Cyber Security Preparedness for Hotels Cyber Attack Prevention
Cyber Security Preparedness for Hotels Cyber Attack Prevention & Mitigation Strategies
Matthew J. Bambrick, CBCP CHS-IV Sr. Information Security Engineer Confidential: This presentation contains confidential, proprietary information and trade secrets of Best Western International, Inc. (“Best Western”). It is intended for use solely by Best Western and its Members, Affiliate Organizations and Master Licensees. This presentation and its content may not be shared with or disclosed to any non-Best Western affiliated third-party. Initiatives described may be amended in Best Western’s sole discretion and may be implemented in whole, in party, as revised, or not at all.

About Best Western Hotels & Resorts Award winning global family of hotels in over 100 countries 11 unique hotel brand offerings Over 70 years of Hospitality Ranked #1 by Business Travel News in upper-mid-price hotel brands in 2017 for the 4 th consecutive year Top Ranked Guest Loyalty Program for Five Consecutive Years - U. S. News & World Report Top Guest Loyalty Program - Loyalty 360 Awards
Agenda Hotel Cyber Security Vulnerabilities Overview Cyber Security Breach Prevention Tips Cyber Security Breach Response Tips Cyber Liability Insurance Useful advice Resources Q&A
Ground Rules Welcome! Please Mute/Silence Phones Ask questions Share and Collaborate Let’s learn and have fun!
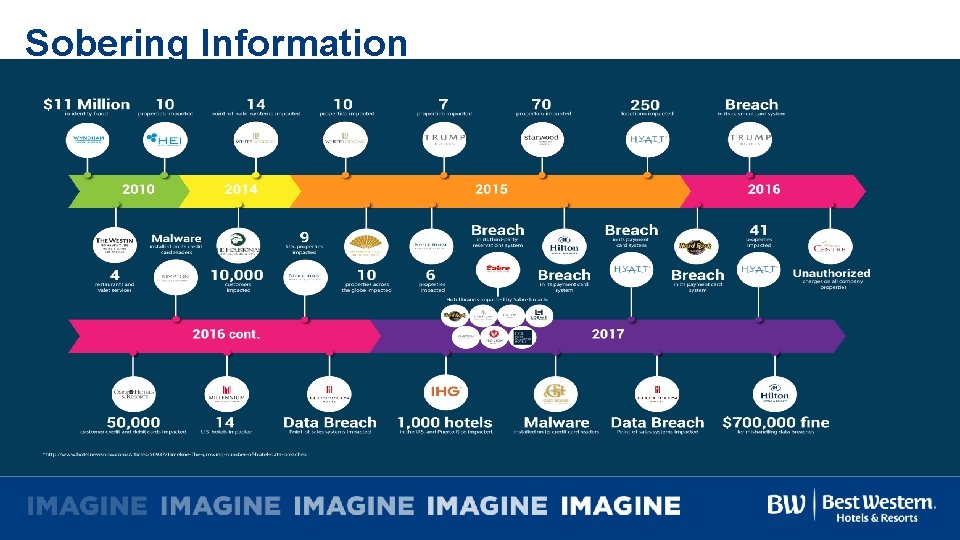
Sobering Information

Major Breaches in 2017

Putting it in Perspective - Hyatt Hotels Breached twice in 2 years 2015 & 2017 2015 Breach impacted 250 properties in 50 countries 2017 Breach impacted 41 properties in 11 countries Is your property ready?
Putting it in Perspective - Hilton Hotels Breach $700, 000 Settlement reached with NY & VT Two separate data breaches exposed more than 360, 000 credit card numbers – Feb 2015 credit-card-targeting malware potentially exposed cardholder data between Nov. 18 and Dec. 5, 2014 – July 2015 - a breach through an intrusion system. Investigation found payment card data was potentially exposed between April 21, 2015 and July 27, 2015, and that attackers rounded up 363, 952 credit card numbers for removal. NY state law - the disclosure must be made in the "most expedient time possible and without unreasonable delay” Hilton didn't provide notice until Nov. 24, 2015, the investigation found
Cyber Security Vulnerabilities

Where Can Things Go Wrong Front Desk Computers • Unlocked PC’s • Weak Passwords • AV/Patching • USB Ports not disabled • Malware • Ransomware • • • POS Devices Malware Skimming Chip/Pin/Swipe Configuration errors Default Passwords PMS Servers • Vulnerabilities • OS Updates • AV/Patching Human/Social • AV Updates Engineering • “Vendor “Calls • System Patching • Vulnerabilities • Phishing • Human Error • Lack of training and awareness
Data Breach Prevention End user training on Security Awareness including – Phishing emails – Social Engineering – Vendor Management & Maintenance – How to report A comprehensive patch management plan Develop a response plan and test (PCI Requirement 12. 10) Antivirus systems up to date (PCI Requirement 5) Perform regular backups Shred/Delete unnecessary data
Data Breach Prevention Manage strong passwords – Change every 90 days (PCI Requirement 8. 2. 4) – Implement 10+ characters (include numbers, upper & lower case, and symbols – Change vendor default passwords (PCI Requirement 2) Close contact with Merchant bank Law enforcement liaisons Treat all data as if it were your own!
Computing Best Practices – “Top 10” Use strong passwords Shut down/Log off computers when unattended Minimize sensitive information storage Password protect all devices Beware of scams Don’t install unknown or unsolicited Secure computers at all times programs/applications Computers are protected with Secure work area before – Anti virus – Patches and Updates are applied leaving unattended Make back up copies

