CYBERSECURITY IN MANUFACTURING Jim Barkley Khai Waterman James
CYBERSECURITY IN MANUFACTURING Jim Barkley, Khai Waterman James. Barkley@uilabs. org, Khai. Waterman@uilabs. org UNLIMITED DISTRIBUTION
AGENDA BACKGROUND Who We Are Industry Challenges Data in Manufacturing Io. T and IIo. T Threat Picture Types of Attacks Prevalence of Attacks Three Key Examples Solutions & Investment Areas Current Solutions Nine Key Initiatives for Industry Digital Manufacturing Commons & Security as a Service Questions

CYBERSECURITY IN MANUFACTURING Atoms are the new bits. - Neil Gershenfeld
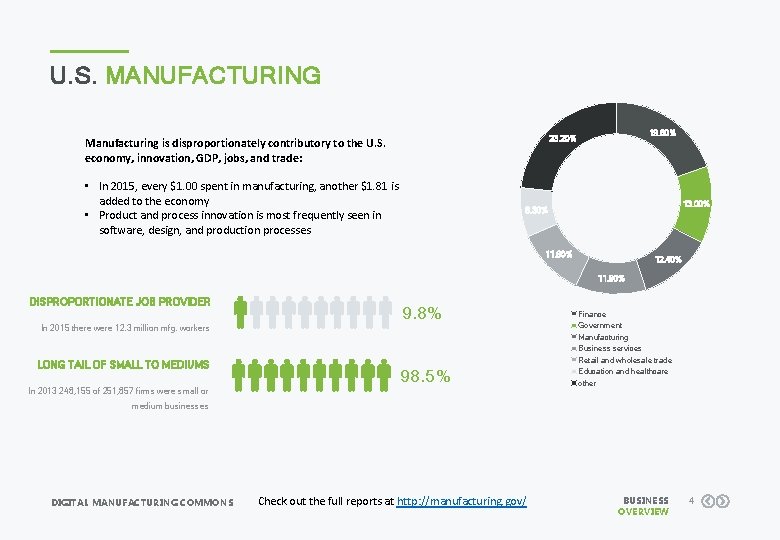
U. S. MANUFACTURING 19. 60% 23. 20% Manufacturing is disproportionately contributory to the U. S. economy, innovation, GDP, jobs, and trade: • In 2015, every $1. 00 spent in manufacturing, another $1. 81 is added to the economy • Product and process innovation is most frequently seen in software, design, and production processes 13. 00% 8. 30% 11. 60% 12. 40% 11. 90% DISPROPORTIONATE JOB PROVIDER 9. 8% In 2015 there were 12. 3 million mfg. workers LONG TAIL OF SMALL TO MEDIUMS 98. 5% In 2013 248, 155 of 251, 857 firms were small or Finance Government Manufacturing Business services Retail and wholesale trade Education and healthcare other medium businesses DIGITAL MANUFACTURING COMMONS Check out the full reports at http: //manufacturing. gov/ BUSINESS OVERVIEW 4

WHO WE ARE? UI LABS is a Chicago-based 501(c)3 non-profit corporation that focuses on leveraging collective investments in innovation to deliver better solutions, more quickly and more efficiently. Our partnerships transform industries. UI LABS Operates the Digital Manufacturing and Design Innovation Institute (DMDII), one of the premiere national manufacturing institutes launched under the Obama Administration. • Established with a $70 M cooperative agreement with the US Department of Defense, +$12 M additional