Cyber Security You Expect It You Need It
Cyber Security You Expect It You Need It Terry Pobst-Martin Chief Information Security Officer State of Idaho, Office of the Chief Information Officer
Securing Digital Government Our Vulnerability and the Real Threats Cyber Security – Trends and Issues What can we do?
The U. S. Government is Vulnerable “Washington-- Computer spies have broken into the Pentagon's $300 billion Joint Strike Fighter project”. . . “suspected to be Chinese Hackers. ” Apr 22, 2009 – Wall Street Journal • “Report: Chinese hack into White House network” Nov 4, 2008 - ZDNet Posted by Andrew Nusca
The U. S. Government is Vulnerable Huge new effort to protect Department of Defense Also plan to help protect citizens in the future Can no longer rely on industry efforts to counter cyber threats Pentagon spent < $100 M in 6 months responding to: cyber attacks related problems
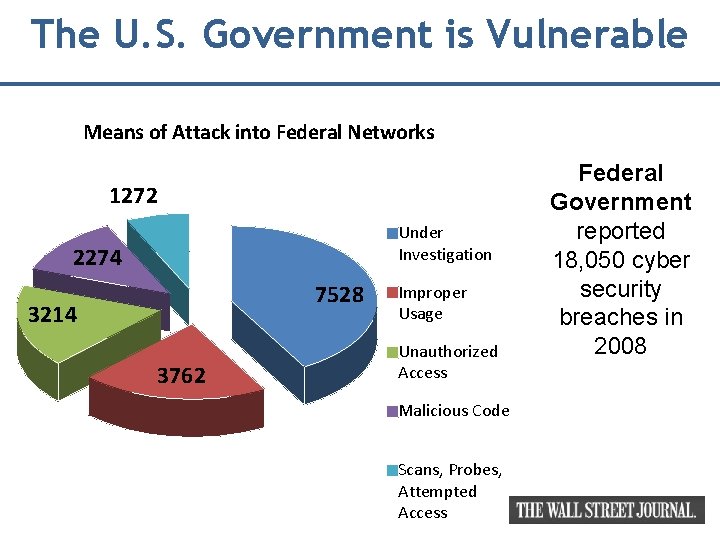
The U. S. Government is Vulnerable Means of Attack into Federal Networks 1272 Under Investigation 2274 7528 3214 3762 Improper Usage Unauthorized Access Malicious Code Scans, Probes, Attempted Access Federal Government reported 18, 050 cyber security breaches in 2008

The U. S. Government is Responding U. S. Cyber Command Operational since October 1
The U. S. Infrastructure is Vulnerable “Cyberspies penetrate electrical grid” 8 April 2009, Reuters Electrical grid network has “Backdoors” to let bad guys in whenever they choose

The U. S. Government is Vulnerable Cyber threats are now considered "Cybersecurity is the soft underbelly of this country. " Weapons of Mass Destruction! INL test Electrical generators are at risk Former National Intelligence Director Mike Mc. Connell Secretary of State Hilary Clinton
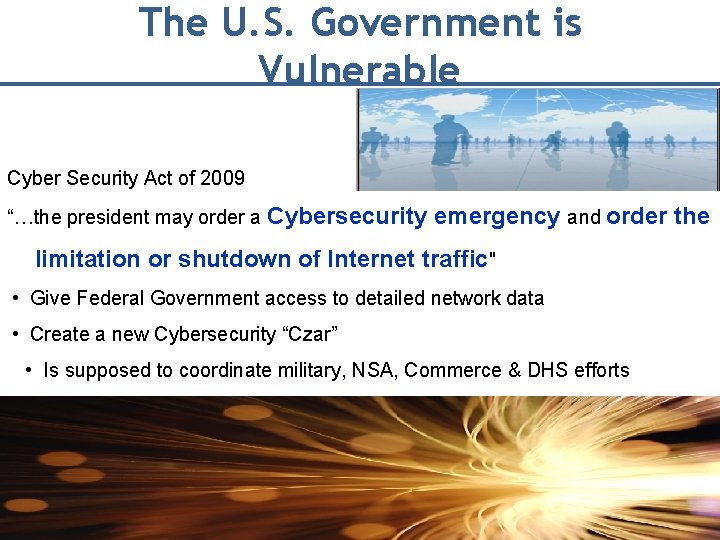
The U. S. Government is Vulnerable Cyber Security Act of 2009 “…the president may order a Cybersecurity emergency and order the limitation or shutdown of Internet traffic" • Give Federal Government access to detailed network data • Create a new Cybersecurity “Czar” • Is supposed to coordinate military, NSA, Commerce & DHS efforts
Idaho Government is Vulnerable A Hacker’s View of the State of Idaho: • Target • Government networks are a valid target • Corporations are valid targets • Individuals are a target • Identity and privacy information = big target
The Overarching Threat in Idaho Overarching Security Issues: Electrical grid Cyber attacks • Won’t stop the wind blowing • Can’t stop the water flowing • Can stop the power to • Your house • Your workplace • Stoplights. . .

