CYBERSAFETY 2017 The Second International Workshop on Computational

CYBERSAFETY 2017 The Second International Workshop on Computational Methods for Cyber. Safety
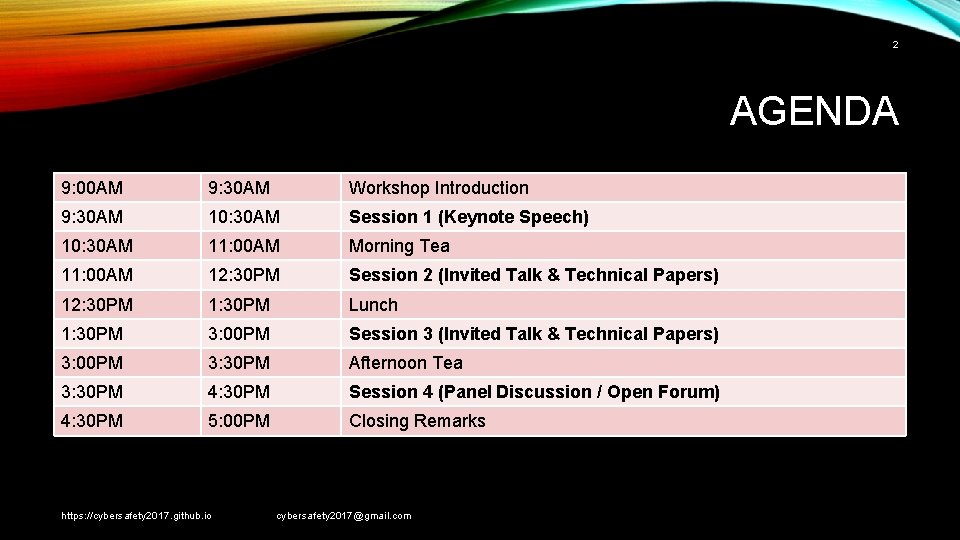
2 AGENDA 9: 00 AM 9: 30 AM Workshop Introduction 9: 30 AM 10: 30 AM Session 1 (Keynote Speech) 10: 30 AM 11: 00 AM Morning Tea 11: 00 AM 12: 30 PM Session 2 (Invited Talk & Technical Papers) 12: 30 PM 1: 30 PM Lunch 1: 30 PM 3: 00 PM Session 3 (Invited Talk & Technical Papers) 3: 00 PM 3: 30 PM Afternoon Tea 3: 30 PM 4: 30 PM Session 4 (Panel Discussion / Open Forum) 4: 30 PM 5: 00 PM Closing Remarks https: //cybersafety 2017. github. io cybersafety 2017@gmail. com
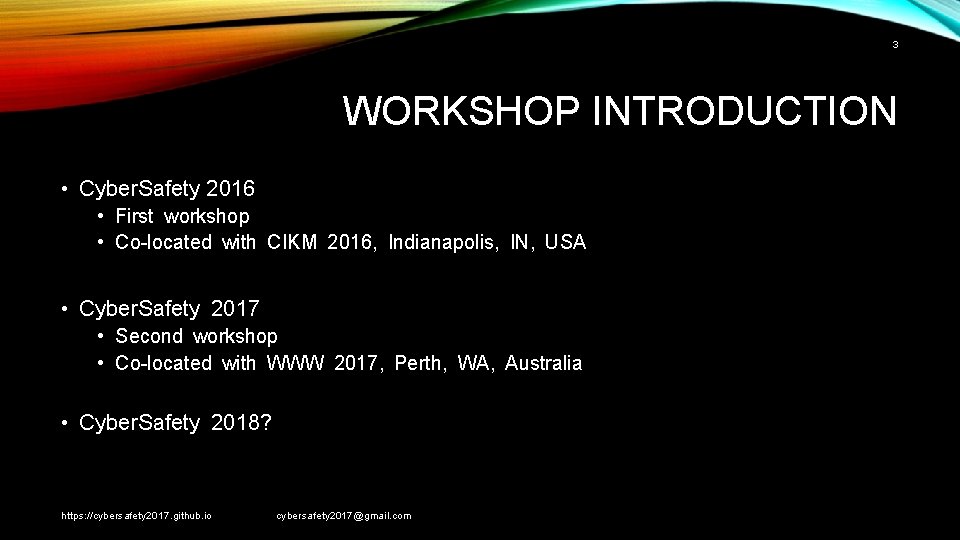
3 WORKSHOP INTRODUCTION • Cyber. Safety 2016 • First workshop • Co-located with CIKM 2016, Indianapolis, IN, USA • Cyber. Safety 2017 • Second workshop • Co-located with WWW 2017, Perth, WA, Australia • Cyber. Safety 2018? https: //cybersafety 2017. github. io cybersafety 2017@gmail. com
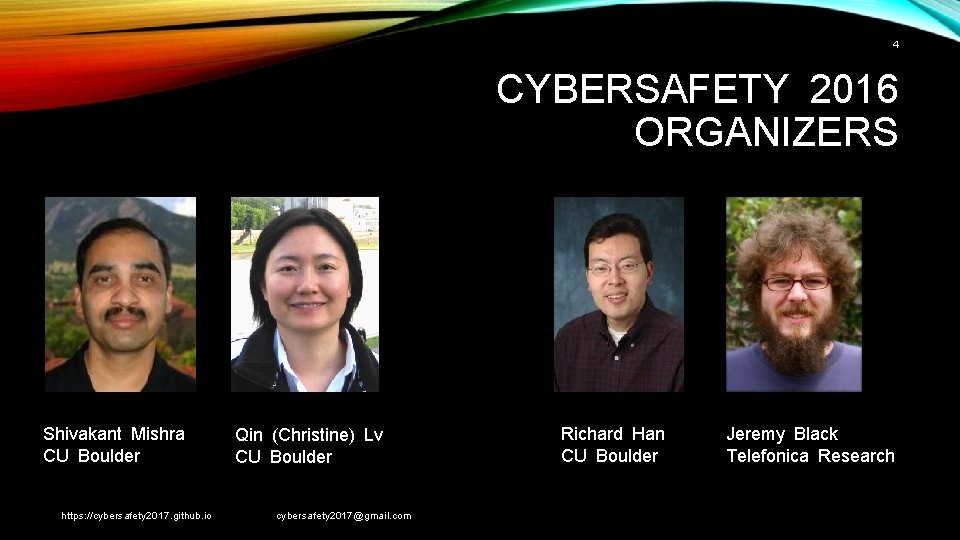
4 CYBERSAFETY 2016 ORGANIZERS Shivakant Mishra CU Boulder https: //cybersafety 2017. github. io Qin (Christine) Lv CU Boulder cybersafety 2017@gmail. com Richard Han CU Boulder Jeremy Black Telefonica Research

