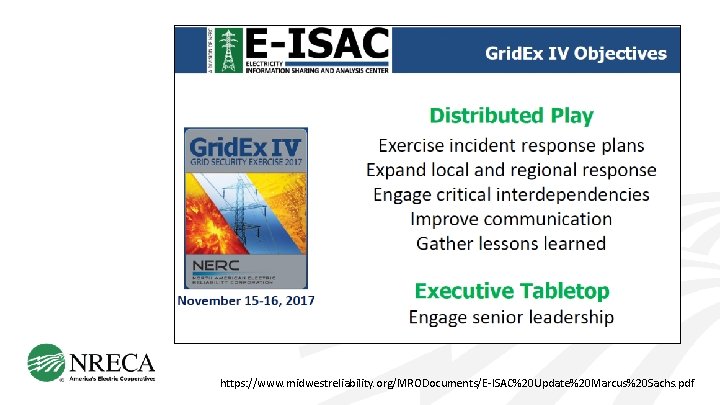
• Products • NERC Alerts • Incident bulletins • Daily, weekly, and monthly summary reports • Issue-specific reports • Programs and Services • Grid. Sec. Con • Grid. Ex • Cyber Risk Information Sharing Program (CRISP) • Physical security outreach visits https: //www. midwestreliability. org/MRODocuments/E-ISAC%20 Update%20 Marcus%20 Sachs. pdf
Sharing Information • Cybersecurity-related information • Indicators of compromise (e. g. IP addresses, domains, URLs, MD 5 s, etc. ) • Forensic artifacts or samples (e. g. malicious email, malware, malicious binaries, logs, or packet captures) • Reports (forensics, after action reports, analyses) • Operational Technology (OT) information sharing • Unknown or unexplained PLC or RTU freezes, reboots, or failures • Discovered zero day vulnerabilities • New adversary tactics, techniques, and procedures (TTPs) aimed at disruption control systems or networks https: //www. midwestreliability. org/MRODocuments/E-ISAC%20 Update%20 Marcus%20 Sachs. pdf
https: //www. midwestreliability. org/MRODocuments/E-ISAC%20 Update%20 Marcus%20 Sachs. pdf
Free! • More than 4, 000 utilities in US, Canada, and Mexico • Any electric utility can join for free https: //www. eisac. com/
