Cybersecurity for UAS Systems SystemAware Cybersecurity Barry Horowitz
Cybersecurity for UAS Systems System-Aware Cybersecurity Barry Horowitz University of Virginia November 2015
Three Aspects to Cybersec for UAS’s • Securing the manufacturing of the system • Securing the final product in the context of the integrated air/ground system
A Systems Engineering View • Because cybersec for UAS’s: – Impacts safety (Policy) – Requires operational doctrine to effectively respond to attacks (Process) – Requires solutions that span a broad array of risks (Technology) • System-oriented research efforts are needed to develop solutions that account for the mix of: – Technology opportunities and limitations – Policy objectives – Process Issues (including human factors)
Traditional Cybersecurity for Internet-based Information Systems • Standard cybersecurity approaches are infrastructural in nature: Network protections/System perimeter protections • Little emphasis on protecting applications within specific information systems • As a result, the cybersecurity community does not have needed experience in securing applications, and in particular physical system control functions • And physical system designers do not have needed experience with designing for better cybersecurity
UVa’s System-Aware Cybersecurity for Computer-Controlled Physical Systems (1 of 2) • Added layer of security, in addition to network and perimeter security, to protect physical system control functions • Monitoring the highest risk system functions for illogical behavior and, upon detection, reconfiguring for continuous operation • Build on cybersecurity, fault tolerant and automatic control technologies • System monitoring/reconfiguring accomplished with support from a highly secured Sentinel – employ many more security features for protecting the Sentinel than the system being protected can practically employ
UVa’s System-Aware Cybersecurity for Computer-Controlled Physical Systems (2 of 2) • Addresses not only externally generated attacks, but also insider and supply chain attacks • Employs reusable design patterns to enable more economical solution development • Includes doctrine for operator response to detected attacks • Includes integrated methodology and tools developed to support assessment of both the consequences of attacks and the impact of potential defenses on the cyber attacker’s potential selection of attacks – Use Sys. Ml for sufficiently detailed description of system to be protected – Use Attack Trees to support a two-sided assessment methodology
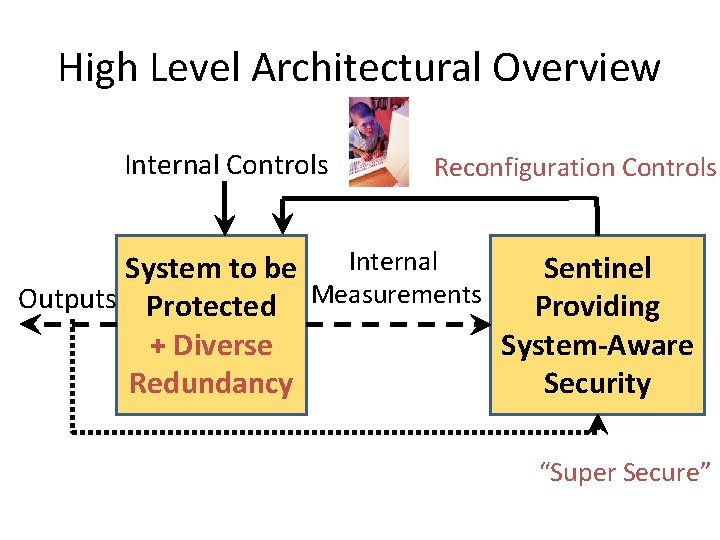
High Level Architectural Overview Internal Controls Reconfiguration Controls Internal System to be Sentinel Outputs Protected Measurements Providing + Diverse System-Aware Redundancy Security “Super Secure”
Sample of Reusable Design Patterns Being Prototyped • Diverse Redundancy for post-attack restoration • Diverse Redundancy + Verifiable Voting for trans-attack deflection • Physical Configuration Hopping for moving target defense • Data Consistency Checking for data integrity and operator display protection • Parameter Assurance for parameter controlled SW functions • Conditional Disablement of automation features • Doctrinal Assurance Checking for critical decisions
UAV Prototype • Live flight tests in December 2014 at Early County Airport in Blakely Georgia • Multiple attacks/detections/responses – – Waypoint changes Camera pointing control GPS navigation errors Meta data to support video interpretation • Secure Sentinel, including: – Triple diverse redundancy – Computer HW/Operating Systems/ Monitoring SW for monitoring – Configuration hopping – Monitoring both the airborne and ground-based subsystems for continuity • Accomplished within power, cooling and physical footprint of an Outlaw UAV carrying video cameras and small phased array radar (currently implemented within a 3”cube
UAV Video
