Cyber Security Its Need in the cyber ecosystem
Cyber Security & It's Need in the cyber ecosystem Course on Information Security Certified Professional (ISCP) Vulnerability Assessment and Penetration Testing
What is Hacking ? ? ? • NTC Server details of their customers ? • Election commission Public Data leak ? • Driving License Data expose ? • Bypassing authentication mechanism of an Ebanking portal? • Guessing your neighbour’s Wi-Fi password by trial and error ?
What is Hacking ? ? ? • Guessing your neighbour’s Wi-Fi password by trial and error ? • Defeating android pattern lock by tracing the finger imprint ? • Watching your friend enter his credentials on his system ? • Your 5 yr old relative using your finger to open the screen lock, while you are sleeping !
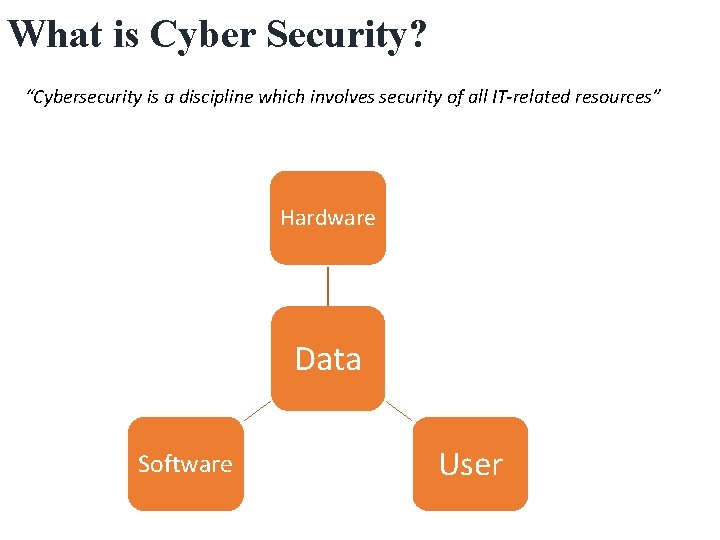
