Cybersecurity Maturity Model Certification CMMC DEEP DIVE Legal


Cybersecurity Maturity Model Certification (CMMC) DEEP DIVE: Legal, Technology, Compliance Ed Bassett, Chief Information Security Officer, Neo. Systems LLC Eric Crusius, Partner, Holland & Knight Maureen Aubrey, Senior Info. Sec Consultant, Talatek LLC

Presenters Ed Bassett CISO, Neo. Systems LLC ed. bassett@neosystemscorp. com Eric Crusius Partner, Holland & Knight eric. crusius@hklaw. com Maureen Aubrey Senior Information Security Consultant, CISSP, CCSP maubrey@talatek. com

CMMC INTRODUCTION Setting the Stage
CMMC INTRODUCTION Setting the Stage • Surrounded by bad actors including insiders, terrorists, nation-states, criminal groups, hacktivists (such as Anonymous), corporate espionage. • Bad actors use various techniques including phishing, whaling, malware, and war driving. • It is more nuanced, but effectively Congress banned certain companies accused of being Russian and Chinese state actors in the 2018 and 2019 NDAA including Kaspersky, Huawei, and ZTE. • In late 2018, Congress established the Federal Acquisition Security Council. • Do. D enacted regulations putting cyber requirements on contractors.
CMMC INTRODUCTION • DFARS clause 252. 204 -7012 • Report Cyber Incidents within 72 hours • Implement NIST SP 800 -171 for minimum security controls • Must be inserted into every contract (and flowed down). There are no exceptions for small businesses or commercial buys. • DFARS clause 252. 246 -7008 • New requirements regarding sourcing of parts: supply chain responsibility on the contractor. • No exclusion for commercial items. • DFARS clause 252. 246 -7007 • If subject to federal Cost Accounting Standards, required to have a risk-based electronic part detection and avoidance system covering 12 key areas • CO can withhold payments if contractor is non-compliant. • DFARS clause 252. 204 -7009 • This clause minimizes the ways in which a contractor (assisting the government) can use information about a cybersecurity breach report. • Contractors must fashion protections, have employees sign NDAs, etc. • FAR Part 4. 19 (applicable to small businesses, but not COTS items) • Requires insertion of 52. 204 -21 Basic Safeguarding of Covered Contractor Information Systems which contains basic cybersecurity requirements and a flowdown requirement. • Agency-specific requirements
CMMC INTRODUCTION • The Cybersecurity Maturity Model Certification (CMMC) is designed to enhance the protection of controlled unclassified information (CUI) and Federal Contract Information (FCI) in the Do. D supply chain. Nearly all contractors probably possess FCI. • All Do. D contractors will be required to have a CMMC certification including: • Small businesses • Contractors that do not possess CUI or FCI • Subcontractors • Commercial contractors • CMMC is designed to build upon DFARS 252. 204 -7012 and NIST 800 -171, which is incorporated into that regulation. The DFARS regulation is a separate obligation and requires certain things that CMMC will not, such as notification of a breach to Do. D within 72 hours. Contractors must also provide Do. D access to impacted systems for Do. D’s own investigation.
CMMC INTRODUCTION • The Expected Process: • Do. D released CMMC version 0. 4, 0. 6, and 0. 7 • CMMC version 1. 0 was released January 31 • RFIs containing a CMMC requirement are expected in June 2020 • RFPs containing a CMMC requirement are expected in September 2020
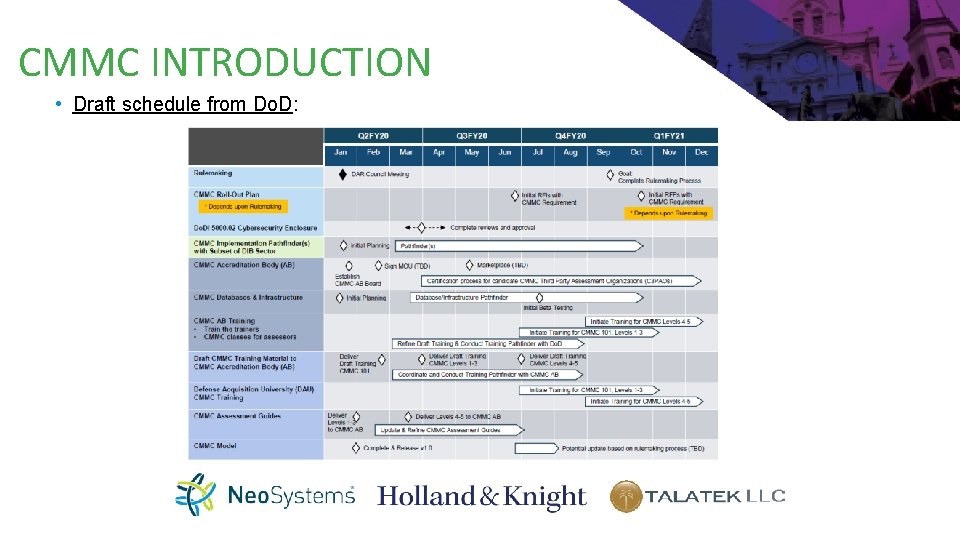
CMMC INTRODUCTION • Draft schedule from Do. D:
CMMC INTRODUCTION • What is Known About Certification: • Accrediting Body coming together • Accrediting Body will enter into an MOU with Do. D shortly • Accrediting Body will train the auditors and provide certifications in exchange for a fee charged to contractors being audited • Contractors will then be audited, but the order or exact timeframe is unknown • Currently, the accrediting body has seven working groups: • The Accrediting Body Scope • Governance • Commercial Standards • Adjudication • Organizational Structure • CMMC Change Management • Budget