The Daily Threat Growing security trends: • Huge increase in spam (Phishing, e-cards, etc. ) • New Threats: Vishing, Pod-Slurping, Thumb-sucking, more • Development of wireless hacking & mobile device viruses • Increase in video sharing exploits (PC or mobile) • Significant Increase in “Drive-by” malicious-ware websites • Increase in “Bots” & rootkits; rootkits hard to find or stop
U of I Website
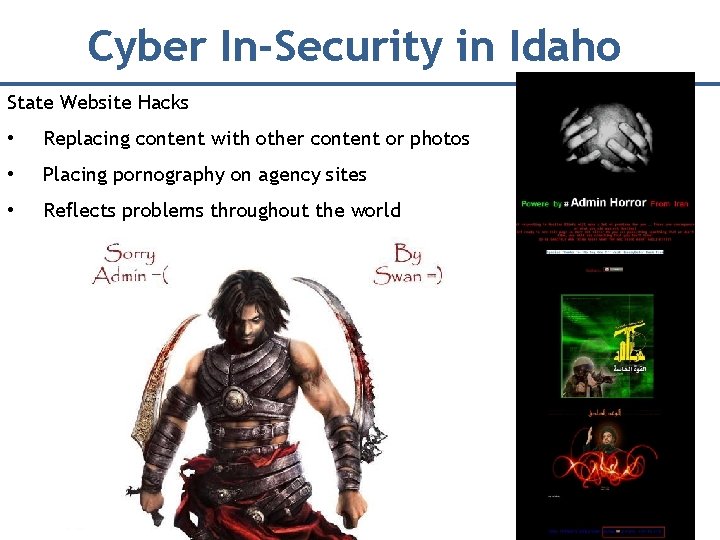
Cyber In-Security in Idaho State Website Hacks • Replacing content with other content or photos • Placing pornography on agency sites • Reflects problems throughout the world
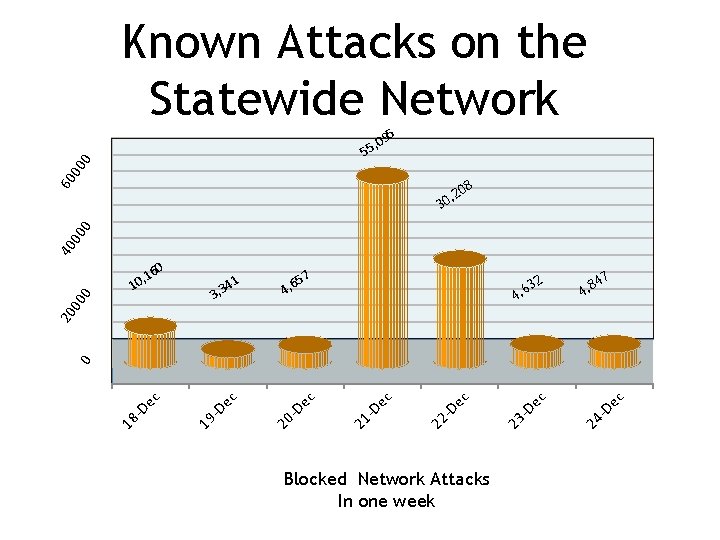
Known Attacks on the Statewide Network 5 9 5, 0 60 00 0 5 40 00 0 08 2 , 30 1 4 3, 3 57 4, 6 3 4, 6 2 4 4, 8 7 Blocked Network Attacks In one week ec -D 24 ec -D 23 ec -D 22 ec -D 21 ec -D 20 ec -D 19 18 -D ec 0 20 00 0 60 , 1 10
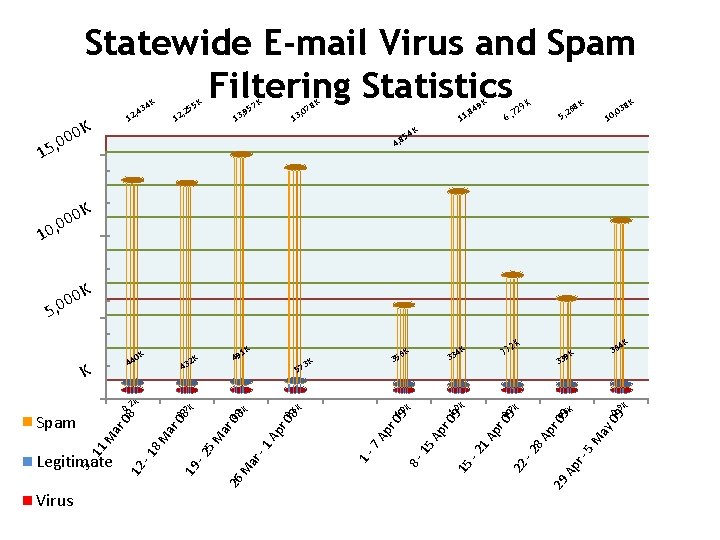
Statewide E-mail Virus and Spam Filtering Statistics K 34 , 4 12 0 K 0 0 5, K 57 K 55 , 2 12 8 K , 07 3 1 , 9 13 K 49 9 K K 5, 2 K 38 68 2 6, 7 , 8 11 , 0 10 K 54 4, 8 1 K 00 0 , 0 1 0 K 0 5, 0 4 K K 0. 9 09 K ay pr 5 M r. Ap 29 pr 1 A -2 15 09 0. 6 09 9 K 0. 7 r 0 Ap 15 pr 3 8 A K 1. 0 36 K 39 -2 K 1. 0 2 K 33 22 4 K 33 8 - ar M 26 7 A Ap r 0 8 08 ar 5 M -2 6 K 35 09 K 0. 6 K 0. 9 19 12 -1 8 M ar ar M 11 5 - Legitimate K 08 08 0. 7 3 K 57 1 - 43 K 0. 2 Spam Virus 2 K 44 K K 1 49 -1 0 K
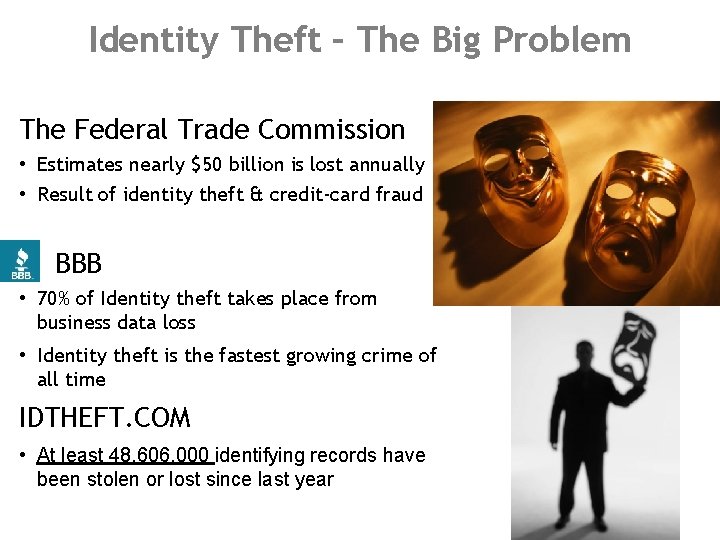
