Cybersecurity Research Challenges Jeannette M Wing Assistant Director
Cybersecurity Research Challenges Jeannette M. Wing Assistant Director Computer and Information Science and Engineering Directorate National Science Foundation and President’s Professor of Computer Science Carnegie Mellon University Cybersecurity Summit, Crystal City, VA May 8, 2008 Cybersecurity Jeannette M. Wing
Outline • The Setting: Then and Now • What’s Missing – Long-term outlook – Big picture – 5 new research areas Cybersecurity 2 Jeannette M. Wing
The Setting: Then and Now We are at risk. Increasingly, America depends on computers. They control power delivery, communications, aviation, and financial services. They are used to store vital information, from medical records to business plans to criminal records. Although we trust them, they are vulnerable—to the effects of poor design and insufficient quality control, to accident, and perhaps most alarmingly, to deliberate attack. The modern thief can steal more with a computer than with a gun. Tomorrow’s terrorist may be able to do more damage with a keyboard than with a bomb. 1991 Computers at Risk, National Academies CSTB Study, p. 7. networked systems 8 8 1999 Trust in Cyberspace, CSTB Study. everywhere, everyone, all the time, 2001 September 11 embedded, invisible, mobile, wearable, handheld, remote, peta, tera, giga, mini, micro, nano, good guys, bad guys ubiquity 2007 Improving Cybersecurity for the 21 st Century, CSTB Study. Cybersecurity 3 Jeannette M. Wing