5 CYBERSAFETY 2017 ORGANIZERS Shivakant Mishra Jeremy Black CU Boulder Telefonica Research https: //cybersafety 2017. github. io Bert Huang Virginia Tech cybersafety 2017@gmail. com Qin (Christine) Lv CU Boulder Homa Hosseinmardi Danaher Labs Srijan Kumar U of Maryland

6 CYBERSAFETY 2017 TPC • • • Richard Han, University of Colorado Boulder, USA Emiliano De Cristofaro, University College London, UK Francesca Spezzano, Boise State University, Boise, USA Gianluca Stringhini, University College, London, UK Emilio Ferrara, University of Southern California, USA Keith W. Ross, New York University, USA April Edwards, Ursinus College, Collegeville, USA Haewoon Kwak, Scientist, Qatar Computing Research Institute, Qatar Michal Ptaszynski, Kitami Institute of Technology, Kitami, Japan Anna Squicciarin, Pennsylvania State University, USA https: //cybersafety 2017. github. io cybersafety 2017@gmail. com
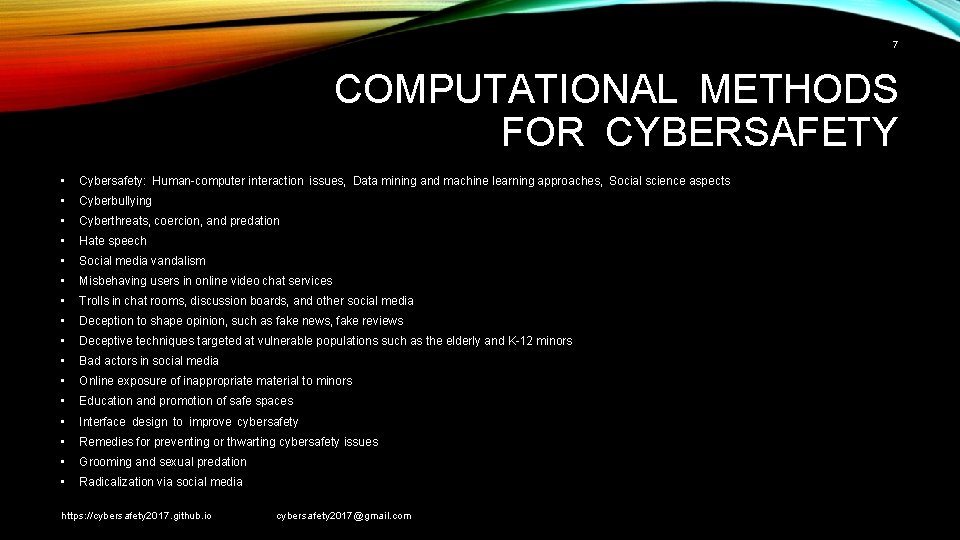
7 COMPUTATIONAL METHODS FOR CYBERSAFETY • Cybersafety: Human-computer interaction issues, Data mining and machine learning approaches, Social science aspects • Cyberbullying • Cyberthreats, coercion, and predation • Hate speech • Social media vandalism • Misbehaving users in online video chat services • Trolls in chat rooms, discussion boards, and other social media • Deception to shape opinion, such as fake news, fake reviews • Deceptive techniques targeted at vulnerable populations such as the elderly and K-12 minors • Bad actors in social media • Online exposure of inappropriate material to minors • Education and promotion of safe spaces • Interface design to improve cybersafety • Remedies for preventing or thwarting cybersafety issues • Grooming and sexual predation • Radicalization via social media https: //cybersafety 2017. github. io cybersafety 2017@gmail. com
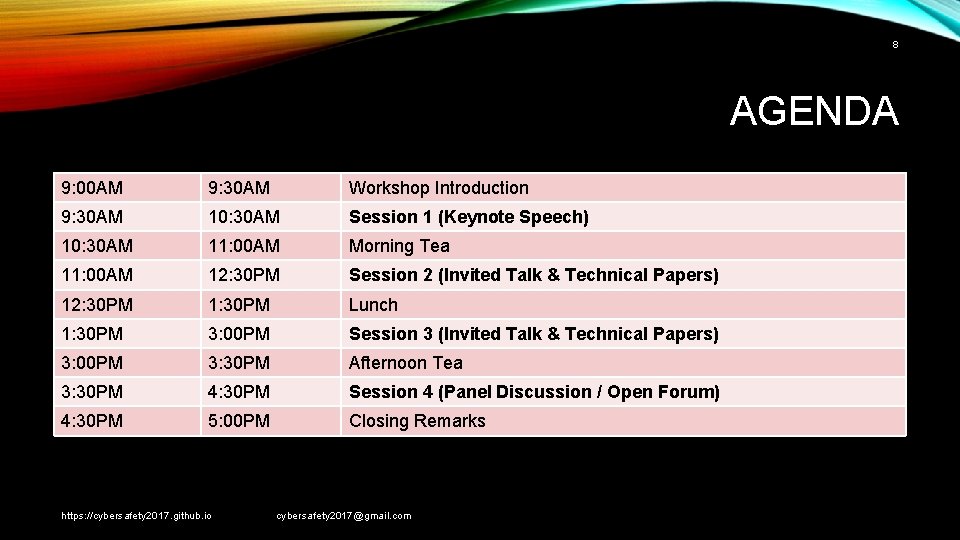
8 AGENDA 9: 00 AM 9: 30 AM Workshop Introduction 9: 30 AM 10: 30 AM Session 1 (Keynote Speech) 10: 30 AM 11: 00 AM Morning Tea 11: 00 AM 12: 30 PM Session 2 (Invited Talk & Technical Papers) 12: 30 PM 1: 30 PM Lunch 1: 30 PM 3: 00 PM Session 3 (Invited Talk & Technical Papers) 3: 00 PM 3: 30 PM Afternoon Tea 3: 30 PM 4: 30 PM Session 4 (Panel Discussion / Open Forum) 4: 30 PM 5: 00 PM Closing Remarks https: //cybersafety 2017. github. io cybersafety 2017@gmail. com
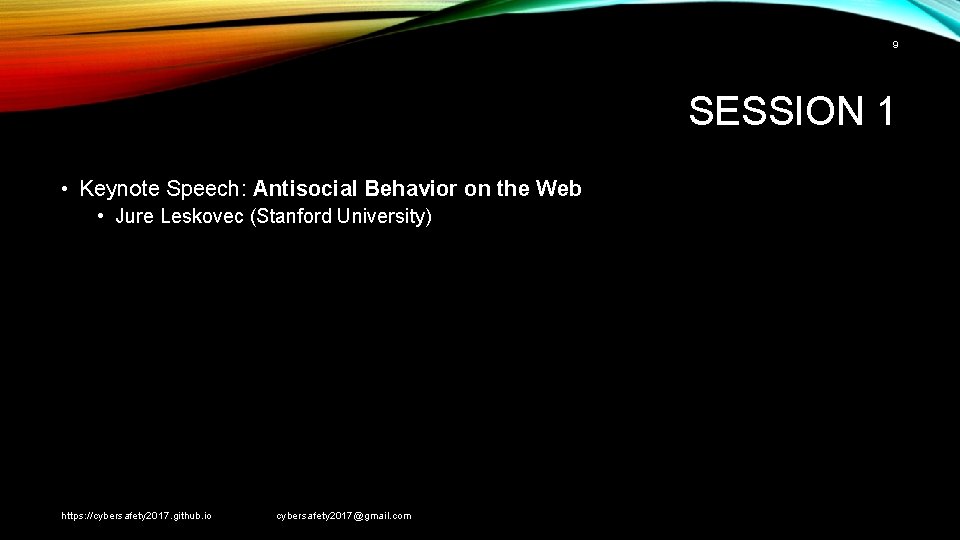