CMMC INTRODUCTION • What is Known About Certification: • Certification is not one size fits all. There are five levels of certification with Level 5 being the most stringent and Level 1 being the most basic. Level 3 is expected to hew closely to NIST 800 -171. • Auditors for Level 4 and Level 5 will require additional training. • Certification will be required upon award. Certification is not necessary during the bid and proposal stage. • Required certification level will be in the RFP. The Do. D agency will have discretion to specify the certification level required at award. • The CMMC requirement must be flowed down to subcontractors. • Hundreds of thousands of contracts will need to be certified FAST. Will Do. D be able to meet this aggressive timeline?
CMMC INTRODUCTION • Intended and Unintended Consequences: • May drive away businesses from Do. D supply chain including companies with emerging technologies • This bucks trend of decreasing regulatory requirements • CMMC level requirements may be a way to artificially limit competition and could emerge as a pre-award protest ground • May cause decrease in cybersecurity-related False Claims Act cases

Breaking Down The CMMC Requirements What you need to know to prepare now!

CMMC REQUIREMENTS “M” is for Maturity

What It Will Take to Achieve Certification Source: Cybersecurity Maturity Model Certification (CMMC), version 1. 0, January 30, 2020 Find the latest CMMC documents here: https: //www. acq. osd. mil/cmmc/draft. html
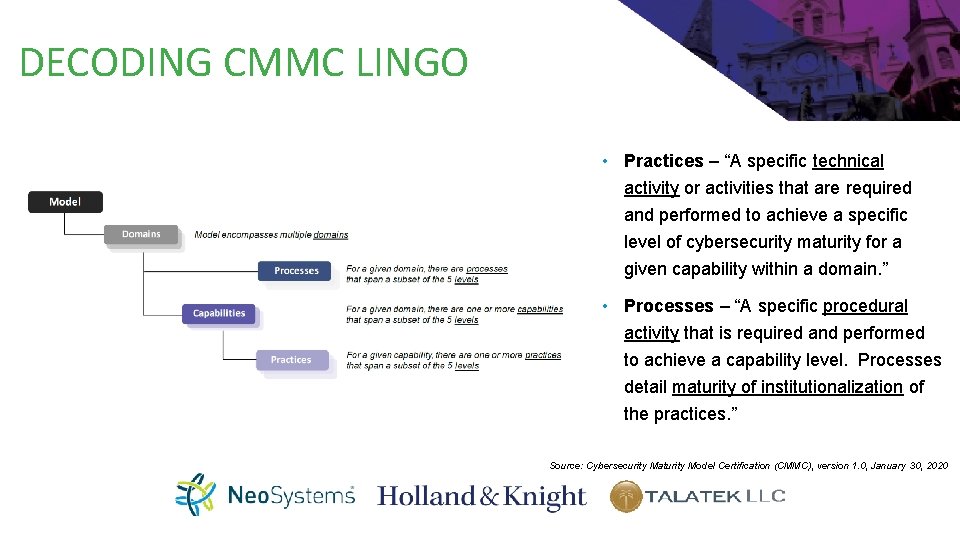
DECODING CMMC LINGO • Practices – “A specific technical activity or activities that are required and performed to achieve a specific level of cybersecurity maturity for a given capability within a domain. ” • Processes – “A specific procedural activity that is required and performed to achieve a capability level. Processes detail maturity of institutionalization of the practices. ” Source: Cybersecurity Maturity Model Certification (CMMC), version 1. 0, January 30, 2020
