Cybersecurity Global Standards National International Cybersecurity Strategy David

Cybersecurity & Global Standards National & International Cybersecurity Strategy David R Kaiser Product Security Office 3 March 2021
TOPICS 1. Datasphere Expansion & Digital Disruption 2. Cybersecurity & Global Standards for Product Security Assurance 3. Validating the Integrity of Computing Devices 4. Provenance & Benefit of Blockchain in the Datasphere 5. Role of Corporate Governance 6. Trust in the Datasphere 2
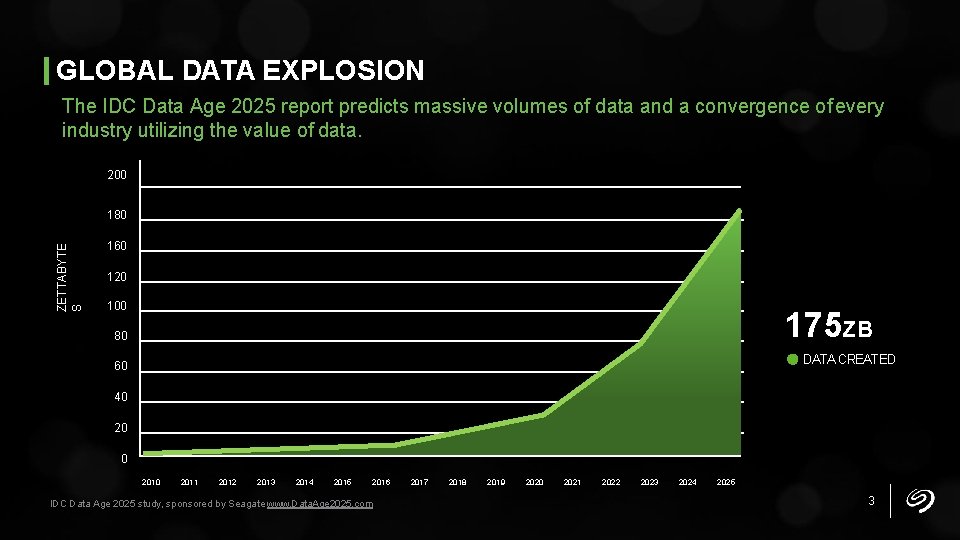
GLOBAL DATA EXPLOSION The IDC Data Age 2025 report predicts massive volumes of data and a convergence of every industry utilizing the value of data. 200 ZETTABYTE S 180 160 120 100 175 ZB 80 DATA CREATED 60 40 2011 2012 2013 2014 2015 2016 IDC Data Age 2025 study, sponsored by Seagate www. Data. Age 2025. com 2017 2018 2019 2020 2021 2022 2023 2024 2025 3