grants • Addresses underinvestment in “pre-competitive” applied R&D that can advance the entire industrial base • Designs “corporate interest projects” to develop proprietary go-to-market solutions WE ARE COMMITTED TO DIGITIZING AMERICAN MANUFACTURING! Placeholder image • Current pipeline of 50+ projects DIGITAL MANUFACTURING COMMONS BUSINESS OVERVIEW 5
DIGITAL MANUFACTURING COMMONS BUSINESS OVERVIEW 6
DIGITAL MANUFACTURING COMMONS BUSINESS OVERVIEW 7
DIGITAL MANUFACTURING COMMONS BUSINESS OVERVIEW 8
DIGITAL MANUFACTURING COMMONS BUSINESS OVERVIEW 9
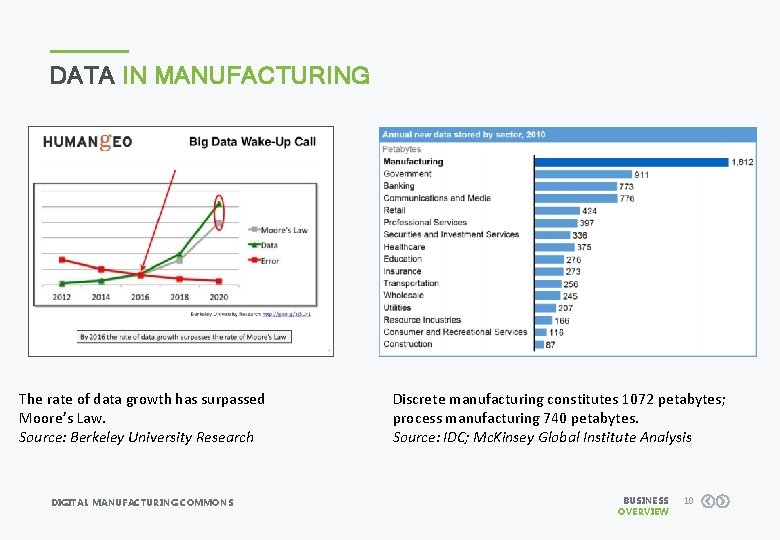
DATA IN MANUFACTURING The rate of data growth has surpassed Moore’s Law. Source: Berkeley University Research DIGITAL MANUFACTURING COMMONS Discrete manufacturing constitutes 1072 petabytes; process manufacturing 740 petabytes. Source: IDC; Mc. Kinsey Global Institute Analysis BUSINESS OVERVIEW 10
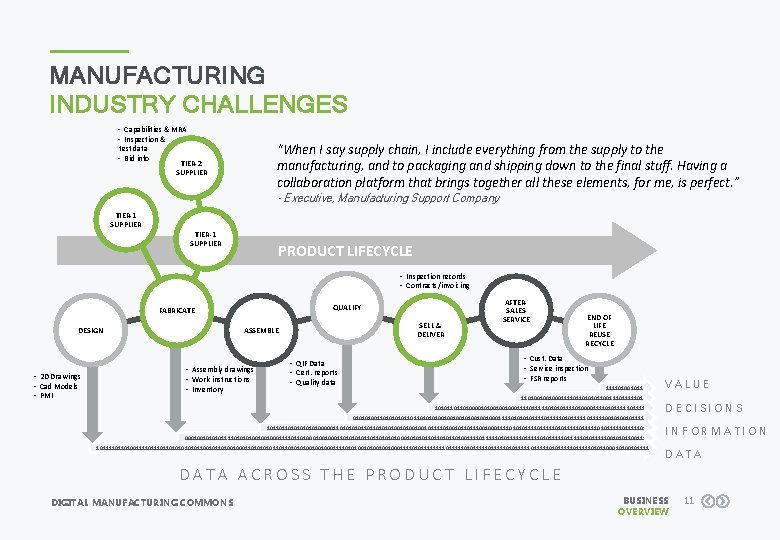
MANUFACTURING INDUSTRY CHALLENGES • Capabilities & MRA • Inspection & “When I say supply chain, I include everything from the supply to the manufacturing, and to packaging and shipping down to the final stuff. Having a collaboration platform that brings together all these elements, for me, is perfect. ” test data • Bid info TIER-2 SUPPLIER - Executive, Manufacturing Support Company TIER-1 SUPPLIER PRODUCT LIFECYCLE • Inspection records • Contracts/invoicing QUALIFY FABRICATE ASSEMBLE DESIGN • 2 D Drawings • Cad Models • PMI SELL & DELIVER • Assembly drawings • Work instructions • Inventory • QIF Data • Cert. reports • Quality data AFTERSALES SERVICE END OF LIFE REUSE RECYCLE • Cust. Data • Service inspection • FSR reports 111101001011 110100100100011110110101011001111101 1010110110100001010010010001111101010111101000011110101111 01010100110101101101001001001000111101011110101111100101111 10110110101000001101011011010010100100101111010010110111001000111101010111110101111101111101 