Cyber Threat Trends for 2018 SSA Elvis Chan
Cyber Threat Trends for 2018 SSA Elvis Chan FBI San Francisco UNCLASSIFIED
Legal Disclaimer v The views and opinions of the presenter are personal to the presenter and do not necessarily reflect the official policy or position of any agency of the U. S. Government. v This presentation should not be considered or construed as legal advice on any individual matter or circumstance. v The contents of this document are intended for general information purposes only and may not be quoted or referred to in any other presentation, publication or proceeding without the prior written consent of the FBI. UNCLASSIFIED 2

The Cyber Threat “This threat is now coming at us from all sides. We’re worried—at the FBI and with our partners—about a wider range of threat actors, from multi-national cyber syndicates and insider threats to hacktivists. ” FBI Director Christopher Wray March 7, 2018 Boston Conference on Cybersecurity UNCLASSIFIED

Cyber Threat Continuum UNCLASSIFIED 4
The Top Cyber Threats for 2018 v. Business Email Compromise (BEC) v. Ransomware v. Advanced Persistent Threat (APT) UNCLASSIFIED
Business Email Compromise (BEC) v “Bank robbers don't rob banks anymore…they hide behind their computer screens and cover their digital tracks. ” v In February 2015, Scoular Co, an Omaha-based company, lost $17. 2 Million. v $360 million losses in U. S. for 2016. v $675 million losses in U. S. for 2017 UNCLASSIFIED

BEC GLOBAL IMPACT BEC Global Statistics Time frame October 2013 to May 2018 Victims: 78, 617 Exposed Loss: $12, 536, 948, 299 UNCLASSIFIED
International Financial Fraud Kill Chain United States Model The Financial Fraud Kill Chain (FFKC) is a partnership between law enforcement and financial entities whose purpose is to recover fraudulent funds wired by victims of any crime type. FFKC requests are coordinated through the Financial Crimes Enforcement Network (Fin. CEN) Rapid Response Team and law enforcement entities. UNCLASSIFIED
Financial Fraud Kill Chain Victims encouraged to notify the following as soon as possible: 1. Financial Institution 2. US Federal Law Enforcement 3. File complaint with ic 3. gov § IC 3 complaints are vetted 24/7 to identify FFKC qualified victims § Investigative analysis 1 3 2 UNCLASSIFIED
Financial Fraud Kill Chain Between 2014 -May 2018, internationally over 331 million dollars recovered for victims Between February – June 2018, domestically 100 million dollars recovered for victims UNCLASSIFIED
Ransomware v Ransomware has become a significant threat to U. S. businesses and individuals. v Perpetrators use ransomware to encrypt a user’s important files and documents, making them unreadable, until a ransom is paid. v Most of the newer ransomware variants collect payment solely in bitcoin. v Approximately $2. 3 million in paid ransom in the U. S. for 2017. UNCLASSIFIED
Advanced Persistent Threat Who is doing it? v. China v. North Korea v. Iran v. Russia Foreign Spies Stealing US Economic Secrets in Cyberspace Office of the Director of National Intelligence Published: October 2011 http: //www. dni. gov/reports/20111103_report_fecie. pdf UNCLASSIFIED
APT– What? What is going on? v State sponsored adversaries are pursuing sensitive U. S. information and proprietary technologies. v U. S. company networks house this information and may be vulnerable to exploitation. UNCLASSIFIED

APT – North Korea UNCLASSIFIED
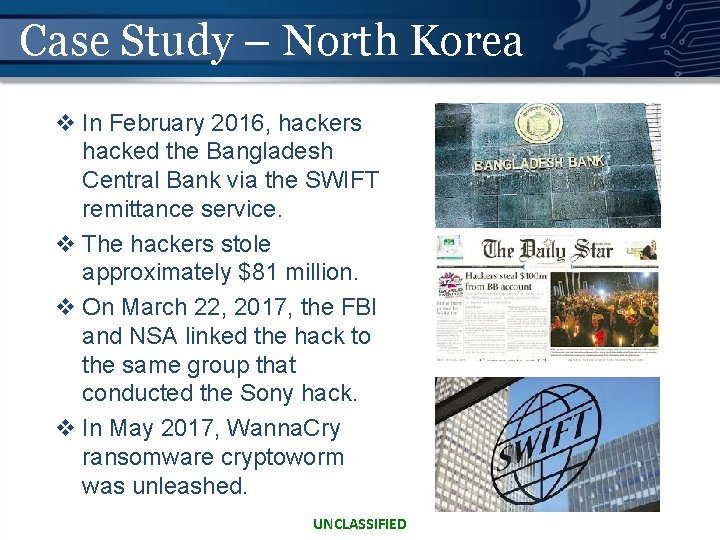
Case Study – North Korea v In February 2016, hackers hacked the Bangladesh Central Bank via the SWIFT remittance service. v The hackers stole approximately $81 million. v On March 22, 2017, the FBI and NSA linked the hack to the same group that conducted the Sony hack. v In May 2017, Wanna. Cry ransomware cryptoworm was unleashed. UNCLASSIFIED
APT - Russia UNCLASSIFIED
Case Study - Russia v From June – November 2016, Democratic National Committee emails were leaked on Wikileaks. v On October 7, 2016, DHS and ODNI stated the DNC breach and leaks were an attempt to interfere with the U. S. Presidential Election. v On December 29, 2016, FBI and DHS released an unclassified report, issued sanctions, and expelled Russian diplomats. v On January 6, 2017, the USIC released another unclassified report concluding the Russian Government tried to help Trump win the election. UNCLASSIFIED