Cybersecurity Information Sharing Resources • Department of Energy – lead agency for electricity subsector cybersecurity issues • https: //www. energy. gov/oe/activities/cybersecurity-critical-energy-infrastructure • https: //www. energy. gov/oe/energy-sector-cybersecurity-preparedness-0) • Department of Homeland Security • For general information see https: //www. dhs. gov/topic/cybersecurity • To report cyber incidents see https: //www. dhs. gov/how-do-i/report-cyber-incidents • Report malware and vulnerabilities to DHS by e-mail at cert@cert. org and soc@us-cert. gov • Infra. Gard – partnership between the FBI and the private sector. You can report cyber crime incidents to http: //www. infragardmembers. org/report-cyber-incident. html • FBI – You can report cyber crime incidents directly to the FBI at https: //www. fbi. gov/tips
NRECA’s RC 3 Program : What Lies Ahead
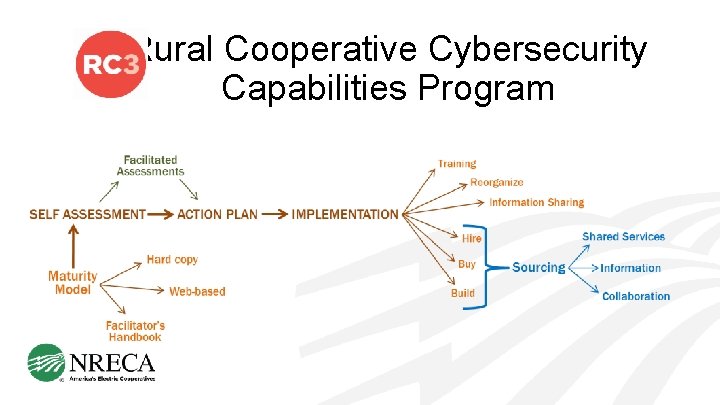
Rural Cooperative Cybersecurity Capabilities Program
Rural Cooperative Cybersecurity Capabilities Program
DEADLINE: MARCH 17, 2017
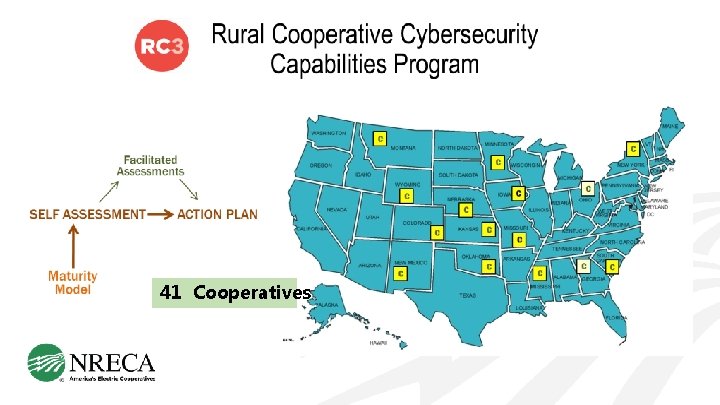
41 Cooperatives
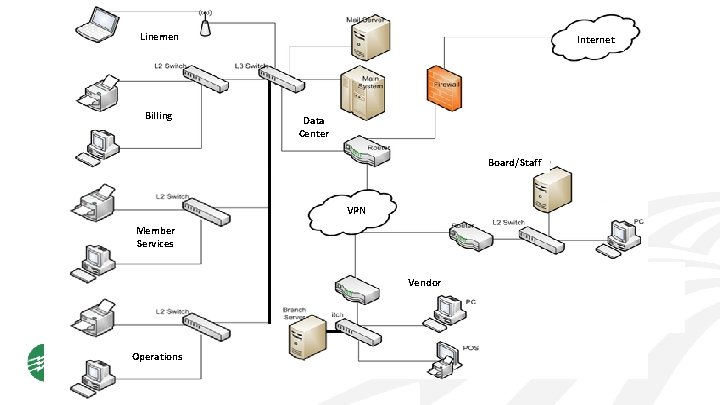
Linemen Billing Internet Data Center Board/Staff VPN Member Services Vendor Operations
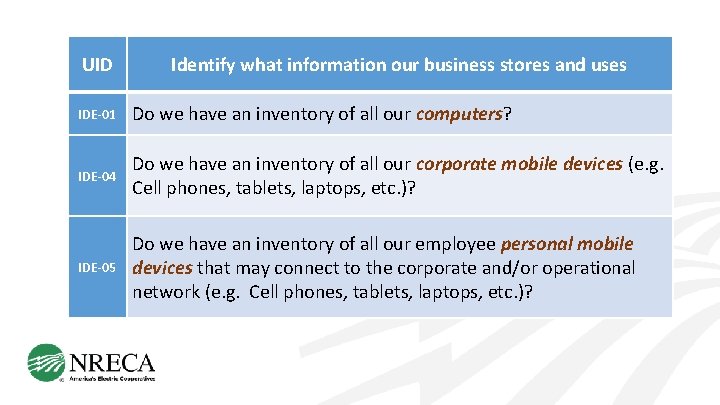
UID Identify what information our business stores and uses IDE-01 Do we have an inventory of all our computers? IDE-04 Do we have an inventory of all our corporate mobile devices (e. g. Cell phones, tablets, laptops, etc. )? IDE-05 Do we have an inventory of all our employee personal mobile devices that may connect to the corporate and/or operational network (e. g. Cell phones, tablets, laptops, etc. )?