00010010111101001001000111101101001000110101101101000101101101001111101011111011111010111110010101100111 1011110110100111101101010110010110100100011010110110100100100011110101001001000111101011110111110101111101111101111101011000101111 VALUE DECISIONS INFORMATION DATA ACROSS THE PRODUCT LIFECYCLE DIGITAL MANUFACTURING COMMONS BUSINESS OVERVIEW 11
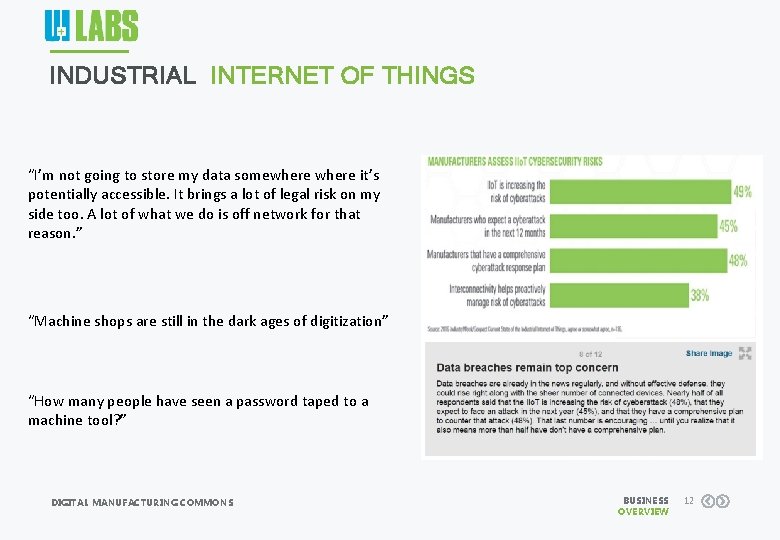
INDUSTRIAL INTERNET OF THINGS “I’m not going to store my data somewhere it’s potentially accessible. It brings a lot of legal risk on my side too. A lot of what we do is off network for that reason. ” “Machine shops are still in the dark ages of digitization” “How many people have seen a password taped to a machine tool? ” DIGITAL MANUFACTURING COMMONS BUSINESS OVERVIEW 12
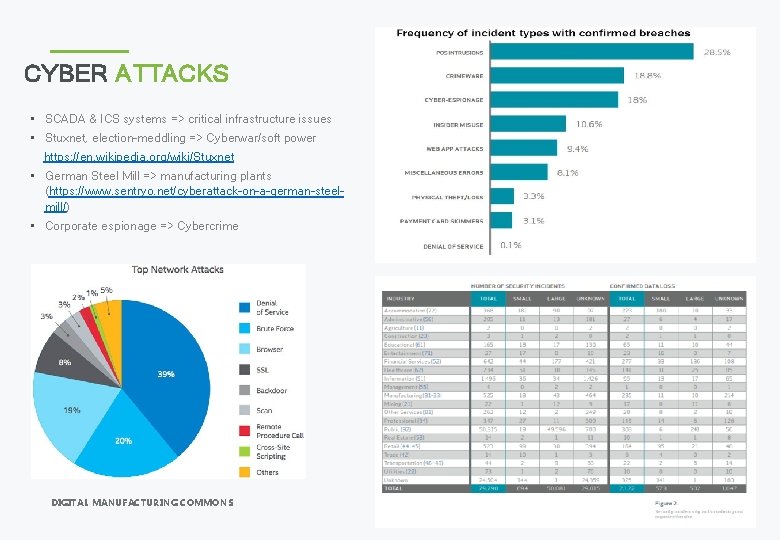
CYBER ATTACKS • SCADA & ICS systems => critical infrastructure issues • Stuxnet, election-meddling => Cyberwar/soft power https: //en. wikipedia. org/wiki/Stuxnet • German Steel Mill => manufacturing plants (https: //www. sentryo. net/cyberattack-on-a-german-steelmill/) • Corporate espionage => Cybercrime DIGITAL MANUFACTURING COMMONS BUSINESS OVERVIEW 14
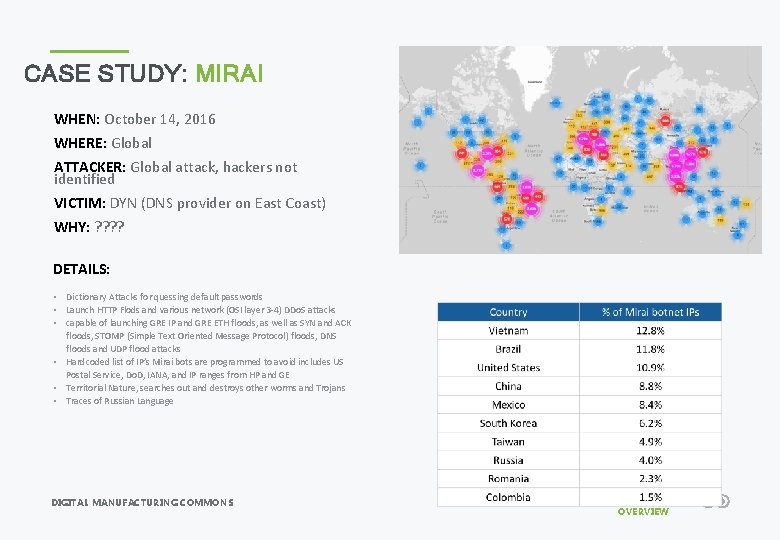
CASE STUDY: MIRAI WHEN: October 14, 2016 WHERE: Global ATTACKER: Global attack, hackers not identified VICTIM: DYN (DNS provider on East Coast) WHY: ? ? DETAILS: • Dictionary Attacks for quessing default passwords • Launch HTTP Flods and various network (OSI layer 3 -4) DDo. S attacks • capable of launching GRE IP and GRE ETH floods, as well as SYN and ACK floods, STOMP (Simple Text Oriented Message Protocol) floods, DNS floods and UDP flood attacks • Hardcoded list of IP’s Mirai bots are programmed to avoid includes US Postal Service, Do. D, IANA, and IP ranges from HP and GE • Territorial Nature, searches out and destroys other worms and Trojans • Traces of Russian Language DIGITAL MANUFACTURING COMMONS BUSINESS OVERVIEW 15