9 SESSION 1 • Keynote Speech: Antisocial Behavior on the Web • Jure Leskovec (Stanford University) https: //cybersafety 2017. github. io cybersafety 2017@gmail. com
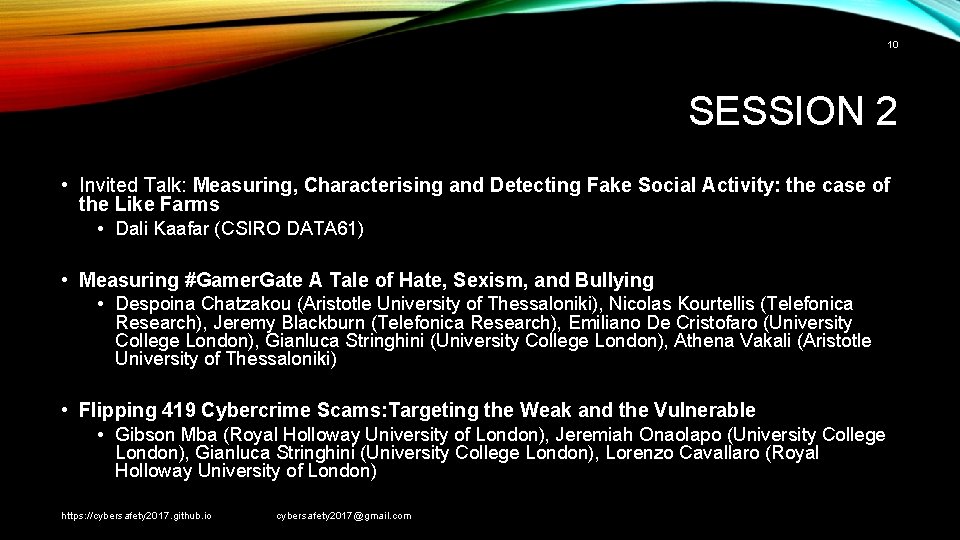
10 SESSION 2 • Invited Talk: Measuring, Characterising and Detecting Fake Social Activity: the case of the Like Farms • Dali Kaafar (CSIRO DATA 61) • Measuring #Gamer. Gate A Tale of Hate, Sexism, and Bullying • Despoina Chatzakou (Aristotle University of Thessaloniki), Nicolas Kourtellis (Telefonica Research), Jeremy Blackburn (Telefonica Research), Emiliano De Cristofaro (University College London), Gianluca Stringhini (University College London), Athena Vakali (Aristotle University of Thessaloniki) • Flipping 419 Cybercrime Scams: Targeting the Weak and the Vulnerable • Gibson Mba (Royal Holloway University of London), Jeremiah Onaolapo (University College London), Gianluca Stringhini (University College London), Lorenzo Cavallaro (Royal Holloway University of London) https: //cybersafety 2017. github. io cybersafety 2017@gmail. com
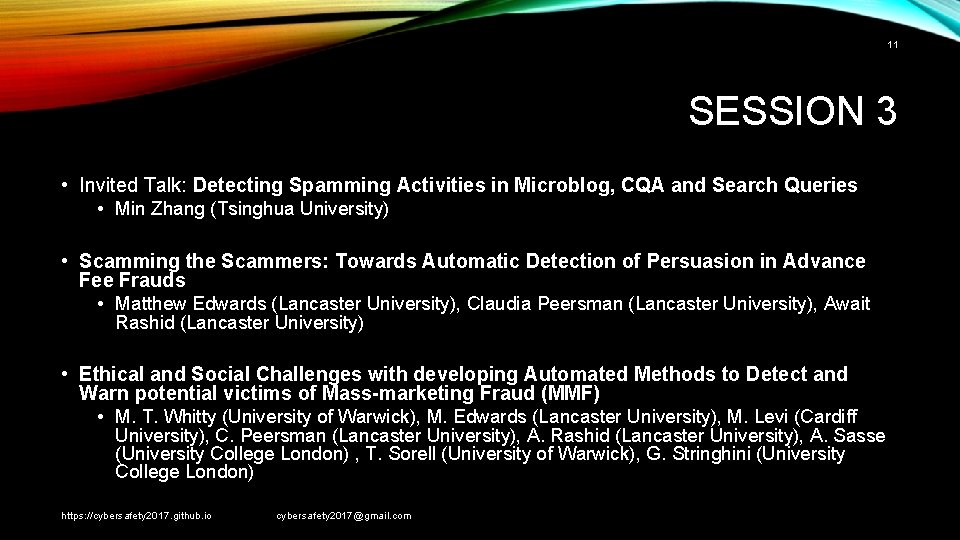
