CyberPhysical Systems and Making them Trustworthy Jeannette M
Cyber-Physical Systems and Making them Trustworthy! Jeannette M. Wing Assistant Director Computer and Information Science and Engineering Directorate National Science Foundation Cyber-Physical Systems Security Workshop Newark, NJ July 22, 2009
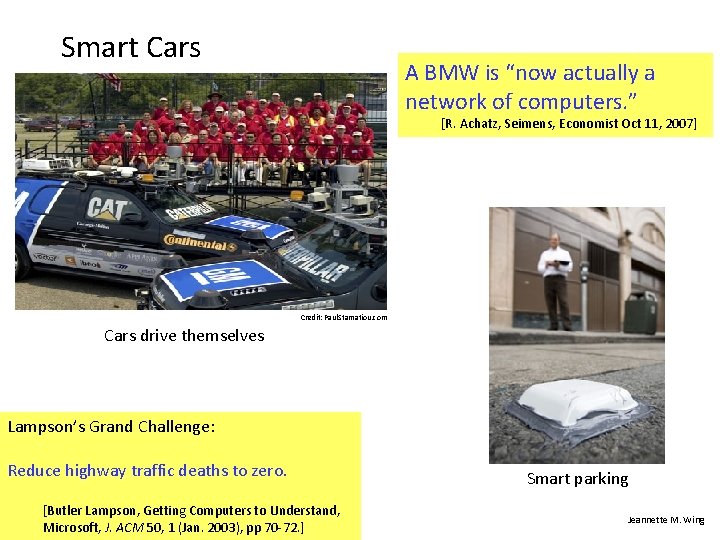
Smart Cars A BMW is “now actually a network of computers. ” [R. Achatz, Seimens, Economist Oct 11, 2007] Credit: Paul. Stamatiou. com Cars drive themselves Lampson’s Grand Challenge: Reduce highway traffic deaths to zero. [Butler Lampson, Getting Computers to Understand, 2 Microsoft, J. ACM 50, 1 (Jan. 2003), pp 70 -72. ] Cyber Physical Systems Security Smart parking Jeannette M. Wing
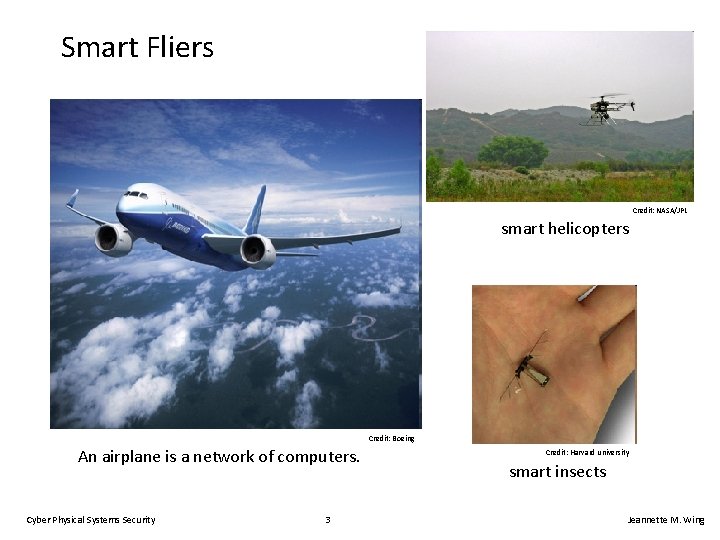
Smart Fliers Credit: NASA/JPL smart helicopters Credit: Boeing An airplane is a network of computers. Cyber Physical Systems Security 3 Credit: Harvard university smart insects Jeannette M. Wing
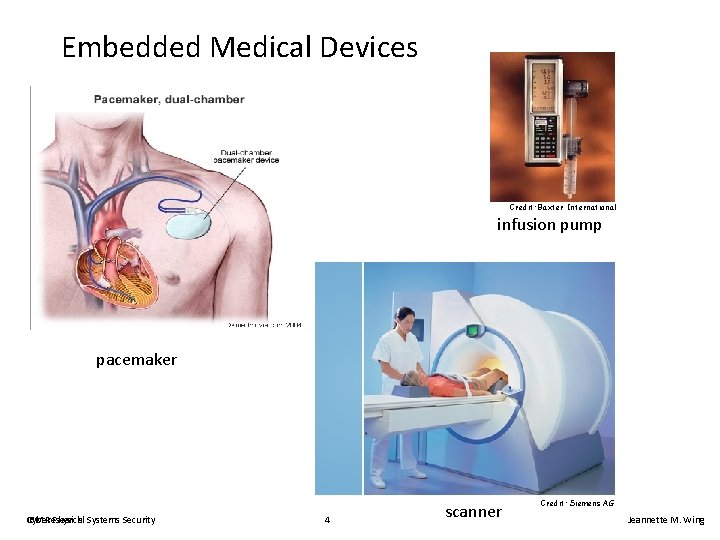
Embedded Medical Devices Credit: Baxter International infusion pump pacemaker Cyber. Research IBM Physical Systems Security 4 scanner Credit: Siemens AG Jeannette M. Wing
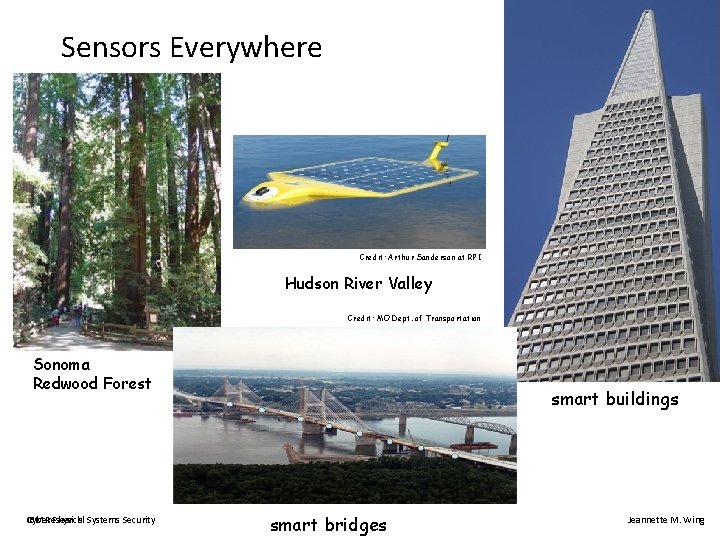
Sensors Everywhere Credit: Arthur Sanderson at RPI Hudson River Valley Credit: MO Dept. of Transportation Sonoma Redwood Forest Cyber. Research IBM Physical Systems Security smart buildings 5 smart bridges Jeannette M. Wing
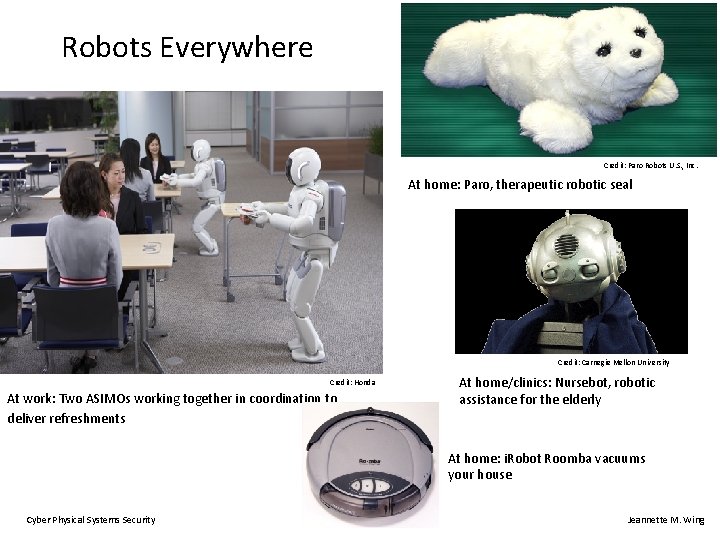
