Cyber weapons A Reality Alexandra Kulikova Program Coordinator
Cyber weapons: A Reality (? ) Alexandra Kulikova Program Coordinator “Global Internet governance and International information Security” PIR Center 3 -4 June 2015 UNIDIR Eurasia Regional Seminar International Law and State Behaviour in Cyberspace Series Muscat, Oman
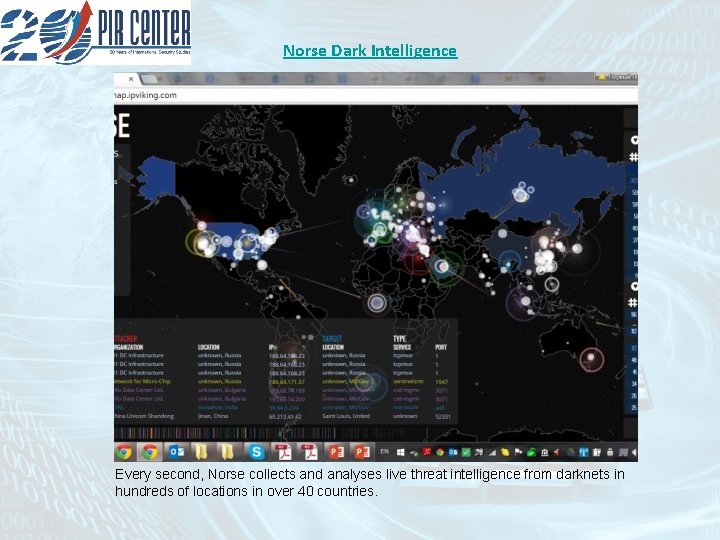
Norse Dark Intelligence Every second, Norse collects and analyses live threat intelligence from darknets in hundreds of locations in over 40 countries.
Terminology: Devil in the metaphors • ICTs vs use of ICTs • Cyber technology ≠ cyber arms • ICTs as implicit weapon “ICTs are dual-use technologies and can be used for both legitimate and malicious purposes. Any ICT device can be the source or the target of misuse. The malicious use of ICTs can be easily concealed and attribution to a specific perpetrator can be difficult, allowing for increasingly sophisticated exploits by actors who often operate with impunity. The global connectivity of ICT networks exacerbates this problem. The combination of global connectivity, vulnerable technologies and anonymity facilitates the use of ICTs for disruptive activities. ” Report of the Group of Governmental Experts on Developments in the Field of Information and Telecommunications in the Context of International Security, General Assembly of the United Nations, A/68/98, 24 June 2013, Paragraph 5
So when does the use of ICTs become the use of cyber weaponry? UN GA resolution 3314 (XXIX) on the Definition of Aggression (14 December 1974) Article I Aggression is the use of armed force by a State against the sovereignty, territorial integrity or political independence of another State, or in any other manner inconsistent with the Charter of the United Nations, as set out in this Definition. Article III The following acts qualify as an act of aggression (non-exhaustive): • • (a) The invasion or attack by the armed forces of a State of the territory of another State, or any military occupation, however temporary, resulting from such invasion or attack, or any annexation by the use of force of the territory of another State or part thereof, (b) Bombardment by the armed forces of a State against the territory of another State or the use of any weapons by a State against the territory of another State; (c) The blockade of the ports or coasts of a State by the armed forces of another State; (d) An attack by the armed forces of a State on the land, sea or air forces, or marine and air fleets of another State; (e) The use of armed forces of one State which are within the territory of another State with the agreement of the receiving State, in contravention of the conditions provided for in the agreement or any extension of their presence in such territory beyond the termination of the agreement; (f) The action of a State in allowing its territory, which it has placed at the disposal of another State, to be used by that other State for perpetrating an act of aggression against a third State; (g) The sending by or on behalf of a State of armed bands, groups, irregulars or mercenaries, which carry out acts of armed force against another State of such gravity as to amount to the acts listed above, or its substantial involvement therein.
Implications for the cyber domain? Tallinn Manual on the International Law Applicable to Cyber Warfare: – “cyber weapons” - cyber means of warfare designed, used or intended to cause either injury or death of people or damage to or destruction of objects - Software, virus, and intrusion device able to disrupt critical infrastructures of other countries (e. g. military defence systems, communications, electric power smart grids, financial systems, air traffic control etc) Cyber operation ( ? ) => Use of force (UN Charter Article 2 (4)) => Armed attack (UN Charter Article 51) => “Whether a cyber operation constitutes an armed attack depends on its scale and effects. ” (Rule 11, 13)
How does it work? - Direct malicious technologies of selective type ( exploiting vulnerabilities, one-off, limited action, no deterrence potential) #Stuxnet - Intrusion with remote operation (data collection through a long-term exploit, modification of the systems functioning, mutative, intelligence + disruption upon necessity) #Red October, Flame, Fanny - Equation Group - Autonomous adaptive and self-upgradable systems. . #Suter
Ambiguities remain Tallinn Manual Rule 11 – Definition of use of force • Cyber operations falling below the use of force threshold are more difficult to characterise as a violation of the principle of non-intervention. The decisive test remains coercion • A cyber operation constitutes a use of force when its scale and effects are comparable to non -cyber operations rising to the level of a use of force - “scale and effects” are to be considered when determining whether particular actions amount to an “armed attack” • Surveillance and espionage and exploitation lacking coercive element do not per se violate the non-intervention principle. Though highly invasive, cyber espionage does not rise to the level of a use of force due to the absence of a direct prohibition in international law on espionage per se • UN Charter offers no criteria by which to determine when an act amounts to a use of force. Cyber operations that involve, or are otherwise analogous to political or economic coercive activities are definitely not prohibited uses of force.
Information weapons? Draft Concept of a UN Convention on International Information Security presented at a meeting of senior international security officials held in Yekaterinburg on September 21 -22, 2011: Article 6 - key measures to prevent armed conflicts in the information space: • • All parties must desisting from the use of force or threats of force against the information space of other countries; Each state must make all possible efforts to prevent the use of its territory or infrastructure for illicit action involving the use of ICT; All parties must refrain from developing and adopting doctrines that could potentially trigger the rise of threats in the information space and the breakout of “information wars” All parties must adopt measures to limit the spread of “information weapons” and technologies of making such weapons. Þ Shanghai Cooperation Organisation Code of Conduct v 1 2011 (China, Russia, Tajikistan and Uzbekistan) v 2 2015 (China, Russia, Tajikistan, and Uzbekistan, Kazakhstan, Kyrgyzstan)
Any chance scale down the cyber race? • 4 th UN GGE on Developments in the Field of Information and Telecommunications in the Context of International Security - Report in June 2015 • SCO Code of Conduct 2015 • US – Russia 2013 cyber deal • Russia – China 2015 cyber deal • Private initiatives: Microsoft’s 6 Norms of State behaviour in cyberspace • USCYBERCOM new strategy vs Secretary of State John Kerry’s speech at the Seoul University on 18 May 2015 – 5 norms of state behaviour in cyberspace BUT
Deterrence? What deterrence? • Cyber-cyber vs cyber-kinetic • Defence vs offence • Non-state actors? • Capacity building vs cyber militarisation • Hybrid warfare
Thank you! Alexandra Kulikova Program Coordinator “Global Internet governance and International information Security” PIR Center kulikova@percenter. org net. pircenter. org
- Slides: 11