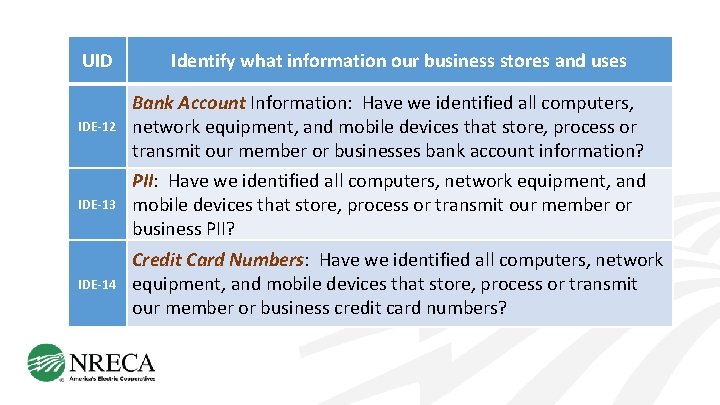
UID Identify what information our business stores and uses IDE-12 Bank Account Information: Have we identified all computers, network equipment, and mobile devices that store, process or transmit our member or businesses bank account information? IDE-13 PII: Have we identified all computers, network equipment, and mobile devices that store, process or transmit our member or business PII? IDE-14 Credit Card Numbers: Have we identified all computers, network equipment, and mobile devices that store, process or transmit our member or business credit card numbers?
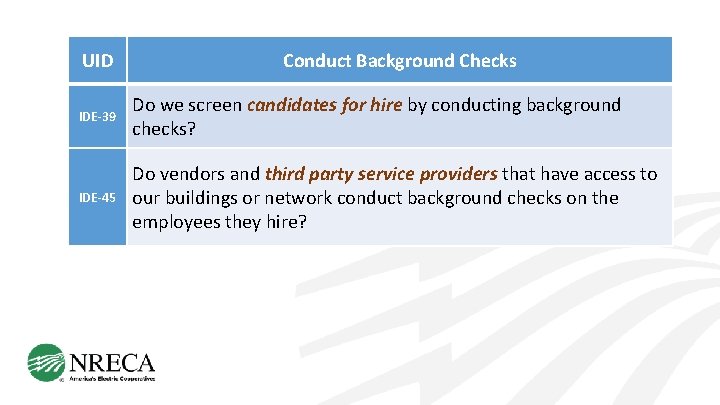
UID Conduct Background Checks IDE-39 Do we screen candidates for hire by conducting background checks? IDE-45 Do vendors and third party service providers that have access to our buildings or network conduct background checks on the employees they hire?
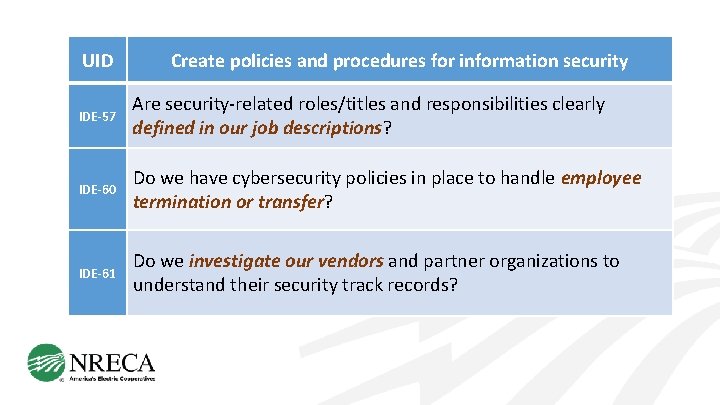
UID Create policies and procedures for information security IDE-57 Are security-related roles/titles and responsibilities clearly defined in our job descriptions? IDE-60 Do we have cybersecurity policies in place to handle employee termination or transfer? IDE-61 Do we investigate our vendors and partner organizations to understand their security track records?