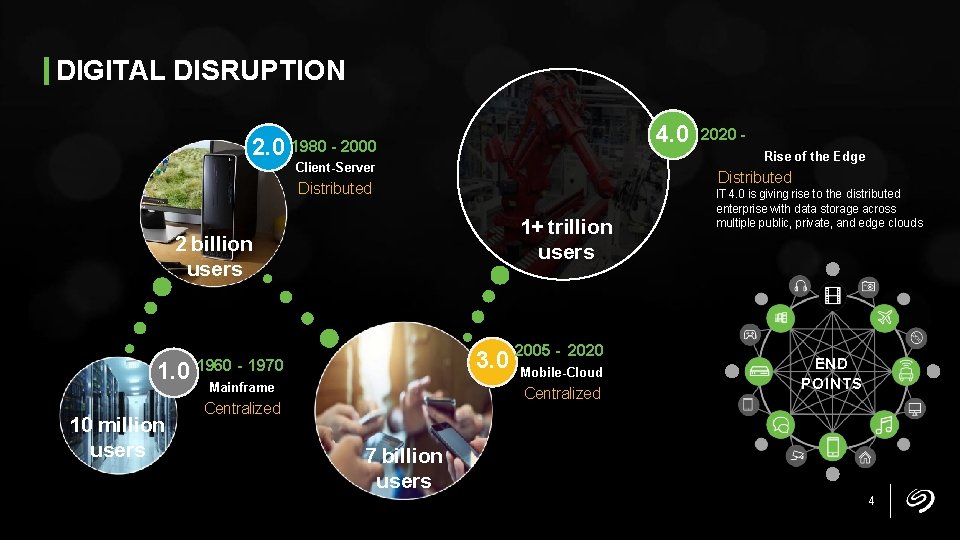
DIGITAL DISRUPTION 4. 0 2. 0 1980 - 2000 Rise of the Edge Client-Server Distributed 1+ trillion users 2 billion users 1. 0 10 million users - 2020 3. 0 2005 Mobile-Cloud 1960 - 1970 Mainframe Centralized 2020 - IT 4. 0 is giving rise to the distributed enterprise with data storage across multiple public, private, and edge clouds END POINTS 7 billion users 4
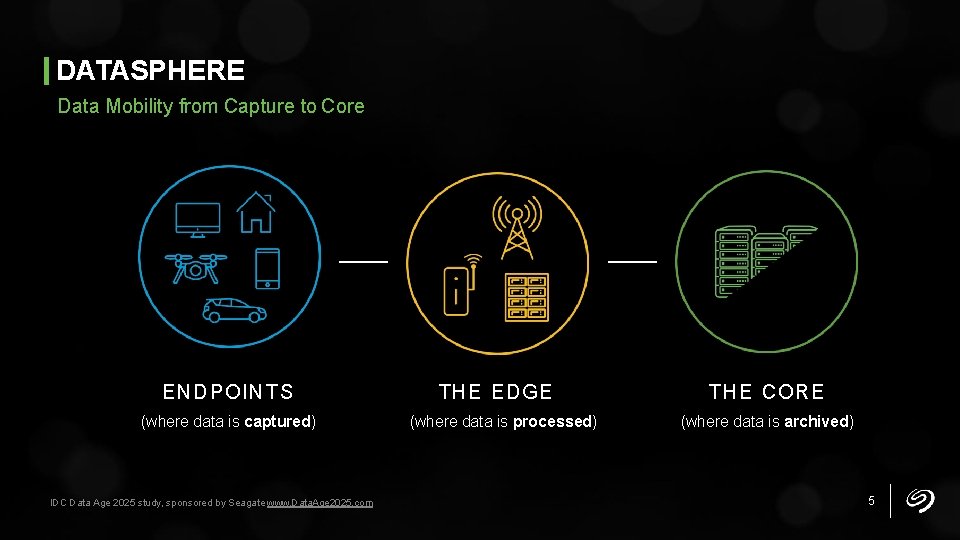
DATASPHERE Data Mobility from Capture to Core ENDPOINTS (where data is captured) IDC Data Age 2025 study, sponsored by Seagate www. Data. Age 2025. com THE EDGE (where data is processed) THE CORE (where data is archived) 5
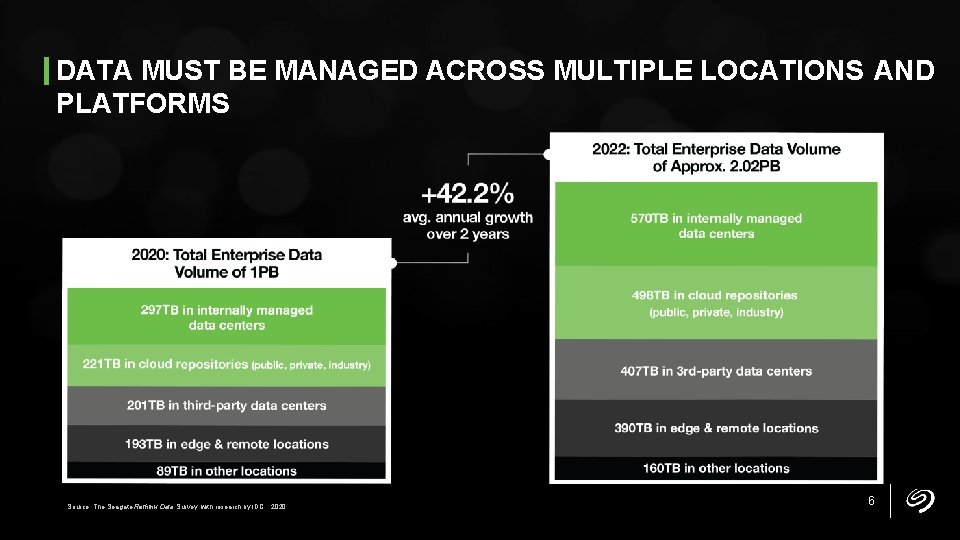
DATA MUST BE MANAGED ACROSS MULTIPLE LOCATIONS AND PLATFORMS Source: The Seagate Rethink Data Survey, with research by IDC, 2020. 6