Identity Theft – The Big Problem The Federal Trade Commission • Estimates nearly $50 billion is lost annually • Result of identity theft & credit-card fraud BBB • 70% of Identity theft takes place from business data loss • Identity theft is the fastest growing crime of all time IDTHEFT. COM • At least 48, 606, 000 identifying records have been stolen or lost since last year
Identity Theft – Sophisticated? • “…laptop stolen from unlocked truck…” • “…former office manager indicted for theft of records…” • “…hard drives missing…” • “…donated computer contained information. ” • “A hacker breaks in…” • “…a data breach occurred…” • “…records dumped in garbage…” • “…employee loses a CD with data…” • “…a customer just walked in and left with a stack of papers…”
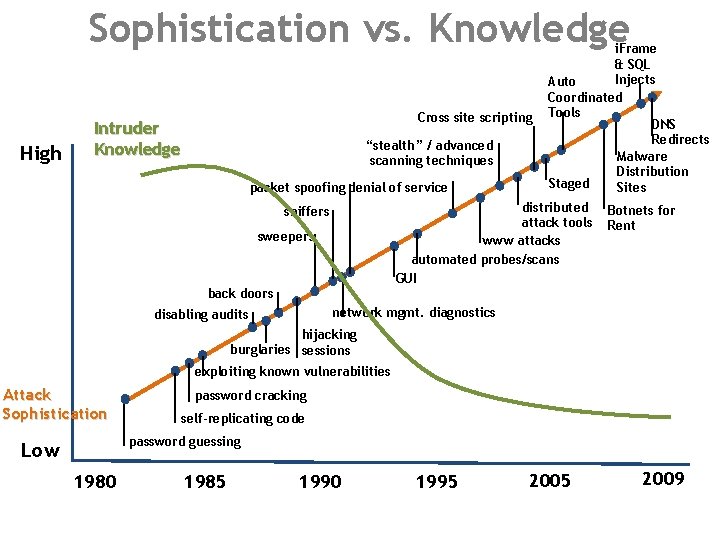
Sophistication vs. Knowledge High Cross site scripting Intruder Knowledge “stealth” / advanced scanning techniques packet spoofing denial of service i. Frame & SQL Injects Auto Coordinated Tools DNS Redirects Malware Distribution Staged Sites distributed attack tools www attacks automated probes/scans GUI sniffers sweepers Botnets for Rent back doors network mgmt. diagnostics disabling audits hijacking burglaries sessions exploiting known vulnerabilities Attack Sophistication password cracking self-replicating code password guessing Low 1980 1985 1990 1995 2009
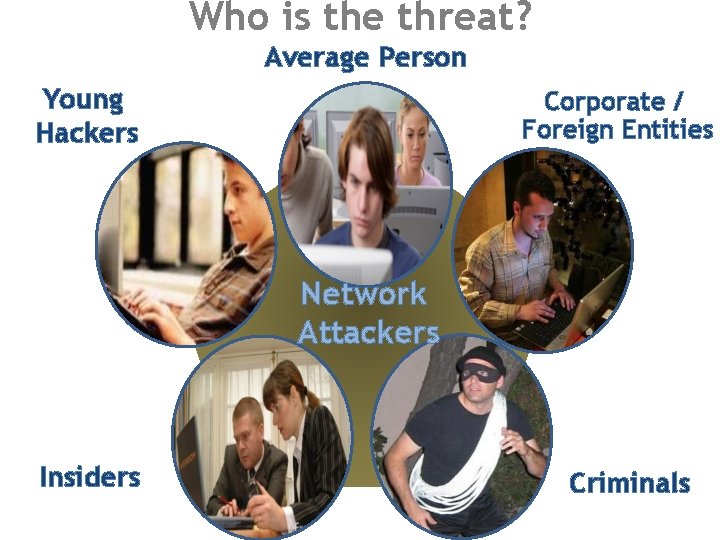
Who is the threat? Average Person Young Hackers Corporate / Foreign Entities Network Attackers Insiders Criminals
Average Person = Big Risk Average people… make mistakes • Visit a site with poor security • Obvious (e. g. , pornography) • Not obvious (e. g. , My. Space, Facebook) • Even trusted sites – thousands every day • Download from the Internet