What is Cyber Security? “Cybersecurity is a discipline which involves security of all IT-related resources” Hardware Data Software User
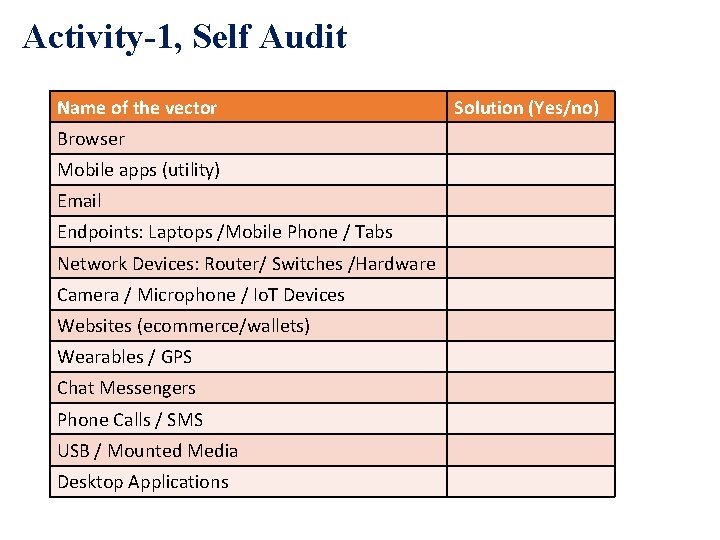
Activity-1, Self Audit Name of the vector Browser Mobile apps (utility) Email Endpoints: Laptops /Mobile Phone / Tabs Network Devices: Router/ Switches /Hardware Camera / Microphone / Io. T Devices Websites (ecommerce/wallets) Wearables / GPS Chat Messengers Phone Calls / SMS USB / Mounted Media Desktop Applications Solution (Yes/no)
Some Facts and Figure
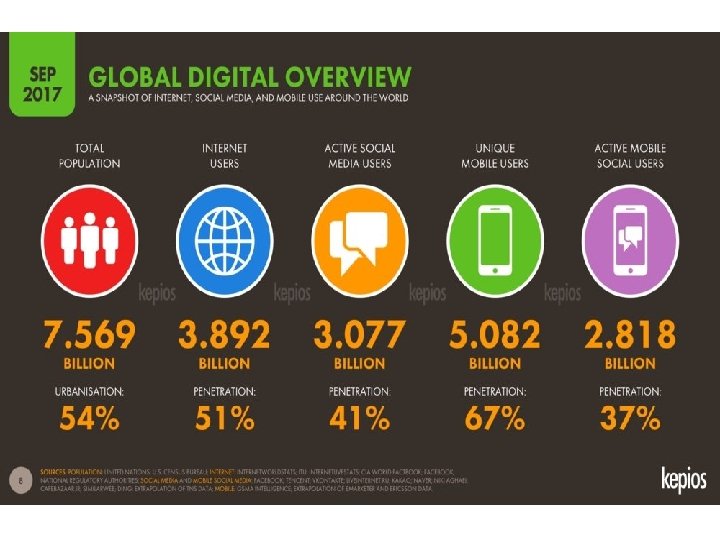


Global Trend The State of Cyber Security • • map. norsecorp. com https: //cybermap. kaspersky. com https: //www. fireeye. com/cyber-map/threat-map. html https: //threatmap. checkpoint. com

Biggest Cyber Attacks 2017