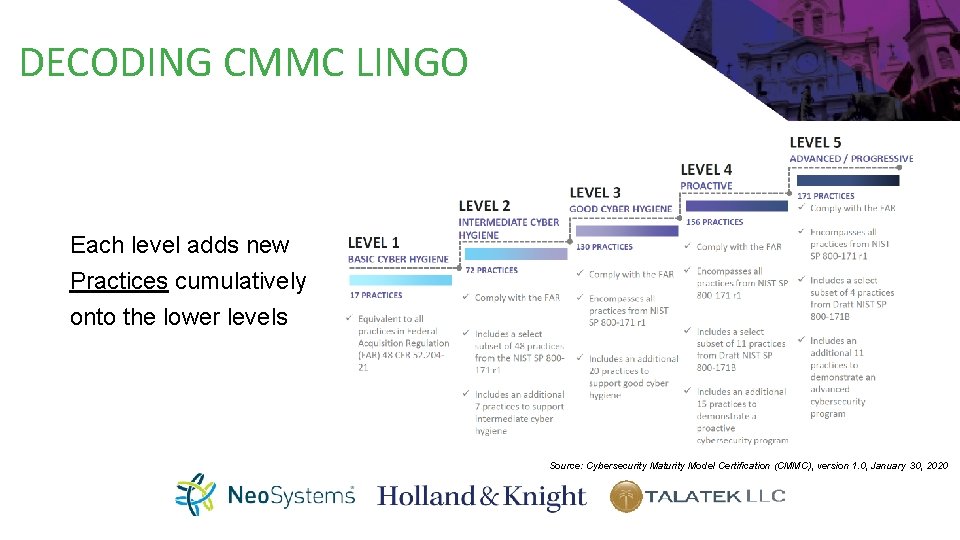
DECODING CMMC LINGO Each level adds new Practices cumulatively onto the lower levels Source: Cybersecurity Maturity Model Certification (CMMC), version 1. 0, January 30, 2020
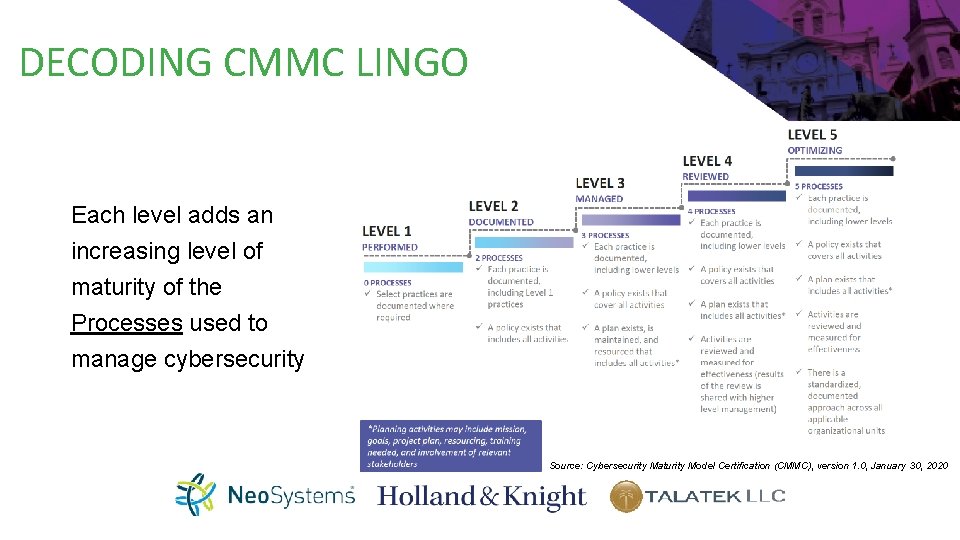
DECODING CMMC LINGO Each level adds an increasing level of maturity of the Processes used to manage cybersecurity Source: Cybersecurity Maturity Model Certification (CMMC), version 1. 0, January 30, 2020
LEVEL 1: BASIC CYBER HYGENE • This level is intended to be equivalent to the requirements in FAR 48 CFR § 52. 204 -21 for safeguarding of Federal Contract Information (FCI) in covered contractor information systems. • 17 Practices (technical activities) covering: • • Limit access Identify users Sanitize media Limit physical access Protect networks Find and fix system flaws Stop malware • At this level, it is sufficient to demonstrate that you “perform” the practices. There is no measurement of process maturity required. You may have limited or inconsistent processes.
LEVEL 2: INTERMEDIATE CYBER HYGENE • This level is intended as a transition step to protecting Controlled Unclassified Information (CUI). Do. D has stated there will be few, if any, contracts issued that require Level 2. • 72 Practices (technical activities) adding: • Least privilege • Control data flows, including paper and digital • Audit logging • Awareness and training • System hardening and configuration management • Password strength • Incident handling • At this level, you must establish policies for each of the capability domains and document the practices so as to perform them in a repeatable way.