Credit: NCO/NITRD Credit: U. S. Department of Homeland Security Credit: NCO/NITRD Cybersecurity 4 Jeannette M. Wing
What’s Missing in Our Thinking • Be proactive, not reactive. – We are using yesterday’s solutions to address today’s threats. – We should be ready today for tomorrow’s threats. – We are not. • Anticipate the future. – Long-term outlook – Big picture view – Foundational research Cybersecurity 5 Jeannette M. Wing
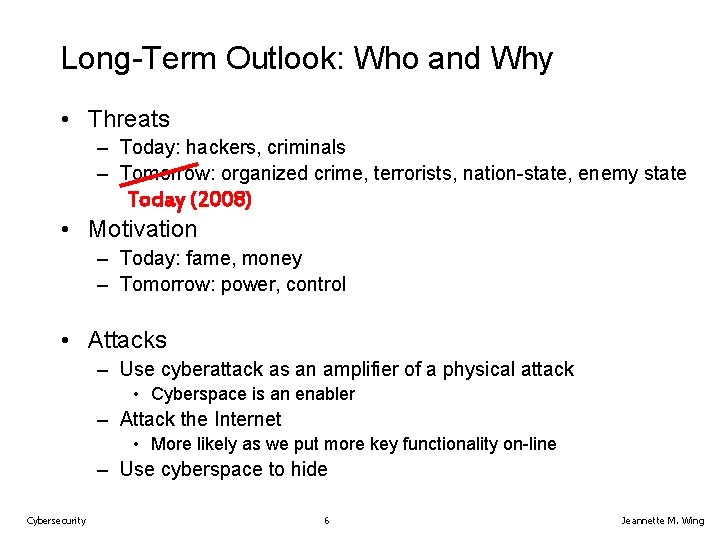
Long-Term Outlook: Who and Why • Threats – Today: hackers, criminals – Tomorrow: organized crime, terrorists, nation-state, enemy state Today (2008) • Motivation – Today: fame, money – Tomorrow: power, control • Attacks – Use cyberattack as an amplifier of a physical attack • Cyberspace is an enabler – Attack the Internet • More likely as we put more key functionality on-line – Use cyberspace to hide Cybersecurity 6 Jeannette M. Wing
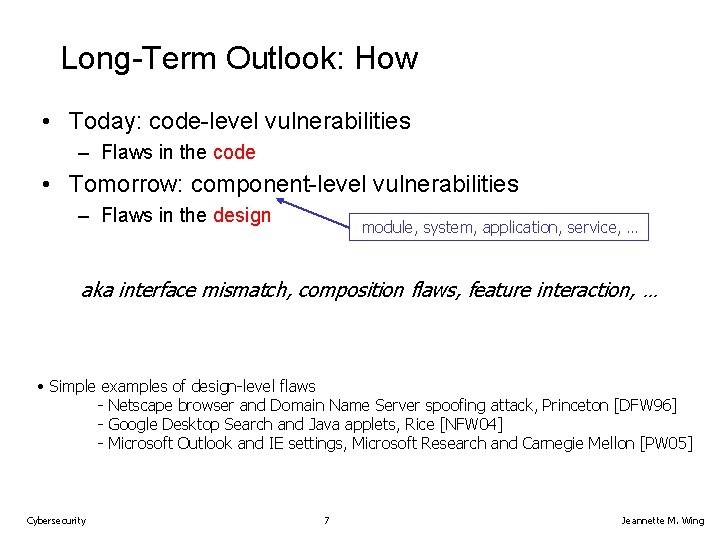
Long-Term Outlook: How • Today: code-level vulnerabilities – Flaws in the code • Tomorrow: component-level vulnerabilities – Flaws in the design module, system, application, service, … aka interface mismatch, composition flaws, feature interaction, … • Simple examples of design-level flaws - Netscape browser and Domain Name Server