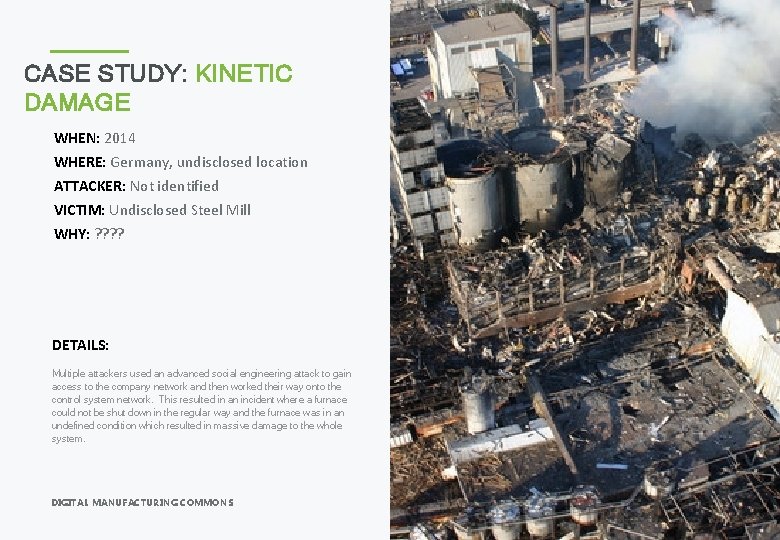
CASE STUDY: KINETIC DAMAGE WHEN: 2014 WHERE: Germany, undisclosed location ATTACKER: Not identified VICTIM: Undisclosed Steel Mill WHY: ? ? DETAILS: Multiple attackers used an advanced social engineering attack to gain access to the company network and then worked their way onto the control system network. This resulted in an incident where a furnace could not be shut down in the regular way and the furnace was in an undefined condition which resulted in massive damage to the whole system. DIGITAL MANUFACTURING COMMONS BUSINESS OVERVIEW 16

CURRENT SOLUTIONS Until recently, solutions have been focused on securing the perimeter. In a globally-connected planet, there ain’t no perimeter! Currently Available Resources • NIST Guide to Industrial Control Systems (https: //www. nist. gov/sites/default/files/documents/cyberfra mework/cybersecurity-framework-021214. pdf http: //nvlpubs. nist. gov/nistpubs/Special. Publications/NIST. SP. 800 -82. pdf) • DHS Guide (https: //www. dhs. gov/science-andtechnology/iot-world-2016) • Industrial Security Incidents Database (RISI, http: //www. risidata. com/) WE ARE COMMITTED TO DIGITIZING AMERICAN MANUFACTURING! Placeholder image DIGITAL MANUFACTURING COMMONS BUSINESS OVERVIEW 18
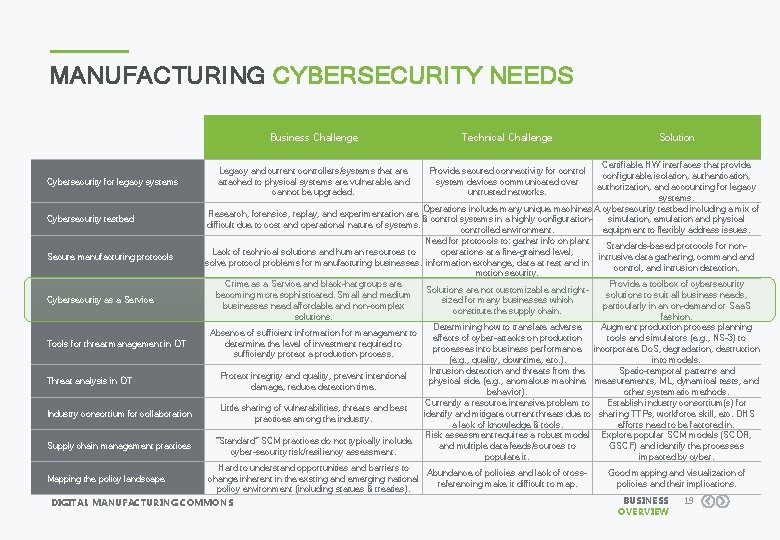
MANUFACTURING CYBERSECURITY NEEDS Business Challenge Technical Challenge Solution Certifiable HW interfaces that provide configurable isolation, authentication, Cybersecurity for legacy systems authorization, and accounting for legacy systems. Operations include many unique machines A cybersecurity testbed including a mix of Research, forensics, replay, and experimentation are Cybersecurity testbed & control systems in a highly configurationsimulation, emulation and physical difficult due to cost and operational nature of systems. controlled