DATA AGE 2025 REPORT Cognitive/AI Systems Change the Landscape Cognitive systems will become proactive drivers of action. New technologies make data analysis more frequent, flexible, and important to our lives. Current uses of cognitive systems include facial recognition, driverless cars, and virtual customer service. IDC Data Age 2025 study, sponsored by Seagate www. Data. Age 2025. com 7
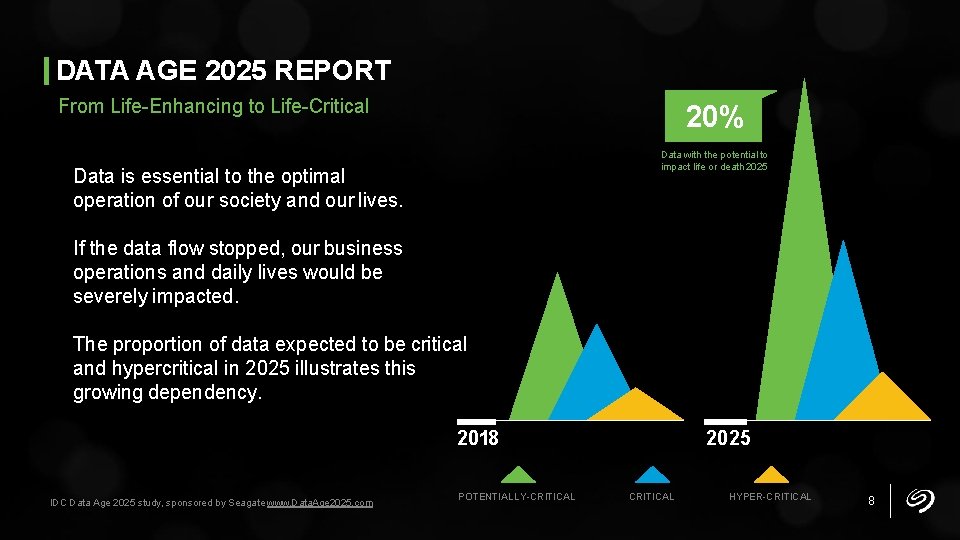
DATA AGE 2025 REPORT From Life-Enhancing to Life-Critical 20% Data with the potential to impact life or death 2025 Data is essential to the optimal operation of our society and our lives. If the data flow stopped, our business operations and daily lives would be severely impacted. The proportion of data expected to be critical and hypercritical in 2025 illustrates this growing dependency. 2018 IDC Data Age 2025 study, sponsored by Seagate www. Data. Age 2025. com POTENTIALLY-CRITICAL 2025 CRITICAL HYPER-CRITICAL 8
