Cybersecurity Patch 1 Curriculum Overview What is Cybersecurity

Cybersecurity Patch 1
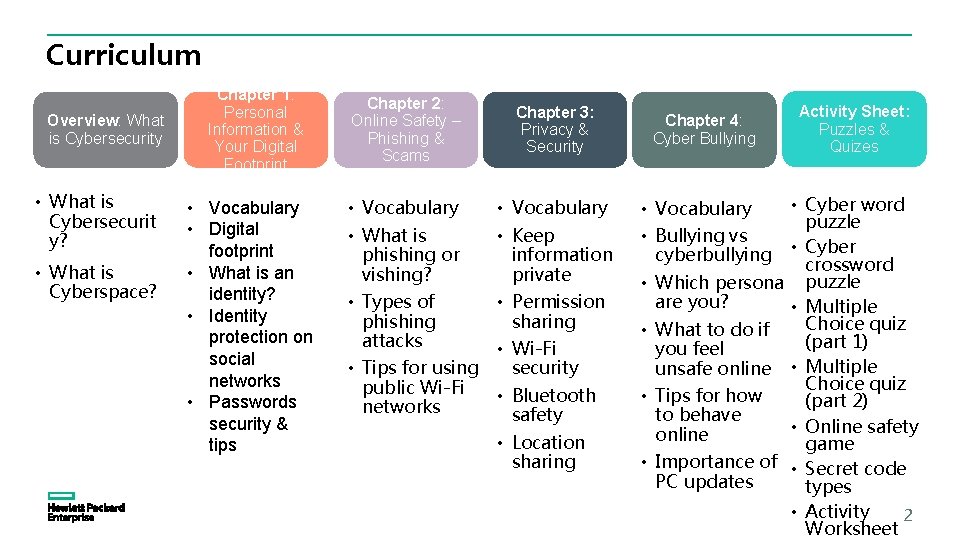
Curriculum Overview: What is Cybersecurity • What is Cybersecurit y? • What is Cyberspace? Chapter 1: Personal Information & Your Digital Footprint • Vocabulary • Digital footprint • What is an identity? • Identity protection on social networks • Passwords security & tips Chapter 2: Online Safety – Phishing & Scams • Vocabulary • What is phishing or vishing? • Types of phishing attacks • Tips for using public Wi-Fi networks Chapter 3: Privacy & Security • Vocabulary • Keep information private • Permission sharing • Wi-Fi security • Bluetooth safety • Location sharing Chapter 4: Cyber Bullying • Vocabulary • Bullying vs cyberbullying • Which persona are you? • What to do if you feel unsafe online • Tips for how to behave online • Importance of PC updates Activity Sheet: Puzzles & Quizes • Cyber word puzzle • Cyber crossword puzzle • Multiple Choice quiz (part 1) • Multiple Choice quiz (part 2) • Online safety game • Secret code types • Activity 2 Worksheet

Overview What is Cybersecurity? 3

What is Cybersecurity? Cybersecurity, computer security or IT security is the protection of your device from theft or damage to their hardware, software or electronic data. 4
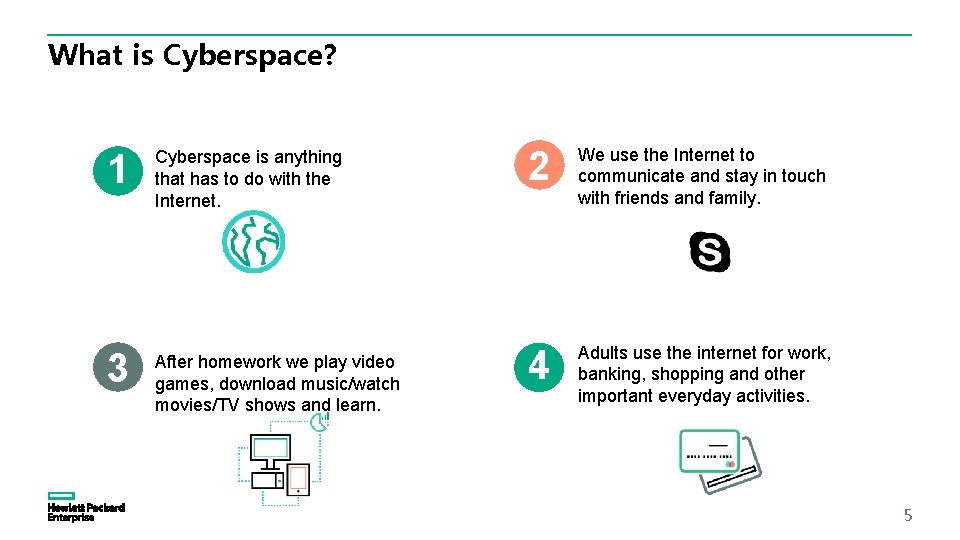
What is Cyberspace? 1 1. Cyberspace is anything that has to do with the Internet. 3 After homework we play video games, download music/watch movies/TV shows and learn. 2. 2 We use the Internet to communicate and stay in touch with friends and family. 4 Adults use the internet for work, banking, shopping and other important everyday activities. 5
Chapter 1 Personal Information & Your Digital Footprint 6
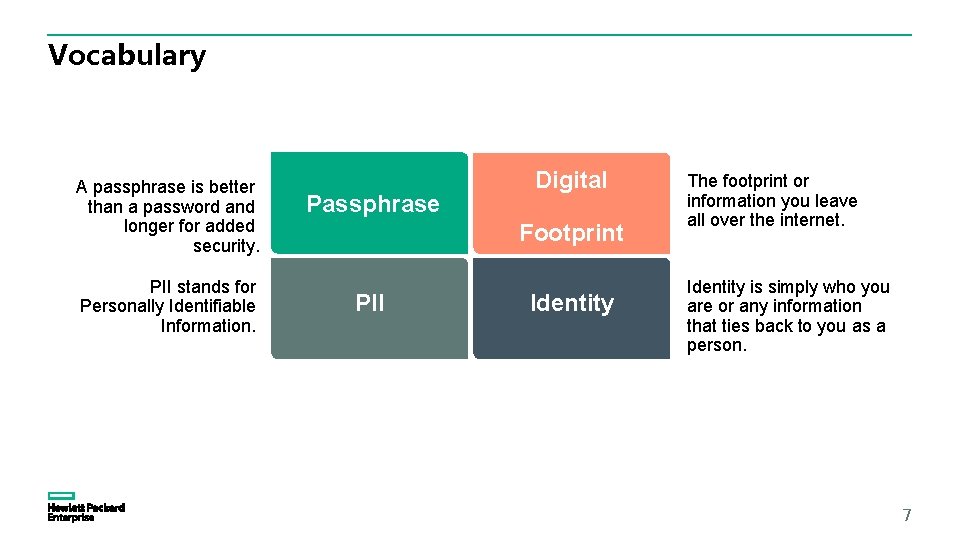
Vocabulary A passphrase is better than a password and longer for added security. PII stands for Personally Identifiable Information. Passphrase Digital Footprint PII Identity The footprint or information you leave all over the internet. Identity is simply who you are or any information that ties back to you as a person. 7
Digital Footprint We're used to looking at all kinds of information on the Internet, but the Internet, it seems, is looking back at us. When we visit websites to get information, share on social media, send instant messages and email, we leave something behind… Saving Digital Footprint Our digital footprints are the traces we leave behind as we use the Internet. Every time we consciously share information on social media or upload pictures, we lose some degree of privacy. 8