spoofing attack, Princeton [DFW 96] - Google Desktop Search and Java applets, Rice [NFW 04] - Microsoft Outlook and IE settings, Microsoft Research and Carnegie Mellon [PW 05] Cybersecurity 7 Jeannette M. Wing
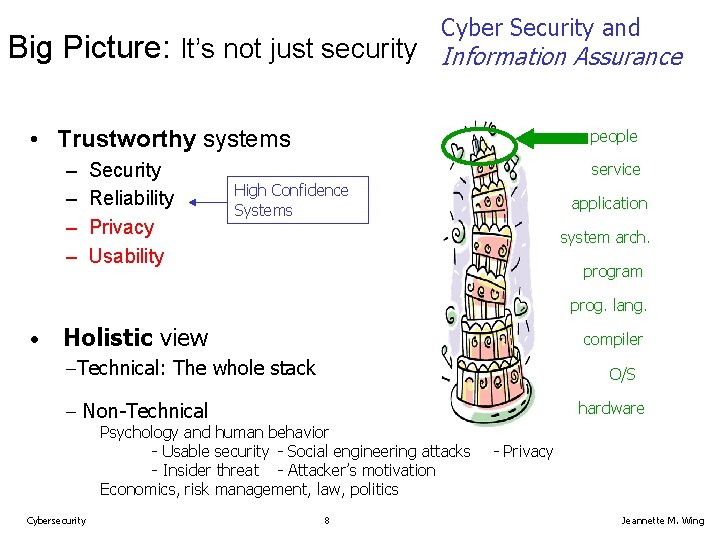
Big Picture: It’s not just security Cyber Security and Information Assurance • Trustworthy systems – – Security Reliability Privacy Usability people service High Confidence Systems application system arch. program prog. lang. • Holistic view compiler Technical: The whole stack O/S Non-Technical hardware Psychology and human behavior - Usable security - Social engineering attacks - Insider threat - Attacker’s motivation Economics, risk management, law, politics Cybersecurity 8 - Privacy Jeannette M. Wing
Cybersecurity 9 Credit: NCO/NITRD Jeannette M. Wing
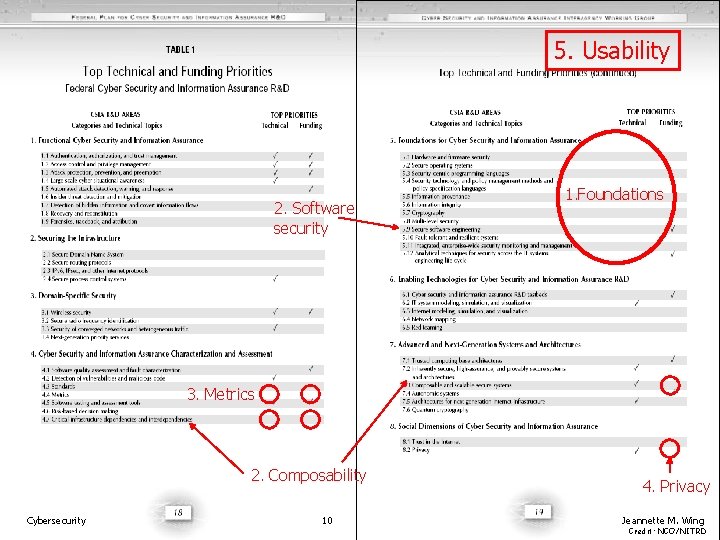
What’s Missing? 2. Software security 5. Usability 1. Foundations 3. Metrics 2. Composability Cybersecurity 10 4. Privacy Jeannette M. Wing Credit: NCO/NITRD
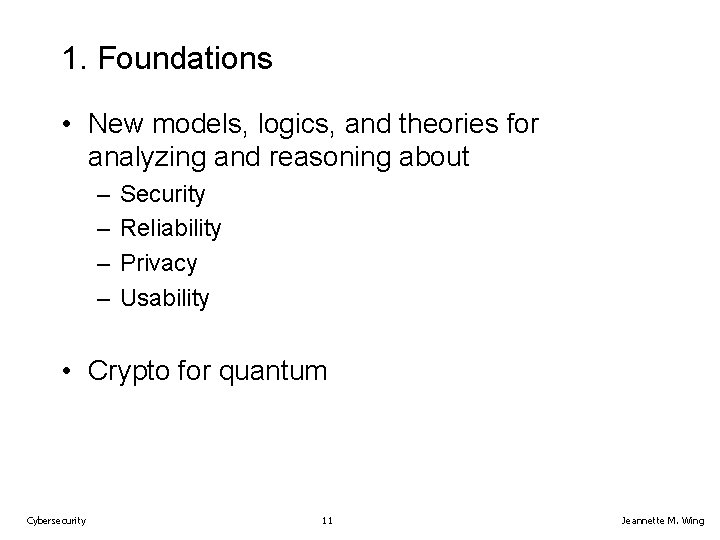
1. Foundations • New models, logics, and theories for analyzing and reasoning about – – Security Reliability Privacy Usability • Crypto for quantum Cybersecurity 11 Jeannette M. Wing
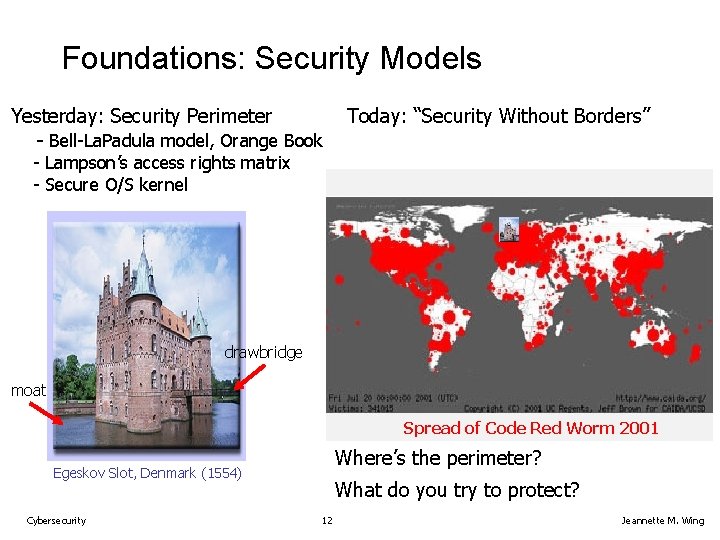