Average Person = Big Risk Average people… make mistakes • Install potentially dangerous software • Freeware / Shareware • Unchecked software • Games • Toolbars (e. g. , Google Toolbar) • Rights & access must be minimized
Average Laptop User Cisco Study: Laptop users bring threats into networks • 56% believe Internet is now “safer” • Less “destructive” viruses • More security products • Limited awareness
Young Hackers “Script Kiddies” or Hacker intraining • Use tools developed by real Hackers • Find excitement in breaking-in • “Bragging Rights” • Often purposely leave evidence • Build a rep • Rarely want long term exploitation
Insiders – Who Are They? Anyone could be an insider • Studies show insiders bring huge losses • Victims at HUGE risk • 12 times more likely hit by fraud
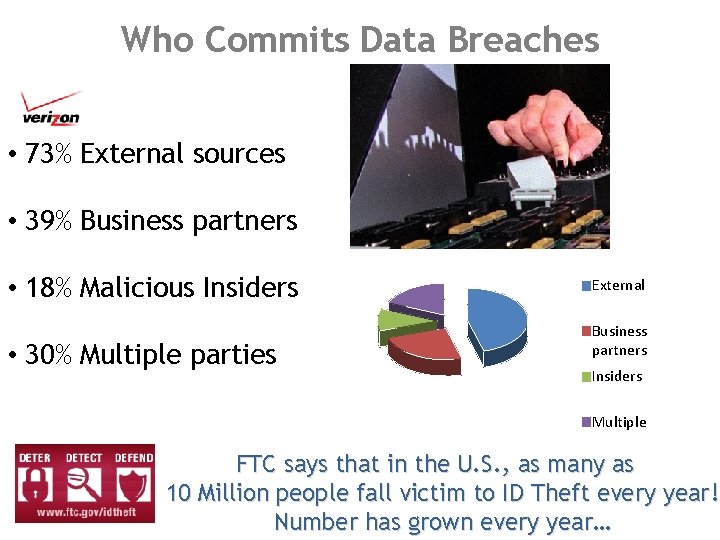
Who Commits Data Breaches • 73% External sources • 39% Business partners • 18% Malicious Insiders • 30% Multiple parties External Business partners Insiders Multiple FTC says that in the U. S. , as many as 10 Million people fall victim to ID Theft every year! Number has grown every year…
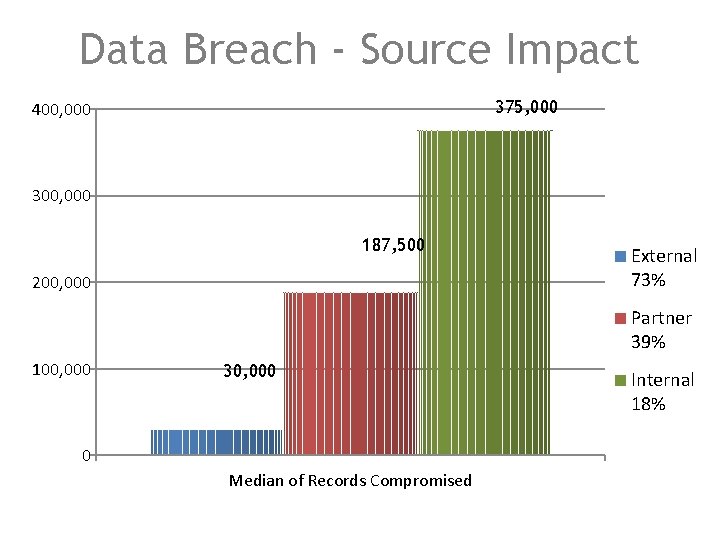
Data Breach - Source Impact 375, 000 400, 000 300, 000 187, 500 200, 000 External 73% Partner 39% 100, 000 30, 000 0 Median of Records Compromised Internal 18%

Foreign / Corporate Threat Grows If there’s a profit or edge to gain • Foreign governments • Active attacks • Network “backdoors” • Use daily or hold for hostilities

Foreign / Corporate Threat Grows If there’s a profit or edge to gain • Corporations • Information is power • Corporate intelligence activities growing • Is it ethical in the market place?