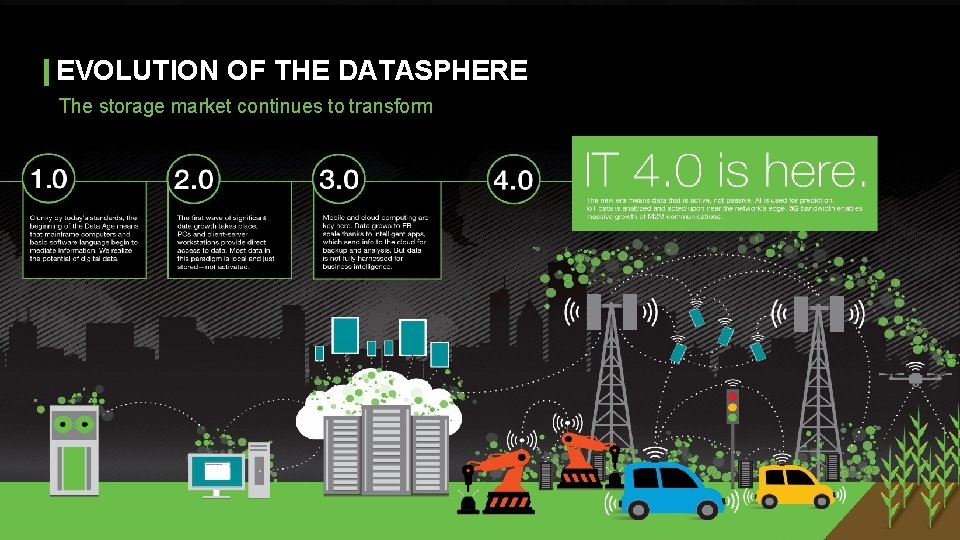
EVOLUTION OF THE DATASPHERE The storage market continues to transform 9

Supply Chain Product Security Establishing Product Trust in the Datasphere 10
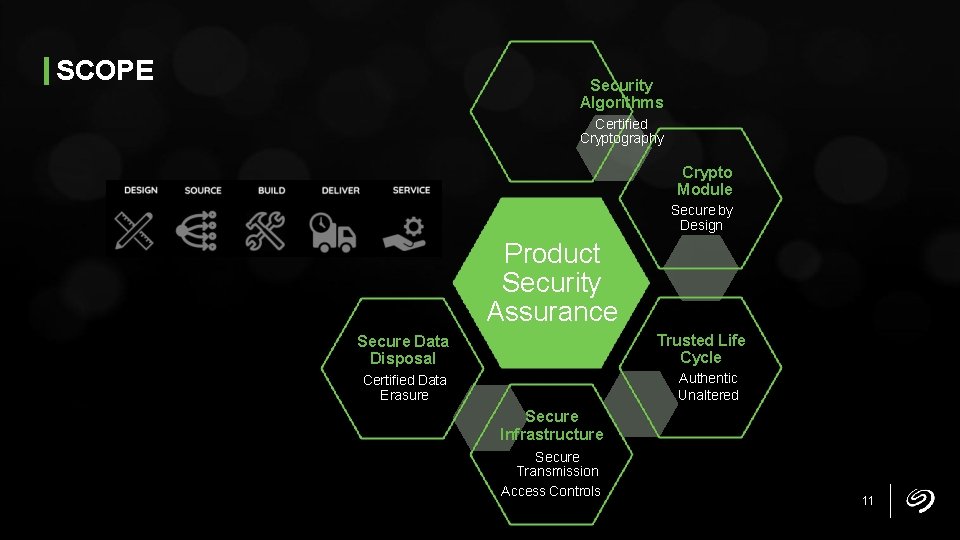
SCOPE Security Algorithms Certified Cryptography Crypto Module Secure by Design Product Security Assurance Trusted Life Cycle Secure Data Disposal Authentic Unaltered Certified Data Erasure Secure Infrastructure Secure Transmission Access Controls 11
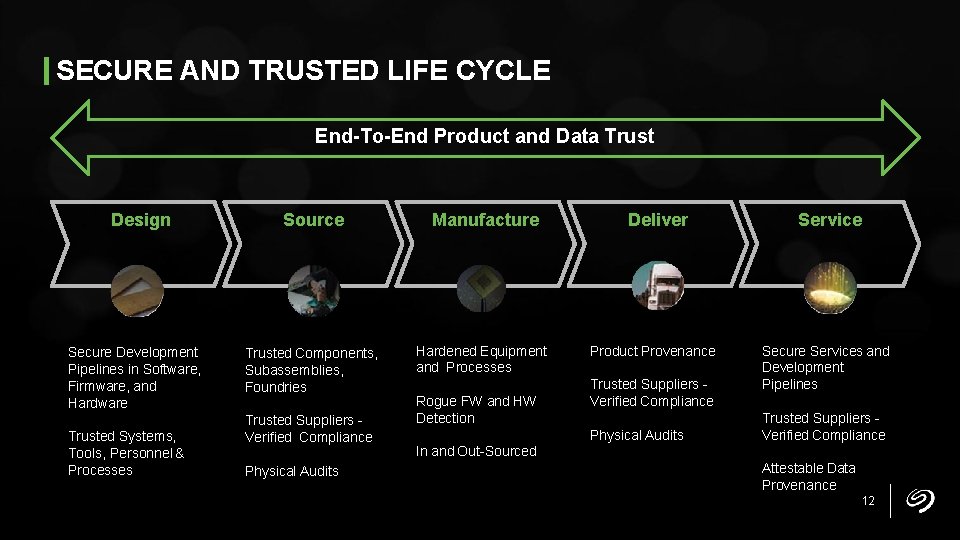
SECURE AND TRUSTED LIFE CYCLE End-To-End Product and Data Trust Design Secure Development Pipelines in Software, Firmware, and Hardware Trusted Systems, Tools, Personnel & Processes Source Manufacture Trusted Components, Subassemblies, Foundries Hardened Equipment and Processes Trusted Suppliers Verified Compliance Physical Audits