Foundations: Security Models Yesterday: Security Perimeter - Bell-La. Padula model, Orange Book Today: “Security Without Borders” - Lampson’s access rights matrix - Secure O/S kernel drawbridge moat Spread of Code Red Worm 2001 Where’s the perimeter? Egeskov Slot, Denmark (1554) Cybersecurity What do you try to protect? 12 Jeannette M. Wing
Foundations: Logics for Reasoning About Privacy • Do you read these? • What are they saying? • Can you trust them? This privacy statement goes on for seven screenfuls! Cybersecurity 13 Credit: Microsoft Jeannette M. Wing
Foundations: Cryptography Credit: Oxford University • Quantum/traditional cryptography immune to quantum-based attacks – Traditional cryptography based on RSA is breakable by Shor’s quantum algorithm Cybersecurity 14 Jeannette M. Wing
2. Security Architectures • What we have – Point solutions to point problems, e. g. , • Code-level solutions buffer overruns • Firewalls for intrusion detection • What we need – Integration of solutions • Up and down the vertical stack, from hardware to appl’ns. • At each layer, e. g. , routers and links at the network layer – Compositionality of components and services Cybersecurity 15 Jeannette M. Wing
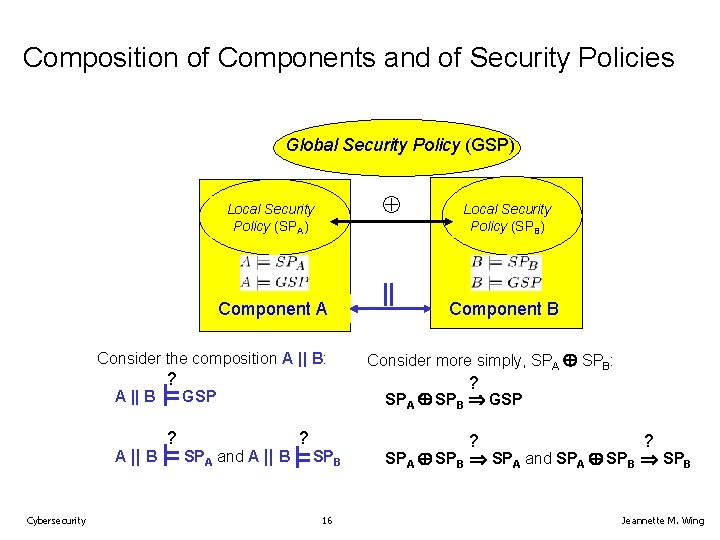
Composition of Components and of Security Policies Global Security Policy (GSP) Local Security Policy (SPA) Component A Consider the composition A || B: A || B Cybersecurity ? ? Component B Consider more simply, SPA SPB: ? GSP SPA and A || B || Local Security Policy (SPB) SPA SPB GSP ? SPB 16 ? ? SPA SPB SPA and SPA SPB Jeannette M. Wing