Criminals Using a Mouse as Weapon Developing new viruses all the time • Created mostly by criminals • A recent popular one is: • JSRedir-R Trojan or “Gumblar” • Infecting a new webpage every 4. 5 seconds – legitimate sites • Loads without knowledge Refining Social Engineering • “Twitterpornnames” • Facebook and many other examples
The Prime Motivator Grows Bigger Global cybercrime is the biggest profit maker for criminals • Surpassed drug trafficking • Is not as dangerous as dealing drugs or robbing banks, etc. • True hackers selling services to non-technical criminals • Expertise is growing rapidly • Money gets bigger every month
The Real Problem: Software • Software has vulnerabilities • We need software • To do our jobs • To entertain ourselves • To make life easier • Over 90% of attacks are on known vulnerabilities • Patches are already out • “Zero Day” exploits always a possibility
Cyber Security – Trends and Issues
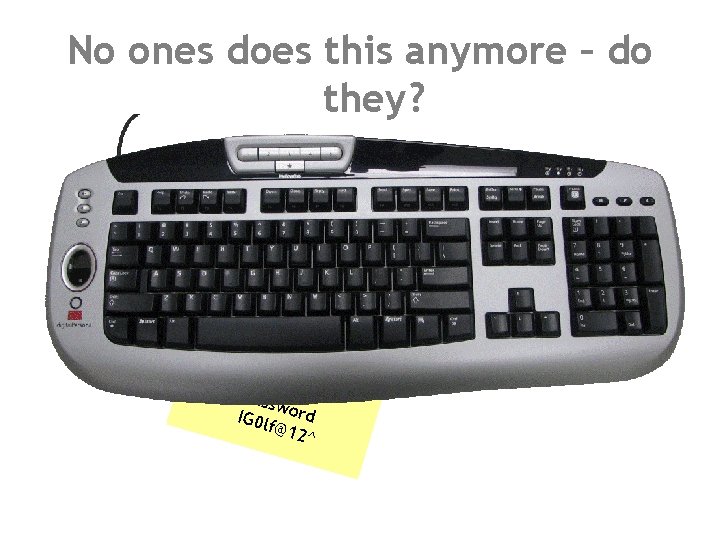
No ones does this anymore – do they? Pass w IG 0 l ord f@12 ^
Good Password Discipline • Password security is critical! • Ensures only you can access your computer • And the network behind it • Use strong passwords always • You will be attacked at the point of the weakest link
Good Password Discipline • NEVER give your network password to anyone else! • Don’t write it down! • Use as long a password as you can and ensure it has – – Upper and Lower case Letters Special Characters and Numbers At least 8 characters Passphrases are very secure
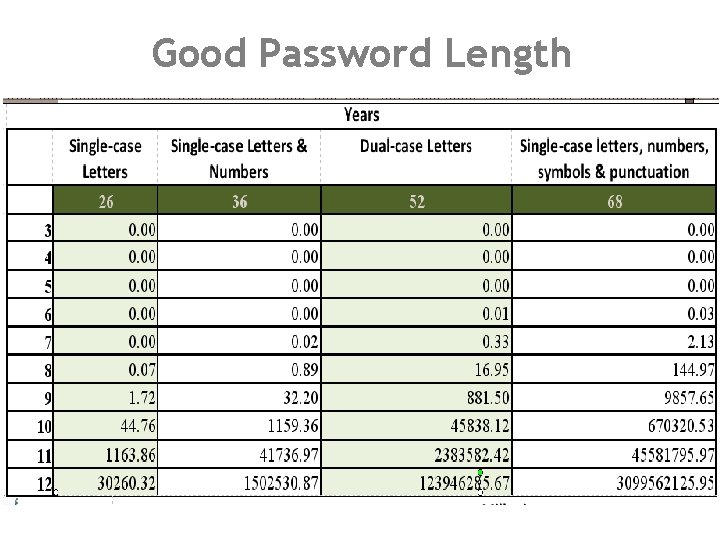
Good Password Length
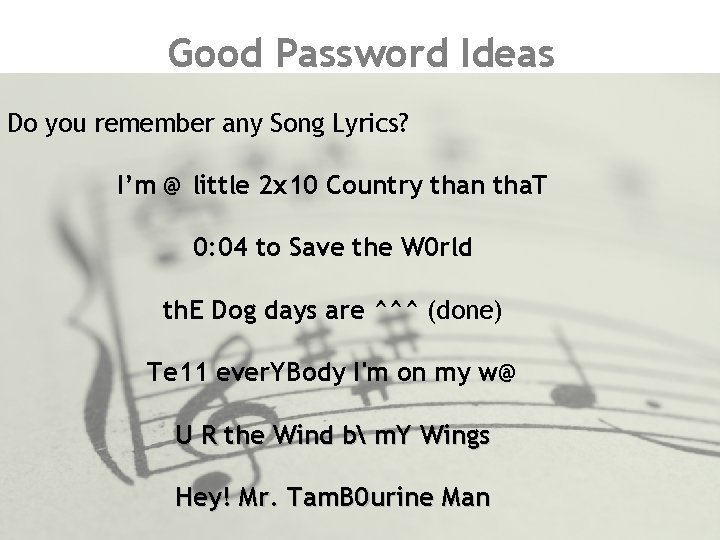
Good Password Ideas Do you remember any Song Lyrics? I’m @ little 2 x 10 Country than tha. T 0: 04 to Save the W 0 rld th. E Dog days are ^^^ (done) Te 11 ever. YBody I'm on my w@ U R the Wind b m. Y Wings Hey! Mr. Tam. B 0 urine Man

Good Password Ideas Do you remember Quotes, Poems, Biblical Phrases? Ask what U can do 4 Ur country! To. Errishuman, 2_4 givedivine Early 2 bed&Early 2 ris. E How do I love thee? Let me 1234 the ways! Once upon a 12: 00 AM dreary 4 God so loved The world! I will fear O evil, 4 thou art with me!