Cyber Security Breach Response

Cyber Security Breach Response Report to Property Help desk Disconnect Affected Computer (Prevents spreading) Document all actions taken Notify ownership Contact Cyber liability insurance carrier Notify legal counsel Password protect all devices Keep Property ownership updated Determine additional stakeholders as needed
Cyber Security Response – Preparedness Plan Create response team and documented plan Define team roles and responsibilities Establish clear actions items and checklists- Keep parties focused Know your Law Enforcement contacts Document & examine your third party vendor security protocols Address and close potential gaps Outline steps necessary in first 72 hours Keep Property ownership updated Track data breach laws (Including GDPR) Train staff to identify and report breaches Test and update regularly
Cyber Security Response – Incident Response Plan Change all passwords immediately Identify types of compromised data and scope of breach Identify who needs to be contacted and how Document your work Determine when the clock starts ticking for potential notification rules Ensure data is no longer being compromised Outline steps necessary in first 72 hours Keep Property ownership updated Track data breach laws (Including GDPR) Train staff to identify and report breaches Test and update regularly
Cyber Security Breach Response – Post Assessment Perform an After Action Review (All parties) Identify lessons learned and close gaps Adjust security and response plans accordingly Update your Incident Response Plan Test your Incident Response Plan (Including training) Train staff on lessons learned

Cyber Liability Insurance
Protect Yourself Through Cyber Liability Insurance By 1 -Sep-2017, each BW hotel was required to obtain Cyber Liability Insurance Coverage of not less than one million dollars Sub limits include • $1, 000 limit for regulatory fines, legal services, public relations, and crisis management expenses • $250, 000 limit for PCI fines levied against any technology breach, and • 100, 000 limit per location for notification and monitoring for guest or personnel records (500, 000 limit in the aggregate)

Cyber Liability Insurance Benefits Closes the gap between traditional coverage and current needs Offsets the expenses of a Data Breach Provides resources for Data Breach Response

Useful Advice
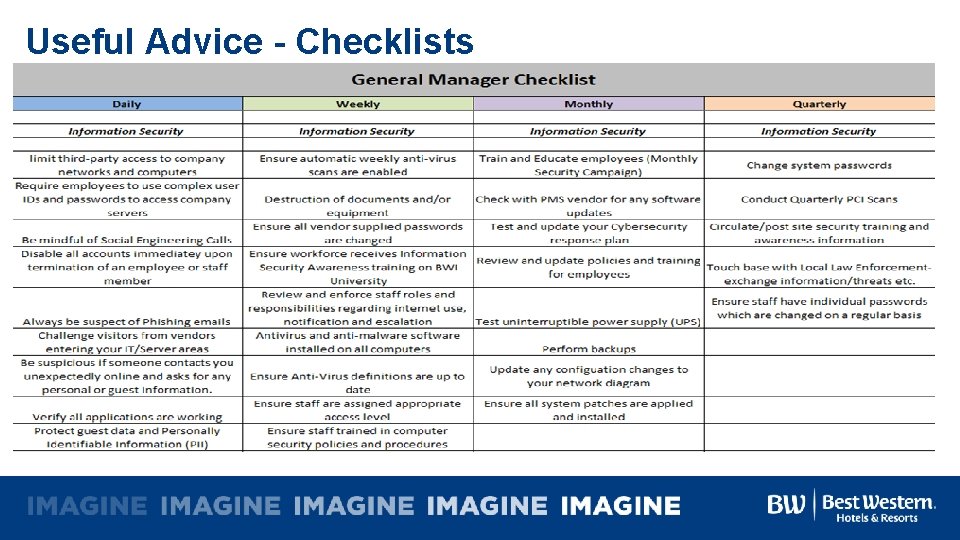
Useful Advice - Checklists

Resources
Resources All About Skimmers: https: //krebsonsecurity. com/all-aboutskimmers/ Payment Card Industry (PCI) Data Security Standard, Requirements and Security Assessment Procedures, Version 3. 2, April 2016, PCI Security Standards Council, https: //www. pcisecuritystandards. org/document_library? cate gory=pcidss&document=pci_dss

Q&A
- Slides: 27