Cyberinfrastructure Many Things to Many People Russ Hobby
Cyberinfrastructure: Many Things to Many People Russ Hobby Program Manager Internet 2
Cyberinfrastructure? • Ask any number of people “What is Cyberinfrastructure? ” and you will probably get an equal number of definitions • We need a common understanding of CI in order to build and operate it. 2
Cyberinfrastructure --- some definitions • The term "cyberinfrastructure" was used by a United States National Science Foundation (NSF) blue-ribbon committee in 2003 in response to the question: how can NSF, as the nation's premier agency funding basic research, remove existing barriers to the rapid evolution of high performance computing, making it truly usable by all the nation's scientists, engineers, scholars, and citizens? • The term describes the new research environments that support advanced data acquisition, data storage, data management, data integration, data mining, data visualization and other computing and information processing services over the Internet 3
Cyberinfrastructure: More Than High-End Computing and Connectivity • Focused on sharing and making greater capabilities available across the science and engineering research communities • Allows applications to interoperate across institutions and disciplines • Ensures that data and software acquired at great expense are preserved and easily available to all • Empowers enhanced collaboration over distance and across disciplines. Report of the National Science Foundation Blue-Ribbon Advisory Panel on Cyberinfrastructure 4

Cyberinfrastructure Vision at NSF’S CYBERINFRASTRUCTURE VISION FOR 21 ST CENTURY DISCOVERY http: //www. nsf. gov/od/oci/ci-v 7. pdf 5
Nature of Today’s Research • Research by Discipline Groups • Researchers at Multiple Organizations • They use technology to work as a team • There is often more connection within the Discipline Group than to researchers institution 6
Example Researcher using CI Jane is an environmental researcher and is going to find a solution to Global Warming. To do this she needs to collect and store data, do analysis of the data and run some simulation models to test her hypothesis. She will share ideas, data and results with her Discipline Group. Here are her steps in using CI 7
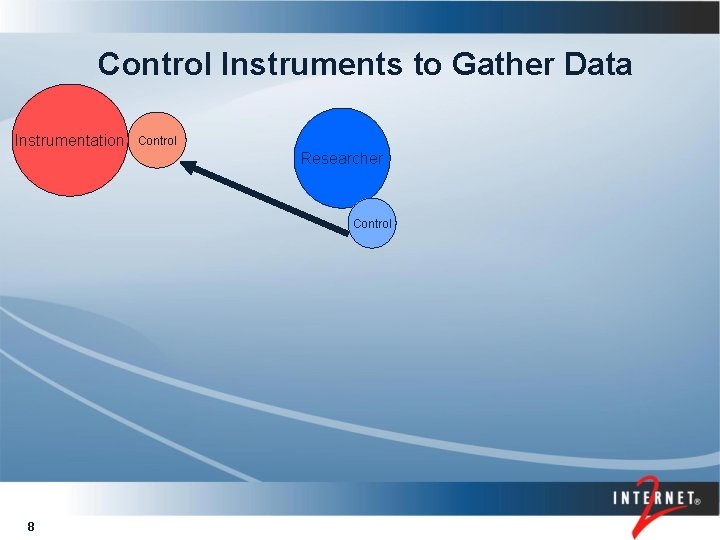
Control Instruments to Gather Data Instrumentation Control Researcher Control 8
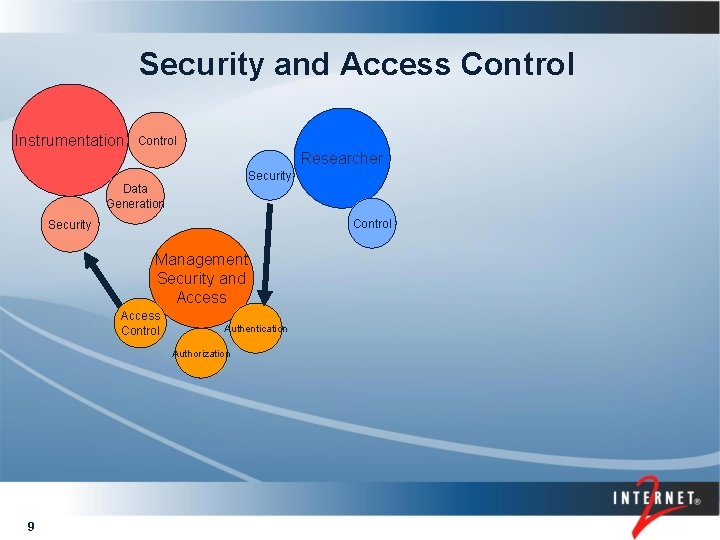
Security and Access Control Instrumentation Control Researcher Security Data Generation Control Security Management Security and Access Control Authentication Authorization 9
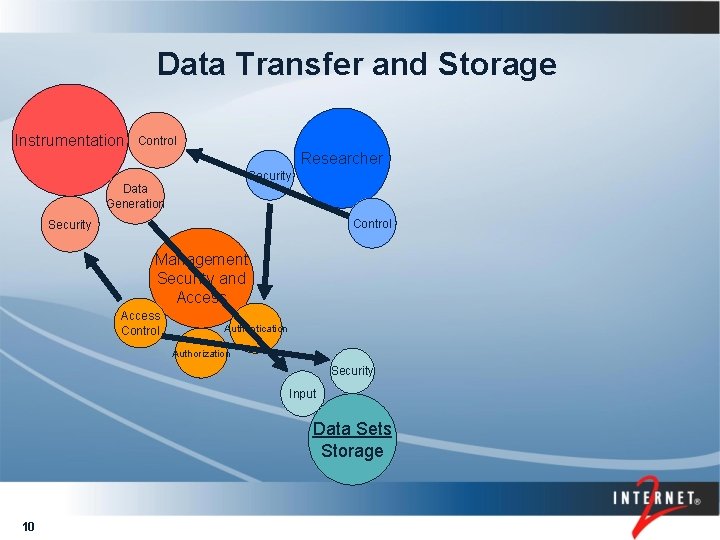
Data Transfer and Storage Instrumentation Control Researcher Security Data Generation Control Security Management Security and Access Control Authentication Authorization Security Input Data Sets Storage 10
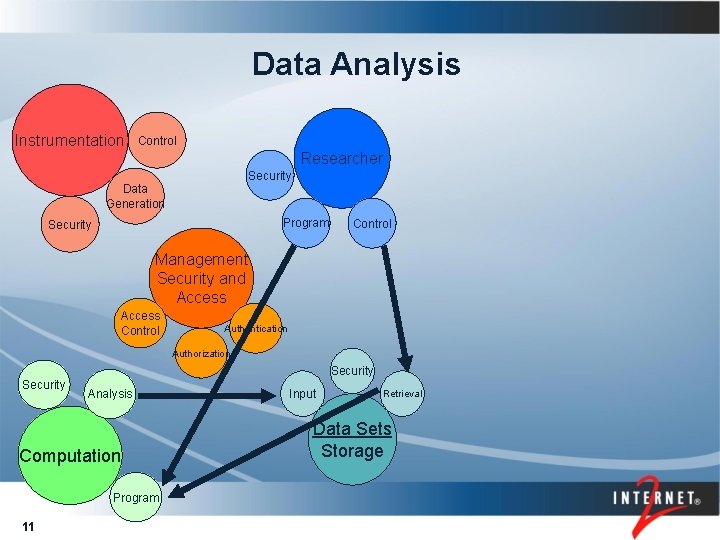
Data Analysis Instrumentation Control Researcher Security Data Generation Program Security Control Management Security and Access Control Authentication Authorization Security Analysis Computation Program 11 Input Retrieval Data Sets Storage