Most Overlooked Aspect – Lock Others Out • • Physically secure your critical systems Screen-lock your system when away from your computer Ensure work areas are secure Be aware of people who don’t belong in the work area
Phishing Threat is not Going Away • Despite public awareness • Scammers are Social Engineers • E-mails look more real • Reeling in the victims • Large amounts of money from small percentage of people
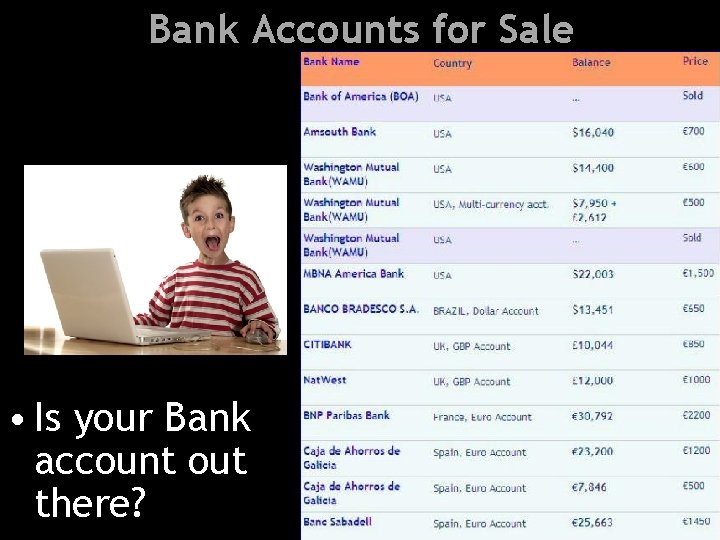
Bank Accounts for Sale • Is your Bank account out there?

Vishing is a “New” Threat Vishing You can trust me • Using Voice over IP (Vo. IP) • Gain access data • Private, personal and financial information • Likely to trust real person • Caller ID spoofing builds trust You can trust me
Spyware is Ever More Pervasive • Spyware infects >80% desktops • P 2 P software can come with Spyware • Now too prevalent and insidious • Your Anti-virus will not find it all • Precursor to Trojans and/or Botnet • Malware, all types, increased 32 K variants in 2004 to >30 Mil in 2009 Now, almost too many to track (1/8 sec)
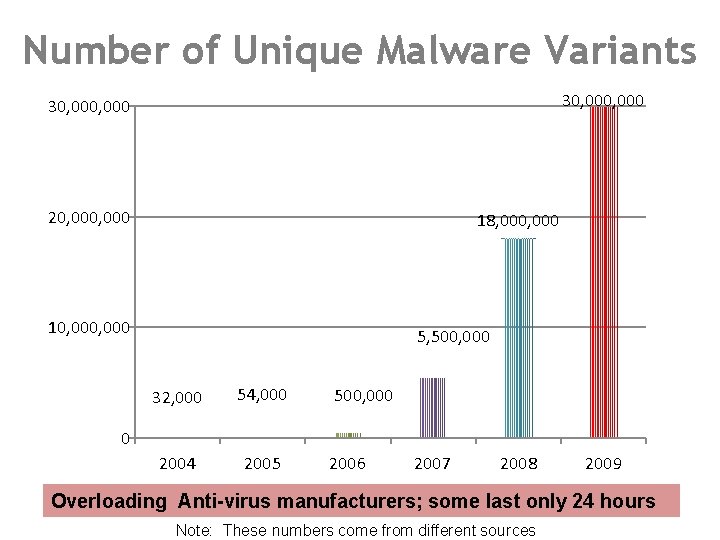
Number of Unique Malware Variants 30, 000, 000 20, 000 18, 000 10, 000 5, 500, 000 32, 000 54, 000 2004 2005 500, 000 0 2006 2007 2008 2009 Overloading Anti-virus manufacturers; some last only 24 hours Note: These numbers come from different sources
Watch Out for Fake AV Rogue anti-virus/spyware programs • Often generate more "alerts" than reputable software • May bombard you with pop-ups, even when not online • Use high-pressure sales to convince you to buy RIGHT NOW! • Other signs of infection include: • new desktop icons • new wallpaper • default homepage redirected to another site