Robots Everywhere Credit: Paro Robots U. S. , Inc. At home: Paro, therapeutic robotic seal Credit: Carnegie Mellon University Credit: Honda At work: Two ASIMOs working together in coordination to deliver refreshments At home/clinics: Nursebot, robotic assistance for the elderly At home: i. Robot Roomba vacuums your house Cyber Physical Systems Security 6 Jeannette M. Wing
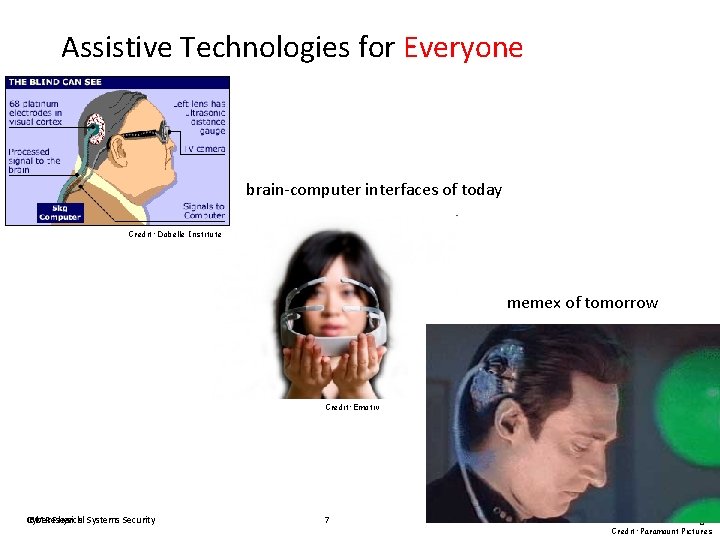
Assistive Technologies for Everyone brain-computer interfaces of today Credit: Dobelle Institute memex of tomorrow Credit: Emotiv Cyber. Research IBM Physical Systems Security 7 Jeannette M. Wing Credit: Paramount Pictures
What is Common to These Systems? • They have a computational core that interacts with the physical world. • Cyber-physical systems are engineered systems that require tight conjoining of and coordination between the computational (discrete) and the physical (continuous). • Trends for the future – Cyber-physical systems will be smarter and smarter. – More and more intelligence will be in software. Cyber Physical Systems Security 8 Jeannette M. Wing
CSTB National Academies Study Software for Dependable Systems: Sufficient Evidence? Daniel Jackson, Martyn Thomas, and Lynette I. Millett, Editors May 9, 2007 Cyber Physical Systems Security 9 Jeannette M. Wing
U. S Broader Research Agenda and Priorities Dan Reed and George Scalise, editors August 2007 Cyber Physical Systems Security 10 Jeannette M. Wing
U. S Broader Research Agenda and Priorities Dan Reed and George Scalise, editors August 2007 #1 Priority: Cyber-Physical Systems Our lives depend on them. Cyber Physical Systems Security 11 Jeannette M. Wing