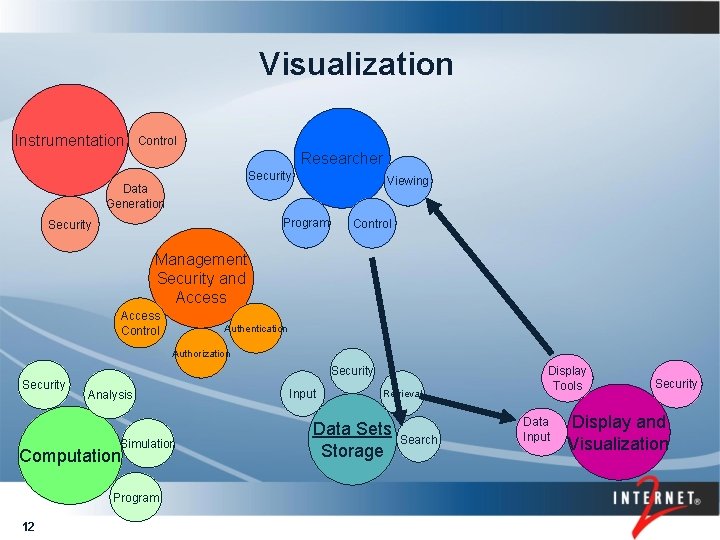
Visualization Instrumentation Control Researcher Security Viewing Data Generation Program Security Control Management Security and Access Control Authentication Authorization Security Analysis Simulation Computation Program 12 Input Retrieval Data Sets Storage Search Display Tools Data. Input Security Display and Visualization
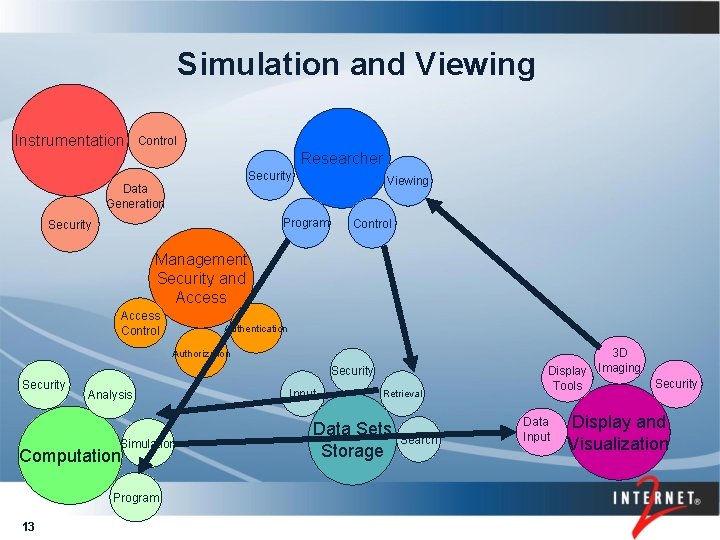
Simulation and Viewing Instrumentation Control Researcher Security Viewing Data Generation Program Security Control Management Security and Access Control Authentication Authorization Security Analysis Simulation Computation Program 13 Input Retrieval Data Sets Storage Search 3 D Imaging Display Tools Data. Input Security Display and Visualization
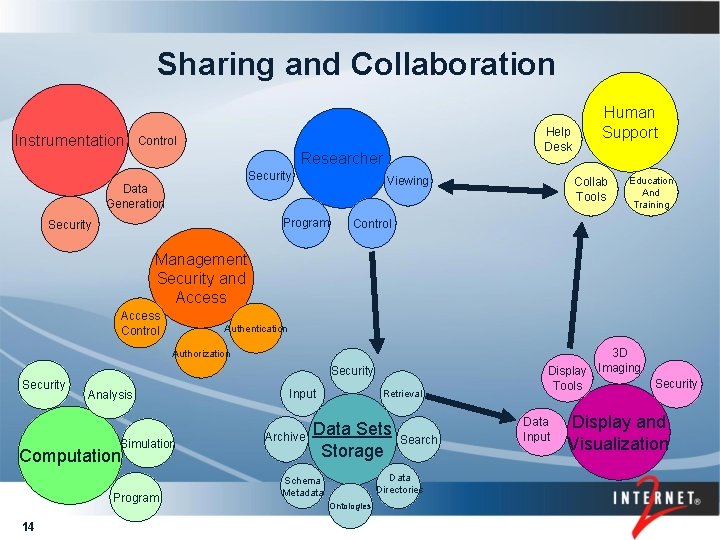
Sharing and Collaboration Instrumentation Help Desk Control Researcher Security Viewing Data Generation Program Security Human Support Collab Tools Education And Training Control Management Security and Access Control Authentication Authorization Security Analysis Simulation Computation Program 14 Input Archive Retrieval Data Sets Storage Search Data Directories Schema Metadata Ontologies 3 D Imaging Display Tools Data. Input Security Display and Visualization
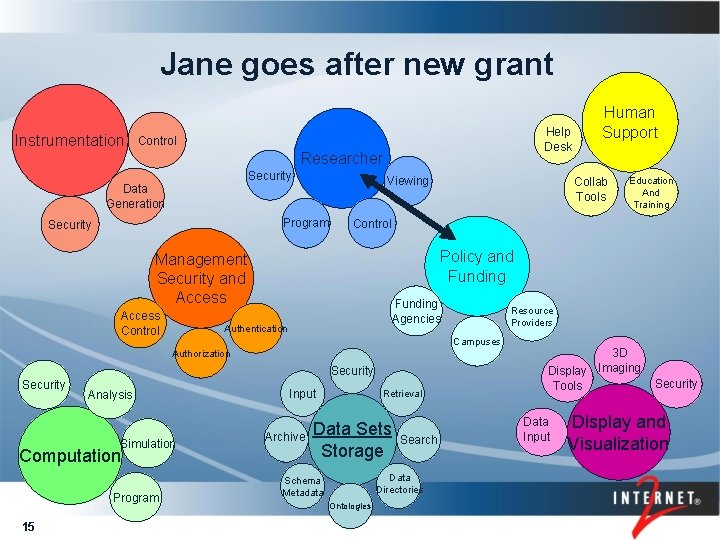