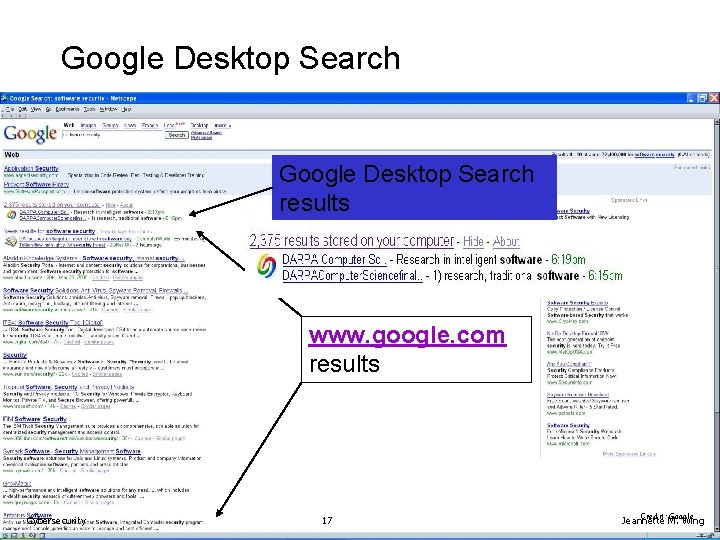
Google Desktop Search results www. google. com results Cybersecurity 17 Credit: Google Jeannette M. Wing
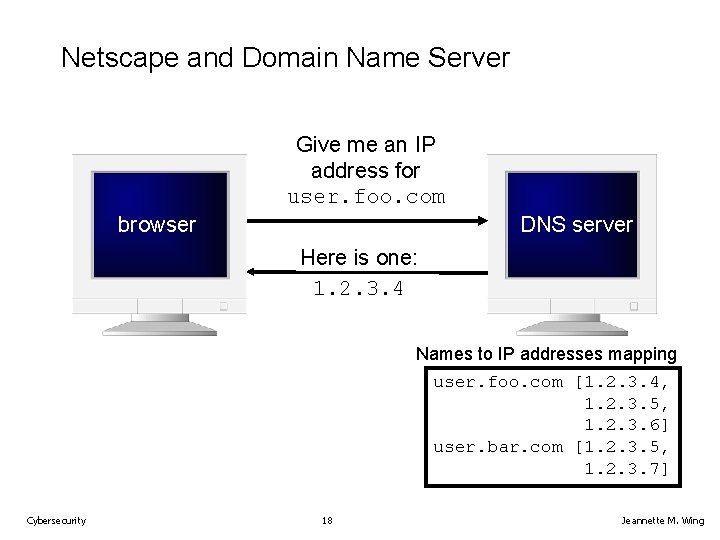
Netscape and Domain Name Server Give me an IP address for user. foo. com DNS server browser Here is one: 1. 2. 3. 4 Names to IP addresses mapping user. foo. com [1. 2. 3. 4, 1. 2. 3. 5, 1. 2. 3. 6] user. bar. com [1. 2. 3. 5, 1. 2. 3. 7] Cybersecurity 18 Jeannette M. Wing
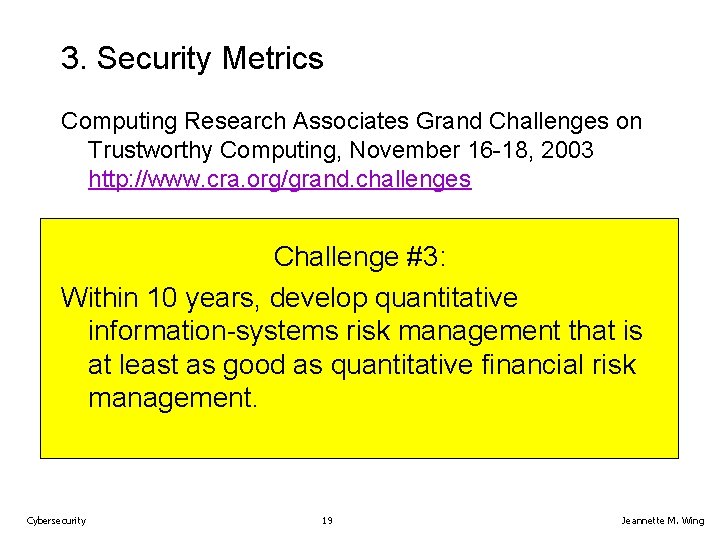
3. Security Metrics Computing Research Associates Grand Challenges on Trustworthy Computing, November 16 -18, 2003 http: //www. cra. org/grand. challenges Challenge #3: Within 10 years, develop quantitative information-systems risk management that is at least as good as quantitative financial risk management. Cybersecurity 19 Jeannette M. Wing
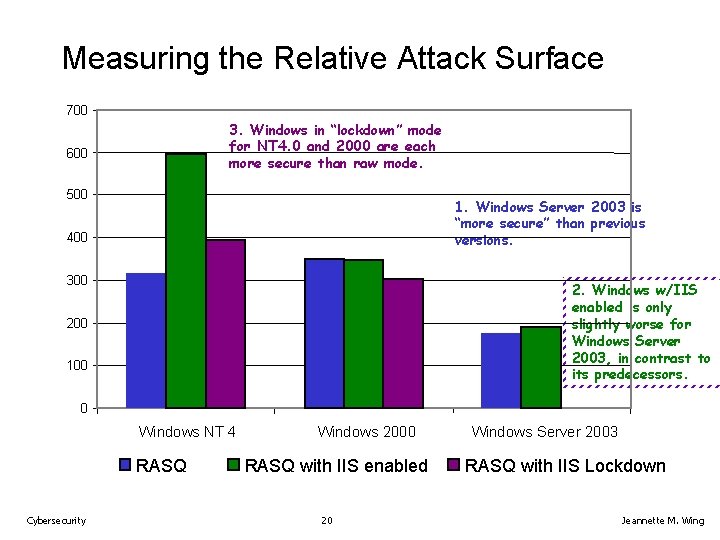
Measuring the Relative Attack Surface 700 3. Windows in “lockdown” mode for NT 4. 0 and 2000 are each more secure than raw mode. 600 500 1. Windows Server 2003 is “more secure” than previous versions. 400 300 2. Windows w/IIS enabled is only slightly worse for Windows Server 2003, in contrast to its predecessors. 200 100 0 Windows NT 4 RASQ Cybersecurity Windows 2000 RASQ with IIS enabled 20 Windows Server 2003 RASQ with IIS Lockdown Jeannette M. Wing
