Cybersecurity A definition across Europe and North America
Cybersecurity: A definition across Europe and North America Katia Guerra Dan J. Kim 07/09/2020
On 2018, the average cost of a data breach globally was $3. 86 million (U. S. dollars) (IBM, 2018). Security/Cybersecurity/Privacy represents the most important IT management issue according to 2019 SIM IT Trends Report (Kappelman et al. , 2020).
A consistent definition of the term cybersecurity is missing in the “professional, governmental, and academic work” (Schatz et al. , 2017). It is challenging to agree on a uniform definition that includes all technical, organizational, and political issues evoked by the term “cybersecurity”.
“Improved” definition of cybersecurity • “Cybersecurity is the organization and collection of resources, processes, and structures used to protect cyberspace and cyberspace-enabled systems from occurrences that misalign de jure from de facto property rights” (Craigen et al. , 2014). • “The approach and actions associated with security risk management processes followed by organizations and states to protect confidentiality, integrity and availability of data and assets used in cyberspace. ” (Schatz et al. , 2017).
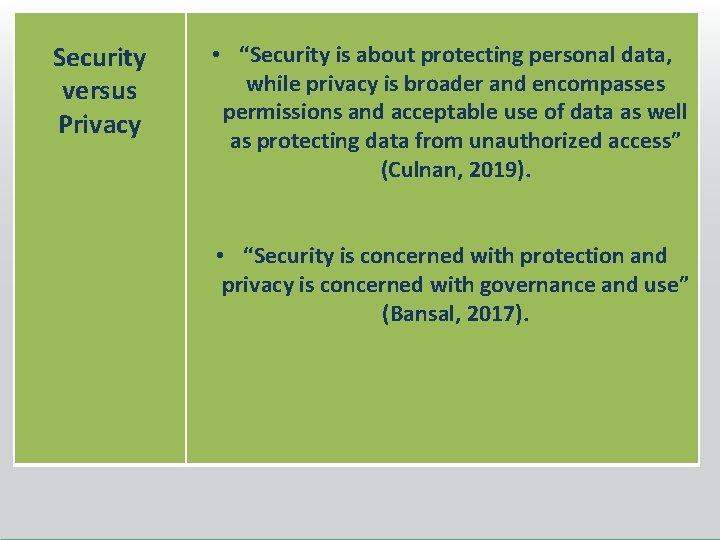
Security versus Privacy • “Security is about protecting personal data, while privacy is broader and encompasses permissions and acceptable use of data as well as protecting data from unauthorized access” (Culnan, 2019). • “Security is concerned with protection and privacy is concerned with governance and use” (Bansal, 2017).
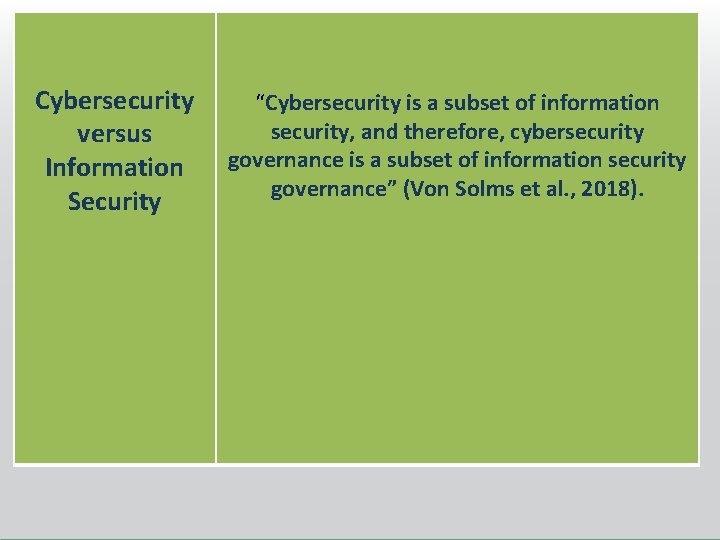
Cybersecurity versus Information Security “Cybersecurity is a subset of information security, and therefore, cybersecurity governance is a subset of information security governance” (Von Solms et al. , 2018).
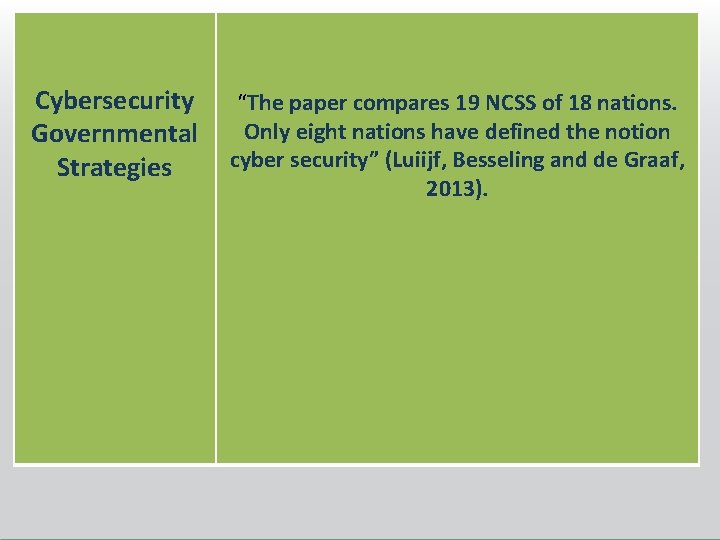
Cybersecurity Governmental Strategies “The paper compares 19 NCSS of 18 nations. Only eight nations have defined the notion cyber security” (Luiijf, Besseling and de Graaf, 2013).