What is an Identity? Identity is simply who you are or any information that ties back to you as person. • It’s not just your name or username to access sites but passwords, SSN or any account numbers. • Your personal preferences, hobbies & other personal information create your identity in the cyber world. What do I look for? 8 Days Old Profile Picture Display Name vs Username Account Age/Set Up 9
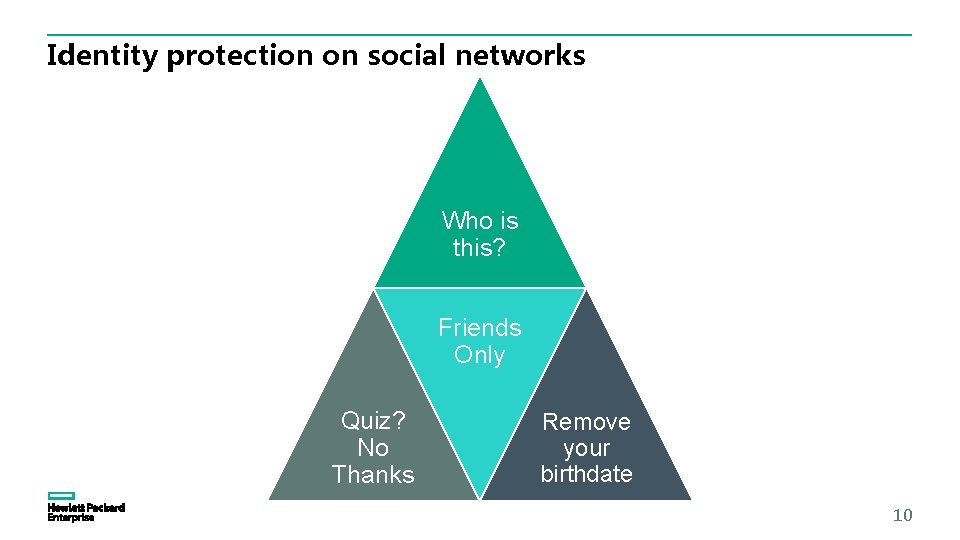
Identity protection on social networks Who is this? Friends Only Quiz? No Thanks Remove your birthdate 10
Passwords are like your toothbrush – Never share it! ‘’Want to borrow my toothbrush? ’’ ‘’Emm, no thanks!’’ 11
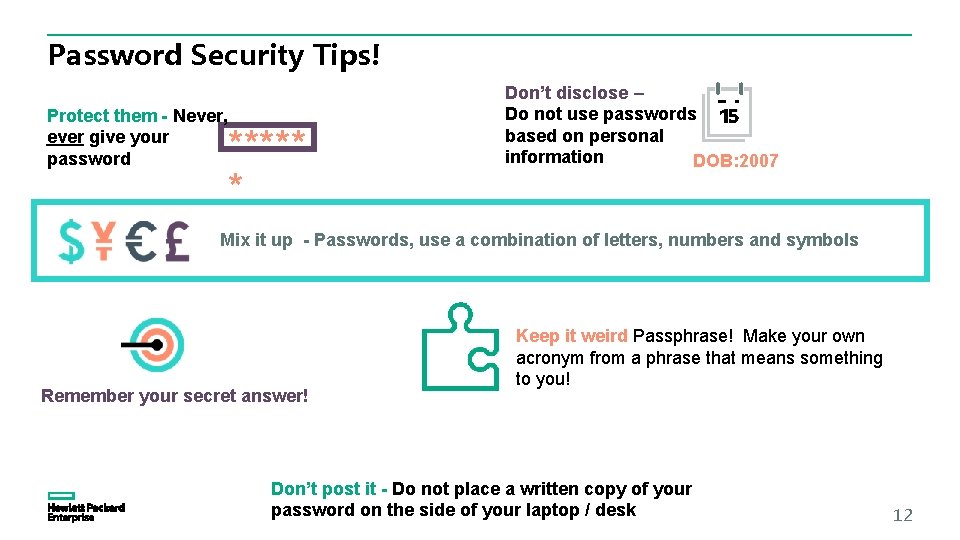
Password Security Tips! Protect them - Never, ever give your password ***** * Don’t disclose – Do not use passwords based on personal information DOB: 2007 Mix it up - Passwords, use a combination of letters, numbers and symbols Remember your secret answer! Keep it weird Passphrase! Make your own acronym from a phrase that means something to you! Don’t post it - Do not place a written copy of your password on the side of your laptop / desk 12
Chapter 2 Online safety – Phishing & Scams 13
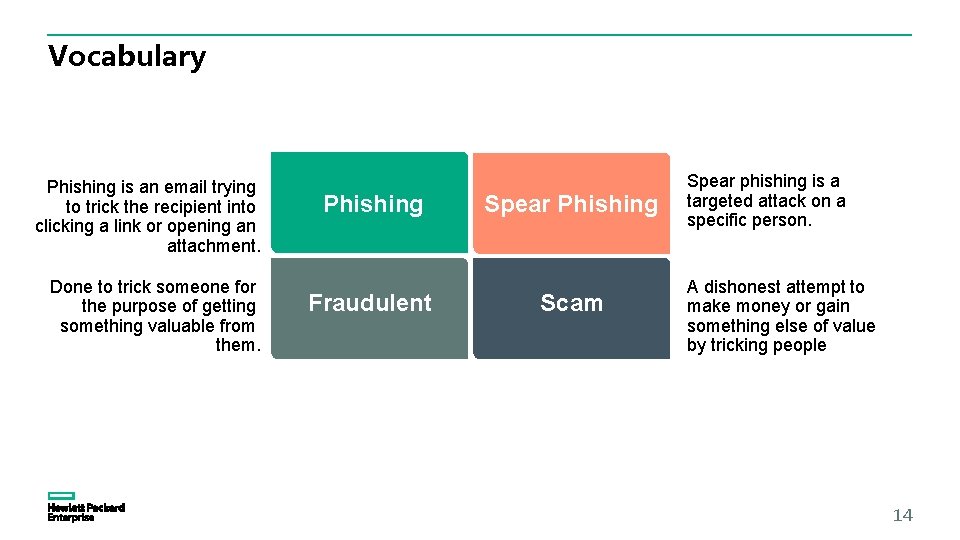
Vocabulary Phishing is an email trying to trick the recipient into clicking a link or opening an attachment. Done to trick someone for the purpose of getting something valuable from them. Phishing Fraudulent Spear Phishing Scam Spear phishing is a targeted attack on a specific person. A dishonest attempt to make money or gain something else of value by tricking people 14
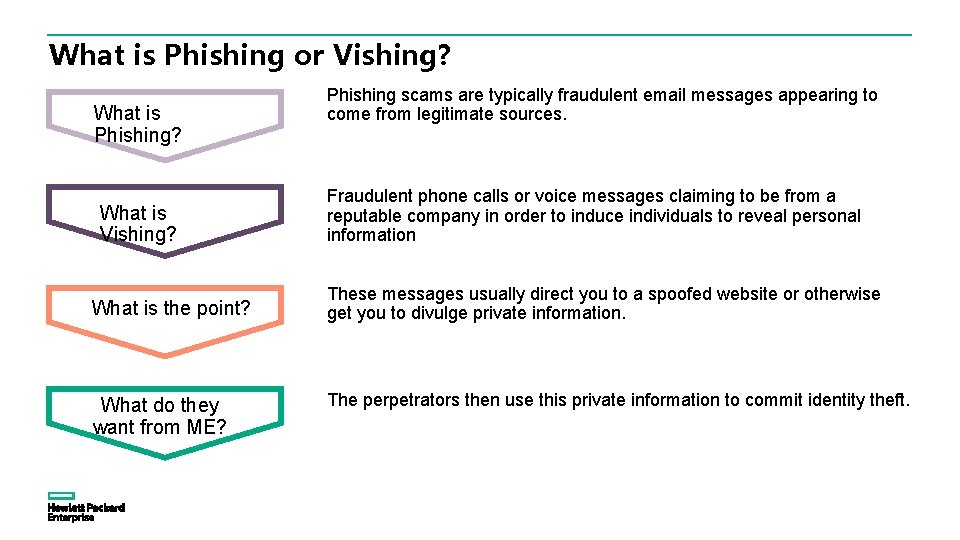
What is Phishing or Vishing? What is Phishing? What is Vishing? What is the point? What do they want from ME? Phishing scams are typically fraudulent email messages appearing to come from legitimate sources. Fraudulent phone calls or voice messages claiming to be from a reputable company in order to induce individuals to reveal personal information These messages usually direct you to a spoofed website or otherwise get you to divulge private information. The perpetrators then use this private information to commit identity theft.
The many faces of phishing attacks Social Engineeri ng Spear Phishing Vishing