Cyber Security Trustworthy Computing • • Security Reliability Privacy Usability Trustworthiness from the BEGINNING. Say “NO” to bolt-on security! In what follows for CPS Research Challenges, I will interleave these aspects of Trustworthy Computing Cyber Physical Systems Security 12 Jeannette M. Wing
Trustworthiness from the Begin Cyber Physical Systems Security 13 Jeannette M. Wing
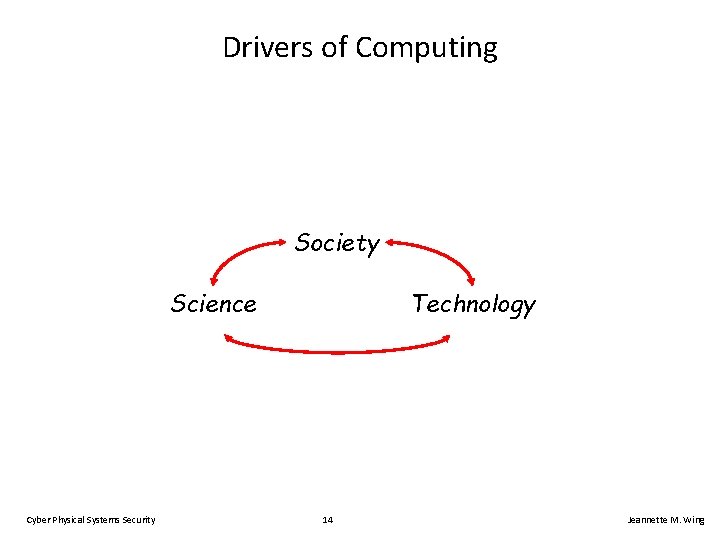
Drivers of Computing Society Science Cyber Physical Systems Security Technology 14 Jeannette M. Wing
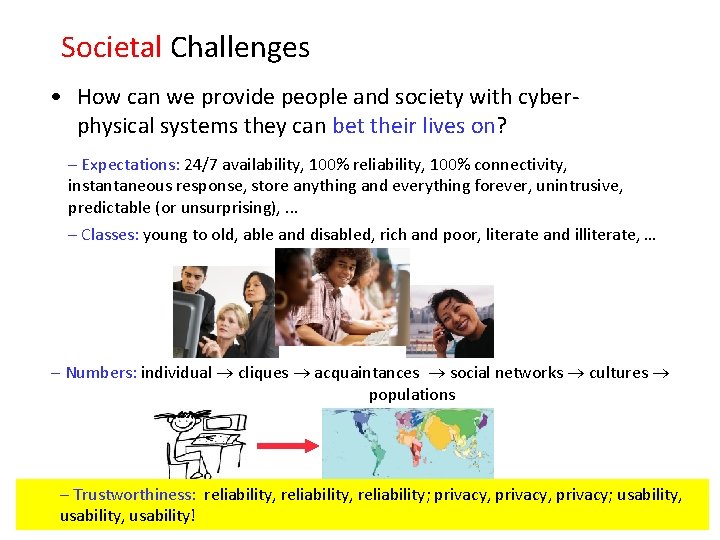
Societal Challenges • How can we provide people and society with cyberphysical systems they can bet their lives on? – Expectations: 24/7 availability, 100% reliability, 100% connectivity, instantaneous response, store anything and everything forever, unintrusive, predictable (or unsurprising), . . . – Classes: young to old, able and disabled, rich and poor, literate and illiterate, … – Numbers: individual cliques acquaintances social networks cultures populations – Trustworthiness: reliability, reliability; privacy, privacy; usability, usability! Cyber Physical Systems Security 15 Jeannette M. Wing
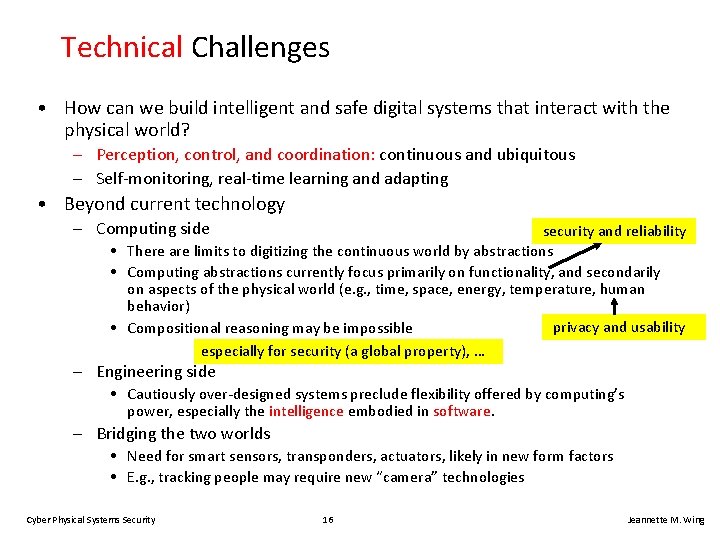
Technical Challenges • How can we build intelligent and safe digital systems that interact with the physical world? – Perception, control, and coordination: continuous and ubiquitous – Self-monitoring, real-time learning and adapting • Beyond current technology – Computing side security and reliability • There are limits to digitizing the continuous world by abstractions • Computing abstractions currently focus primarily on functionality, and secondarily on aspects