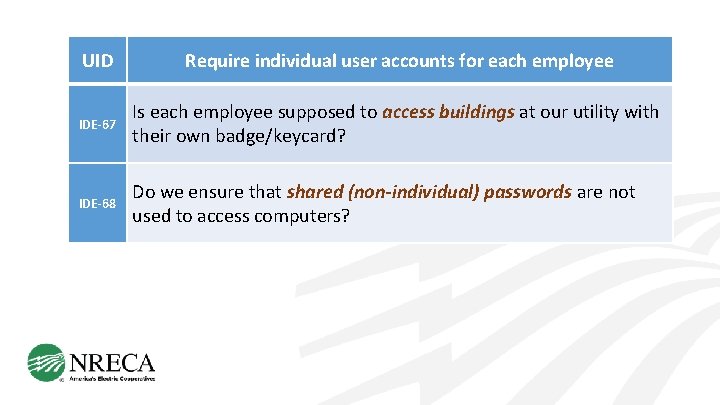
UID Require individual user accounts for each employee IDE-67 Is each employee supposed to access buildings at our utility with their own badge/keycard? IDE-68 Do we ensure that shared (non-individual) passwords are not used to access computers?
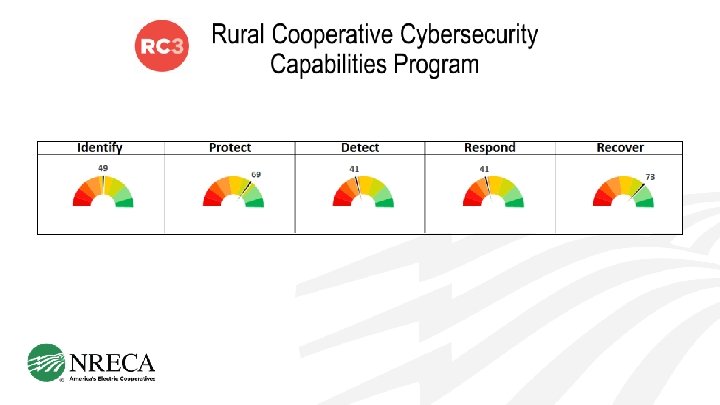
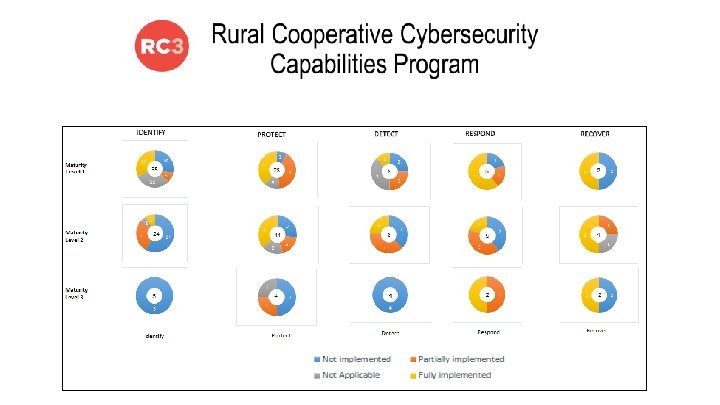
October 2017 Completed – 33 Cooperatives Trained – > 160 staff
It gave us a sense of how important this is going forward. I realized as we went through it that there is much more value from a Human Resources stand point than I had expected. The cross-department engagement – that was the most awesome thing. All the VPs need to be there and be engaged. It absolutely made sense for the non-IT people to be there – everyone felt the same way – it really worked.
At first I thought “well this is four hours of my life I’ll never be getting back. ” But after we went through it, I thought it was well worthwhile.