Rogue FW and HW Detection Deliver Product Provenance Trusted Suppliers Verified Compliance Physical Audits Service Secure Services and Development Pipelines Trusted Suppliers Verified Compliance In and Out-Sourced Attestable Data Provenance 12
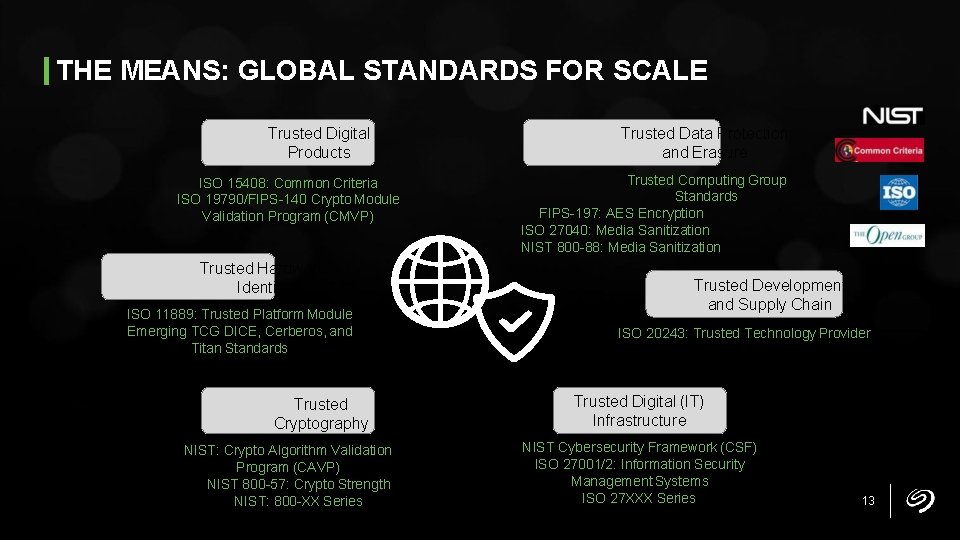
THE MEANS: GLOBAL STANDARDS FOR SCALE Trusted Digital Products ISO 15408: Common Criteria ISO 19790/FIPS-140 Crypto Module Validation Program (CMVP) Trusted Hardware Identity ISO 11889: Trusted Platform Module Emerging TCG DICE, Cerberos, and Titan Standards Trusted Cryptography NIST: Crypto Algorithm Validation Program (CAVP) NIST 800 -57: Crypto Strength NIST: 800 -XX Series Trusted Data Protection and Erasure Trusted Computing Group Standards FIPS-197: AES Encryption ISO 27040: Media Sanitization NIST 800 -88: Media Sanitization Trusted Development and Supply Chain ISO 20243: Trusted Technology