LEVEL 3: GOOD CYBER HYGENE • This level is intended to be equivalent to the requirements NIST SP 800 -171 Rev 1 specified under DFARS 252. 204 -7012 for safeguarding of Controlled Unclassified Information (CUI) and Covered Defense Information (CDI) in contractor information systems. • 130 Practices (technical activities) adding: • Separation of duties • Control mobile devices • Encryption (FIPS-validated) • Centralized audit log management • Software blacklisting or whitelisting • At this level, you must demonstrate that you establish and maintain plans for each of the capability domains and allocate adequate resources to meet the plans.
LEVEL 4: PROACTIVE CYBER HYGENE • Cybersecurity programs at this level are intended to reduce the risk from Advanced Persistent Threats (APTs) • 156 Practices (technical activities) adding: • Situational awareness • Threat intelligence • Automated discovery • Automated analysis/alerting • Exercises • Application whitelisting • 24/7 response • At this level, you must demonstrate a process to review and measure activities for effectiveness, review the status with high-level management and resolve issues.
LEVEL 5: ADVANCED/PROGRESSIVE CYBER HYGENE • 171 Practices (technical activities) adding: • Code signing • Automated real-time response • Unannounced exercises • Redundancy • Packet capture • Tailored (bespoke) boundary protections • Behavioral analysis • At this level, you must demonstrate optimized processes for each control such that you standardize the approach across the organization and share improvements.
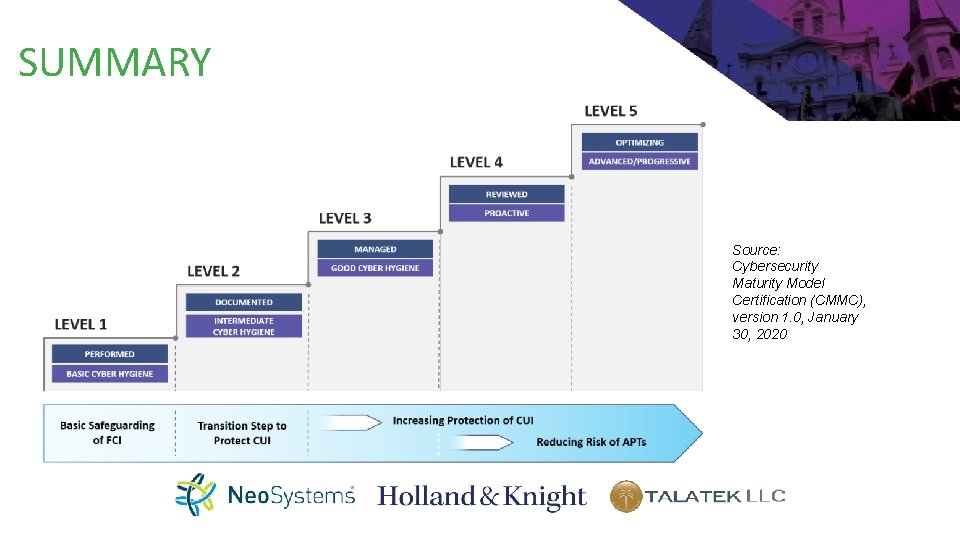
SUMMARY Source: Cybersecurity Maturity Model Certification (CMMC), version 1. 0, January 30, 2020