of the physical world (e. g. , time, space, energy, temperature, human behavior) privacy and usability • Compositional reasoning may be impossible especially for security (a global property), … – Engineering side • Cautiously over-designed systems preclude flexibility offered by computing’s power, especially the intelligence embodied in software. – Bridging the two worlds • Need for smart sensors, transponders, actuators, likely in new form factors • E. g. , tracking people may require new “camera” technologies Cyber Physical Systems Security 16 Jeannette M. Wing
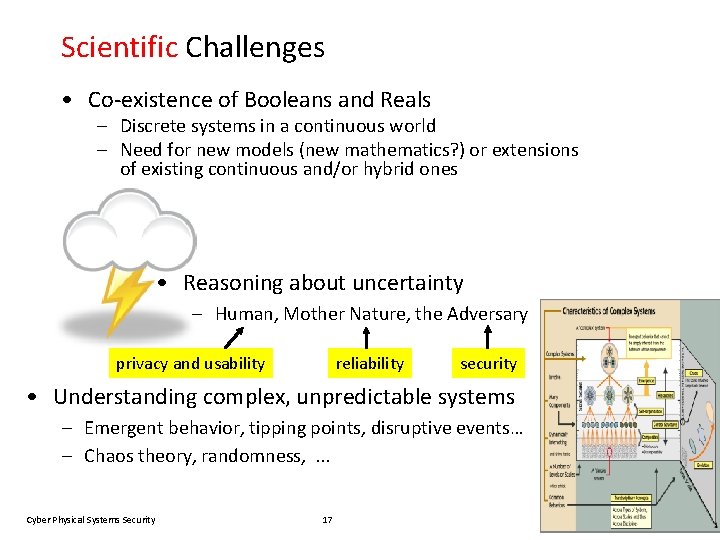
Scientific Challenges • Co-existence of Booleans and Reals – Discrete systems in a continuous world – Need for new models (new mathematics? ) or extensions of existing continuous and/or hybrid ones • Reasoning about uncertainty – Human, Mother Nature, the Adversary privacy and usability reliability security • Understanding complex, unpredictable systems – Emergent behavior, tipping points, disruptive events… – Chaos theory, randomness, . . . Cyber Physical Systems Security 17 Jeannette M. Wing

Communities Needed to Meet These Challenges
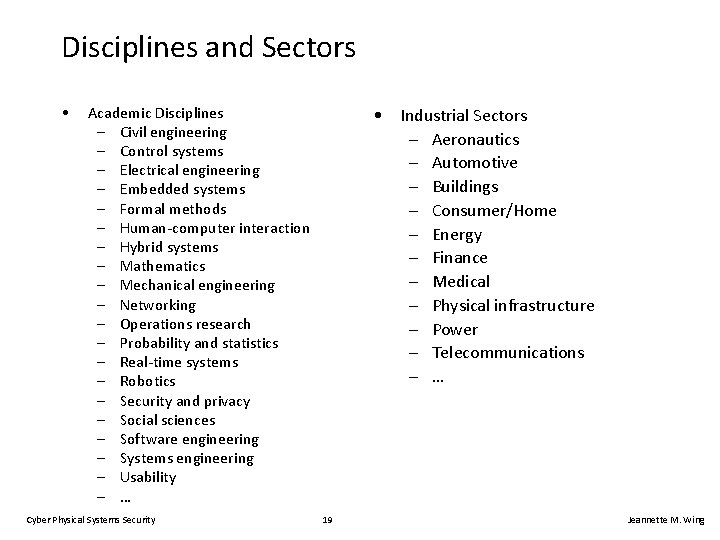
Disciplines and Sectors • Academic Disciplines – Civil engineering – Control systems – Electrical engineering – Embedded systems – Formal methods – Human-computer interaction – Hybrid systems – Mathematics – Mechanical engineering – Networking – Operations research – Probability and statistics – Real-time systems – Robotics – Security and privacy – Social sciences – Software engineering – Systems engineering – Usability – … Cyber Physical Systems Security • Industrial Sectors – Aeronautics – Automotive – Buildings – Consumer/Home – Energy – Finance – Medical – Physical infrastructure – Power – Telecommunications – … 19 Jeannette M. Wing