Provider Trusted Digital (IT) Infrastructure NIST Cybersecurity Framework (CSF) ISO 27001/2: Information Security Management Systems ISO 27 XXX Series 13
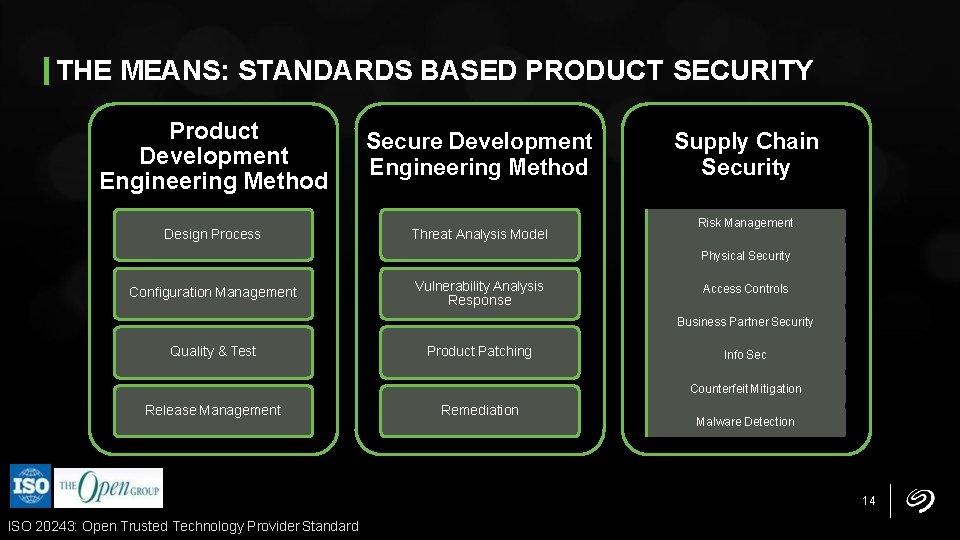
THE MEANS: STANDARDS BASED PRODUCT SECURITY Product Development Engineering Method Secure Development Engineering Method Design Process Threat Analysis Model Supply Chain Security Risk Management Physical Security Configuration Management Vulnerability Analysis Response Access Controls Business Partner Security Quality & Test Product Patching Info Sec Counterfeit Mitigation Release Management Remediation Malware Detection 14 ISO 20243: Open Trusted Technology Provider Standard
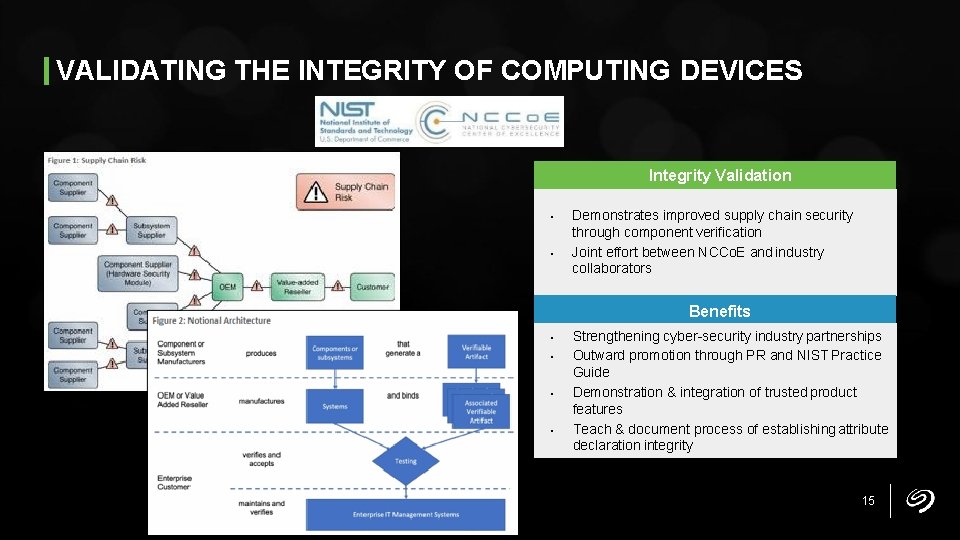
VALIDATING THE INTEGRITY OF COMPUTING DEVICES Integrity Validation • • Demonstrates improved supply chain security through component verification Joint effort between