Biggest Cyber Attacks 2017 • Equifax Data Breach – 145. 5 Million Accounts • Uber Data Breach – 57 Million Records
Biggest Cyber Attacks 2017 • Wanna. Cry Cyber Attack 300, 000 Systems • Makes History, Again – 3 Billion Accounts leaked
Biggest Cyber Attacks 2017 • Deep Root Analytics Data Breach – 198 Million U. S. Voters • Rasputin Attacks – 60 Universities and Federal Agencies
Nepal is not an exception in terms of Cyber Crimes • Increase in use of Computer and Internet. • Most Nepalese use Computer and Internet for entertainment purpose and are not aware of risk and knowledge of cyber security
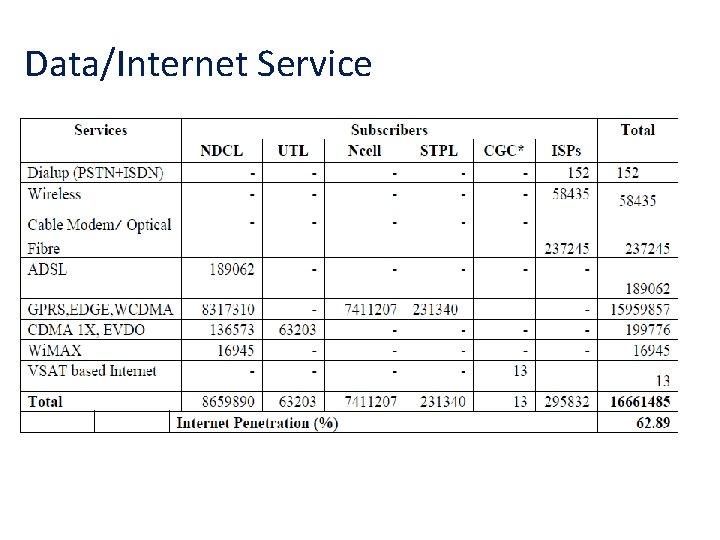
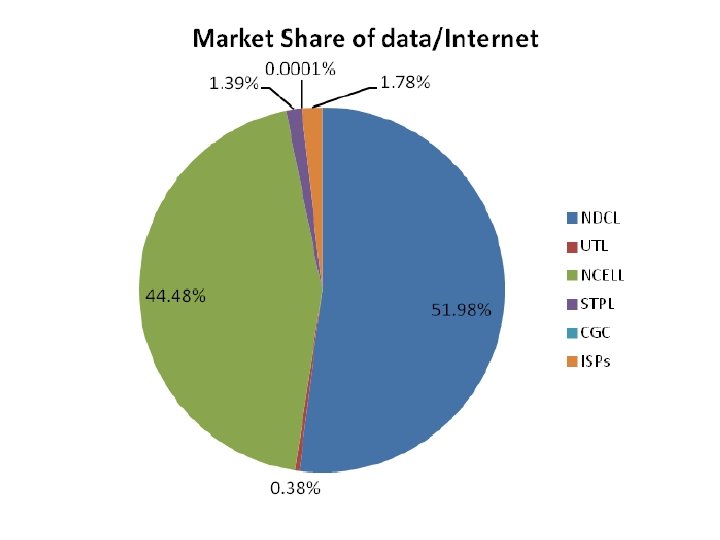
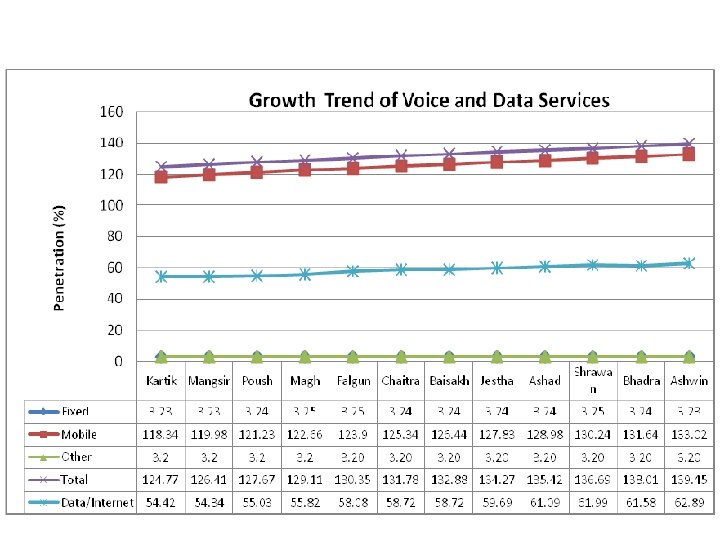
Data/Internet Service
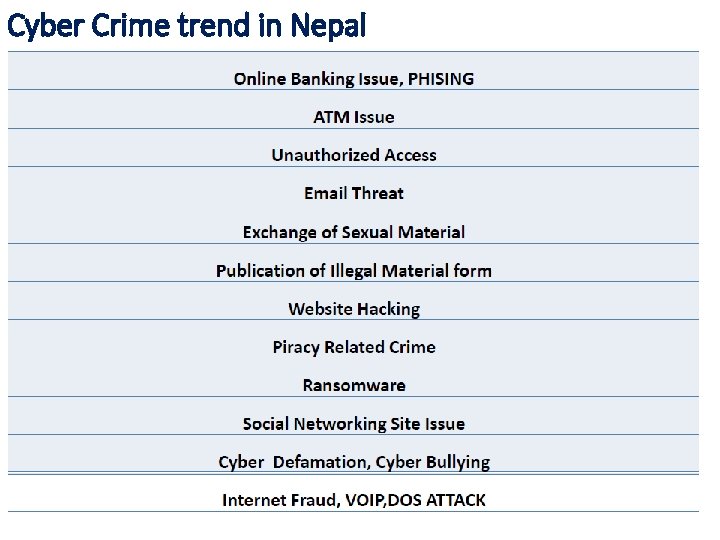
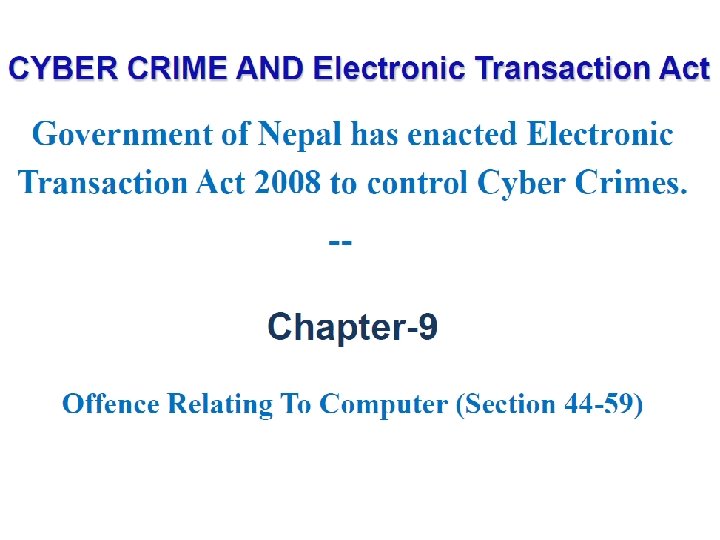