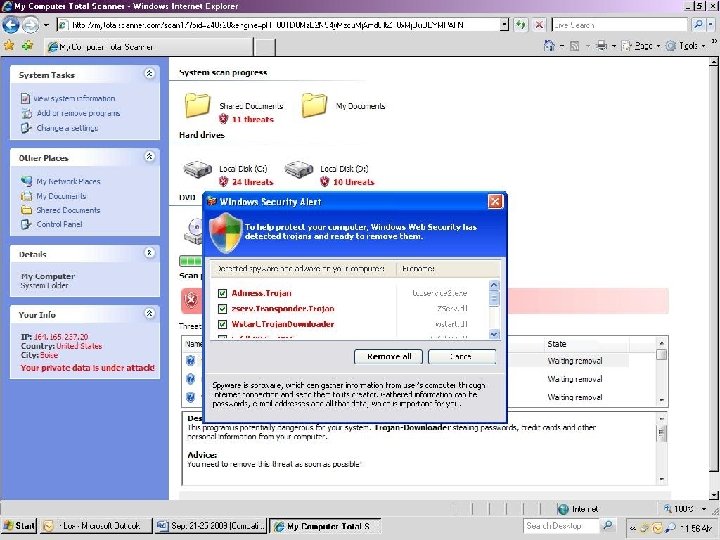
Watch Out for Fake AV
Drive-by Malware Surfing the web is becoming a more treacherous adventure Safe website? Infected Websites grew 300% in 2008
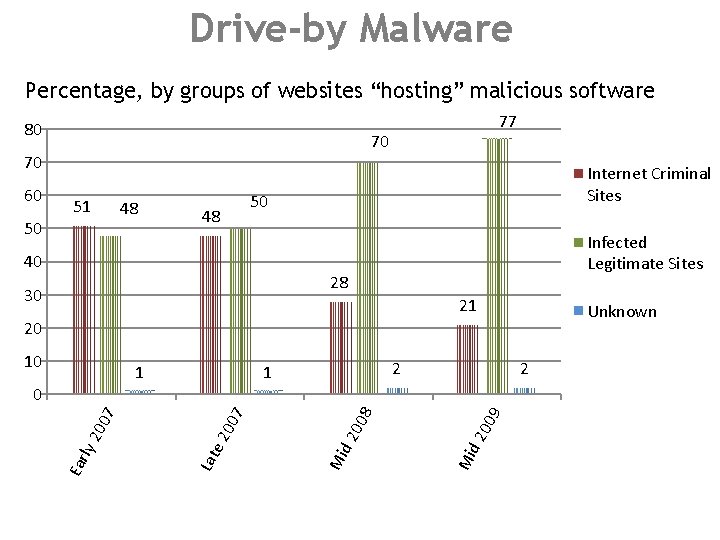
Drive-by Malware Percentage, by groups of websites “hosting” malicious software 80 70 70 60 77 51 50 48 48 Internet Criminal Sites 50 40 Infected Legitimate Sites 28 30 21 Unknown 20 10 1 2 00 9 d 2 Mi 00 8 d 2 Mi 07 20 Lat e Ear l y 2 00 7 0
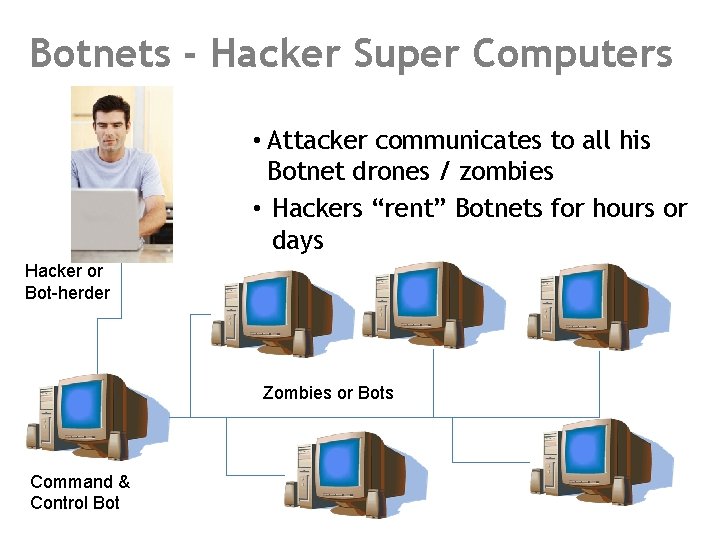
Botnets - Hacker Super Computers • Attacker communicates to all his Botnet drones / zombies • Hackers “rent” Botnets for hours or days Hacker or Bot-herder Zombies or Bots Command & Control Bot

Botnets – For Rent
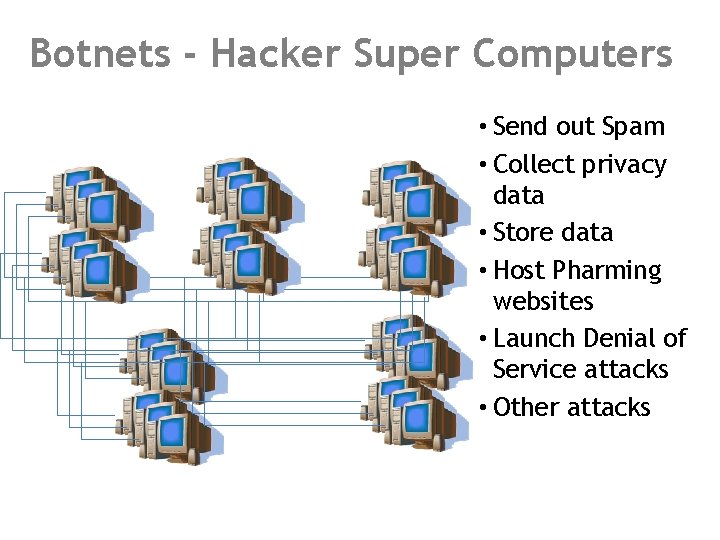
Botnets - Hacker Super Computers • Send out Spam • Collect privacy data • Store data • Host Pharming websites • Launch Denial of Service attacks • Other attacks

Pod-Slurping and Thumb-Sucking “Autorun” should be disabled to stop this…

USB Powered Devices Free malicious software with the purchase of any digital frame? ? Or other USB powered devices
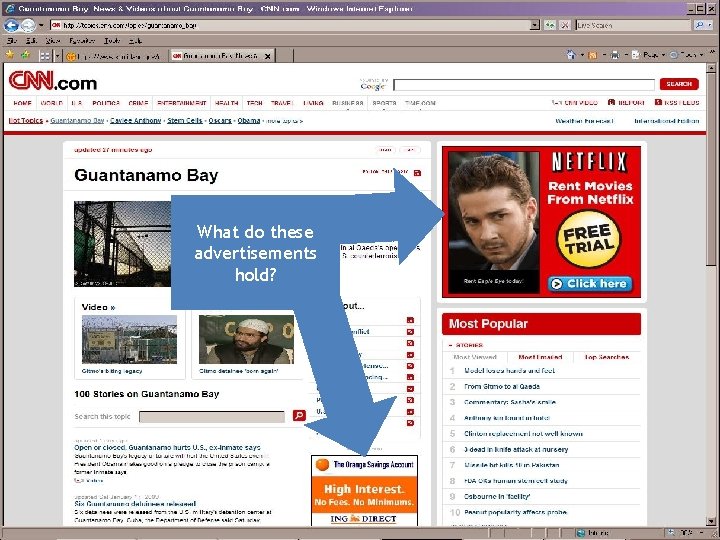
What do these advertisements hold?
What can you do?

We are the Keys to Security Step 1: Understand that computer user involvement is key to successful network / cyber security
We are the Keys to Security Step 1 a: Don’t Be Scared

IT Must Put the Security in Place Step 2 – Manage Risk • Rapidly changing landscape for IT solutions • Constantly changing IT security environment • Security tools are growing – capability, complexity, cost • IT budgets won’t increase as quickly as demand