Case Study #10 - Russia v In May 2017, Mueller was appointed by Deputy Attorney General Rod Rosenstein as special counsel overseeing an ongoing investigation into Russian interference in the 2016 U. S. presidential election and related matters, including any links between the Russian government and Donald Trump's campaign. UNCLASSIFIED

Case Study - Russia v On February 16, 2018, special counsel Robert Mueller's team announced it had filed an indictment of 13 Russian nationals and three Russian organizations. v On June 28, 2018, new sanctions were levied against Russia. UNCLASSIFIED
How Are They Doing This? UNCLASSIFIED 20
Social Engineering Only amateurs attack machines; professionals target people UNCLASSIFIED 21
Why Does Social Engineering Work? “The user’s going to pick dancing pigs over security every time” Bruce Schneier UNCLASSIFIED 22
Social Engineering and Social Media v Non-technical kind of intrusion that relies heavily on human interaction and often involves tricking other people to break normal security procedures v ALMOST ALL businesses and executives have web presence v Results of Social Engineering – 15% of Americans use social media to report when they have left the home* *http: //homesecurityblog. protectamerica. com/category/home-security-information/page/3/ UNCLASSIFIED 23
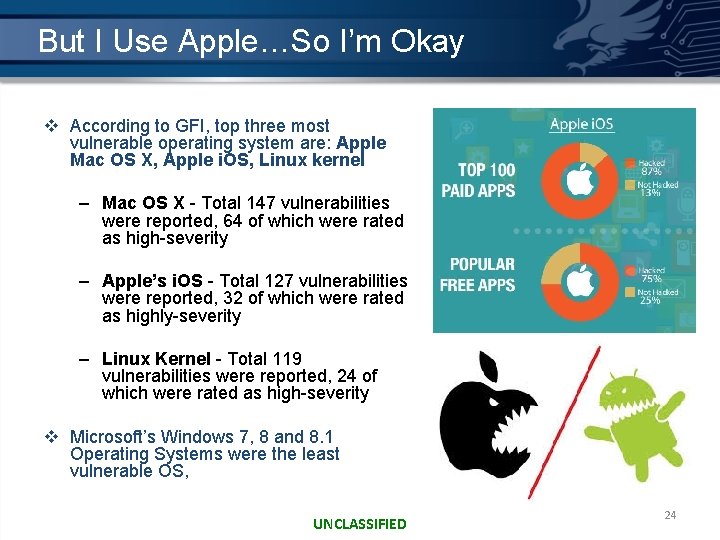
But I Use Apple…So I’m Okay v According to GFI, top three most vulnerable operating system are: Apple Mac OS X, Apple i. OS, Linux kernel – Mac OS X - Total 147 vulnerabilities were reported, 64 of which were rated as high-severity – Apple’s i. OS - Total 127 vulnerabilities were reported, 32 of which were rated as highly-severity – Linux Kernel - Total 119 vulnerabilities were reported, 24 of which were rated as high-severity v Microsoft’s Windows 7, 8 and 8. 1 Operating Systems were the least vulnerable OS, UNCLASSIFIED 24
Guidance - Prevention Our guidance for private industry: v Establish Security Policies…then prioritize v Support Established Security Policies v Monitor and Analyze Network Traffic v Assess Vulnerabilities v Configure Systems for Security (may mean $$) v Support/Provide Training for Employees UNCLASSIFIED 25
Guidance – Incident Response Our guidance for private industry after an incident: v Follow your emergency plan and start protecting your data. v Call the local FBI field office. v Preserve original media as evidence (if not, ask if they can make a forensic image). v Request your IT specialists conduct analysis from a copy instead of the original (if possible). v Gather all pertinent log files (DNS, Firewall, Proxy, System Event Logs). v Contact ISP for additional logs and possibly provide filtering. v Conduct a damage assessment (including damage valuation). UNCLASSIFIED 26
What the FBI does not do v Take over your systems. v Repair your systems. v Share proprietary information with competitors. v Provide investigation-related information to the media or your shareholders. UNCLASSIFIED 27
What can the FBI do for you? v Investigate – National and global reach – Combined technical skills and investigative experience – Long-term commitment of resources v Forensics – Silicon Valley Regional Computer Forensics Laboratory (SVRCFL) – Keeps options open for your company v Analyze Patterns and Links v Bring national security concerns to the U. S. Intelligence Community UNCLASSIFIED 28

Questions? UNCLASSIFIED
- Slides: 29