environment. equipment to flexibly address issues. Need for protocols to: gather info on plant Standards-based protocols for non. Lack of technical solutions and human resources to operations at a fine-grained level, Secure manufacturing protocols intrusive data gathering, command solve protocol problems for manufacturing businesses. information exchange, data at rest and in control, and intrusion detection. motion security. Crime as a Service and black-hat groups are Provide a toolbox of cybersecurity Solutions are not customizable and rightbecoming more sophisticated. Small and medium solutions to suit all business needs, Cybersecurity as a Service sized for many businesses which businesses need affordable and non-complex particularly in an on-demand or Saa. S constitute the supply chain. solutions. fashion. Determining how to translate adverse Augment production process planning Absence of sufficient information for management to effects of cyber-attacks on production tools and simulators (e. g. , NS-3) to Tools for threat management in OT determine the level of investment required to processes into business performance incorporate Do. S, degradation, destruction sufficiently protect a production process. (e. g. , quality, downtime, etc. ). into models. Intrusion detection and threats from the Spatio-temporal patterns and Protect integrity and quality, prevent intentional Threat analysis in OT physical side (e. g. , anomalous machine measurements, ML, dynamical tests, and damage, reduce detection time. behavior). other systematic methods. Currently a resource intensive problem to Establish industry consortium(s) for Little sharing of vulnerabilities, threats and best Industry consortium for collaboration identify and mitigate current threats due to sharing TTPs, workforce skill, etc. DHS practices among the industry. a lack of knowledge & tools. efforts need to be factored in. Risk