Tips for using Public Wi-Fi Networks: § Free Wi-Fi hotspots EG hotels, buses, coffee shops, restaurants often are NOT secure. § This makes it easy for someone to access your online accounts and steal your personal information. § To reduce the risk, you should use encryption. § When information is encrypted, it means that it is scrambled into a code so that others cannot read it – only you. How to ensure your information is encrypted – § Use a secure connection to access the internet. Public Wi-Fi often has no encryption. This requires a WPA or WPA 2 password. If you are not sure – best to assume it’s not secure. § Use a secure website to send your information. For example: in https, the ‘s’ stands for secure. This will encrypt your information before you even send it. Look for the lock icon in every site that you visit. § If you use an unsecure Wi-Fi network to log in to an unencrypted website, strangers using that network can hijack your account and steal your private documents, contacts, family photos as well as your username and password. Steps to take when using public Wi-Fi – § Only log in and enter personal information to sites that use encryption (https ) § Don’t use the same username and password for various accounts. § Never email financial information, social security number or credit card information. § Don’t stay permanently signed into accounts – always log out after use. Reference: https: //www. consumer. ftc. gov/blog/2016/09/3 -videos-help-you-be-cyberaware 17
Ask yourself: Real World scenarios – Internet Scenarios: § Would you leave your front door open § Do you use the internet to talk to your or unlocked? friends? § Would you take a photo of yourself § Do you have your own personal profile and allow the world to see it? online? § Would you talk to strangers? § Do you add people as friends that you do § Would you tell a stranger where you not know? lived? § Do you talk to people online that you do § Would your parents approve of you not know? talking to strangers? Why do you § Do you have pictures on your profile that think this is? you would not like your parents to see? § Should you trust people you speak to § Can anyone see those photos (IE the that you have never met? public? ) § Would you like a stranger to have § Could someone find out where you live information about you - like where or go to school by your profile page? you like to hang out, when you go § Are you more careful about your safety in there and what your hobbies are? the real world than you are in the online § Would you let anyone look through world? your personal things? § Is it time this changed? Reference: https: //www. consumer. ftc. gov/blog/2016/09/3 -videos-help-you-be-cyberaware 18