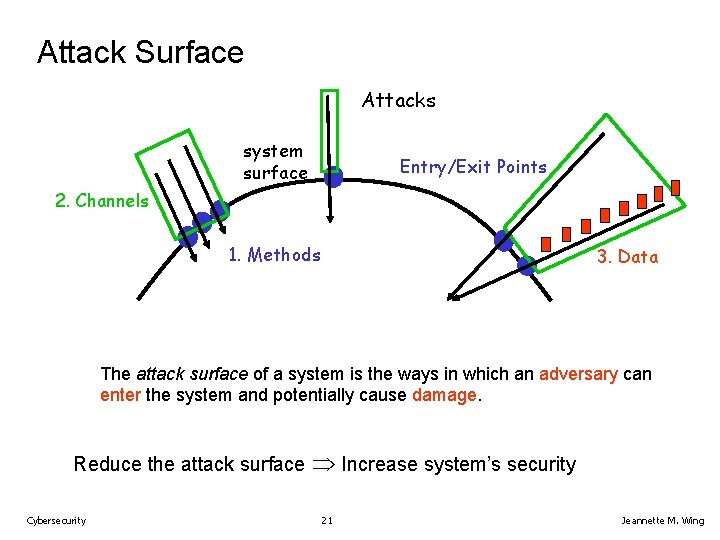
Attack Surface Attacks system surface Entry/Exit Points 2. Channels 1. Methods 3. Data The attack surface of a system is the ways in which an adversary can enter the system and potentially cause damage. Reduce the attack surface Cybersecurity Increase system’s security 21 Jeannette M. Wing
4. Privacy • Today: Threats to citizens’ privacy in many sectors of daily life – Health, financial, e-commerce, social networks, e-voting • Fundamental challenge: Once someone learns a secret about you, you cannot take away that knowledge – Different from security (e. g. , revoking access to a file, changing a lock on a door) Cybersecurity 22 Jeannette M. Wing
Privacy: A Few Questions to Ponder 1. What does privacy mean? 2. How do you state a privacy policy? How can you prove your system satisfies it? 3. How do you reason about privacy? How do you resolve conflicts among different privacy policies? 4. Are there things that are impossible to achieve wrt some definition of privacy? 5. How do you implement practical mechanisms to enforce different privacy policies? As they change over time? 6. How do you measure privacy? (Is that a meaningful question? ) Cybersecurity 23 Jeannette M. Wing
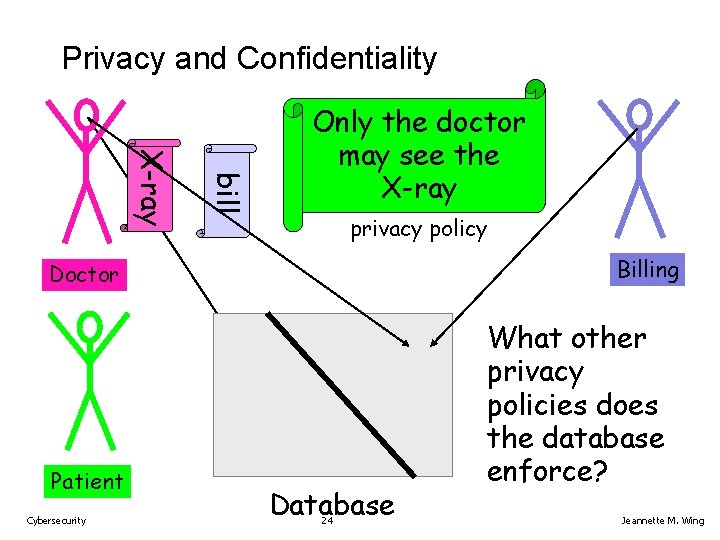
Privacy and Confidentiality bill X-ray Only the doctor may see the X-ray privacy policy Billing Doctor Patient Cybersecurity Database 24 What other privacy policies does the database enforce? Jeannette M. Wing
