Cybersecurity Expanding the Front Lines of Defense Dr
Cybersecurity: Expanding the Front Lines of Defense Dr. George K. Kostopoulos Professor Electrical and Computer Engineering New York Institute of Technology Nanjing University of Posts and Telecomm www. kostopoulos. us Cybersecurity Information Assurance University of Maryland, USA

Cybersecurity: Expanding the Front Lines of Defense Importance of Cyberspace to Society 1990 – Cyberspace was just a novelty with uncertain future. 2011 – Cyberspace is the Operational Level of practically every aspect of human interaction. Dependence of Society on Cyberspace 1990 – 0% 2011 – 100% Level of Cyberspace Security 1990 – 0% 2011 – 0% to ? ? No one knows
Cybersecurity: Expanding the Front Lines of Defense Cyberspace Security Threat #2 – Malware • With a six month delay effective anti-malware being continuously developed. • Every three months a new malware infects the Cyberspace. • We are not winning the war against malware, but at least we are not losing it.
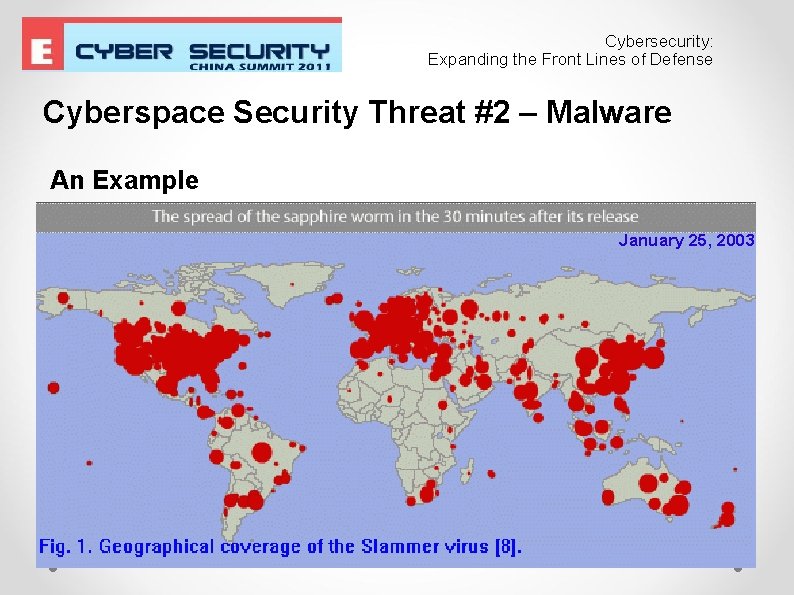
Cybersecurity: Expanding the Front Lines of Defense Cyberspace Security Threat #2 – Malware An Example January 25, 2003

Cybersecurity: Expanding the Front Lines of Defense Cyberspace Security Threat #1 – Distributed Denial of Service • Attacker “enslaves” computers with in diverse parts of the world using them as “handlers”. • Over time, the “handlers “ install code in “agent” computers. • • That code makes repeated requests for service out of the targeted website. • Collectively, the requests exceed the capacity of the website's server. • Bona fide visitors to the targeted website are denied service.

Cybersecurity: Expanding the Front Lines of Defense Cyberspace Security Threat #1 – Distributed Denial of Service

Cybersecurity: Expanding the Front Lines of Defense Cyberspace Security Threat #1 – Denial of Service Volume of attack on the increase.

Cybersecurity: Expanding the Front Lines of Defense Cyberspace Security Threat #1 – Denial of Service E-Crime using Denial of Service attacks: Bookie reveals $100, 000 cost of denial-of-service extortion attacks. http: //www. silicon. com/technology/security/2004/06/11/bookie-reveals-100000 -cost-of-denial-of-service-extortionattacks-39121278/ New anti-Do. S strategies: Downtime caused by DDo. S attacks can cost your business tens, hundreds of thousands, or even millions of dollars. Due to the complex nature of these attacks, it is extremely difficult and expensive to stop. . . “. http: //www. gigenet. com/ddos-protection. html Brute force solution using servers of vast capacity Consequences “. . . denial of service attacks reduce future visits. . . changing surfer preferences. . . ” http: //infosecon. net/workshop/pdf/6. pdf

Cybersecurity: Expanding the Front Lines of Defense The Proposal Routers throughout the Internet to have embedded a Suprvisory Control And Data Acquisition, SCADA, software with 1. Artificial Intelligence that monitors the volume of traffic destined to websites. 2. Maintains a database and creates “ceilings” for expected traffic taking into account statically and dynamically established parameters. a. Static parameters are provided by the destination server. b. Dynamic parameters are calculated by the Traffic Control Algorithm. 3. Communicates with surounding routers – horizontally and vertically – optimizing the performance of the SCADA. 4. Communicates with the destination server, reports traffic and receives updated traffic controlparameters.

Cybersecurity: Expanding the Front Lines of Defense Hardware viewpoint of the Internet: Internet routers Server hosting the website of interest

Cybersecurity: Expanding the Front Lines of Defense Hardware viewpoint of the Internet: To other nodes Internet routers Server hosting the website of interest connected to the first Internet node.

Cybersecurity: Expanding the Front Lines of Defense Traffic Flow on the Internet Typical Histogram of Router Traffic for 100 URL Destinations. Requests Entering a Router. Assuming Uniform Traffic.

Cybersecurity: Expanding the Front Lines of Defense Flow Analysis Algorithm: Basic Functions • Monitors Traffic Rate - Increases are Expected to Be Gradual. • Maintains Records of Traffic to Each Destination.

Cybersecurity: Expanding the Front Lines of Defense Router Traffic Normalized to the Respective Average Flow Showing the Level of the Potential Threat.

Cybersecurity: Expanding the Front Lines of Defense Conclusion • The Internet Routers located throughout the world are custodians of very valuable raw data. Namely, packet origin IP, destination IP, traveled path, timing, etc This wealth of information when cross correlated can create valuable information that can absolutely block and document Denial-of-Service attacks.

Cybersecurity: Expanding the Front Lines of Defense Current Research Modeling and simulation of Internet router traffic control algorithms. Use of artificial intelligence aiming at the detection and prevention Denial of Service attacks.
- Slides: 16