Chapter 3 Privacy and Security 19
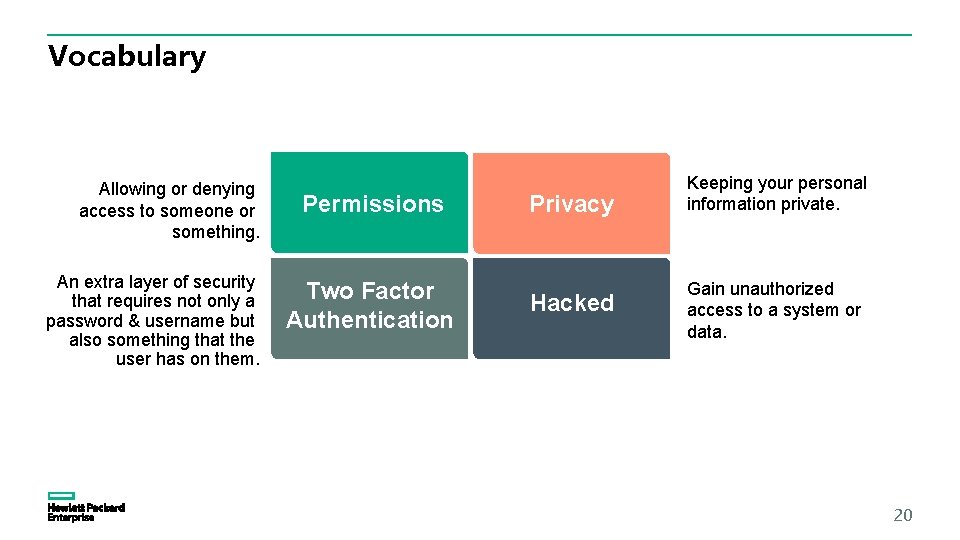
Vocabulary Allowing or denying access to someone or something. An extra layer of security that requires not only a password & username but also something that the user has on them. Permissions Two Factor Authentication Privacy Hacked Keeping your personal information private. Gain unauthorized access to a system or data. 20
Keeping information private • Never use your real name, address, number, birthday and password. • Identity theft uses this information to steal money or credit. • Generic usernames are safer. • Don’t enter competitions without permission. • If something seems too good to be true, it usually is. 21
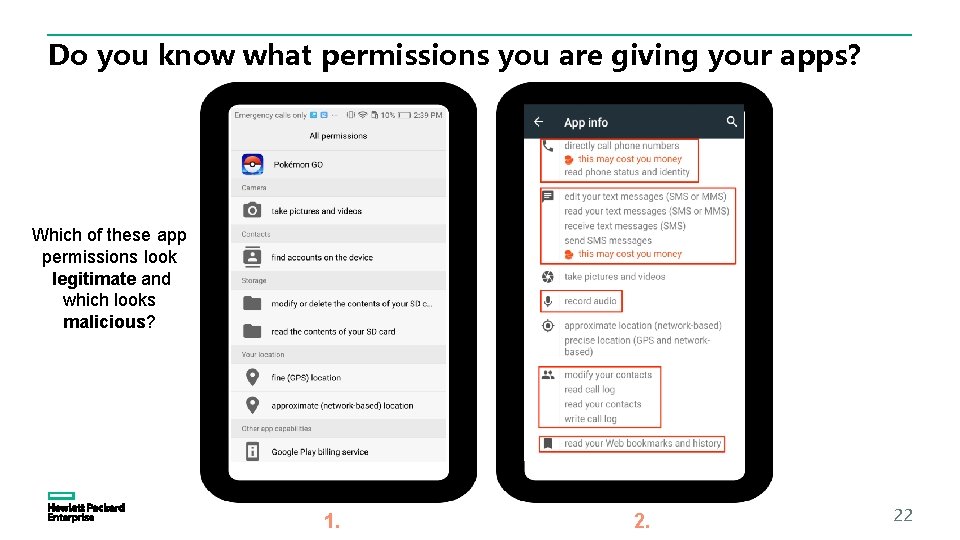
Do you know what permissions you are giving your apps? Which of these app permissions look legitimate and which looks malicious? 1. 22
Wi-Fi Security Do you know what Wi-Fi stands for? Answer: Wireless Fidelity 23
Accessing Wi-Fi Securely Ensure the Wi-Fi you are using requires a password ? Do you know why ****** ? This means the Wi-Fi is not open and people can’t see what you are typing or where you are surfing. If the Wi-Fi asks for a password, it means it will be harder for someone to snoop on what you are doing. 24
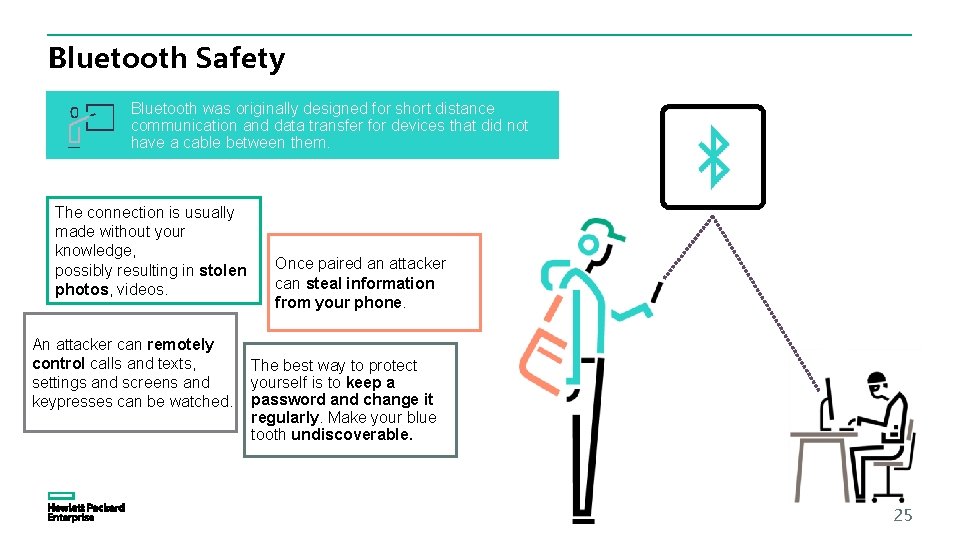
Bluetooth Safety Bluetooth was originally designed for short distance communication and data transfer for devices that did not have a cable between them. The connection is usually made without your knowledge, possibly resulting in stolen photos, videos. An attacker can remotely control calls and texts, settings and screens and keypresses can be watched. Once paired an attacker can steal information from your phone. The best way to protect yourself is to keep a password and change it regularly. Make your blue tooth undiscoverable. 25
Sharing your Location I am here! 26
Chapter 4 Cyberbullying 27
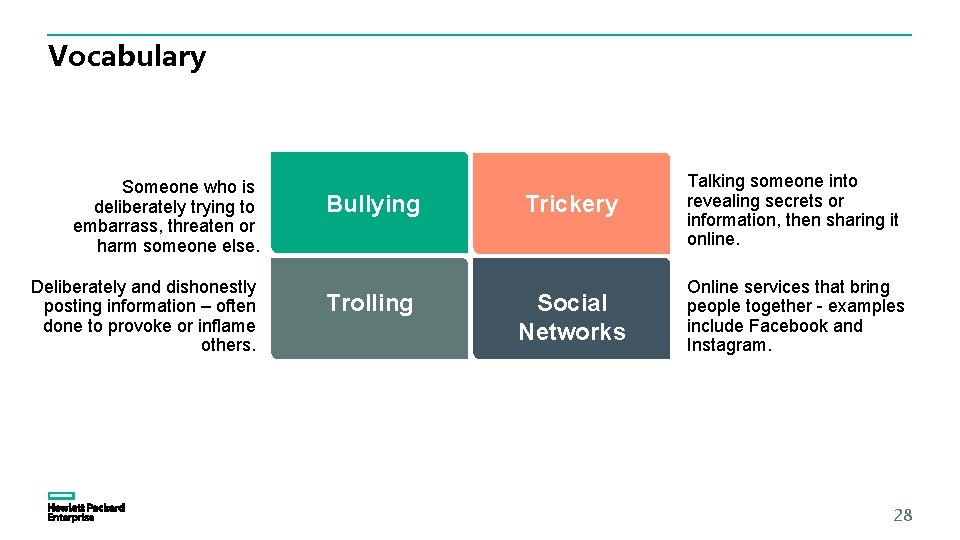
Vocabulary Someone who is deliberately trying to embarrass, threaten or harm someone else. Deliberately and dishonestly posting information – often done to provoke or inflame others. Bullying Trolling Trickery Talking someone into revealing secrets or information, then sharing it online. Social Networks Online services that bring people together - examples include Facebook and Instagram. 28
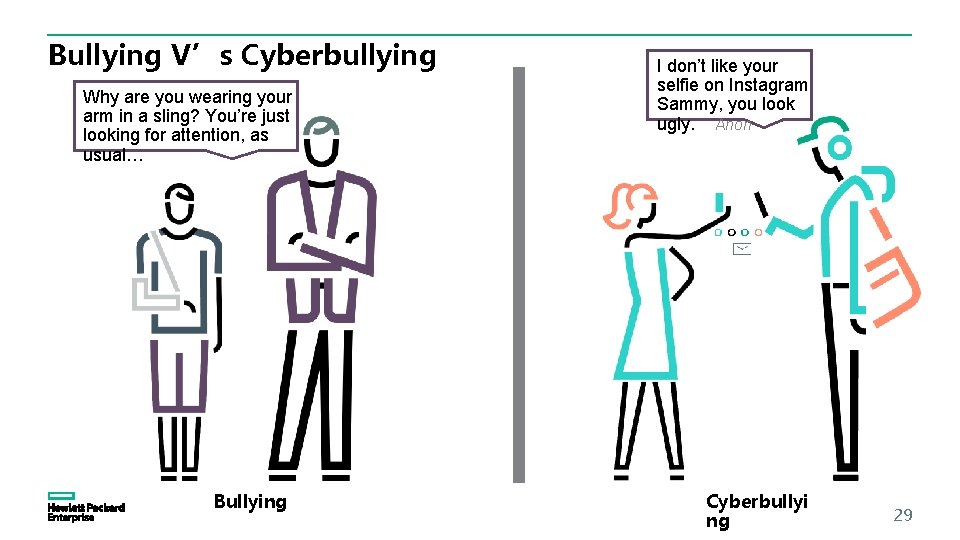
Bullying V’s Cyberbullying Why are you wearing your arm in a sling? You’re just looking for attention, as usual… Bullying I don’t like your selfie on Instagram Sammy, you look ugly. Anon Cyberbullyi ng 29
