Cybersecurity Liberal Arts Workshop Xenia Mountrouidou Dr X
Cybersecurity + Liberal Arts Workshop Xenia Mountrouidou (Dr. X)
Outline • Motivation • Cybersecurity & Liberal Arts • Cyber Paths – Liberal Arts – GENI
Motivation: Cybersecurity Education Challenges • Cybersecurity: fast paced, changing field • Predominantly undergraduate institutions have limited resources • Experiential learning in cybersecurity requires large investments
Cybersecurity Education: Solutions • General education can feed diverse cohorts to the cybersecurity profession • Cloud computing infrastructures can be instrumental
Broadening the Path to the STEM Profession through Cybersecurity Learning
Cybersecurity Paths • General education – Discover • Intro to cybersecurity – Understand • Cybersecurity courses & capstone – Apply
Liberal Arts Education: Gen Ed Definition: a program of education (as in some liberal-arts colleges and secondary schools) intended to develop students as personalities rather than trained specialists and to transmit a common cultural heritage — compare liberal education.
General Education & Cybersecurity • Aesthetic and interpretive understanding; Hacker = Aesthete (Brian Harvey, UC Berkley), CITA @ Cof. C • Culture and belief • Empirical reasoning; Security Assessment, Pen Test • Ethical reasoning; Ethics vs Aesthetics • Science of living systems; • Science of the physical universe; • Societies of the world; and • The United States in the world. http: //harvardmagazine. com/2007/03/general-education-finall. html
Cybersecurity & Liberal Arts
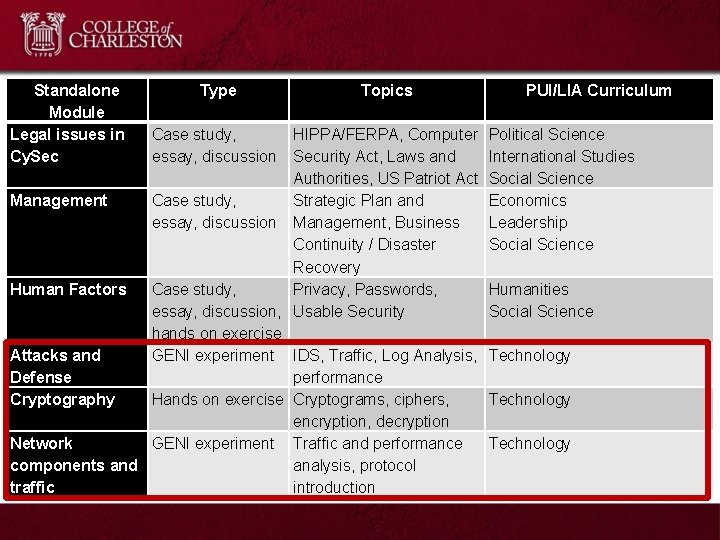
Standalone Module Legal issues in Cy. Sec Type Case study, essay, discussion Topics HIPPA/FERPA, Computer Security Act, Laws and Authorities, US Patriot Act Management Case study, Strategic Plan and essay, discussion Management, Business Continuity / Disaster Recovery Human Factors Case study, Privacy, Passwords, essay, discussion, Usable