NCCo. E and industry collaborators Benefits • • Strengthening cyber-security industry partnerships Outward promotion through PR and NIST Practice Guide Demonstration & integration of trusted product features Teach & document process of establishing attribute declaration integrity 15
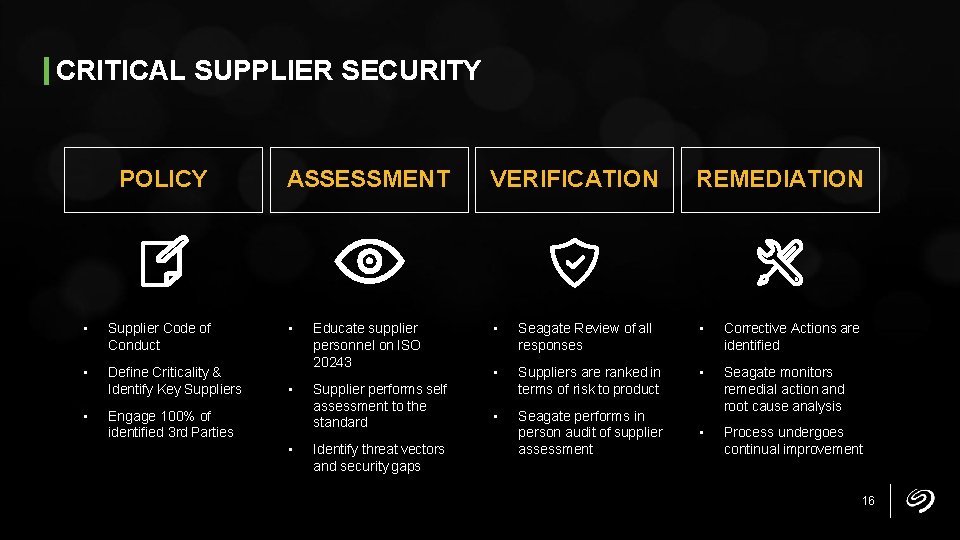
CRITICAL SUPPLIER SECURITY POLICY • Supplier Code of Conduct • Define Criticality & Identify Key Suppliers • ASSESSMENT • • Engage 100% of identified 3 rd Parties • Educate supplier personnel on ISO 20243 Supplier performs self assessment to the standard Identify threat vectors and security gaps VERIFICATION REMEDIATION • Seagate Review of all responses • Corrective Actions are identified • Suppliers are ranked in terms of risk to product • • Seagate performs in person audit of supplier assessment Seagate monitors remedial action and root cause analysis • Process undergoes continual improvement 16