assessment requires a robust model Explore popular SCM models (SCOR, “Standard” SCM practices do not typically include Supply chain management practices and multiple data feeds/sources to GSCF) and identify the processes cyber-security risk/resiliency assessment. populate it. impacted by cyber. Hard to understand opportunities and barriers to Abundance of policies and lack of cross. Good mapping and visualization of Mapping the policy landscape change inherent in the exsting and emerging national referencing make it difficult to map. policies and their implications. policy environment (including statues & treaties). BUSINESS 19 DIGITAL MANUFACTURING COMMONS OVERVIEW Legacy and current controllers/systems that are attached to physical systems are vulnerable and cannot be upgraded. Provide secured connectivity for control system devices communicated over untrusted networks.
THE COMMONS The DMC is a leading open-source platform for connecting communities and sharing solutions across the manufacturing product life cycle. Expose tools, data and compute in a searchable automation platform Advertise company capabilities Manage storefront offerings
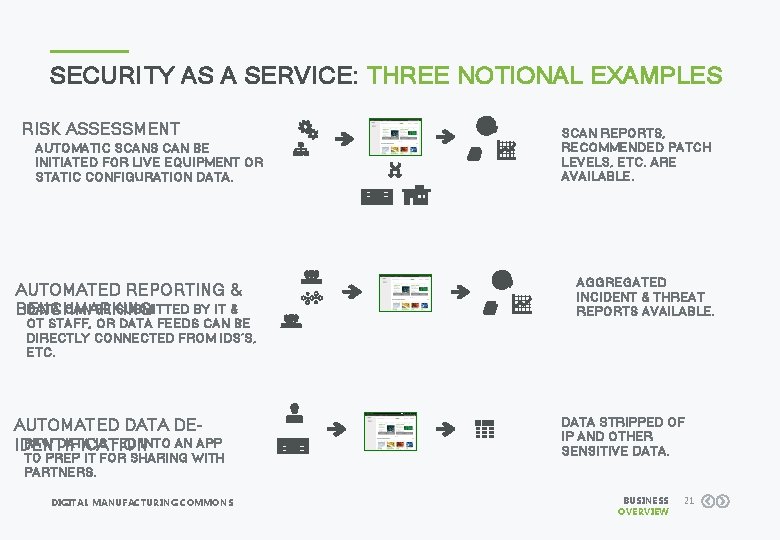
SECURITY AS A SERVICE: THREE NOTIONAL EXAMPLES RISK ASSESSMENT AUTOMATIC SCANS CAN BE INITIATED FOR LIVE EQUIPMENT OR STATIC CONFIGURATION DATA. AUTOMATED REPORTING & DATA CAN BE SUBMITTED BY IT & BENCHMARKING OT STAFF, OR DATA FEEDS CAN BE DIRECTLY CONNECTED FROM IDS’S, ETC. AUTOMATED DATA DERAW DATA IS FED INTO AN APP IDENTIFICATION TO PREP IT FOR SHARING WITH PARTNERS. DIGITAL MANUFACTURING COMMONS SCAN REPORTS, RECOMMENDED PATCH LEVELS, ETC. ARE AVAILABLE. AGGREGATED INCIDENT & THREAT REPORTS AVAILABLE. DATA STRIPPED OF IP AND OTHER SENSITIVE DATA. BUSINESS OVERVIEW 21
QUESTIONS? FIND OUT MORE: HTTP: //OPENDMC. ORG/ ASKDMC@UILABS. ORG DIGITAL MANUFACTURING COMMONS BUSINESS OVERVIEW 22
- Slides: 20