Security hands on exercise Attacks and GENI experiment IDS, Traffic, Log Analysis, Defense performance Cryptography Hands on exercise Cryptograms, ciphers, encryption, decryption Network GENI experiment Traffic and performance components and analysis, protocol traffic introduction PUI/LIA Curriculum Political Science International Studies Social Science Economics Leadership Social Science Humanities Social Science Technology
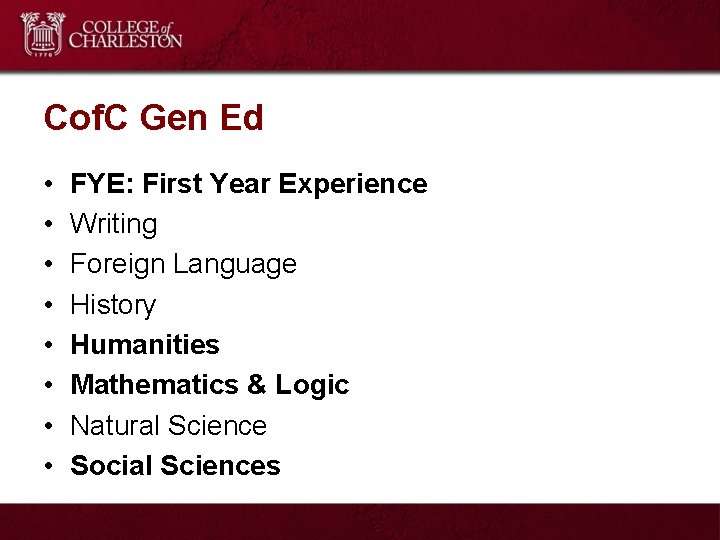
Cof. C Gen Ed • • FYE: First Year Experience Writing Foreign Language History Humanities Mathematics & Logic Natural Science Social Sciences
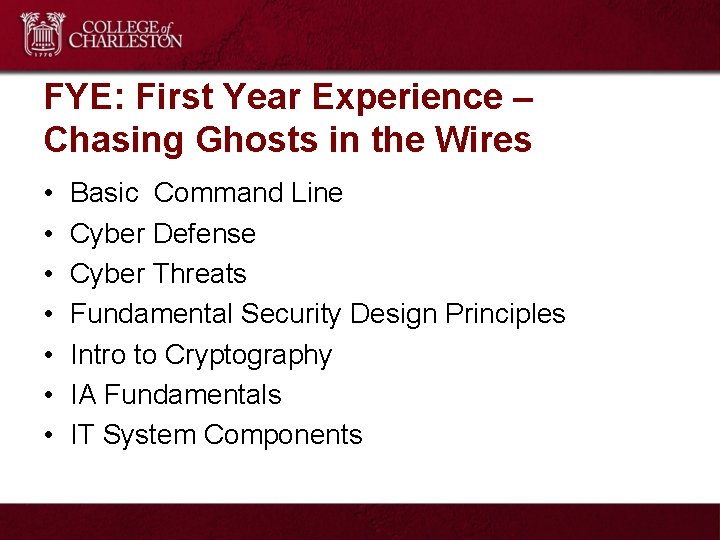
FYE: First Year Experience – Chasing Ghosts in the Wires • • Basic Command Line Cyber Defense Cyber Threats Fundamental Security Design Principles Intro to Cryptography IA Fundamentals IT System Components
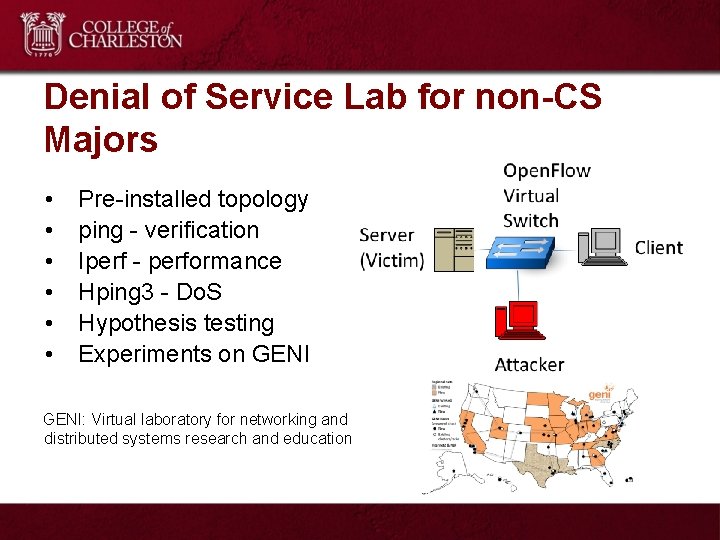
Denial of Service Lab for non-CS Majors • • • Pre-installed topology ping - verification Iperf - performance Hping 3 - Do. S Hypothesis testing Experiments on GENI: Virtual laboratory for networking and distributed systems research and education
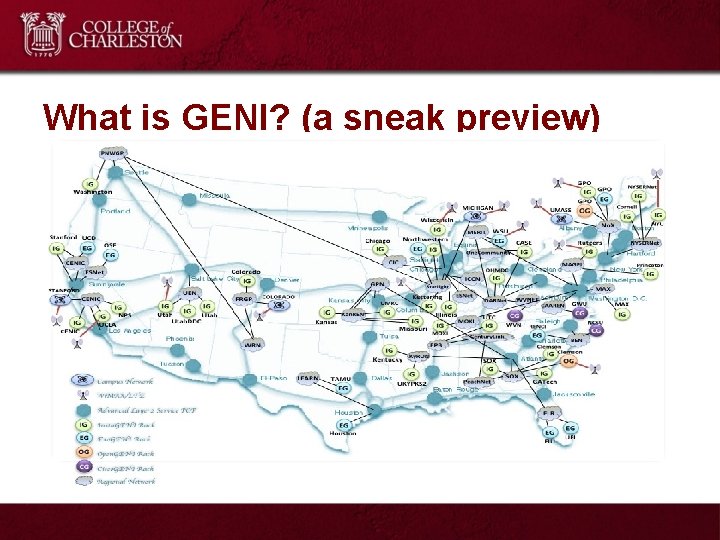
What is GENI? (a sneak preview)
GENI and Gen Ed • Wofford – Computational Science Gen Ed – 15 students – Mandatory for Lab requirement • College of Charleston – FYE – 20 students – Mandatory for first year students gen ed
Pilot Survey • Conducted at Wofford College. • Cohort: – 15 students – 2 computer science declared majors – Self-assessment of CS knowledge: 40% novice; 40% intermediate; 20% advanced • Pilot Questionnaire: 1. I have a better understanding of CS. 2. I understand how information is transmitted through the internet. 3. I understand the basics of computer attacks and computer network attacks. 4. I understand how computer and network attacks can harm me and my organization. 5. I am considering to take another CS course.