Cyber Crime trend in Nepal
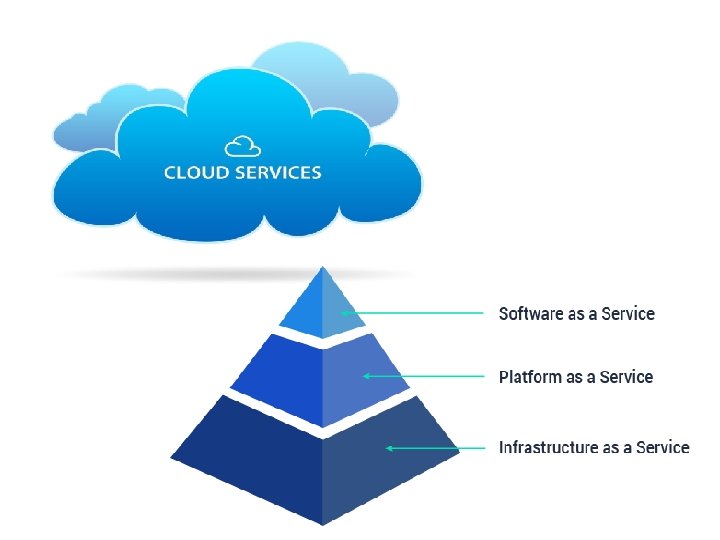
Core Competencies 1. Web Applications 1. Application Server Ø Cross technology: PHP, Nodejs, 2. Java Database Server Ø Cross Framework: Joomla, Wordpress 3. File Server 2. Mobile Applications Ø Android Ø i. OS Application Security Server Security 1. 2. 3. 4. 5. Network Security Wired Networks Wireless Networks Firewalls, IDS, IPS and Honeypots Denial of Service Attacks Malware Attacks Cloud Security Io. T Security
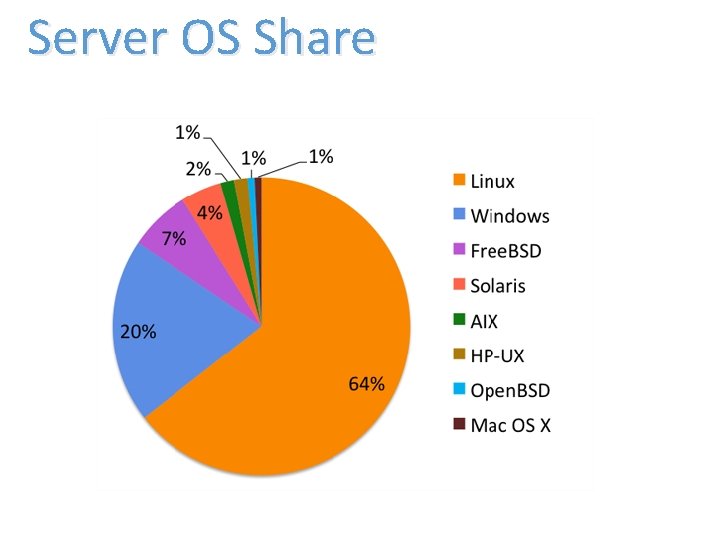
Server OS Share

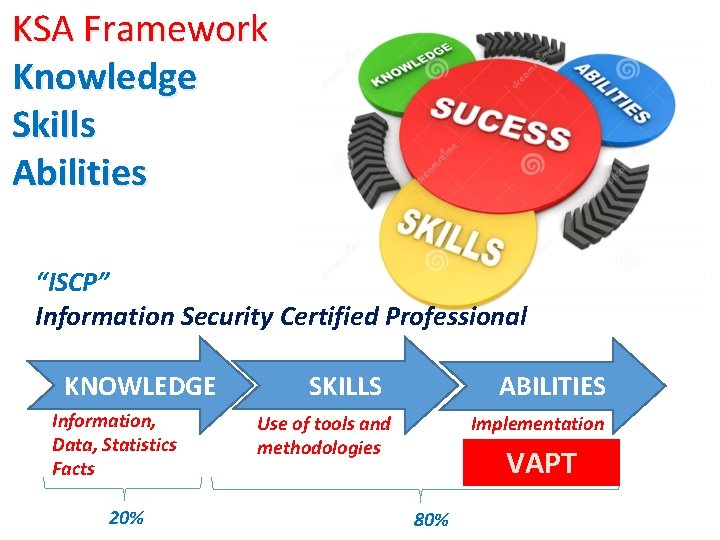
KSA Framework Knowledge Skills Abilities “ISCP” Information Security Certified Professional KNOWLEDGE Information, Data, Statistics Facts 20% SKILLS ABILITIES Use of tools and methodologies Implementation VAPT 80%

Thank You
- Slides: 28