Jane goes after new grant Instrumentation Help Desk Control Researcher Security Viewing Data Generation Program Security Funding Agencies Authentication Security Simulation Computation Program 15 Resource Providers Campuses Analysis Education And Training Policy and Funding Authorization Security Collab Tools Control Management Security and Access Control Human Support Input Archive Retrieval Data Sets Storage Search Data Directories Schema Metadata Ontologies 3 D Imaging Display Tools Data. Input Security Display and Visualization
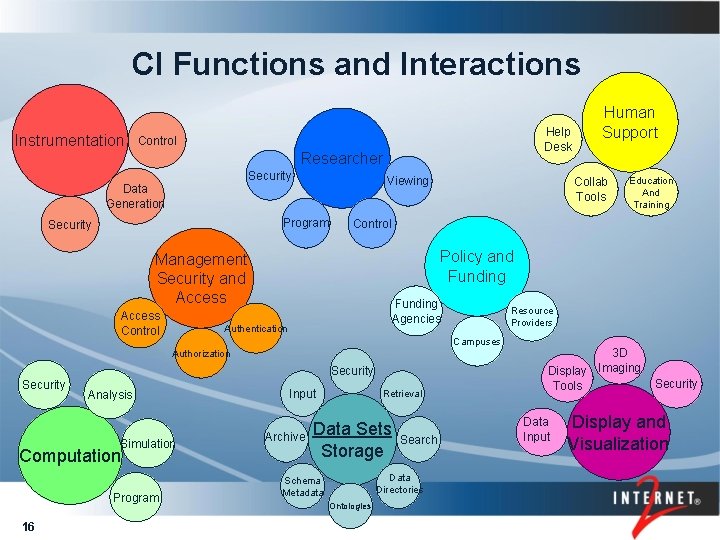
CI Functions and Interactions Instrumentation Help Desk Control Researcher Security Viewing Data Generation Program Security Funding Agencies Authentication Security Simulation Computation Program 16 Resource Providers Campuses Analysis Education And Training Policy and Funding Authorization Security Collab Tools Control Management Security and Access Control Human Support Input Archive Retrieval Data Sets Storage Search Data Directories Schema Metadata Ontologies 3 D Imaging Display Tools Data. Input Security Display and Visualization
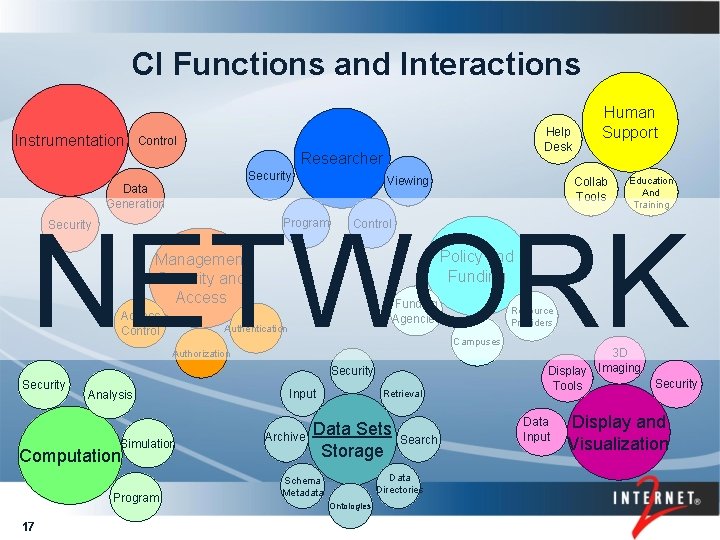
CI Functions and Interactions Instrumentation Help Desk Control Researcher Security Viewing Data Generation Human Support Collab Tools Education And Training NETWORK Program Security Control Policy and Funding Management Security and Access Control Funding Agencies Authentication Campuses Authorization Security Analysis Simulation Computation Program 17 Resource Providers Input Archive Retrieval Data Sets Storage Search Data Directories Schema Metadata Ontologies 3 D Imaging Display Tools Data. Input Security Display and Visualization