11 SESSION 3 • Invited Talk: Detecting Spamming Activities in Microblog, CQA and Search Queries • Min Zhang (Tsinghua University) • Scamming the Scammers: Towards Automatic Detection of Persuasion in Advance Fee Frauds • Matthew Edwards (Lancaster University), Claudia Peersman (Lancaster University), Await Rashid (Lancaster University) • Ethical and Social Challenges with developing Automated Methods to Detect and Warn potential victims of Mass-marketing Fraud (MMF) • M. T. Whitty (University of Warwick), M. Edwards (Lancaster University), M. Levi (Cardiff University), C. Peersman (Lancaster University), A. Rashid (Lancaster University), A. Sasse (University College London) , T. Sorell (University of Warwick), G. Stringhini (University College London) https: //cybersafety 2017. github. io cybersafety 2017@gmail. com

12 SESSION 4 • Panel Discussion / Open Forum • • • Proceed with another workshop? Hold the next workshop in the US? How to build the community? What is within scope for this workshop? Differentiating / merging with other related conferences (e. g. , social networking) Industry participation? (social networking services: fake news, hate speech, …) Government? Law enforcement? Third-party/indepent tools and algorithms offered by our community? … https: //cybersafety 2017. github. io cybersafety 2017@gmail. com
- Slides: 12