Lack of comparison among definitions of cybersecurity, information security, and privacy in the academic literature and the governmental bodies, Europe and North America. Such comparison will be worthy because it will provide new insights to develop a shared definition of cybersecurity across Europe and North America.
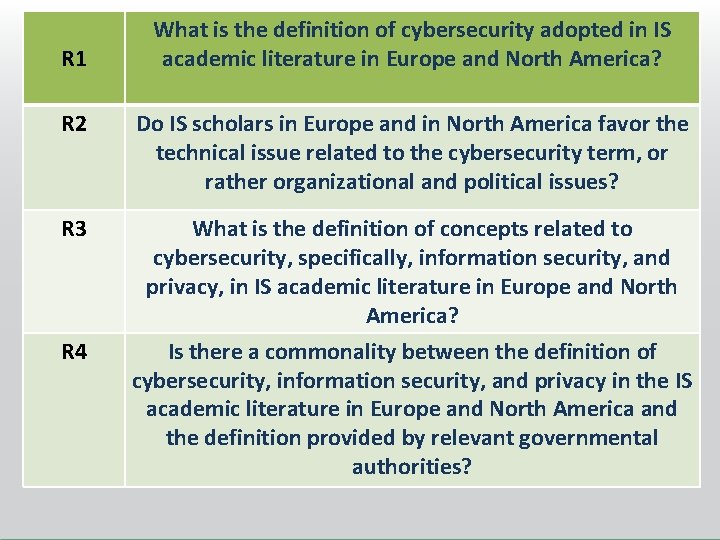
R 1 What is the definition of cybersecurity adopted in IS academic literature in Europe and North America? R 2 Do IS scholars in Europe and in North America favor the technical issue related to the cybersecurity term, or rather organizational and political issues? R 3 What is the definition of concepts related to cybersecurity, specifically, information security, and privacy, in IS academic literature in Europe and North America? Is there a commonality between the definition of cybersecurity, information security, and privacy in the IS academic literature in Europe and North America and the definition provided by relevant governmental authorities? R 4

RESEARCH METHOD Systematic Literature Review: ü Selection of a list of IS journals in North America and in Europe using the ABI/Inform Database. ü Identification of specific articles published from 2000 to 2020 by scanning the full text on the base of specific keyword search results. Identification of the most representative terms used to describe cybersecurity, information security, and privacy.
RESEARCH METHOD Selection of European and North America provisions that contain definitions of cybersecurity, information security, and privacy. Comparison of definitions provided by regulations with those obtained through the systematic literature review.
IMPLICATIONS Better understanding of the definition status of cybersecurity, information security, and privacy, both in Europe and North America. Development of a cohesive definition shared across Europe and North America. The idea to adopt a standard cybersecurity definition will allow to move toward a potential international law on cybersecurity. The uniformity of such law will lead organizations that operate worldwide to implement more effectively possible cybersecurity measures against cyberattacks.
References • • • Ackerman, M. 2004. “Privacy in Pervasive Environments”: Next Generation Labeling Protocols, ” Personal and Ubiquitous Computing (8: 6), pp. 430 -439. Baylon, C. 2014. “Challenges at the Intersection of Cyber Security and Space Security: Country and International Institution Perspectives”. Retrieved from London: http: //www. chathamhouse. org/publication/challenges-intersection-cyber-security-andspace securitycountry-and-international. Craigen, D. , Diakun-Thibault, N. , and Purse, R. 2014. “Defining Cybersecurity”. Technology Innovation Management Review, 4(10), pp. 13 -21. Giles, K. , and Hagestad, W. 2013. “Divided by a common language: Cyber definitions in Chinese, Russian and English”. 2013 5 th International Conference on Cyber Conflict K. Podins, J. Stinissen, M. Maybaum (Eds. ) Luiijf, E. , Besseling, K. , and de Graaf, P. 2013. “Nineteen national cyber security strategies”, International Journal of Critical Infrastructures, 9(1), pp. 3 -31. Kappelman, L. , Torres, R. , Mc. Lean, E. , Maurer, C. , Johnson, V. , and Kim, K. 2018. "The 2018 SIM IT Issues and Trends Study, " MIS Quarterly Executive, 18 (1), article 7. IBM (2018). “IBM Study: Hidden Costs of Data Breaches Increase Expenses for Businesses”. Retrieved from https: //newsroom. ibm. com/2018 -07 -10 -IBM-Study-Hidden-Costs-of-Data-Breaches-Increase-Expenses-for. Businesses. Schatz, D. Bashroush, R. and Wall, J. 2017. “Towards a More Representative Definition of Cybersecurity”, Journal of Digital Forensics, Security and Law, 12(2), pp. 53 -74. Von Solms, R. and Van Niekerk, J. 2013. “From information security to cyber security”, Computers & Security, (38) pp. 97 -1 -2. Von Solms, B. , Von Solms, R. 2018. “Cybersecurity and information security – what goes where? ”, Information and Computer Security, (26: 1), pp. 2 -9.

THANK YOU Katia Guerra katia. Guerra@unt. edu Dan J. Kim dan. unt@unt. edu
- Slides: 14