Performance CI is a System. Individual components may perform well but the overall performance depends on the components working well together. Work is needed so that users can determine the best combination of components and how to determine the problem when there are performance is lacking 18
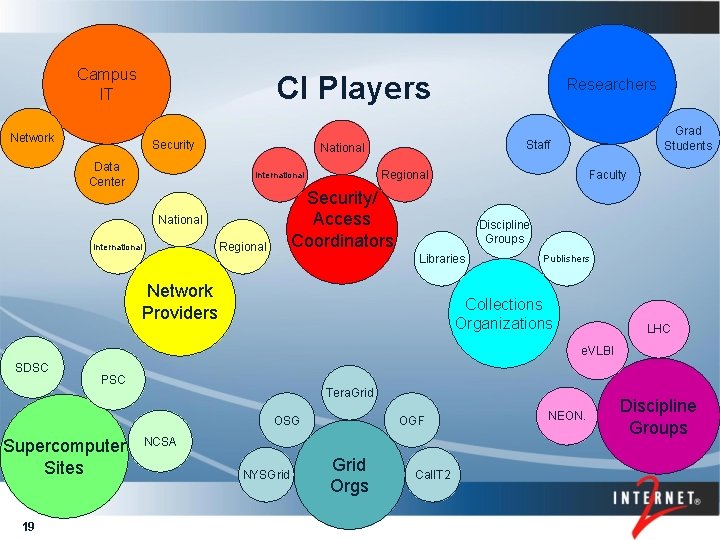
Campus IT CI Players Network Security Data Center Faculty Regional Security/ Access Coordinators National Regional Grad Students Staff National International Researchers Discipline Groups Libraries Network Providers Publishers Collections Organizations LHC e. VLBI SDSC PSC Tera. Grid OSG Supercomputer Sites 19 OGF NCSA NYSGrid Orgs Cal. IT 2 NEON. Discipline Groups
Evolution of CI Users • First Grid Builders • Built their own clusters • Use resources at supercomputer sites • Infrastructure for just their discipline • They provided their own technology support 20
Evolution of CI Users Second Wave Grid Builders • Infrastructure still for their own community • They create their own IT support organization • Their IT organization runs the infrastructure 21
Evolution of CI Users Upcoming Disciplines • Currently planning their CI needs • Looking primarily at their requirements for CI • Are assuming that CI can be obtained from others 22
CI is not just for Researchers The current focus on CI is its use by Researchers. However this is an emerging technology that will be used by all, just as the individual computer and the Internet has become a regular work tool. 23