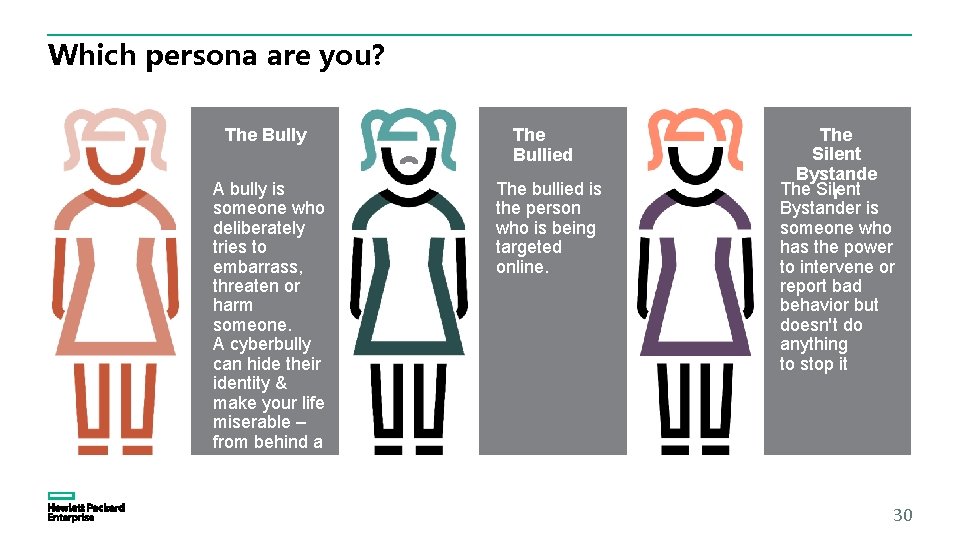
Which persona are you? The Bully A bully is someone who deliberately tries to embarrass, threaten or harm someone. A cyberbully can hide their identity & make your life miserable – from behind a screen. The Bullied The bullied is the person who is being targeted online. The Silent Bystande The Silent r Bystander is someone who has the power to intervene or report bad behavior but doesn't do anything to stop it 30
What to do if you feel unsafe online. Tell/Talk: Tell adults, parents or leaders and keep on telling until something is done Block: Block emails or messages – Don’t respond to them Report: Use online reporting tools – Most Social networking sites contain a reporting tool Record: Keep a record of bullying messages & when you received them. It may be easier to verify what went on and who the bully is 31
Tips for how to behave online 1. Treat others as you would like to be treated yourself. 2. Be respectful of others opinion, everybody has one. 3. Strive to include, help and encourage. 4. Avoid abusing or harassing others. 5. Avoid trolling people. 6. Think before your post! What's funny for you may be hurtful to others. 32
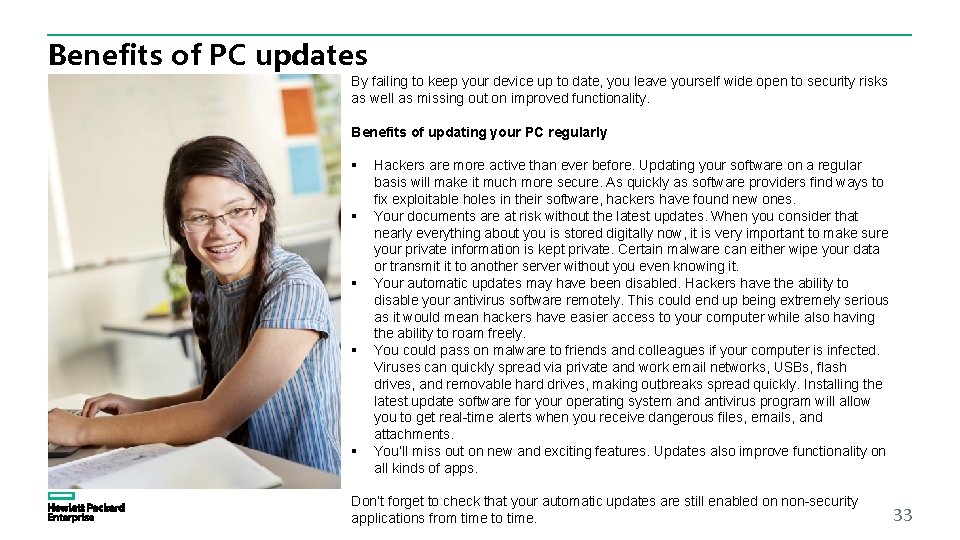
Benefits of PC updates By failing to keep your device up to date, you leave yourself wide open to security risks as well as missing out on improved functionality. Benefits of updating your PC regularly § § § Hackers are more active than ever before. Updating your software on a regular basis will make it much more secure. As quickly as software providers find ways to fix exploitable holes in their software, hackers have found new ones. Your documents are at risk without the latest updates. When you consider that nearly everything about you is stored digitally now, it is very important to make sure your private information is kept private. Certain malware can either wipe your data or transmit it to another server without you even knowing it. Your automatic updates may have been disabled. Hackers have the ability to disable your antivirus software remotely. This could end up being extremely serious as it would mean hackers have easier access to your computer while also having the ability to roam freely. You could pass on malware to friends and colleagues if your computer is infected. Viruses can quickly spread via private and work email networks, USBs, flash drives, and removable hard drives, making outbreaks