Partnerships • Theoreticians, experimentalists, domain experts • Computer scientists, engineers (of all types) • Industry, Academia, Government – domain experts, domain problems – general solutions that work for specific problems Cyber Physical Systems Security 20 Jeannette M. Wing
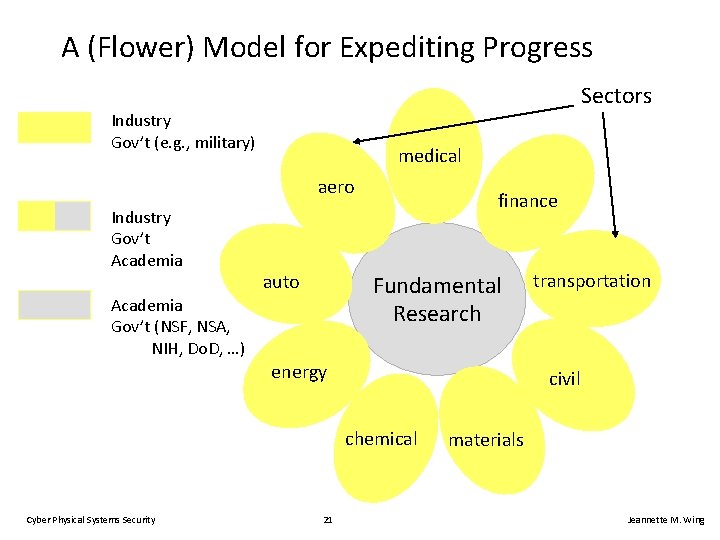
A (Flower) Model for Expediting Progress Sectors Industry Gov’t (e. g. , military) medical aero Industry Gov’t Academia Gov’t (NSF, NSA, NIH, Do. D, …) auto finance Fundamental Research energy civil chemical Cyber Physical Systems Security 21 transportation materials Jeannette M. Wing
NSF Cyber-Physical Systems Program • CISE and ENG, $30 M FY 09 – – All three divisions in CISE are participating CISE PDs: Michael Branicky, Helen Gill, Paul Oh, Lenore Zuck ENG PD: Scott Midkiff http: //www. nsf. gov/funding/pgm_summ. jsp? pims_id=503286&or g=CISE • Deadline: February 27, 2009 • Small, medium, large • Unique: CPS-Virtual Organization – My dream is that CPS-VO will help realize my Flower Model! Cyber Physical Systems Security 22 Jeannette M. Wing
What the EU is Spending on CPS • Advanced Research and Technology for Embedded Intelligent Systems (ARTEMIS) [Cyber-Physical Systems] • Annual budget of € 243 M ($325 M), includes € 144 M in private funds • 10 -yr budget € 1. 1 B public funds, € 1. 6 B private funds • Part of European Community Framework 7 • One of four ICT calls for proposals for 7 -year projects Cyber Physical Systems Security 23 Jeannette M. Wing