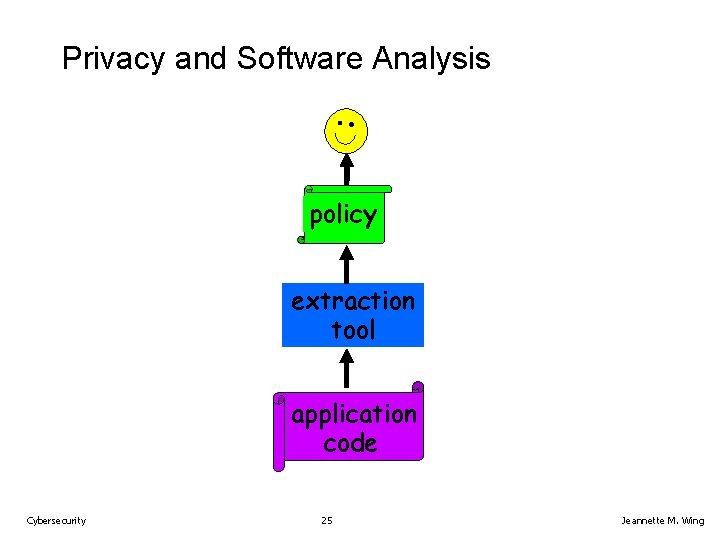
Privacy and Software Analysis policy extraction tool application code Cybersecurity 25 Jeannette M. Wing
5. Usability • The user is the weakest link in security. • Challenges – Striking a balance between control and convenience – Users are human. • Targets of social engineering attacks • Sources of insider threats Cybersecurity 26 Jeannette M. Wing
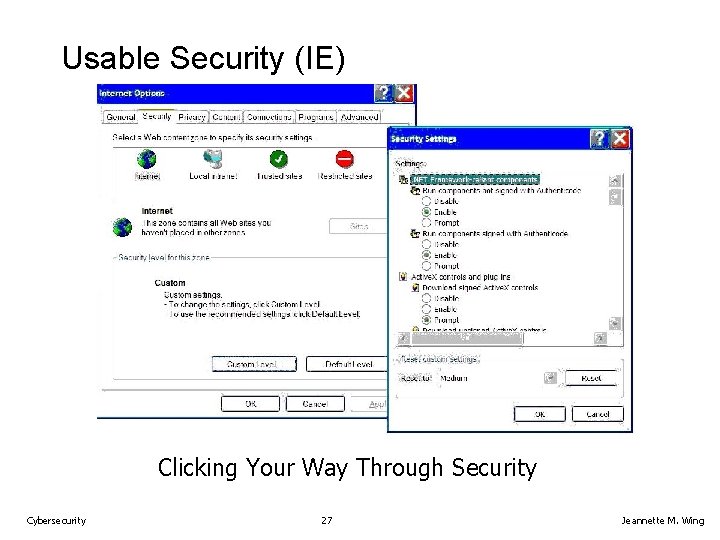
Usable Security (IE) Clicking Your Way Through Security Cybersecurity 27 Jeannette M. Wing
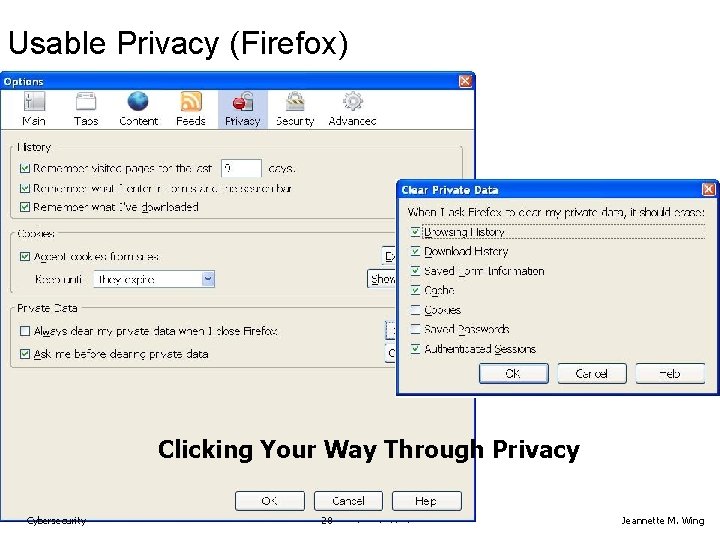
Usable Privacy (Firefox) Clicking Your Way Through Privacy Cybersecurity 28 Jeannette M. Wing
Summary of Research Challenges • New research foci 1. 2. 3. 4. 5. • Theoretical foundations: models, logics, crypto Software architecture Metrics Privacy Usability Enhanced investments in existing research foci: 1. Software security engineering 2. Networking 3. Testbeds Cybersecurity 29 Jeannette M. Wing
Summary of What’s Missing • Anticipate tomorrow’s threat. • Take a broad view. – Long-term – Holistic • Research – Basic research in new areas – Enhanced investments in existing areas • Education Cybersecurity 30 Jeannette M. Wing
Trustworthy Security Axiom Good guys and bad guys are in a never-ending race! Cybersecurity 42 Jeannette M. Wing