spread quickly. Installing the latest update software for your operating system and antivirus program will allow you to get real-time alerts when you receive dangerous files, emails, and attachments. You’ll miss out on new and exciting features. Updates also improve functionality on all kinds of apps. Don’t forget to check that your automatic updates are still enabled on non-security applications from time to time. 33
Activity Sheet Puzzles & Quizes 34
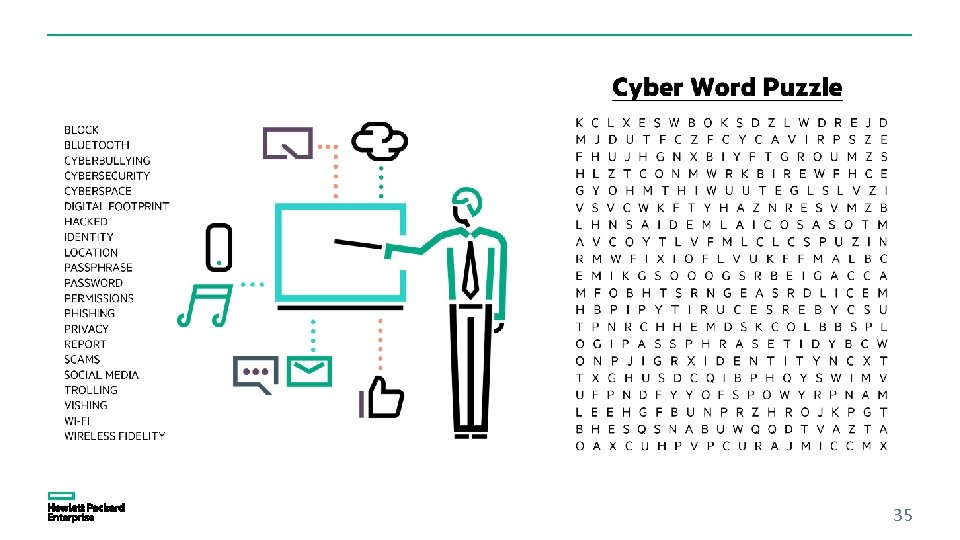
35
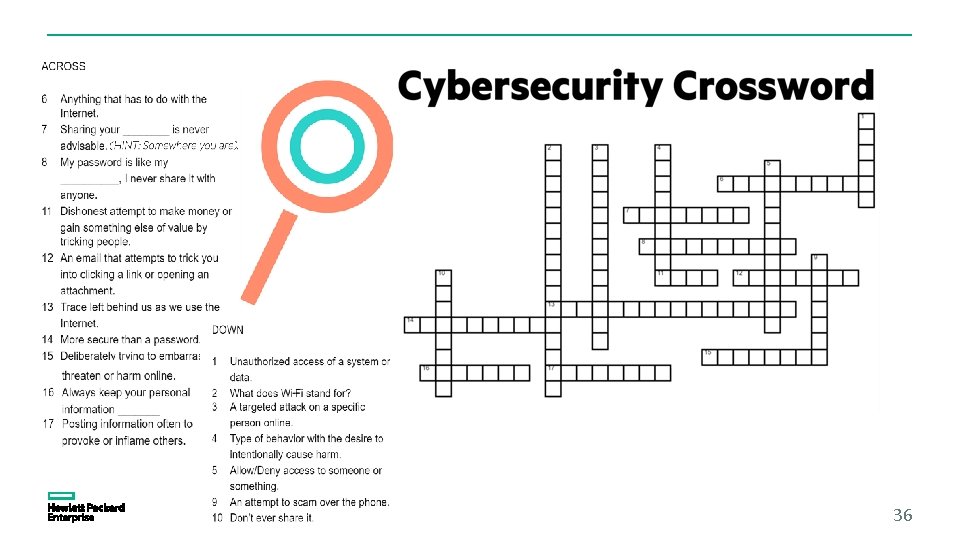
36
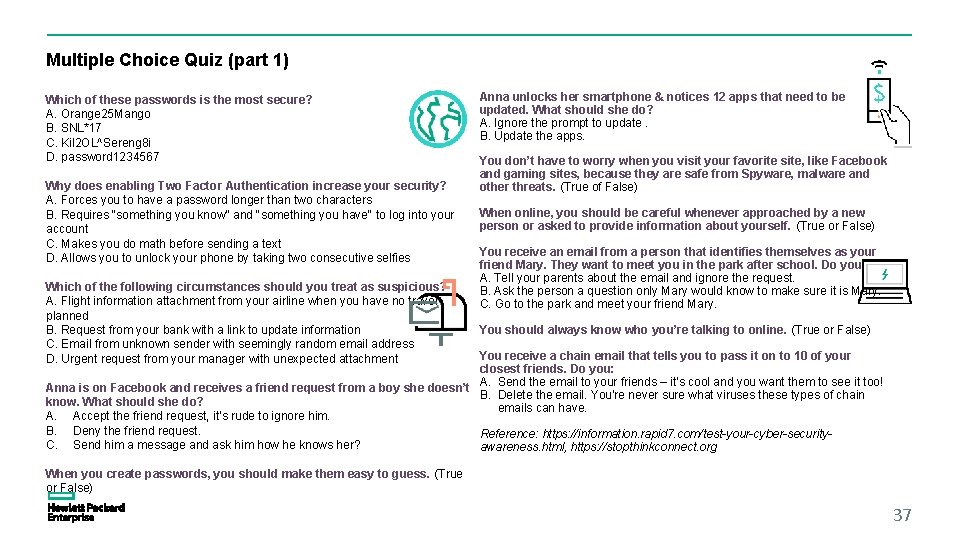
Multiple Choice Quiz (part 1) Which of these passwords is the most secure? A. Orange 25 Mango B. SNL*17 C. Kil 2 OL^Sereng 8 i D. password 1234567 Why does enabling Two Factor Authentication increase your security? A. Forces you to have a password longer than two characters B. Requires "something you know" and "something you have" to log into your account C. Makes you do math before sending a text D. Allows you to unlock your phone by taking two consecutive selfies Which of the following circumstances should you treat as suspicious? A. Flight information attachment from your airline when you have no travel planned B. Request from your bank with a link to update information C. Email from unknown sender with seemingly random email address D. Urgent request from your manager with unexpected attachment Anna unlocks her smartphone & notices 12 apps that need to be updated. What should she do? A. Ignore the prompt to update. B. Update the apps. You don’t have to worry when you visit your favorite site, like Facebook and gaming sites, because they are safe from Spyware, malware and other threats. (True of False) When online, you should be careful whenever approached by a new person or asked to provide information about yourself. (True or False) You receive an email from a person that identifies themselves as your friend Mary. They want to meet you in the park after school. Do you: A. Tell your parents about the email and ignore the request. B. Ask the person a question only Mary would know to make sure it is Mary. C. Go to the park and meet your friend Mary. You should always know who you’re talking to online. (True or False) You receive a chain email that tells you to pass it on to 10 of your closest friends. Do you: Anna is on Facebook and receives a friend request from a boy she doesn’t A. Send the email to your friends – it’s cool and you want them to see it too! B. Delete the email. You're never sure what viruses