Step 2 a - Determine Risk Analyze the security environment – focus on the risk • What information / resources are you protecting • What are threats to your information / assets • What is the risk to the organization if information / asset is • Lost • Stolen • Changed
Step 2 b – Security Plan • Develop a security plan to manage your risk • Develop a security budget based on the security plan • Assign the right people manage and run with the plan
Individual Tools for Security – at Work at work Step 3: Take security seriously wo • • • Use strong passwords Lock your workstations Use care with e-mails Do not download from the Internet Do not install unchecked programs – rely on IT Be aware of your Anti-Virus – is it running? Laptop Firewalls should be on if away from the office Make backups of important files and folders Use a file encryption process Ensure Security is part of all Business and IT Plans
Individual Tools for Security – at Home Step 4: Take security seriously at home • Install / Use Anti-Virus & Spyware programs • Install / Use a Firewall program • Keep system patched – all your programs • Use care when reading e-mail • Make backups of important files and folders • Use strong passwords (different ones for different sites) • Use care when downloading and installing • Consider using a file encryption program
Reassess Step 5: Assess success of security procedures: • Are risks mitigated? . . reduced? • Modify plan when necessary • Overcome disappointment; security can’t stop all attacks • Experts are no longer saying “if” but “when” Good Security can make you happy
Questions Terry Pobst-Martin terry. pobst-martin@cio. idaho. gov 332 -1851
- Slides: 66