HOW TO PREPARE CHARTING THE PATH TO CMMC CERTIFICATION

CHART THE PATH • Think about scope and segmentation • Understand gaps in both security management processes and technical practices • Work on maturity gaps first – policies, procedures, plans • Select technical solutions that fill practices gaps

PARTNER • For any CMMC level above Level 1, consider a specialized security services provider who can provide: • Accelerated process maturity • Access to specialized skillsets • Turnkey technical solutions • Evaluate technology partner and service provider commitment to meeting CMMC requirements • Use cloud services to shift portions of the compliance burden

ISN’T THERE AN EASIER WAY?

A FEW IDEAS… SELF ATTESTATION VS. ASSESSMENT • This is one of the major differences between 800 -171 and CMMC – entities seeking certification will have to engage a C 3 PAO to perform the assessment and issue a recommendation on certification • These type of independent assessments will require entities seeking certification be able to demonstrate they are meeting the requirements of the level of certification they seek • There will need to be documented Evidence • Personnel will need to be able to speak to Capabilities • All Capabilities should be fully demonstrable
IT’S ALL ABOUT THE DETAILS • Security Audits are designed to be methodical and meticulous – auditors will go down the list of requirements and test each one • You must be able to demonstrate that you have implemented each requirement commensurate with the Level you are trying to achieve • Having documentation and evidence is essential – Even for Level 1 documentation will make demonstrating the required practices so much easier
IT’S ALL ABOUT THE DETAILS ACCESS CONTROL (AC. 1. 002) – LIMIT INFORMATION SYSTEM ACCESS TO THE TYPES OF TRANSACTIONS AND FUNCTIONS THAT AUTHORIZED USERS ARE PERMITTED TO EXECUTE Plain English – Make sure to limit users/employees to only the systems, roles or applications they are permitted to use and that are needed for their job How Can I Demonstrate This? Wouldn’t life be easier if you had a document that listed all your company’s users in one location? - This can be simple – word document, spreadsheet, quick book, etc. Instead of a document you could utilize an access management system – Think Active Directory Just for your own piece of mind wouldn’t you want to review this access every once in a while? All of a sudden you’re moving into Level 4 and 5 territory!