“I came away from the first day with a hopeless feeling. I thought, as small a co-op as we are, we can’t possibly do this. The second day was totally different. We learned - ‘Here’s what you can do. ’ It was much more enjoyable, much more helpful. I came away realizing that we’ve got to beef up our system. Look, I’ve got 14 employees that’s all. And zero in IT… [but] I think we can come up with solutions. ”
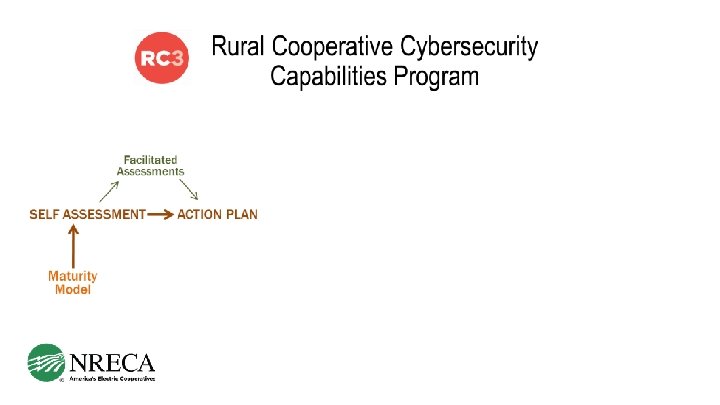
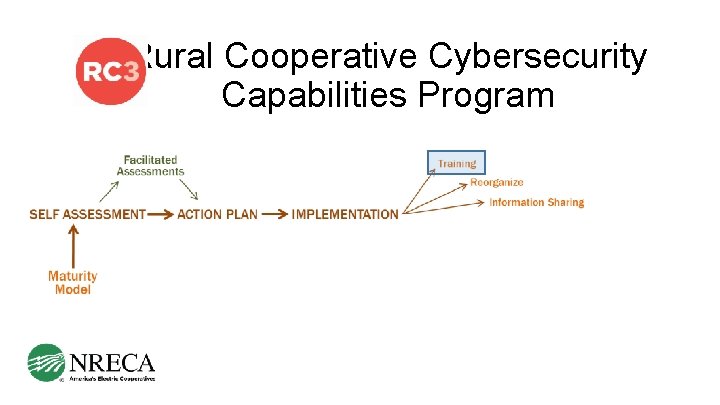
Rural Cooperative Cybersecurity Capabilities Program
Cybersecurity Summits: Addressing Cybersecurity Risks Peer-to-Peer training for more than 200 co-op staff
INCREASING ACCESS TO EXISTING CYBERSECURITY COURSES: Training Cybersecurity training for CEOs/GMs and Directors Launching in 2018 Advanced cybersecurity training for technical staff Launching in 2018
CREATING NEW CURRICULA: Training • Purchasing • Hardware & Software • Security Assessment Services • Legal • Communicators • Human Relations • Finance/Administrative • Engineers/Operators • CEOs/General Managers • Board Members
CREATING NEW CURRICULA: Training • Purchasing • Hardware & Software • Security Assessment Services