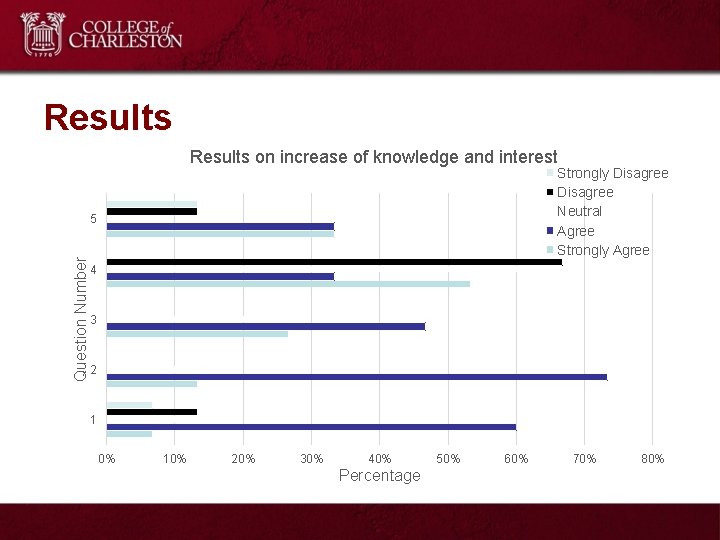
Results on increase of knowledge and interest Strongly Disagree Neutral Agree Strongly Agree Question Number 5 4 3 2 1 0% 10% 20% 30% 40% Percentage 50% 60% 70% 80%
Comments Q: What - did you like best about the GENI lab and why? I liked the opportunity to take part in a live experiment with real computers. Doing to the denial of service attack was really cool. I liked that we did a real world issue in a safe and controlled environment. Working with terminal and the command line It was cool to see how flooding a computer actually works rather than it just happens. I liked how we were able to simulate a real attack. This really puts it into prospective on how hackers can do this to anyone.
Comments Q: What did you like least about the GENI lab. • I did not like how repetitive it was, and how some things took a very long time to do. • I think that my least favorite thing about GENI was trying to get GENI to work. • The GENI infrastructure seemed to be unstable and difficult to work with at times. It's also hard to have a complete understanding of how to perform the lab without already having an understanding in computer science.
Preliminary results - FYE Lab • 20 students – 6 computer science declared majors • Pre & Post Survey – Demographic questions – Perception – Class • Focus Group – 4 students
Preliminary Results
Cybersecurity courses & GENI • Intrusion Detection Systems • Digital Certificate • Advanced topics
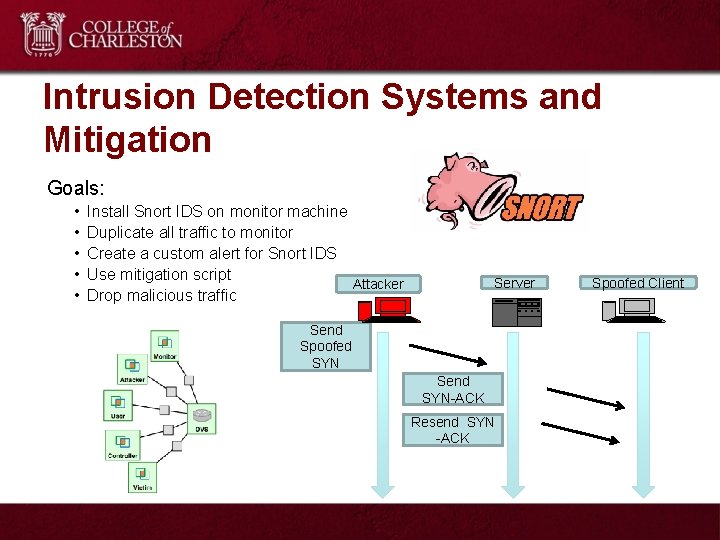
Intrusion Detection Systems and Mitigation Goals: • • • Install Snort IDS on monitor machine Duplicate all traffic to monitor Create a custom alert for Snort IDS Use mitigation script Attacker Drop malicious traffic Server Send Spoofed SYN Send SYN-ACK Resend SYN -ACK Spoofed Client
Digital Certificate • Create a certificate authority • Validate & revoke certificate • Understand Open. SSL
Advanced Topics • Covert Channel Communication – Manipulate TCP flags to send exfiltrated passwords – Analyze traffic using information theory • Software Defined Networking (SDN) solutions for security – Use SDN flow tables to identify attacker – Use network programmability to drop malicious traffic
Conclusions • With cybersecurity in liberal arts we produce better citizens in our graduates • Cybersecurity labs + cloud infrastructure = experiential learning with low overhead • Cybersecurity belongs to the liberal arts
Questions? THANK YOU!