Continuing to Learn through Multiple Prototype Projects • Do. D – – – UAV/Surveillance system, including in-flight evaluation Creech AF Base human factors exercise Currently employed AF/Army AIMES video exploitation system Radar system (In early design phase) Initiating Army tank project related to advanced fire control system Laboratory-based multi-sensor collection system • 3 d Printers – NIST • Automobile cybersecurity – DARPA Urban Challenge autonomous vehicle – Virginia State Police project
Important Factors Regarding Securing Physical Systems • Monitoring for and responding to attacks that have gained control of physical systems is a more contained objective than for information systems – – – • But More limited access to physical controls Fewer system functions Less distributed Bounded by laws of physics Less SW – Successful attacks can do physical harm – Reconfiguration requires operational procedures for rapid response – Solutions requires operators who are trained and ready to react to very infrequent and unprecedented (zero day) cyber attack events – Physical system operators have no experience or expectations regarding physical system attacks, and – When selecting attacks to defend agains, need to be careful when building on historic safety related analyses - multiple concurrent failures, considered as independent and acceptably rare from a safety viewpoint, can be purposefully accomplished as part of a cyber attack (e. g. , Stuxnet)
Scope of System-Aware Research Activities • Human Factors – Working with AF Human Factors community at Wright Pat exploring “suspicion” as a measurable human characteristic, and how it relates to behavior in cyber attack situations and response to Sentinel information • Methodology for selection of physical system functions to protect, based upon: – – Operational risk-based prioritization Dependable Sys. Ml system descriptions Integrated Sys. Ml descriptions/ Attack Tree tools for red team participation Penetration testing • System-of-Systems based, mission-level security considerations governing widget level security implementation decisions – Currently using a laboratory environment (emulated base defense system) to address solution requirements and doctrine
System Aware Cyber Security Publications JOURNAL ARTICLES: • B. M. Horowitz, R. A. Jones, Smart security sentinels for providing cybersecurity for critical system functions: unmanned aerial vehicle case study, Journal of Aerospace Operations, (Under review) • R. A. Jones, B. Luckett, P. Beling, B. M. Horowitz, Architectural Scoring Framework for the Creation and Evaluation of System-Aware Cyber Security Solutions, Journal of Environmental Systems and Decisions 33, no. 3 (2013): 341 -361. • B. M. Horowtiz and K. M. Pierce, The integration of diversely redundant designs, dynamic system models, and state estimation technology to the cyber security of physical systems, Systems Engineering, vol 16, Issue 4 (2013): 401 -412 • R. A. Jones and B. M. Horowitz, A system-aware cyber security architecture, Systems Engineering, Volume 15, No. 2 (2012), 224 -240. • J. L. Bayuk and B. M. Horowitz, An architectural systems engineering methodology for addressing cyber security, Systems Engineering 14 (2011), 294 -304. REFEREED CONFERENCE ARTICLES • G. L. Babineau, R. A. Jones, and B. M. Horowitz, A system-aware cyber security method for shipboard control systems with a method described to evaluate cyber security solutions, 2012 IEEE International Conference on Technologies for Homeland Security (HST), 2012. • R. A. Jones, T. V. Nguyen, and B. M. Horowitz, System-Aware security for nuclear power systems, 2011 IEEE International Conference on Technologies for Homeland Security (HST), 2011, pp. 224 -229.
Patent Related Activity • US Patent Application – US Patent App No. 14/660, 278: “Cyber-Physical System Defense” • Provisional Patents – US Prov. No. 61/955, 669: “Cloud Based System Aware Cybersecurity and Related Methods Thereof” – US Prov. No. 62/075, 179: “System Aware Cybersecurity and Related Methods Thereof” • In Preparation – Additive Manufacturing (3 D Printer) Cyber Security
- Slides: 15