CREATING NEW CURRICULA: Training Cybersecurity Guidebook and Training Series • • • Engineers/Operators Legal • CEOs/General Managers Communicators • Directors Human Relations Finance/Administrative
Cybersecurity Guidebook and Training Series Training
Cybersecurity Guidebook and Training Series Training • Legal • Communicators Cybersecurity resources and training materials designed for cooperative staff Available Spring 2018
Cybersecurity Guidebook and Training Series Training • Human Relations • Finance/Administrative • Engineers/Operators • CEOs/General Managers • Directors Available Fall 2018
OUTREACH AND AWARENESS: Training

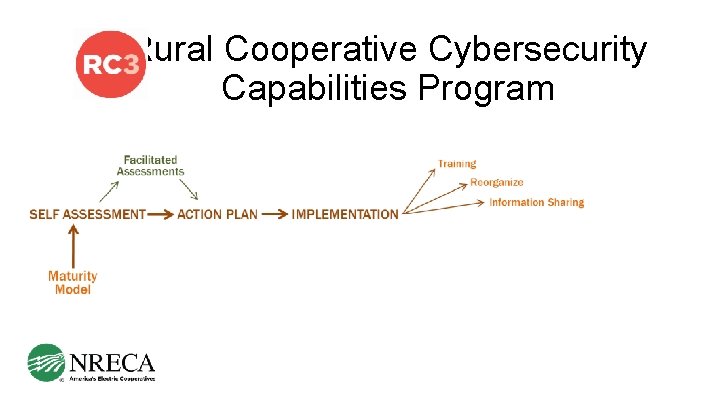
Rural Cooperative Cybersecurity Capabilities Program
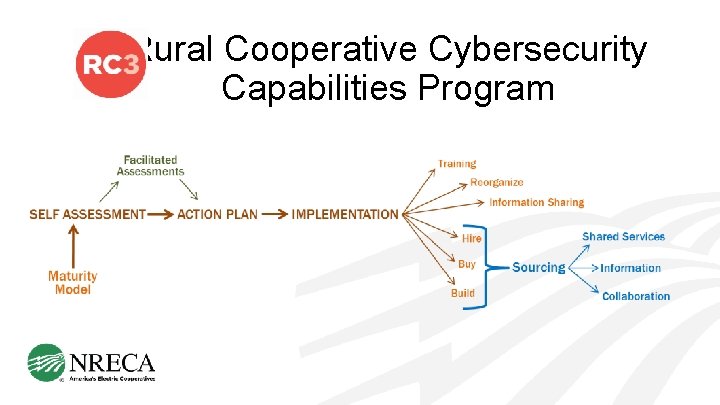
Rural Cooperative Cybersecurity Capabilities Program
Rural Cooperative Cybersecurity Capabilities Program
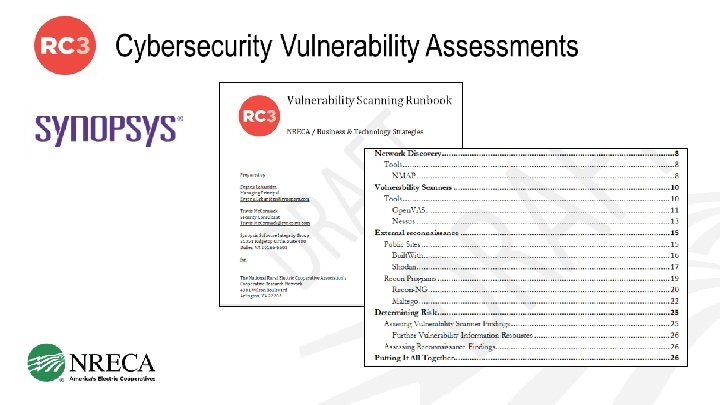
Cybersecurity: Vulnerability Assessments Information Sharing Technology R&D
Technology R&D and Information Sharing Cybersecurity: Collect-Communicate-Collaborate – improve cyber security of cooperatives through information sharing among the cooperatives and with experts outside the cooperative community.