these types of chain know. What should she do? emails can have. A. Accept the friend request, it’s rude to ignore him. B. Deny the friend request. Reference: https: //information. rapid 7. com/test-your-cyber-security. C. Send him a message and ask him how he knows her? awareness. html, https: //stopthinkconnect. org When you create passwords, you should make them easy to guess. (True or False) 37
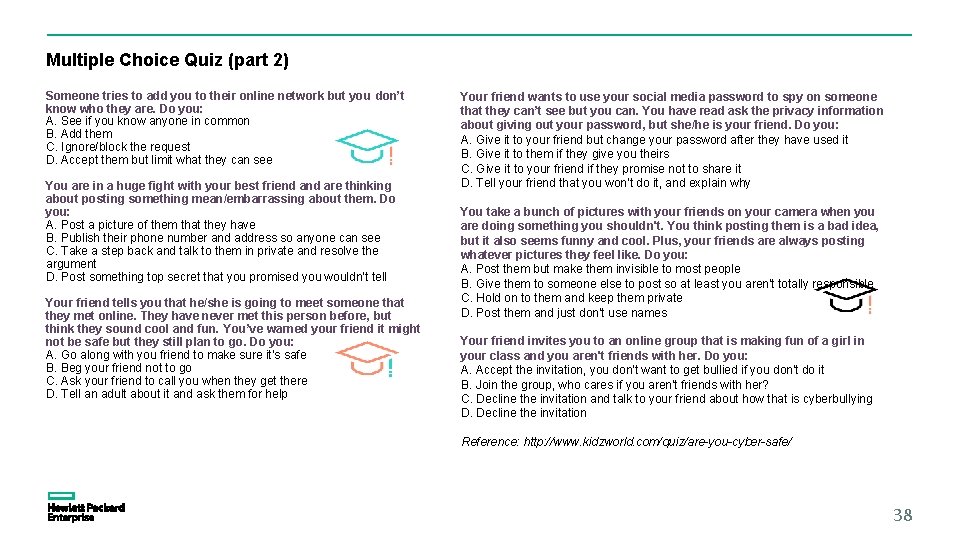
Multiple Choice Quiz (part 2) Someone tries to add you to their online network but you don’t know who they are. Do you: A. See if you know anyone in common B. Add them C. Ignore/block the request D. Accept them but limit what they can see You are in a huge fight with your best friend are thinking about posting something mean/embarrassing about them. Do you: A. Post a picture of them that they have B. Publish their phone number and address so anyone can see C. Take a step back and talk to them in private and resolve the argument D. Post something top secret that you promised you wouldn’t tell Your friend tells you that he/she is going to meet someone that they met online. They have never met this person before, but think they sound cool and fun. You’ve warned your friend it might not be safe but they still plan to go. Do you: A. Go along with you friend to make sure it’s safe B. Beg your friend not to go C. Ask your friend to call you when they get there D. Tell an adult about it and ask them for help Your friend wants to use your social media password to spy on someone that they can’t see but you can. You have read ask the privacy information about giving out your password, but she/he is your friend. Do you: A. Give it to your friend but change your password after they have used it B. Give it to them if they give you theirs C. Give it to your friend if they promise not to share it D. Tell your friend that you won’t do it, and explain why You take a bunch of pictures with your friends on your camera when you are doing something you shouldn't. You think posting them is a bad idea, but it also seems funny and cool. Plus, your friends are always posting whatever pictures they feel like. Do you: A. Post them but make them invisible to most people B. Give them to someone else to post so at least you aren't totally responsible C. Hold on to them and keep them private D. Post them and just don't use names Your friend invites you to an online group that is making fun of a girl in your class and you aren't friends with her. Do you: A. Accept the invitation, you don't want to get bullied if you don't do it B. Join the group, who cares if you aren't friends with her? C. Decline the invitation and talk to your friend about how that is cyberbullying D. Decline the invitation Reference: http: //www. kidzworld. com/quiz/are-you-cyber-safe/ 38