NSF/CISE Trustworthy Computing Program • Covers all aspects of trustworthiness – Foundations: crypto, quantum, algorithms, models, logics, languages, software – Systems: architecture, O/S, devices, I/O, networking, sensors, testbeds – Information: data – People: privacy, usability • CNCI FY 09 foci: foundations of trustworthiness, privacy, usablity • FY 09 investment $65 M, including $20 M ARRA • Program cuts across entire directorate – PDs: Amy Baylor, Richard Beigel, Karl Levitt, Sylvia Spengler, Lenore Zuck Cyber Physical Systems Security 24 Jeannette M. Wing
Thank you!
Credits • Copyrighted material used under Fair Use. If you are the copyright holder and believe your material has been used unfairly, or if you have any suggestions, feedback, or support, please contact: jsoleil@nsf. gov • Except where otherwise indicated, permission is granted to copy, distribute, and/or modify all images in this document under the terms of the GNU Free Documentation license, Version 1. 2 or any later version published by the Free Software Foundation; with no Invariant Sections, no Front. Cover Texts, and no Back-Cover Texts. A copy of the license is included in the section entitled “GNU Free Documentation license” (http: //commons. wikimedia. org/wiki/Commons: GNU_Free_Documentation_License) • The inclusion of a logo does not express or imply the endorsement by NSF of the entities' products, services or enterprises Cyber Physical Systems Security 26 Jeannette M. Wing
- Slides: 26