CI Days Workshops Tera. Grid, Open Science Grid, Internet 2 and EDUCAUSE have come together to try to help better understand the CI picture, and to better coordinate functions and roles in the creation of this infrastructure. One activity started by this group is the “CI Days” held for campuses to assist in their CI planning. This workshop brings together players from the campus, region and nation to share information and plan how to provide CI functions for the campus. The national and regional groups will also learn the campus needs to help better direct the evolution of the services. 24
More Info Russ Hobby rdhobby@internet 2. edu 530 -863 -0513 25

26
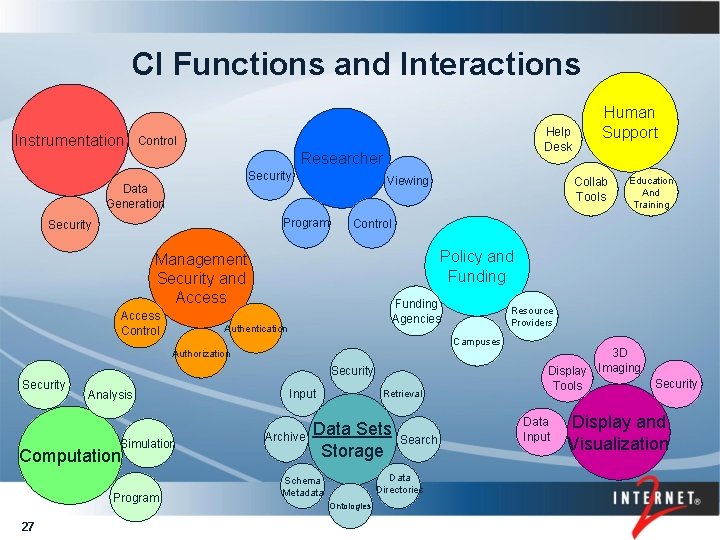
CI Functions and Interactions Instrumentation Help Desk Control Researcher Security Viewing Data Generation Program Security Funding Agencies Authentication Security Simulation Computation Program 27 Resource Providers Campuses Analysis Education And Training Policy and Funding Authorization Security Collab Tools Control Management Security and Access Control Human Support Input Archive Retrieval Data Sets Storage Search Data Directories Schema Metadata Ontologies 3 D Imaging Display Tools Data. Input Security Display and Visualization
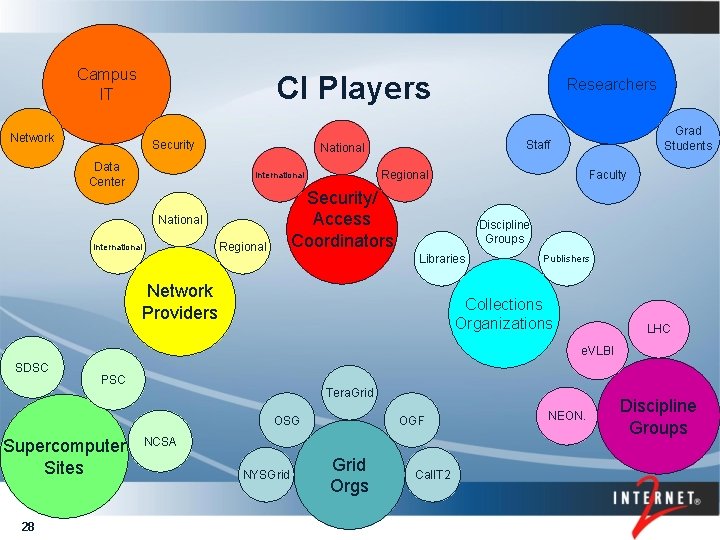
Campus IT CI Players Network Security Data Center Faculty Regional Security/ Access Coordinators National Regional Grad Students Staff National International Researchers Discipline Groups Libraries Network Providers Publishers Collections Organizations LHC e. VLBI SDSC PSC Tera. Grid OSG Supercomputer Sites 28 OGF NCSA NYSGrid Orgs Cal. IT 2 NEON. Discipline Groups
- Slides: 28