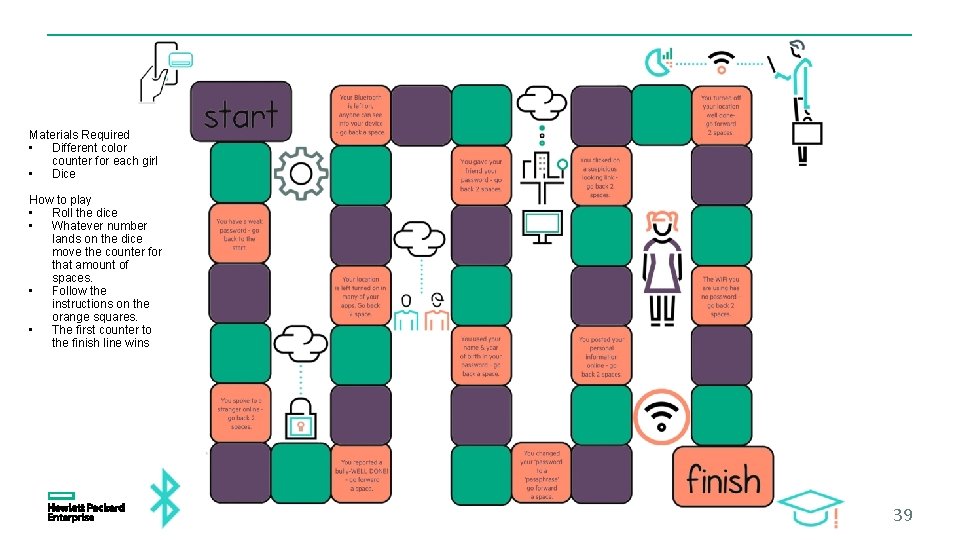
Materials Required • Different color counter for each girl • Dice How to play • Roll the dice • Whatever number lands on the dice move the counter for that amount of spaces. • Follow the instructions on the orange squares. • The first counter to the finish line wins 39
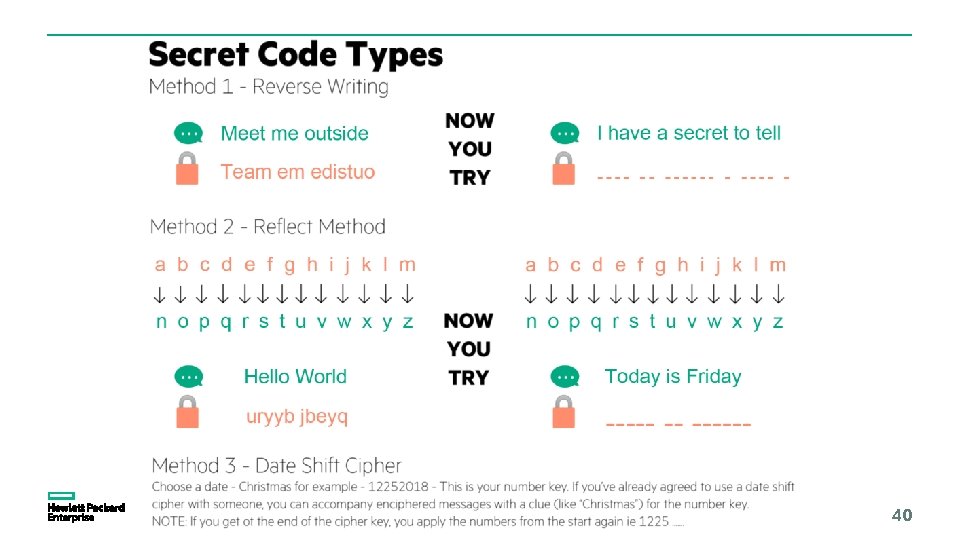
40
41
Activity Worksheet: Activity …. But say it nicely! Read the comments below. After each comment, discuss: § How could you have made the same or similar points in a more positive and constructive way? § If one of your classmates made comments like these, how could you respond in a way that would make the conversation more positive? Use the spaces below each comment to write down ideas. “Lol, Connor is the only one not going on the camping trip this weekend. ” “Everybody wear purple tomorrow and don’t tell Lilly. ” “Sorry I don’t think you can come to my party. It’ll cost too much money. ” “No offence but your handwriting is embarrassing so you should probably switch groups for this project. ” 42
Scenarios: WWYD What would you do? Tom has an Instagram account and wants to post a funny picture of his friend with a rip in his pants. Tom thinks this is really funny - should he post it? Amy loves listening to music on her i. Pod but was asked to let her parents know when she was downloading albums from i. Tunes as she ran up a huge bill last month. Her friend Mark told her about a great site where she could download songs for free. Should Amy tell her parents about the site? Matthew is in the house alone when the phone rings and the person on the phone says they are from Microsoft support and they have detected many viruses on his home computer. Should he give them access to the home PC without telling his parents? Jake is doing a school project and decides to check his emails. He sees two new emails, one from his grandad and one from luckywinner 2016 saying that he has won $500. Jake opens the email from luckywinner 2016 and clicks on a link to receive his $500. A popup appears telling Jake that his computer has been infected, what should Jake do? 43
Interactive Element See leader notes for activities HPE online cybersecurity awareness game 44
- Slides: 44