PREPARING FOR AN AUDIT THERE’S A LOT TO DO BUT IT CAN BE DONE • We know that Level 3 CMMC includes all 110 requirements of NIST 800 -171 with 20 additional requirements – For a total of 130 practices • Think about what Level is going to be acceptable for your organization – if you process CUI, technically 800 -171 is the law. • Level 1 is only meant for the processing of FCI • Level 2 is only meant to be a step to get to Level 3 • You should start by conducting a Gap Analysis of NIST 800 -171 – put a roadmap into place to address any gaps • Continue to monitor developments as the CMMC program matures • Don’t be afraid to reach out to partners for help • Security Audits can be confusing but there are plenty of people that can help
PREPARING FOR AN AUDIT • As auditors we have to be intimately familiar with all requirements of a certification program. • This includes the processes of the actual certification • Real-world knowledge of the processes and practices – we tend to speak in plain English • We specialize in Gap Analysis and creating an actionable road map to help our clients achieve the certification they are seeking. This can be: • From the ground up • Maturing from level to level • Utilizing information from one certification program to fit another program AUDITORS AREN’T THE DEVIL: WE CAN HELP!
PREPARING FOR AN AUDIT YOU KNOW HOW MANY PERFECT AUDITS I’VE CONDUCTED? ZERO • CMMC is coming – you will need to be able to demonstrate all processes and practices of your desired level • What if you are currently falling short? That’s OK! – It’s all part of the process • This is where proactively addressing deficiencies from any Gap Analyses and/or internal audits comes into play • At the end of an audit or Gap Analysis you will have a Plan of Action and Milestones (POA&M) – Think of it as a Road Map for making you more secure and compliant with the coming certification requirements

POTENTIAL PITFALLS: THERE’S ALWAYS SOME! • Do. D has stated that there are potentially 350, 000+ vendors that will need to be certified through CMMC – they have targeted a FY 21 FY 25 phased rollout approach - Starting FY 26 all new contracts will contain CMMC requirement • This timeline is still relatively intensive • Fed. RAMP program is comparable and in the 10 years its in existence it has issued 170 accreditations • CMMC has been discussed as an organizational certification however, there are numerous system-specific practices defined in the CMMC model • If this is the case how will boundaries be established? (i. e. ; when an auditor comes in to audit, what exactly will they be looking at? ) • The importance of boundaries cannot be overstated and this is something Do. D and the CMMC Accreditation Body will have to consider and define • This could lead to organizations having to obtain multiple CMMC certifications
Current assessment assumptions: based on what we know to this point • While I can’t speak to the exact cost of the certification audits – we don’t know the depth and breadth of the assessments yet – I can say that the audit cost will be based on the Level of Certification an entity is trying to achieve (i. e. ; Level 1 audits will cost less than Level 2 and so on and so forth) • An entity will have to maintain their certification – this will likely mean annual assessments – though the accreditation body and Do. D may decide to lengthen the period in between audits – The cost of certification will not be a one-time cost • Level 3 is likely going to be the most requested Level in RFP vehicles as it is most similar to 800 -171 • Level 4 and 5 will likely be reserved for main service providers to Do. D – The 24/7 SOC requirement is very limiting for these levels – small business will have a hard time meeting these requirements • Level 1 will likely only be allowed by enth-party providers that only have access to FCI – doubt this certification Level will provide much value added • Given the establishment of an Accreditation Body and general failure of the 800 -171 self-attestation model, there is likely going to be a fair amount of oversight – companies will benefit from getting their certification done early, before all the rules and regulations are established

Contact Information • Managed Security Services – solutions providing full coverage of administrative and technical CMMC requirements for Do. D contractors • • Managed IT Services – network, server, workstation, and user support • Government contract litigation and expertise in compliance issues specific to government contractors including Service Contract Act (SCA), small business, trade agreements, supply chain, subcontracting, and teaming and compliance • Expertise in regulatory requirements including the Federal Acquisition Regulation (FAR) and agency regulatory supplements • Provides advice in cybersecurity regulatory requirements including NIST 800 -171 and CMMC • Accredited 3 PAO through the Fed. RAMP program and will obtain C 3 PAO status as soon as requirements are released • Assist in an advisory role to align organizations with 800 -171 and CMMC requirements, provide gap analysis and a roadmap to achieve certification • Perform C 3 PAO audits to help firms achieve the CMMC certification level desired and provide recommendations to remediate any findings discovered during assessments Fed. RAMP Ready cloud hosting – secure enclave for ERP applications and hosted desktops

Q&A / CONTACT US Ed Bassett CISO, Neo. Systems LLC ed. bassett@neosystemscorp. com Eric Crusius Partner, Holland & Knight eric. crusius@hklaw. com Maureen Aubrey Senior Information Security Consultant, CISSP, CCSP maubrey@talatek. com
- Slides: 38