CyberSecurity Internal Threats Rachael Bourgeois Ngan Do Abraham
Cyber-Security Internal Threats Rachael Bourgeois Ngan Do Abraham Aviles Fatima Clementino Cynthia Castillo
Introduction �Article Name: “Companies are Tracking Employees to Nab Traitors” by Dune Lawrence �What is our article about and how does it relate to our class? �What big event encouraged companies to invest in cyber security?
Implementation � Why is it important for companies to implement cyber-security software? � Protect customer list information, any product design, and sensitive information. � May help track outside hackers. � How do companies implement the software? � Software is placed on company’s computers and on company-issued laptops � It creates a private profile for each employee. � “Scout”=emails and other forms of communication.
How The Softwares Work - Fortscale and Securonix sell software that pulls data from a company’s computer systems - feeds it through algorithms to create a profile of each employee. - showing what’s normal behavior for that user - generates a risk score for users -it becomes much easier to spot suspicious activity
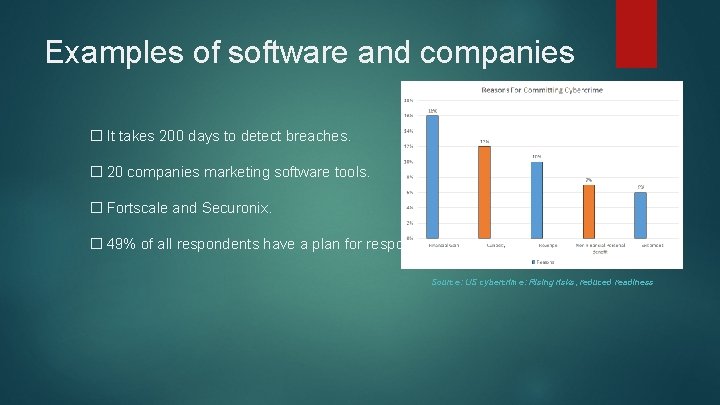
Examples of software and companies � It takes 200 days to detect breaches. � 20 companies marketing software tools. � Fortscale and Securonix. � 49% of all respondents have a plan for responding to insider threats. Source: US cybercrime: Rising risks, reduced readiness
Conclusion � To minimize internal threats: 1. We need to hire the right people for your team 2. People with good work ethic and commitment who are dependable and reliable. 3. Employees who knows how to manage stress, time, and maintain a professional workspace. 4. We need to watch out from employees who act suspicious such as downloading thousands of documents from a database she/he has permission to use but never has before. 5. Getting to know your employees and employers daily builds trust and confident in your workplace which can also eliminate internal theft.
Works Cited Lawrence, Dune. "Companies Are Tracking Employees to Nab Traitors. " Bloomberg Businessweek 12 Mar. 2015. http: //www. bloomberg. com/news/articles/2015 -03 -12/companies-aretracking-employees-to-nab-traitors Kelley, Michael B. “Former US Official: The NSA Thinks Edward Snowden Copied ‘Almost Everything That Place Does’. ” Business Insider. Web. 8 Apr. 2015. Key findings from the 2014 US State of Cybercrime Survey US Cybercrime: Rising risks, reduced readiness. www. pwc. com/cybersecurity
- Slides: 7