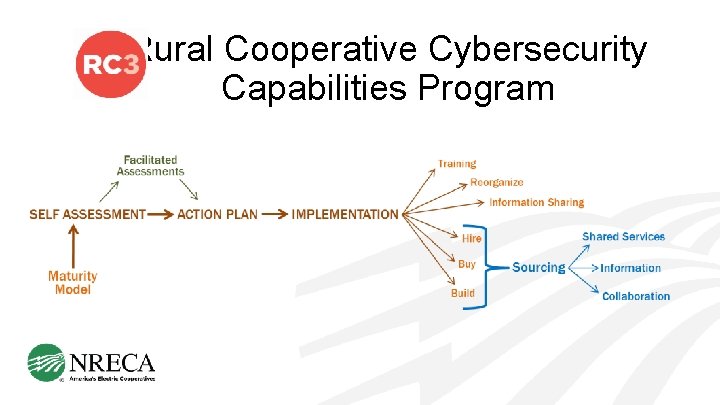
Rural Cooperative Cybersecurity Capabilities Program
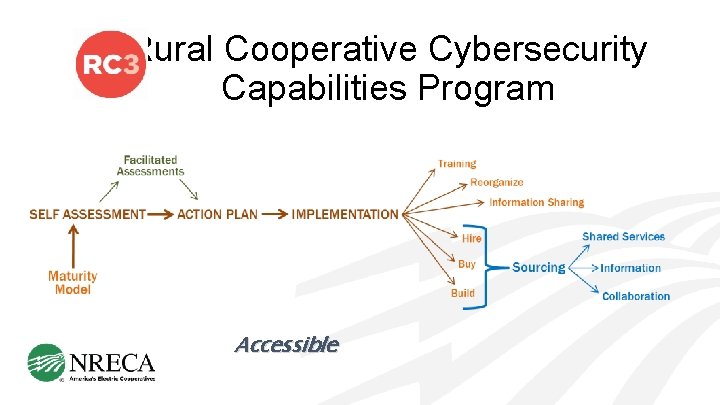
Rural Cooperative Cybersecurity Capabilities Program Accessible
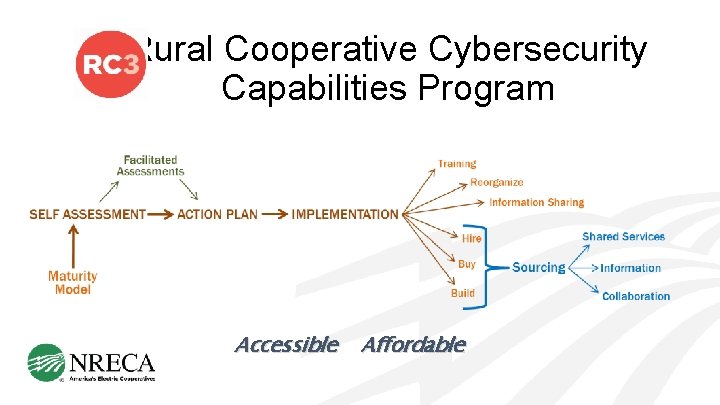
Rural Cooperative Cybersecurity Capabilities Program Accessible Affordable
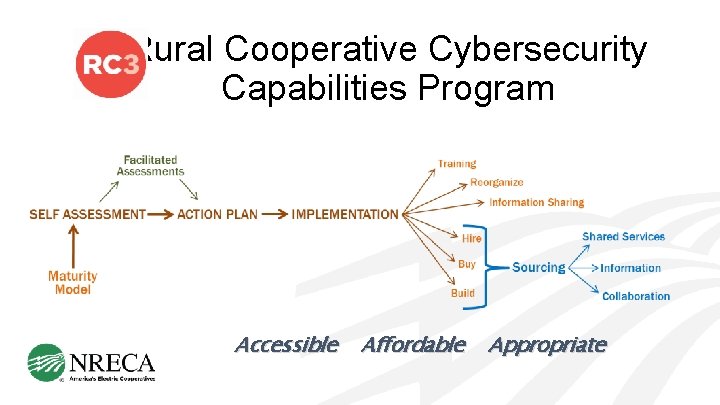
Rural Cooperative Cybersecurity Capabilities Program Accessible Affordable Appropriate
Tech. Update: twicemonthly email newsletter containing the latest information on technical publications, articles, reports, webinars, and conferences. Sign-up at: https: //www. cooperative. com/public/bts/tech-update/Pages/Sign-up. aspx
IT’S A DOG EAT DOG WORLD OUT THERE
IT’S A DOG EAT DOG WORLD OUT THERE
CYBERSECURITY POLICY AND LEGISLATIVE AFFAIRS BARRY LAWSON SENIOR DIRECTOR POWER DELIVERY &RELIABILITY 703. 907. 5781 BARRY. LAWSON@NRECA. COOP BRIDGETTE L. BOURGE SENIOR PRINCIPAL LEGISLATIVE AFFAIRS 703. 907. 6386 BRIDGETTE. BOURGE@NRECA. COOP
Rural Cooperative Cybersecurity Capabilities Program CYNTHIA HSU, PH. D. CYBERSECURITY PROGRAM MANAGER OFFICE: 703 -907 -5500 MOBILE: 703 -403 -8698 EMAIL: CYNTHIA. HSU@NRECA. COOP
- Slides: 121