Thank you. Cybersecurity Jeannette M. Wing
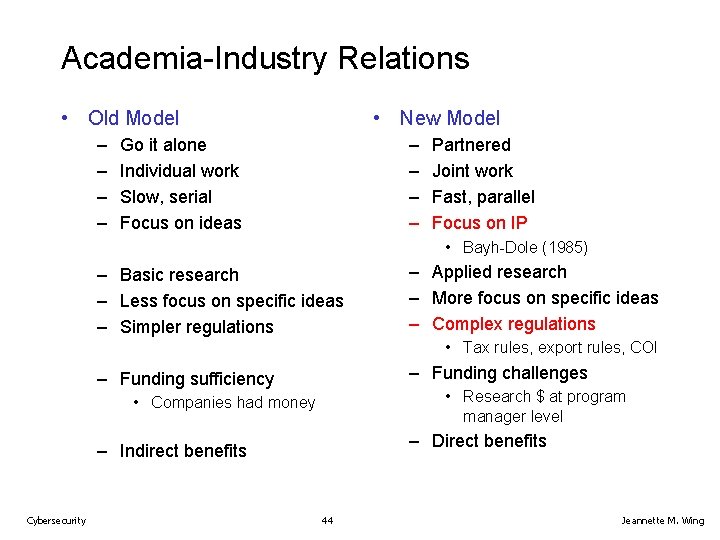
Academia-Industry Relations • Old Model – – • New Model – – Go it alone Individual work Slow, serial Focus on ideas Partnered Joint work Fast, parallel Focus on IP • Bayh-Dole (1985) – Basic research – Less focus on specific ideas – Simpler regulations – Applied research – More focus on specific ideas – Complex regulations • Tax rules, export rules, COI – Funding challenges – Funding sufficiency • Research $ at program manager level • Companies had money – Direct benefits – Indirect benefits Cybersecurity 44 Jeannette M. Wing
Credits • Copyrighted material used under Fair Use. If you are the copyright holder and believe your material has been used unfairly, or if you have any suggestions, feedback, or support, please contact: jsoleil@nsf. gov • Except where otherwise indicated, permission is granted to copy, distribute, and/or modify all images in this document under the terms of the GNU Free Documentation license, Version 1. 2 or any later version published by the Free Software Foundation; with no Invariant Sections, no Front-Cover Texts, and no Back-Cover Texts. A copy of the license is included in the section entitled “GNU Free Documentation license” (http: //commons. wikimedia. org/wiki/Commons: GNU_Free_Documentation_License) Cybersecurity 45 Jeannette M. Wing
- Slides: 34