Please take the survey to help us improve this workshop goo. gl/i 6787 a
APPENDIX
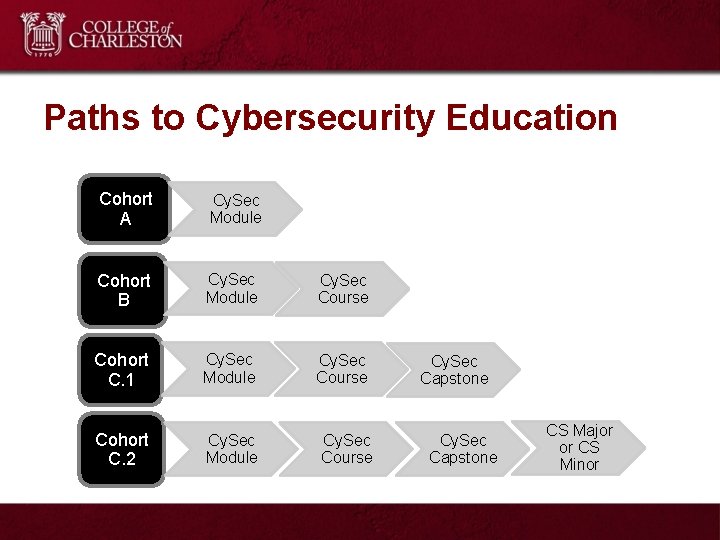
Paths to Cybersecurity Education Cohort A Cy. Sec Module Cohort B Cy. Sec Module Cy. Sec Course Cohort C. 1 Cy. Sec Module Cy. Sec Course Cohort C. 2 Cy. Sec Module Cy. Sec Course Cy. Sec Capstone CS Major or CS Minor
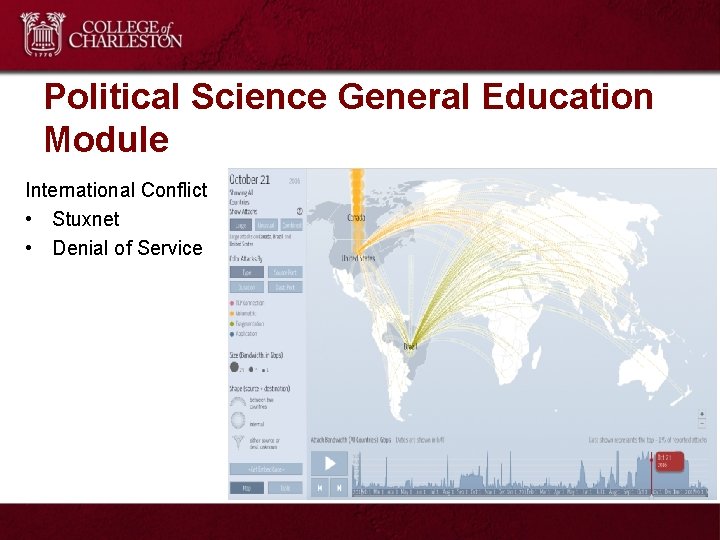
Political Science General Education Module International Conflict • Stuxnet • Denial of Service
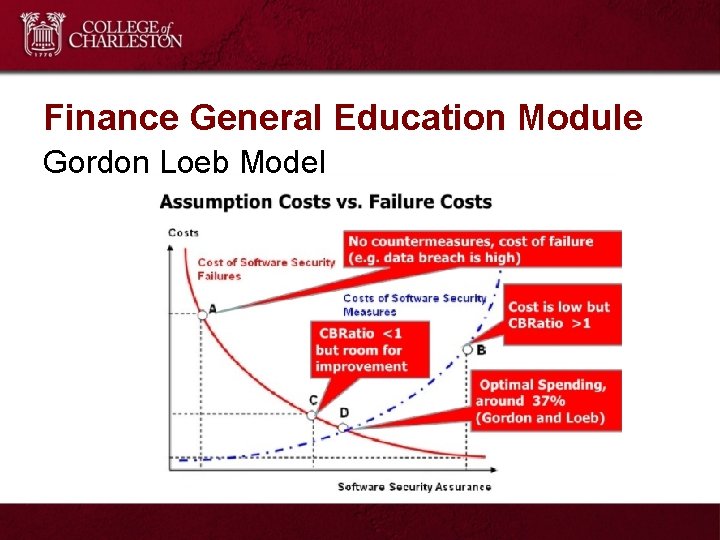
Finance General Education Module Gordon Loeb Model
- Slides: 32