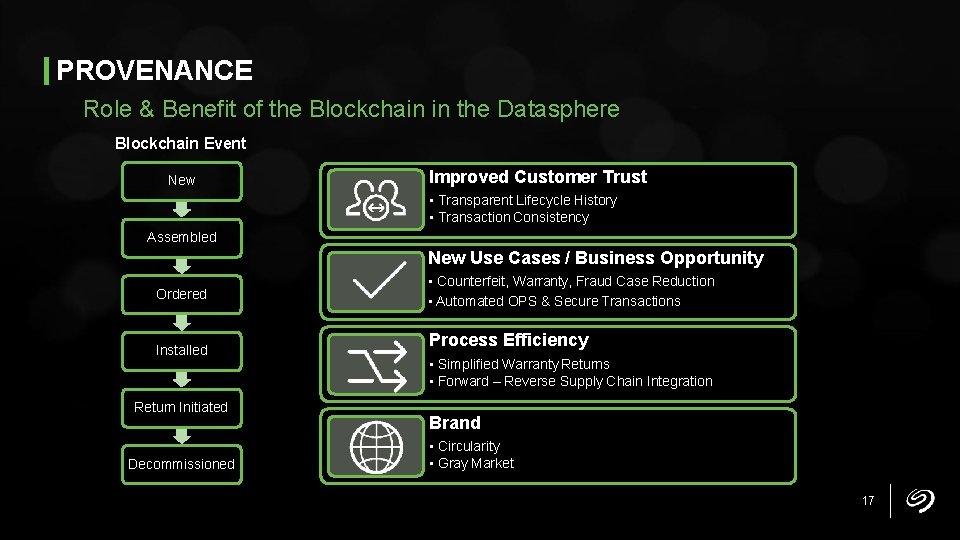
PROVENANCE Role & Benefit of the Blockchain in the Datasphere Blockchain Event New Improved Customer Trust • Transparent Lifecycle History • Transaction Consistency Assembled New Use Cases / Business Opportunity Ordered Installed Return Initiated Decommissioned • Counterfeit, Warranty, Fraud Case Reduction • Automated OPS & Secure Transactions Process Efficiency • Simplified Warranty Returns • Forward – Reverse Supply Chain Integration Brand • Circularity • Gray Market 17
GOVERNANCE SECURITY ASSURANCE INTEGRATION ACROSS THE ENTERPRISE CYBER PRODUCT PHYSICAL DATA PRIVACY / PROTECTION 18
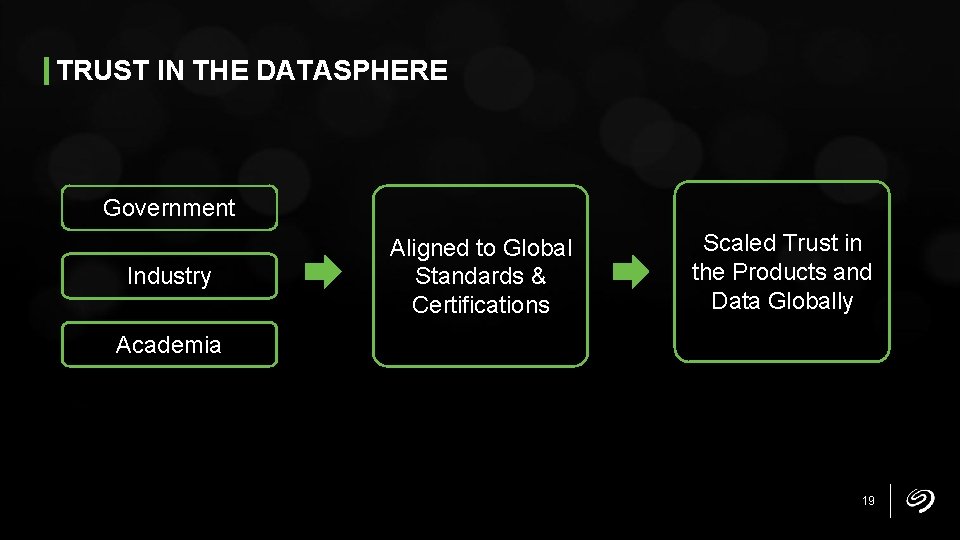
TRUST IN THE DATASPHERE Government Industry Aligned to Global Standards & Certifications Scaled Trust in the Products and Data Globally Academia 19

Thank You 20
- Slides: 20